Key Takeaways
- This policy controls how aggressively Microsoft Defender blocks and scans suspicious files.
- Higher blocking levels provide stronger security but may cause false positives.
- Lower blocking levels focus on balanced protection and better performance.
- Zero tolerance level blocks all unknown executables for maximum security.
Hey, let’s discuss about Managing Suspicious File Blocking in Microsoft Defender using Intune. This policy controls how strictly Microsoft Defender Antivirus scans and blocks suspicious files. In simple terms, it decides how quickly and aggressively Defender should act when it finds something unusual. When the setting is enabled, Defender becomes more aggressive it blocks and scans suspicious files more often to reduce risk. When it’s disabled, Defender is less strict, which can lower interruptions but may also reduce protection.
Table of Contents
Table of Contents
Managing Suspicious File Blocking in Microsoft Defender using Intune
When enabled, Defender becomes more aggressive in blocking and scanning files. The levels range from 0x0 (default) with balanced protection, 0x1 (moderate) for high-confidence detections only, 0x2 (high) and 0x4 (high+) for stronger blocking with possible false positives or performance impact, up to 0x6 (zero tolerance), which blocks all unknown executables for maximum security.
- Block Executable Files with Prevalence Age or Trusted List Criteria using Intune ASR Rules
- Supporting Secure Login Practices Through NTLM Auditing using Intune Policy
- Restrict All Downloads from Microsoft Edge Browser to Protect Data using Intune
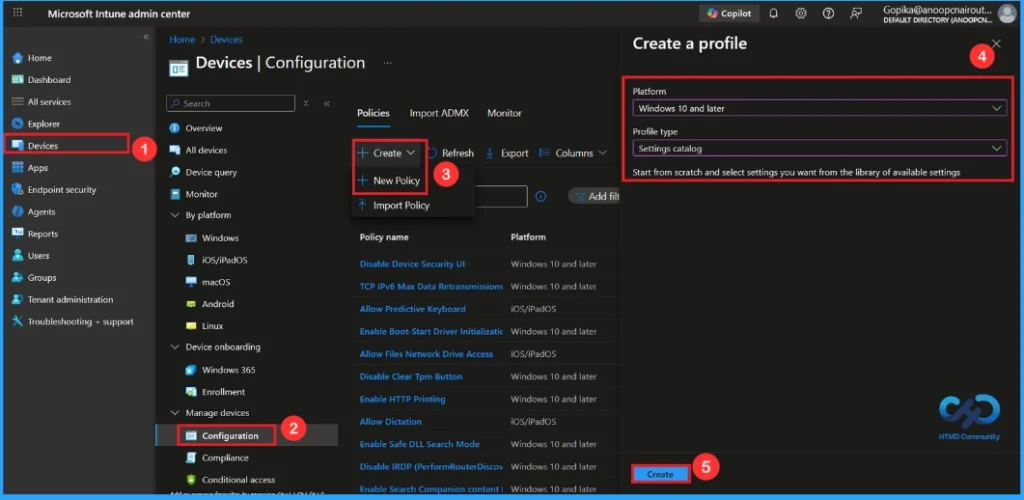
How to Start Policy Creation
By sign in with your Credentials an admin can easily configure Cloud Block Level policy with Microsoft Intune. After Sign in Go to Devices > Configuration >+ Create > +New Policy .Profile creation is the necessary step that helps you to assign the policy to appropriate platform and Profile. Then click on the Create button.
| Platform | Profile Type |
|---|---|
| Windows 10 and later | Settings Catalog |
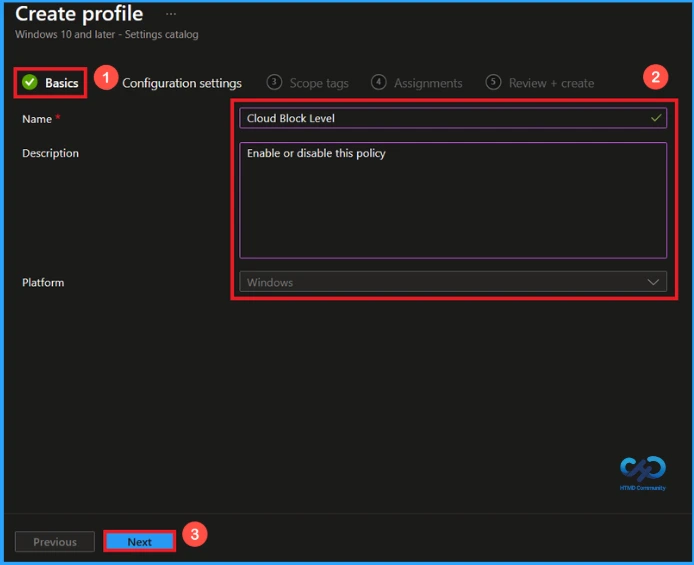
Basic Tab for Name and Description
This is an important and necessary step that allows you to know the purpose of the policy. Here is Name(cloud block level) is mandatory and description is optional. After adding this click on the Next button.
