Hello Everyone. I’m back with a new interesting topic, Microsoft 365 Defender Attack Simulation to Educate Users about Phishing Emails. Every organization will have trouble educating their users about Phishing Emails. Even with many awareness sessions conducted for their employees, we have seen organizations fall prey to the threats.
In this article, we will learn how to educate users regarding Phishing emails by launching the Attack Simulation feature in Microsoft Defender. Attack Simulation is the process of simulating real-time attacks that are not harmful to the organization and checking the user’s awareness of Phishing Emails.
Suppose a user clicks on the URLs or falls prey to the simulated emails. In that case, we can assign them related training and provide awareness on how to be conscious in the future to avoid these kinds of situations happening in the real world using the Microsoft Defender Attack Simulator.
Phishing is a generic term used for email attacks that try to steal sensitive information from organizations. These emails appear to be from trusted resources. In Attack Simulator, Defender uses Safe Links for Office 365 to securely track click data for the URL in the payload message sent to targeted phishing campaign recipients.
- Latest MDE Architecture Changes to Enhance Onboarding Experience
- Microsoft Defender Antivirus Periodic Scanning in Windows 11
Prerequisites for Launching Attack Simulation
Attack Simulation and training help in the reduction of Phishing attacks and help in measuring the users’ awareness of phishing attacks. We can also measure the behavioural change of users by simulating similar attacks repeatedly. Now, Let’s see the Prerequisites for launching an Attack Simulation from the Security portal/Microsoft Defender Portal.
- An organization should have purchased Microsoft 365 E5 or Microsoft Defender for Office 365 Plan 2 license.
- An Admin should have the following Azure Roles
- Global Administrator
- Security Administrator
- Attack Simulation Administrators
- Attack Payload Author
Types of Microsoft 365 Defender Attack Simulations Available for use
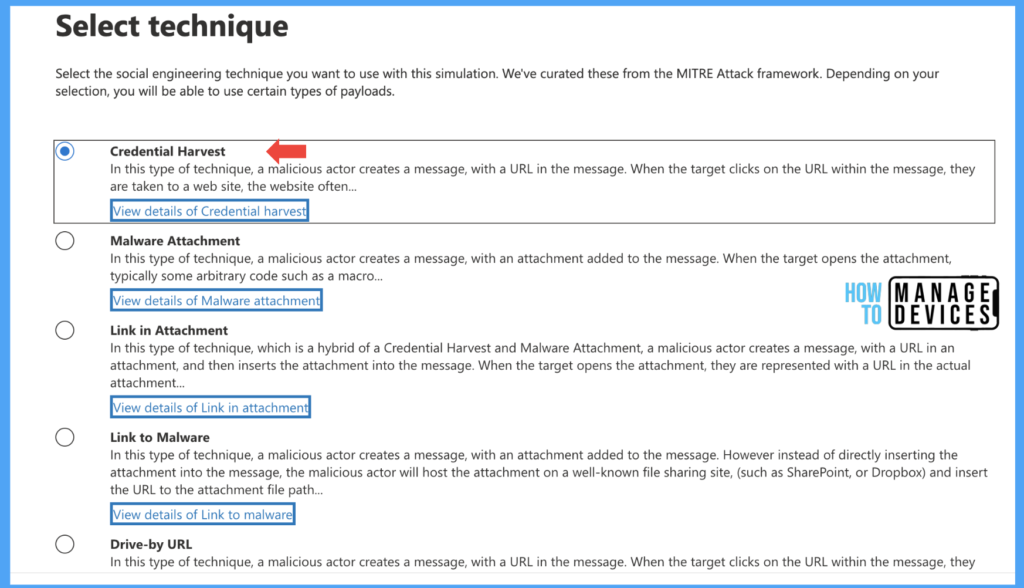
Attack Simulation will help organizations with actionable insights and training for end users. Microsoft Defender provides various Social Engineering techniques to simulate various attacks. Let’s see the different techniques that can be used to launch the attack.
| Technique | Description |
|---|---|
| Credential harvest | In this technique, the user will receive an email with a URL to the malicious site, asking the user to enter a username and password. |
| Malware Attachment | In this technique, the user will receive an email with an attachment containing Malware (typically macros). When opens the attachment, the macros will be installed on the user’s device. |
| Link in Attachment | This technique combines both Credential Harvest and Malware Attachment. The user will receive an email with the attachment. The attachment contains a URL to the malicious website where the user is prompted to enter credentials. |
| Link To Malware | In this technique, the user will receive an email with a link to Malware, the link typically of (SharePoint, OneDrive or well-known file-sharing websites). When the user clicks on the URL, the device will install Malware. |
| Drive-by URL | In Drive-by URL techniques, the Email message will contain a URL for a malicious website(compromised website or clone website of a well-known website). When the user clicks on the URL, the website will try to install the Malware or run code to gather information about the device. |
| OAuth Consent Grant | In this technique, the user will receive an email where a malicious actor has created an Azure Application that asks the target to grant the application permissions over some of the target’s data. Clicking on the URL will activate the application’s consent grant mechanism. |
| How-to Guide | This technique is not an attack, but it is a How-to guide with details about pushing and how to report the messages as pushing. |
Note! All the URLs and Malware used for attack Simulations are not real-time Phishing data. Microsoft developed the URLs, which are documented on the Microsoft learning page.
