Today, we will discuss the Intune Scope Tags Implementation Guide. Intune Scope tags were introduced in the MEM portal. Use them to give administrative users a filtered view of securable objects.
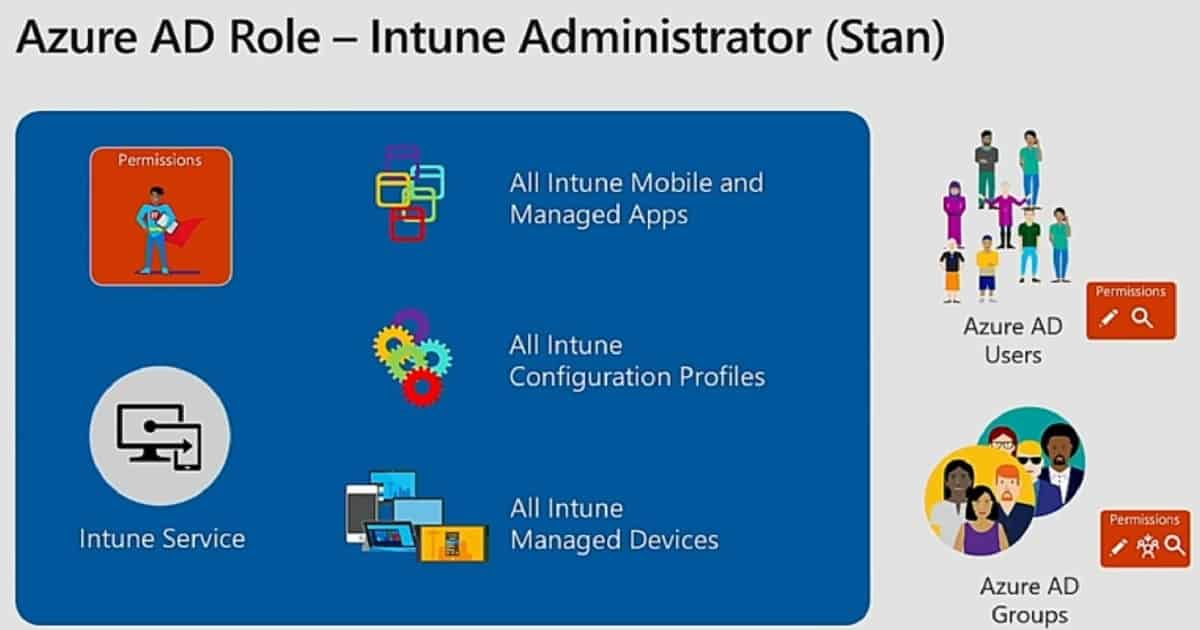
Azure AD global admins are not required to perform all the Intune admin roles. So, it’s better to minimize AAD admin roles in your organization.
Scope tags are an Intune feature that allows admins to set a tag (fundamentally a feature) on any content in Intune, such as apps, profiles, devices and more. This permits them to manage only resources assigned with a specific tag.
The Intune team did excellent work, including scope features in Intune RBAC. I recommend watching David Falkus and Dave Randall’s Ignite session BRK3026.
Table of Contents
- Intune Role-Based Administration RBAC
- Intune Read the Only Experience to Create Read-Only Operators]
Intune RBAC Implementation – Tips
I don’t recommend setting up the Intune administrator role in Azure AD for all RBAC Intune operation teams. Instead, you need to create RBAC Intune operation team member IDs as normal user IDs in Azure AD.
And use those normal IDs to provide the relevant access using Intune Roles, Scope Groups, and Scope Tags. You can have some Intune Admins in Azure AD who will have all the Intune access.
But remember, when your admin is part of Intune Administrator, you can’t reduce the permissions using Intune roles in the Intune blade.
Azure AD – Intune Administrator Role – Super Admin Role for Intune (You can’t reduce this admin permission using Intune Roles)
Note – The feature explained in the post is not working as expected during my testing. So, I have not included the Intune admin experience. I will soon share a follow-up post and video guide.
Video Guide – How to Implement Intune RBAC
The following video guide explain how to implement RBAC in Microsoft Intune.
What are Intune Scope Tags?
Use Intune scope tags to give administrative users a filtered view of securable objects. Scope tags are filtering options provided in Intune to facilitate admin tasks.
When I write this post, all the Intune objects are not secure. You can add scope tags to all Intune objects, such as applications (coming soon), policies, profiles, etc.
