Human vulnerabilities are more dangerous than Windows 10 Endpoint security vulnerabilities. However, we need to make sure endpoints are adequately protected to avoid any security violations.
In this post, you will find Windows 10 Security considerations and a security checklist.
Did you get a chance to read about Microsoft Numbers article and the 1.5 billion Windows-powered devices used around the world?
This number is one of the reasons for having a more sophisticated attack on Windows devices.
Endpoint Security Vulnerabilities
Endpoint devices are most vulnerable in your business environment than any other components. Your Data Centers have two layers of protection.
- Physical Security Protection
- Digital Security Protection
Why Windows is the most commonly attacked platform is because Windows is the most used endpoint operating system (OS) in the enterprise world. What are the security measures we take for endpoints?
All our endpoint devices are protected as data centers and servers? No, endpoints are not covered and secured (both digitally and physically) as servers and other devices in the Data Center.
Windows 10 Endpoints Should Connect to DMZ Network (Crazy?)
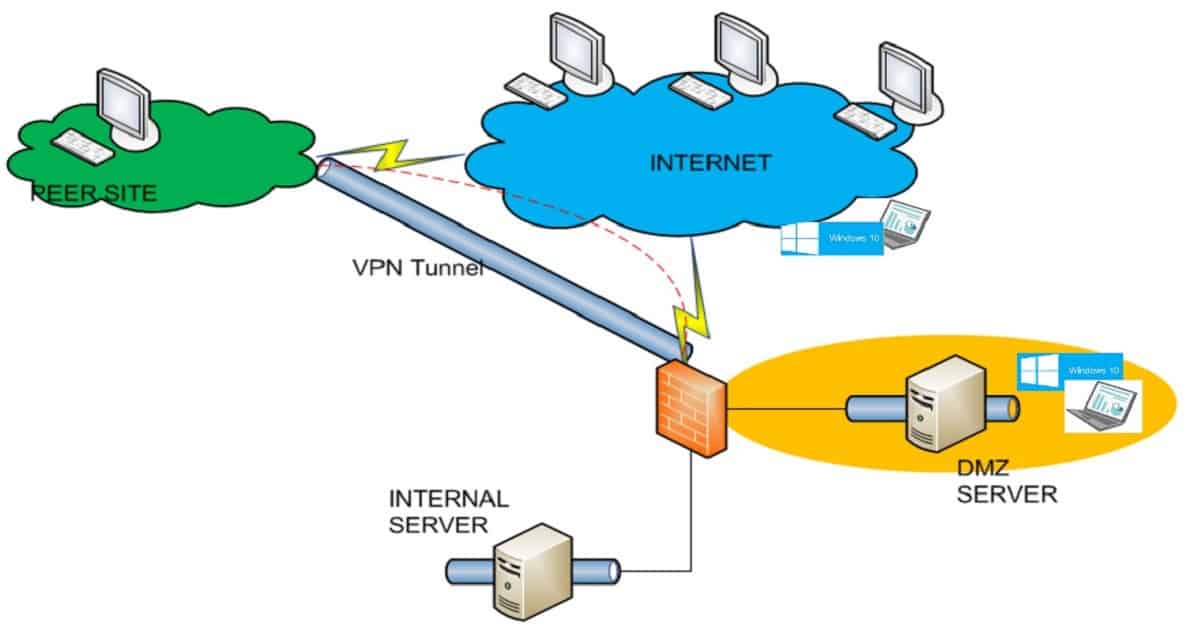
We have different network segments in every organization, and the DMZ segment is the most secure network? Mainly proxy servers and internet-connected servers are placed in this network zone.
DMZs are intended to function as a buffer zone between the public internet and the organizational network. There will be two firewalls to screen all inbound network packets before they arrive at the organization’s servers in the DMZ.
My crazy idea is to consider endpoints as highly vulnerable and place all endpoints into the DMZ segment of your organization’s network.
But I don’t think this will work out because the end-user experience would be pathetic if you connect Windows 10 endpoints to the DMZ network segment.
Windows 10 should NOT Connect to Enterprise Network?
What if I say Windows 10 endpoint should not directly connect to the enterprise network at all? Do you think that would be possible? We can make it possible.
You can manage Windows 10 devices that are on the internet with Intune. Even SCCM CMG can be used to manage internet-based Windows 10 endpoint management. Is this direct internet connection more secure?
You can use modern technologies like Azure App Proxy and Per-App VPN to connect to on-prem applications without direct connection to the enterprise network.
Is this safer? Yes, it could be safer. But still, you need to ensure that your Windows 10 security is tight.
Windows 10 Security Checklist Starter Kit?
Windows 10 already provides the following security features. Hardware-based isolation, Network Protection, Controlled Folder Access, Exploit Protection, and other technologies reduce the attack surface and increase attacker costs.
Microsoft is delivering advanced world protection for Windows 10 powered devices. Recently, they announced an enhancement to Windows Defender Antivirus. Defender antivirus can now run in a sandbox.
The following are some points you need to check before your Windows 10 mass deployment. The full Windows 10 security checklist is explained in the webinar by IT PRO Today and Adaptiva.
Device Guard Enabled
Credential Guard Enabled
Application Guard Enabled
Application Control Enabled
Attack Surface Reduction Applied
Adaptiva has provided a checklist for Windows 10 security. There was also a webinar on Windows 10 security checklist.
I think all IT Pros should watch this recorded webinar and implement these security measures on their Windows 10 devices.
More details are available in the following link Windows 10 Security Checklist Webinar.