Launch Attack Simulation from the Microsoft Defender portal
So far, we have discussed Attack Simulation, prerequisites and Social Engineering techniques available in Microsoft Defender Portal. Let’s learn how to create a simulation and assign training to the user if they click on malicious URLs sent as part of the Simulation.
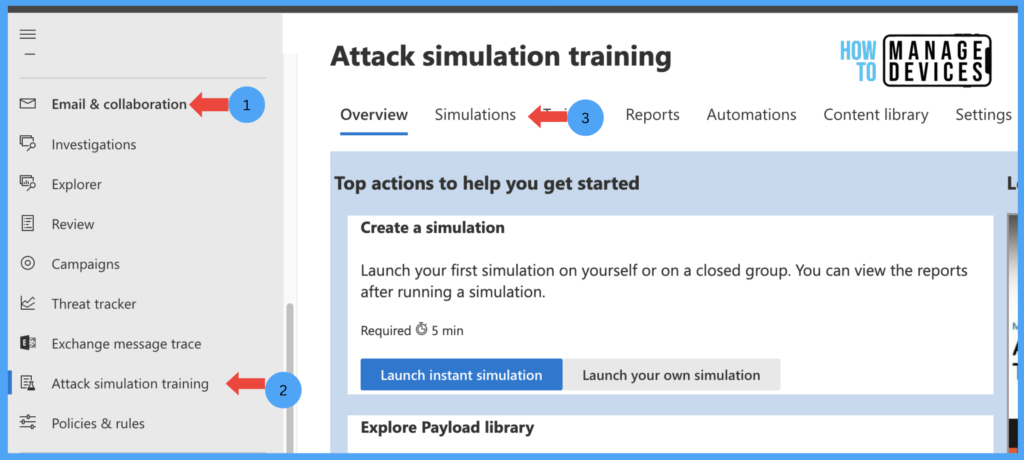
- Log in to the Microsoft 365 Defender portal using the admin account with the appropriate access.
- Click on Email & Collaboration
- Click on Attack Simulation
- Click on the Simulations tab
Under the Simulations tab, we can view all the simulations we created earlier. In our case, we didn’t create any simulation so far, so it is blank. Now click on Launch Simulation.
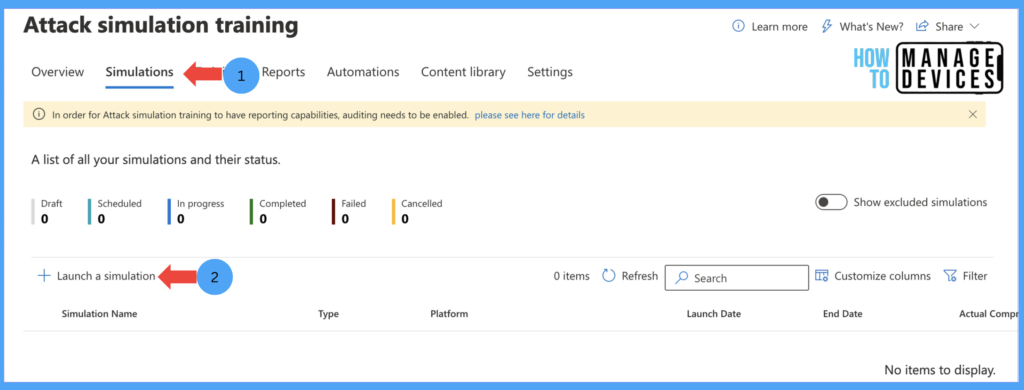
Now, we will be presented with Multiple Social Engineering Techniques, which we have discussed above. For our testing, I have chosen the Credential Harvest technique (you can choose the required technique) and click on Next.