The following are the Intune securable objects. As you can see, some of the Intune-managed devices are NOT secure now, but those objects will soon become secure.
Automation for auto-assigning tag options is coming soon for Intune-managed objects. All these details are explained in the Ignite session below.
List of Intune Securable Objects
- Configuration Profiles
- Compliance Policies
- Update Rings
- Compliance Notifications
- Managed Device
- Client Apps (Coming Soon)
- VPP Tokens (Coming Soon)
- App Categories (Coming Soon)
- App Protection Profiles (Coming Soon)
- App Config (Coming Soon)
What are Scope Groups and Member Group Users?
You can only assign scope tags to an Intune admin from the role assignments blade. You can only assign a scope tag you have in your role assignment(s).
This is what was shared by David Falkus & Dave Randall in the above-mentioned ignite session.
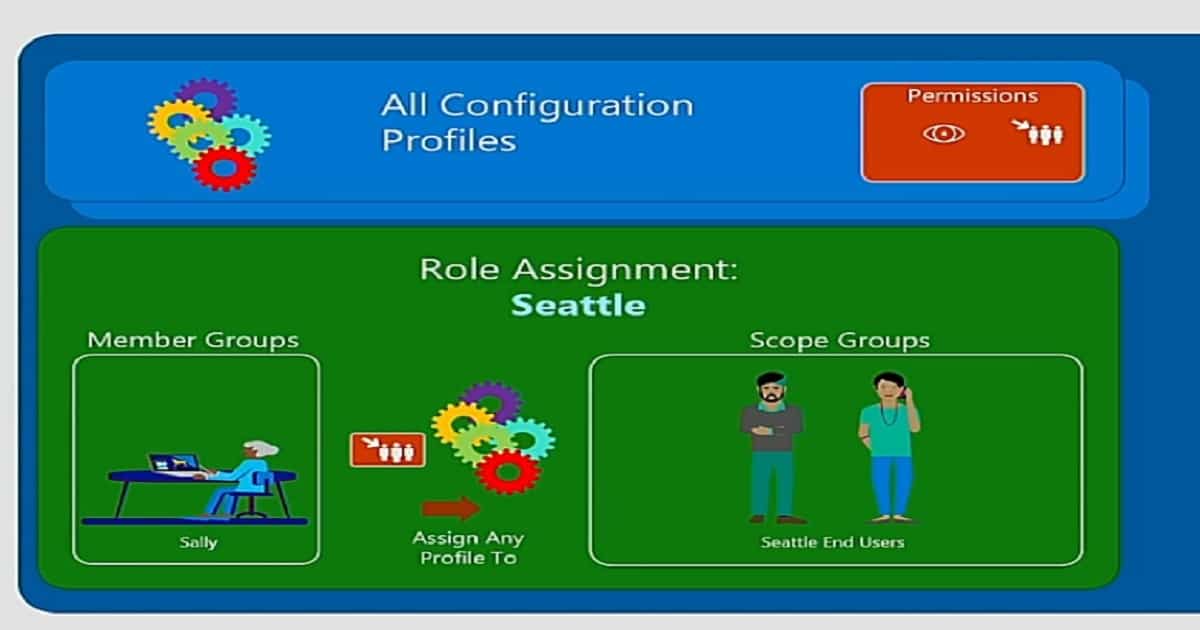
Intune Administrator Members are the admins who can do Intune activities. Member Group users are the administrators assigned to this role.
Intune Scope Groups—Intune Admins in this Role Assignment can target policies, small tasks, or applications to these Scope Groups. This grouping is similar to limiting collection in SCCM RBAC security scopes.