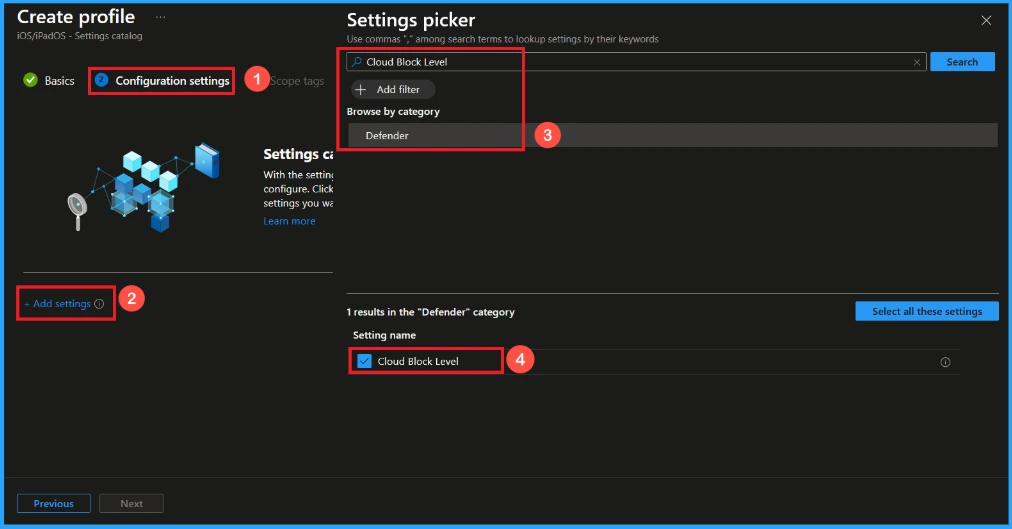
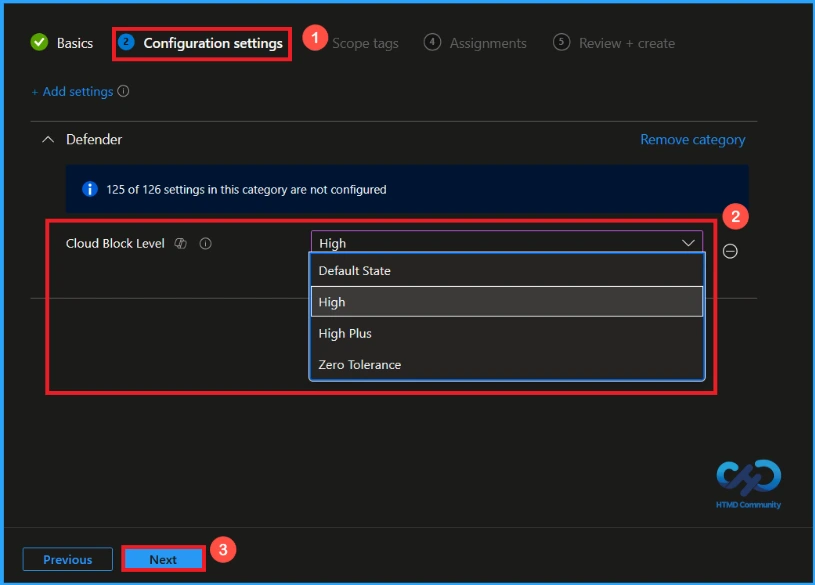
Configure Cloud Block Level Policy
On this tab, you can click on the +Add Settings hyperlink to get the Settings Picker. The settings picker shows huge number of settings. Here, i choose Defender as category and select cloud block level settings.