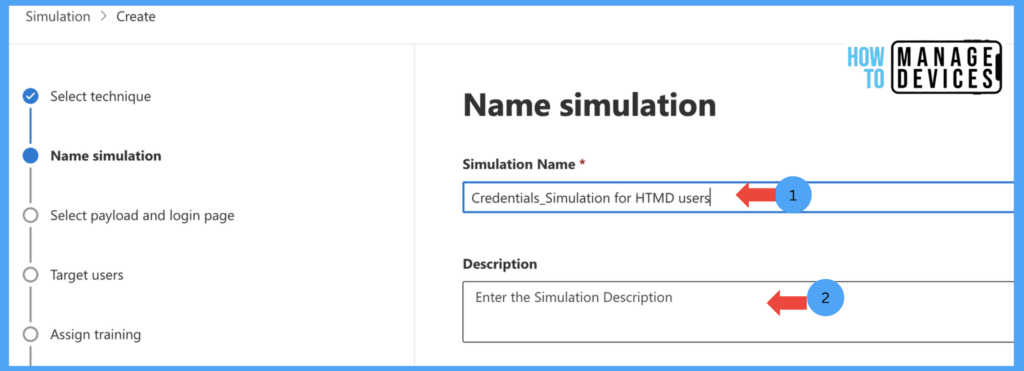
Now, on the Name simulation page, provide the Name and Description for the Simulation and click Next to proceed to Select payload and login page.
On the Select Payload and login page, we must select Payload (Payload –> type of phishing email that should be sent to the end users). By default, Microsoft provides 100s of readily available payloads, which can be used to deploy the Simulation.
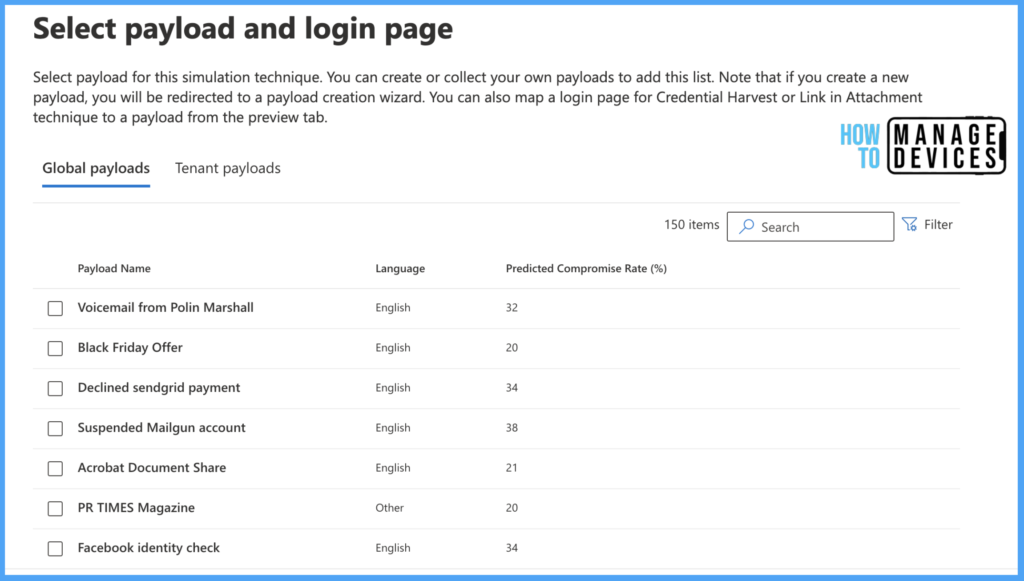
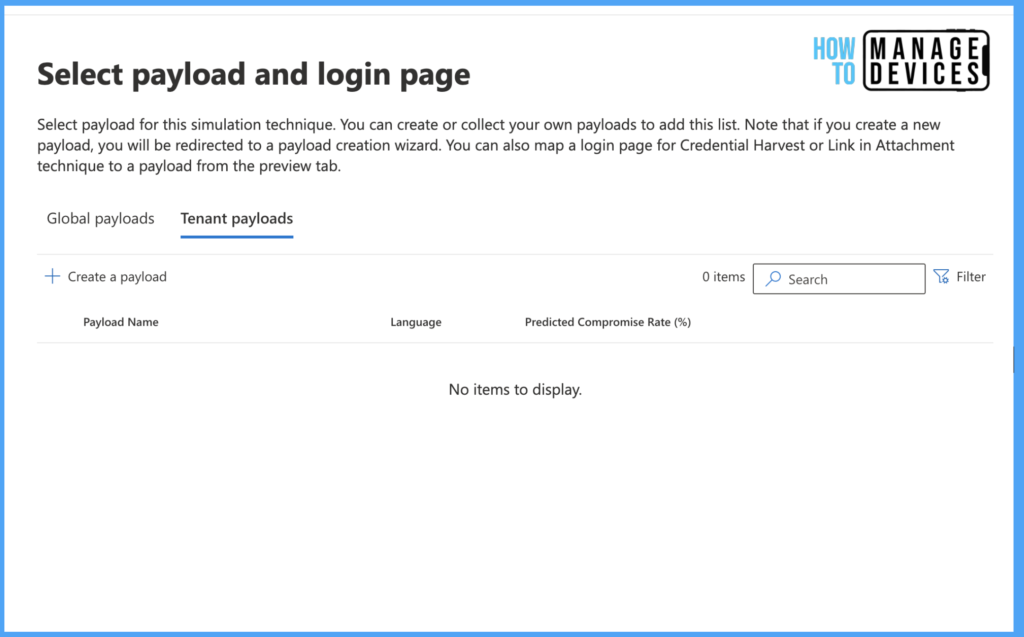
Microsoft also allows us to create an organization Payload per your requirement by clicking Teant Payload and clicking Create a Payload, as shown below.