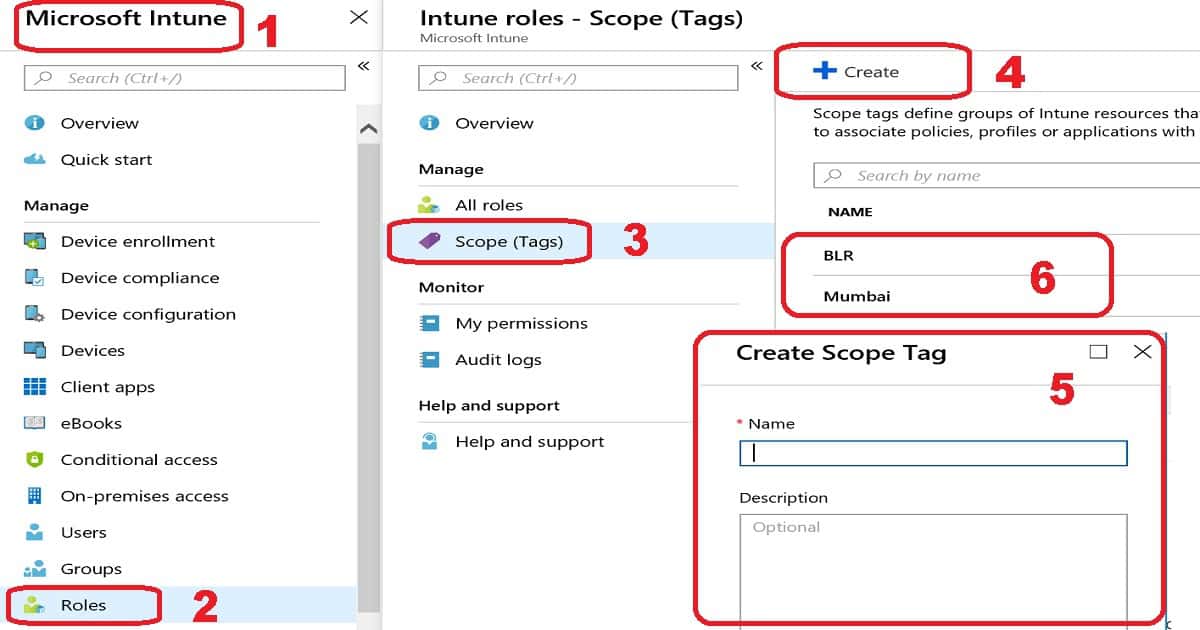
How to Create Intune Scope Tags?
- Login to Azure Portal Navigate to Intune blade
- Select Role and then select Scope (tags)
- Select the + Create button
- Enter a Name and Description. I have given my branch office location names like Mumbai and Bangalore. You can create the name and description as per your requirement.
How to Assign an Intune Scope Tag to an Admin Role
This section will learn how to assign an Intune scope tag to an Intune Admin role. As I mentioned in the second paragraph of this post, try to reduce Intune FULL admins for your tenant by assigning segregated Intune admins roles. I also explained this in the previous post
Using the following method, You can assign an Intune Admin role to an admin. Also, you can assign access only to a particular group of users/devices using Intune Scope tags.
[Related Posts – Intune Role-Based Administration RBAC and Intune Read the Only Experience to Create Read-Only Operators]
- Ensure you have created the Security Scope Tags mentioned in the above section.
- Login to Azure Portal and Navigate to Intune Blade
- Select Role and then select a Built-in or custom Intune admin role (For example – Policy and Profile Manager, School Administrator, Help Desk Operator, Application Manager, Read-Only Operator, or Intune Role Administrator )
- Select Assignments, and Select the +Assign button to create a new assignment. In the new assignment, you will define all the details about Scope Tags, Scope Groups, and Member Group users.
- Enter the Assignment name and Description. I have given the Assignment name Mumbai Admins. You can provide an appropriate name. The description: This is the role assignment for Mumbai Admins. This admin shall have access to Mumbai location-related objects and groups.
Click the Members (Groups) option and select Azure AD Group for Intune Admins, who will be assigned to Intune roles, scope tags, and scope groups. In my scenario, I have selected the AAD group created for Mumbai Intune Admins.
Their admins will manage all deployments related to the Mumbai location. Member Group users are the administrators assigned to this role.
Click Scope (Groups). In this role assignment, Administrators (the group you selected in STEP #6 above) can target policies, applications, or small tasks to these Scope Groups.
You can select Scope to All Users & All Devices if you want the admin group to manage all devices and users in your organization.
Click on Select Groups to Include to select a specific AzureAD Group for a set of users or devices if these Intune admins are part of a particular location or business unit.
Follow the steps mentioned in the below pic. Administrators in this Role Assignment can target policies, applications, or small tasks to these Scope Groups.
Click on Scope (Tags) and click on +Add. Ensure you have completed the above “How to Create Intune Scope Tags?” section. Select Intune Security Scope “Mumbai.” Click on the button. Click on OK.
Click OK to complete the Role Assignment process and close the blade.
