Key Takeaways
- Microsoft has newly introduced a focus on post-quantum cryptography in Windows security
- Quantum computing could break current encryption methods like RSA and Diffie-Hellman
- Post-quantum cryptography offers quantum-resistant alternatives
- Enterprises must begin transitioning to quantum-safe systems early
In this post we are discussing Microsoft Introduces Post-Quantum Cryptography for Future Windows Security. Microsoft has newly introduced a strong focus on post-quantum cryptography (PQC) as part of its evolving Windows security strategy. This move comes in response to the growing awareness that future quantum computers could break many of the encryption methods used today to protect sensitive data, communications, and digital identities.
Table of Contents
Table of Contents
Microsoft Introduces Post-Quantum Cryptography for Future Windows Security
Encryption is a part of technology, securing everything from online transactions and emails to enterprise systems and cloud services. However, most of today’s widely used cryptographic algorithms, especially those based on asymmetric encryption, depend on mathematical problems that are difficult for classical computers to solve but could become vulnerable with the advancement of quantum computing.
- Advancing Windows 11 Security with In-Memory Patching and Zero Trust DNS
- 8 Ways to Know Security Identifier SID of User in Windows 11
- TPM 2.0 Transition to Windows 11 For Better Security
Why Quantum Computing is a Turning Point
Quantum computing introduces a new model of computation using qubits, allowing multiple calculations to occur continuously. This significantly increases processing power compared to classical systems.
With sufficient scale, quantum computers could break current encryption algorithms like RSA and Diffie-Hellman using advanced techniques. This creates a serious risk for systems that rely on these methods for securing communications and data.
Key Uses of Asymmetric Cryptography
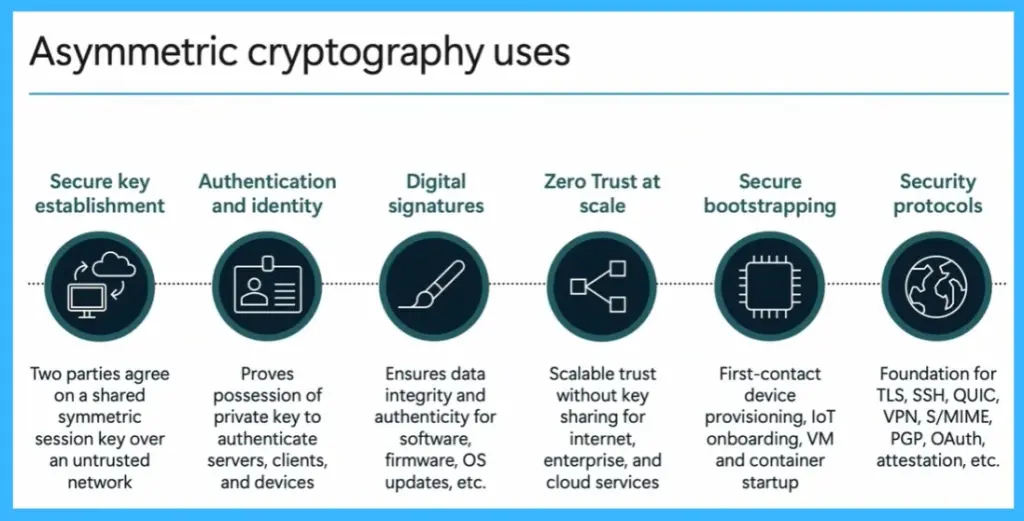
It is used for secure, where two parties can safely agree on a shared key over an untrusted network. It also supports authentication and identity by allowing systems to verify users, devices, and servers through private key ownership. In addition, asymmetric cryptography enables digital signatures, ensuring the integrity and authenticity of software, firmware, and operating system updates.
It is also for implementing zero trust at scale, allowing secure communication without directly sharing keys. Other important uses include secure bootstrapping for device provisioning, IoT onboarding, and virtual machine startup. Overall, it forms the foundation of major security protocols such as TLS, SSH, VPN, S/MIME, PGP, and OAuth.
| Asymmetric cryptography uses | info |
|---|---|
| Secure key establishment | Two parties agree on a shared symmetric session key over an untrusted network |
| Authentication and identity | Proves possession of private key to authenticate servers, clients, and devices |
| Digital signatures | Ensures data integrity and authenticity for software, firmware, OS updates, etc. |
| Zero Trust at scale | Scalable trust without key sharing for internet, enterprise, and cloud services |
| Secure bootstrapping | First-contact device provisioning, loT onboarding, VM and container startup |
| Security protocols | Foundation for TLS, SSH, QUIC, VPN, S/MIME, PGP, OAuth, attestation, etc. |
How Quantum Computers Threaten Current Encryption
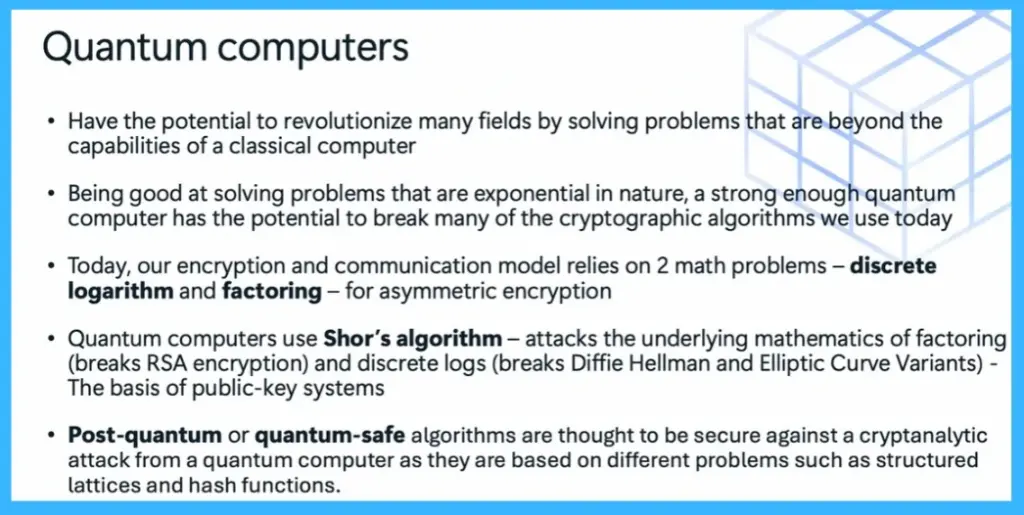
Quantum computers have the potential to transform computing by solving problems that are beyond the capabilities of classical systems. They are particularly effective at solving complex mathematical problems that grow exponentially, which are the basis of many current encryption methods.