After selecting the policy, you will be on the Configuration Settings page. Here, you can see the cloud block level policy which is currently in the default state. If you continue with that, click the Next button.
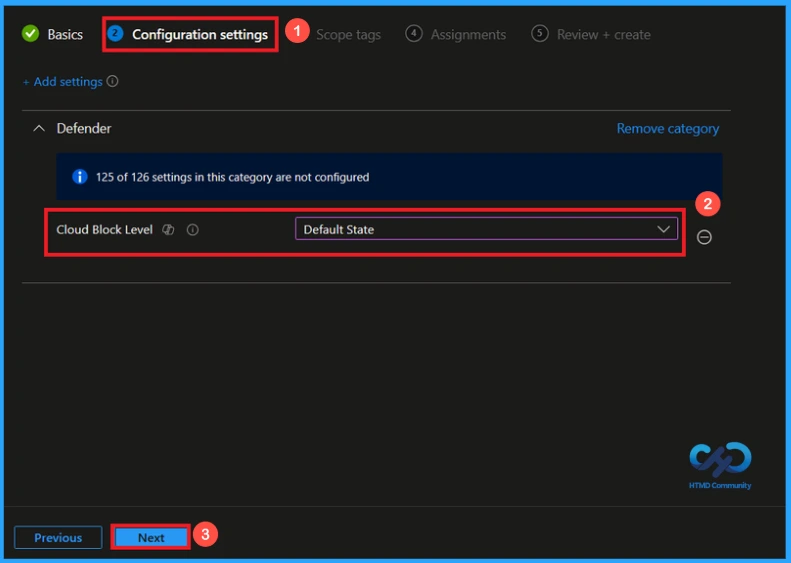
Here, when you click the drop down arrow next to cloud block level, you can see options such as default state, high, high plus, and zero tolerance. After selecting the High option, i click the Next button to proceed.
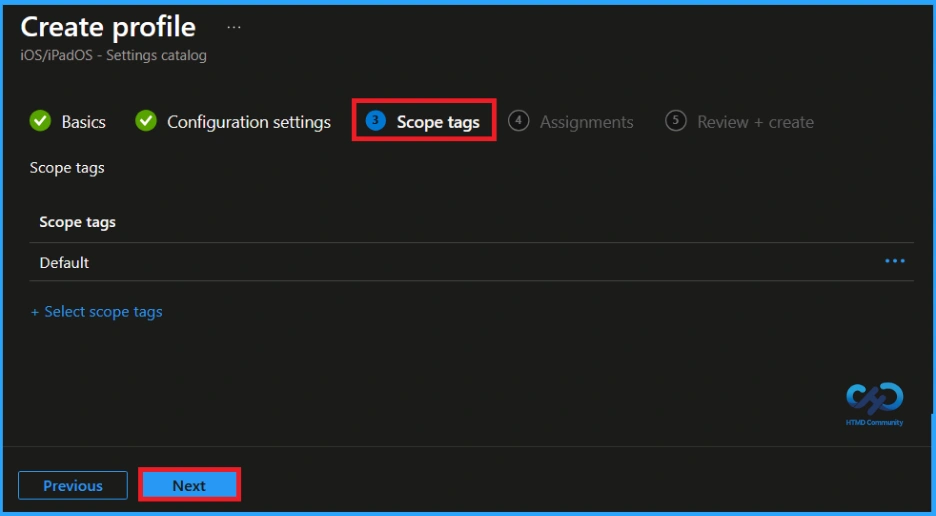
Scope Tags
After configuring the settings, click Next. You will then reach the Scope Tag section. Scope tags help you organize and filter policies based on departments, locations, or roles. They make it easier to manage and assign policies to the right groups. If you want to add a scope tag for your policy, you can easily do that. Once done, click Next to continue further.