[Related Posts – Intune Role-Based Administration RBAC and Intune Read the Only Experience to Create Read-Only Operators]
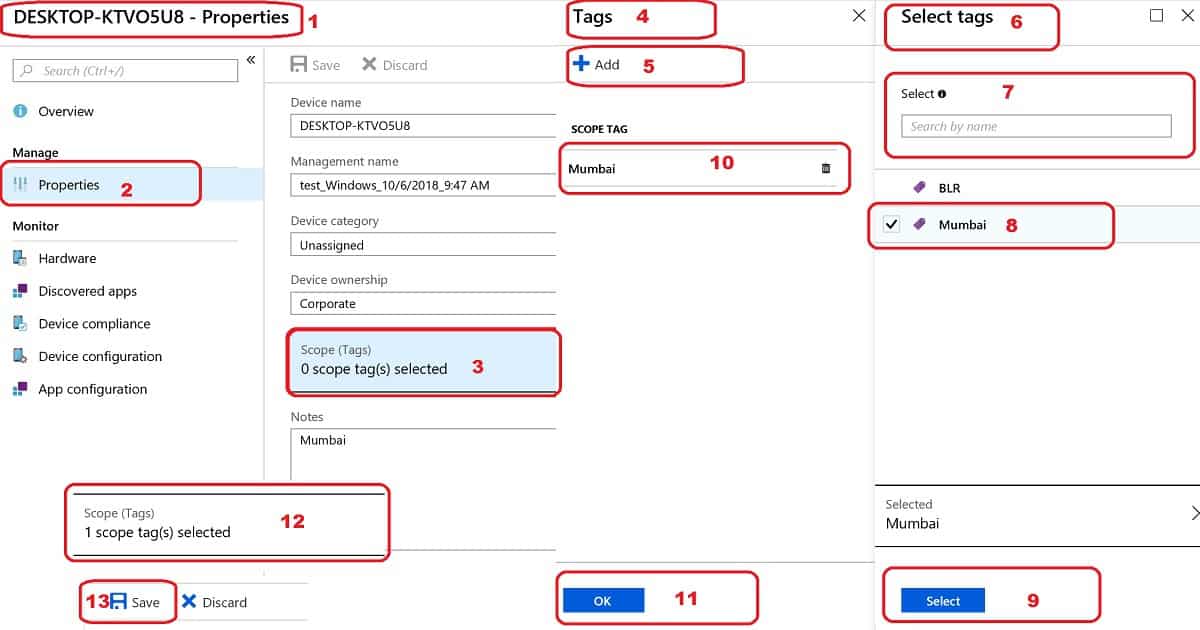
How to Change the Intune Scope Tags of Devices
In this section, you will learn how to change the scope tag of Intune objects. I recommend reading the above paragraph, where I explain Intune objects and which are securable Intune objects.
You can change the Intune Scope Tag for all securable Intune objects. More details are available in the Intune Securable Object section above.
The following is one example of setting the scope tags for Intune objects. But you can use a similar method to set the Intune scope tags for all the supported Intune objects.
- Login to Azure Portal and Navigate to Intune Blade
- Click on Devices & then Click on All Devices
- Select the Device on which you want to Set the Scope Tag and go to the Properties of that device
- Click on Scope (Tags) to set that device.
- Click on +Add to search Scope (Tags). I have used Scope (Tags) for Mumbai
- Click on the OK, OK, and Save button to close all the blades and complete the process
Automation of Intune Scope Tags for All Intune Objects
There is also an automated way to change the Intune scope tags of all the supported objects. This has been explained in the Ignite session I referred to in the post. Intune PowerShell module can be used to automate Intune Scope Tags for existing objects.
Download the Intune PowerShell module
Resources
We are on WhatsApp. To get the latest step-by-step guides and news updates, Join our Channel. Click here –HTMD WhatsApp.
Author
Anoop C Nair is Microsoft MVP! He is a Device Management Admin with more than 20 years of experience (calculation done in 2021) in IT. He is a Blogger, Speaker, and Local User Group HTMD Community leader. His primary focus is Device Management technologies like SCCM 2012, Current Branch, and Intune. He writes about ConfigMgr, Windows 11, Windows 10, Azure AD, Microsoft Intune, Windows 365, AVD, etc.

Is there any information on how to use powershell to automate or batch assign scope tags to devices?
Hi John M, here there is an example of how to use Powershell to automate scope tags assignment for devices.
https://github.com/microsoftgraph/powershell-intune-samples/blob/master/RBAC/RBAC_ScopeTags_DeviceAssign.ps1
Regards,
Since the Roles option is no longer available in the new EM console do you have any update on doin this in the new console