However, quantum computers can use Shor’s algorithm to break these problems efficiently, putting widely used algorithms such as RSA, Diffie-Hellman, and elliptic curve cryptography at risk. To address this, post-quantum cryptography introduces new algorithms based on different mathematical approaches, such as lattice structures and hash functions, which are designed to resist quantum attacks.
| Quantum computers |
|---|
| Have the potential to revolutionize many fields by solving problems that are beyond the capabilities of a classical computer |
| Being good at solving problems that are exponential in nature, a strong enough quantum computer has the potential to break many of the cryptographic algorithms we use today |
| Today, our encryption and communication model relies on 2 math problems – discrete logarithm and factoring – for asymmetric encryption |
| Quantum computers use Shor’s algorithm – attacks the underlying mathematics of factoring (breaks RSA encryption) and discrete logs (breaks Diffie Hellman and Elliptic Curve Variants) – The basis of public-key systems |
| Post-quantum or quantum-safe algorithms are thought to be secure against a cryptanalytic attack from a quantum computer as they are based on different problems such as structured lattices and hash functions. |
Why Post-Quantum Cryptography Matters
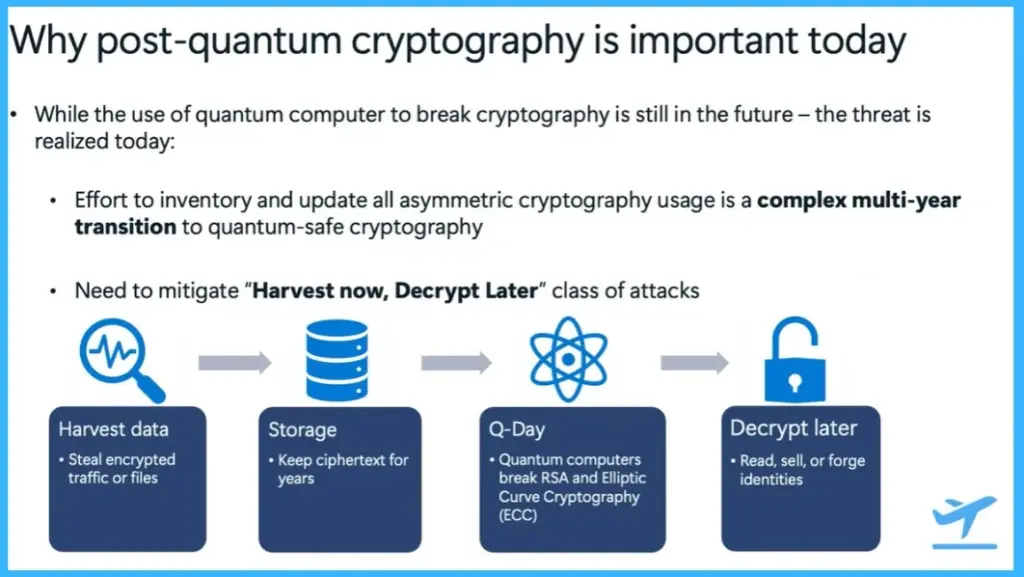
Although quantum computers capable of breaking encryption are not yet fully developed, the risk is already present. One of the main challenges is that transitioning to quantum-safe cryptography is a complex and long-term process that requires updating systems across enterprises, applications, and devices.
Attackers collect encrypted data and store it for future decryption when quantum computers become powerful enough. This is especially risky for long-term sensitive data, as it could be exposed years later. Because of these risks, organizations must start preparing now to ensure their systems remain secure in the future.
- While the use of quantum computer to break cryptography is still in the future – the threat is realized today:
- Effort to inventory and update all asymmetric cryptography usage is a complex multi-year transition to quantum-safe cryptography
- Need to mitigate “Harvest now, Decrypt Later” class of attacks
Need Further Assistance or Have Technical Questions?
Join the LinkedIn Page and Telegram group to get the latest step-by-step guides and news updates. Join our Meetup Page to participate in User group meetings. Also, join the WhatsApp Community and the Whatsapp channel to get the latest news on Microsoft Technologies. We are there on Reddit as well.
Author
Anoop C Nair is a Workplace Technology solution architect with 25+ years of experience. Microsoft Certified Trainer. Microsoft MVP from 2015 onwards for consecutive 11+ years! He is a blogger, Speaker, and Founder of HTMD Community and HTMD Conference. His main focus is on Device Management technologies like Intune, Windows, and Cloud PC. He writes about technologies like Intune, SCCM, Windows, Cloud PC, Entra, and Microsoft Security.