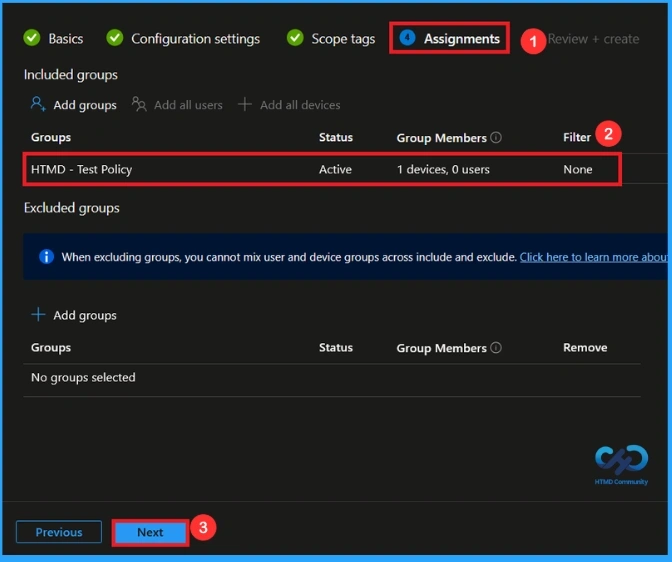
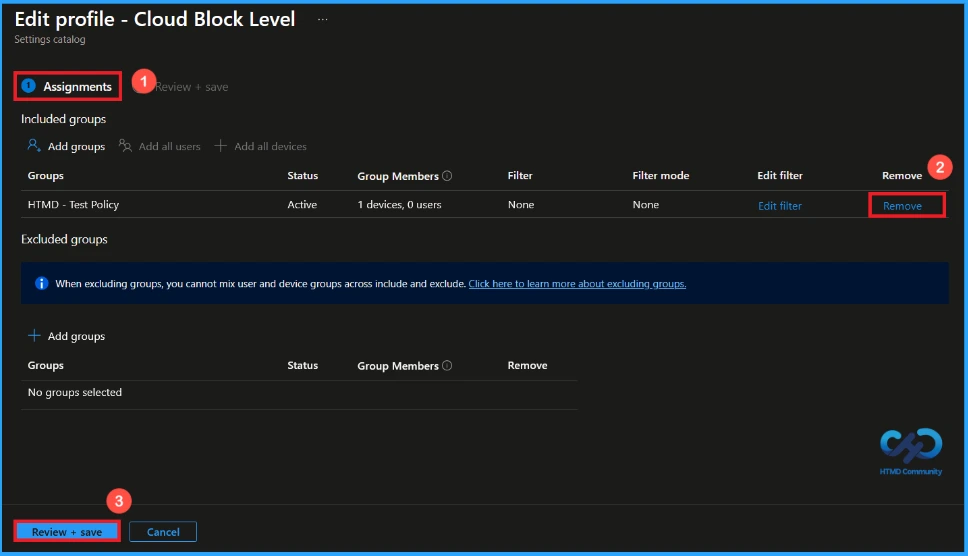
Assignment Tab
To assign the policy to specific groups, you can use the Assignment Tab. Here I click, +Add groups option under Included groups. I choose a group(HTMD – Test Policy) from the list of groups and click on the Select button. Again, I click on the Next button to continue.
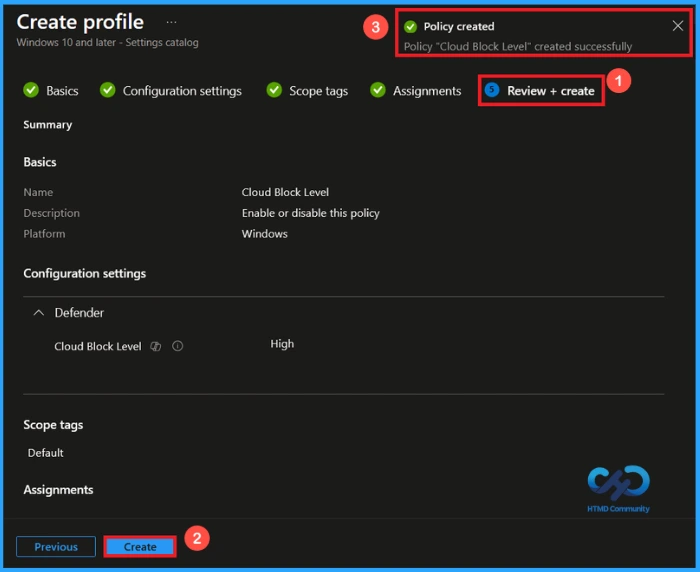
Review + Create Tab
After Assignments, you will reach the Review + Create page. Here, you can review all the information and settings you have entered. If you need to make any changes, you can go back to the previous tabs and edit the configurations. Once you click Create, the policy will be successfully created and ready for deployment.
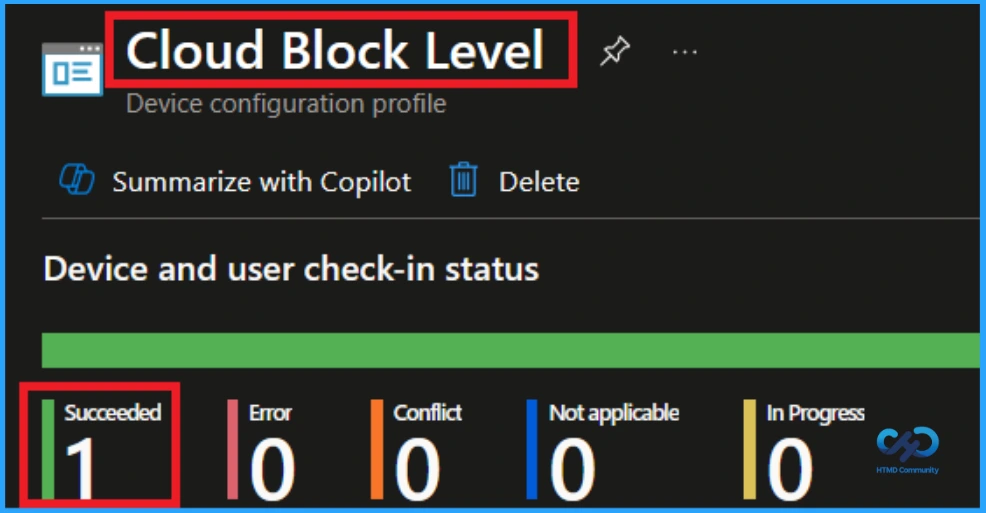
Monitoring Status
The Monitoring Status page shows whether the policy has succeeded or not. To quickly configure the policy and take advantage of the policy sync the assigned device on Company Portal. Open the Intune Portal. Go to Devices > Configuration > Search for the Policy. Here, the policy shows as successful.
How to Remove Assigned Group from Cloud Block Level Policy
After creating the policy, if you want to remove the specific group that you previously selected, you can easily do that. First, go to Devices > Configuration policies. In the Configuration policy section, search and select the policy. In the Assignment section, you will find an Edit option and click on it. Then, click the Remove option.
For detailed information, you can refer to our previous post – Learn How to Delete or Remove App Assignment from Intune using by Step-by-Step Guide.
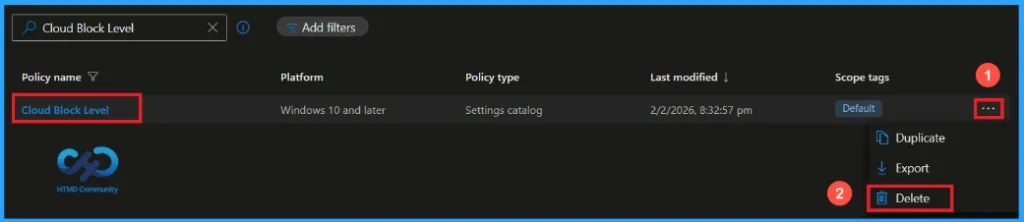
How to Delete Cloud Block Level Policy from Intune
If you want to delete this policy for any reason, you can easily do so. First, search for the policy name in the configuration section. When you find the policy name, you will see a 3-dot menu next to it. Click on the 3 dots, then click the Delete button.
For detailed information, you can refer to our previous post – How to Delete Allow Clipboard History Policy in Intune Step by Step Guide.
Need Further Assistance or Have Technical Questions?
Join the LinkedIn Page and Telegram group to get the step-by-step guides and news updates. Join our Meetup Page to participate in User group meetings. Also, Join the WhatsApp Community and WhatsApp Channel to get the latest news on Microsoft Technologies. We are there on Reddit as well.
Author
Anoop C Nair has been Microsoft MVP for 10 consecutive years from 2015 onwards. He is a Workplace Solution Architect with more than 22+ years of experience in Workplace technologies. He is a Blogger, Speaker, and Local User Group Community leader. His primary focus is on Device Management technologies like SCCM and Intune. He writes about technologies like Intune, SCCM, Windows, Cloud PC, Windows, Entra, Microsoft Security, Career, etc.