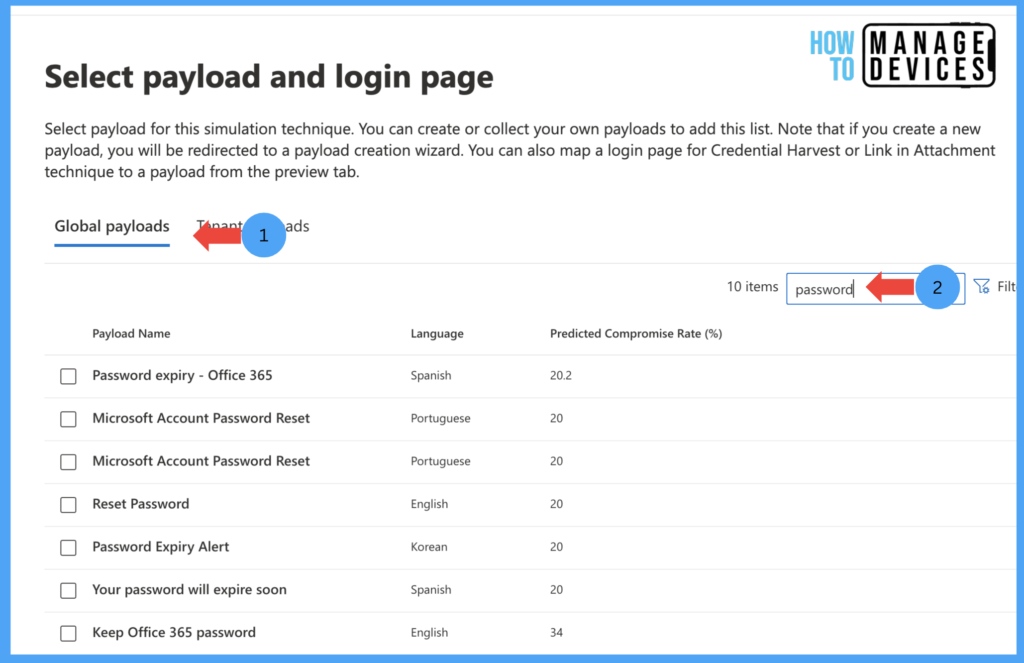
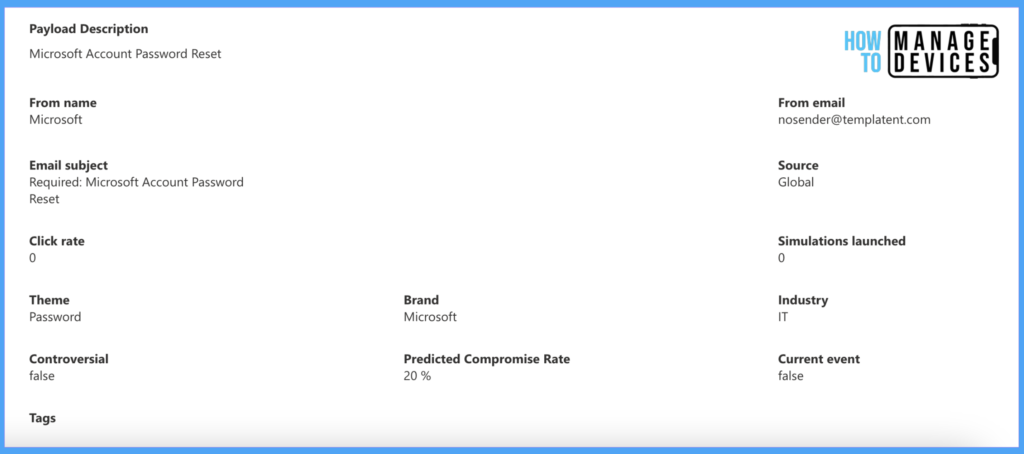
For our discussion, I’m choosing a readily available payload. I searched for the password-related Payload and chose the Microsoft Account Password Reset below. We can view what the Payload looks like
Click on the Payload, and this will open the payload page, where we can view the message that the Payload contains.

We can also view the Simulation’s description, Theme, prediction rate and many details of the Simulation. We can see this in the screenshot below.
Now close the details of Paylod, select the message as per your requirement and click on Next to Target users screen. Here, we can assign the Simulation to all users or a few users.
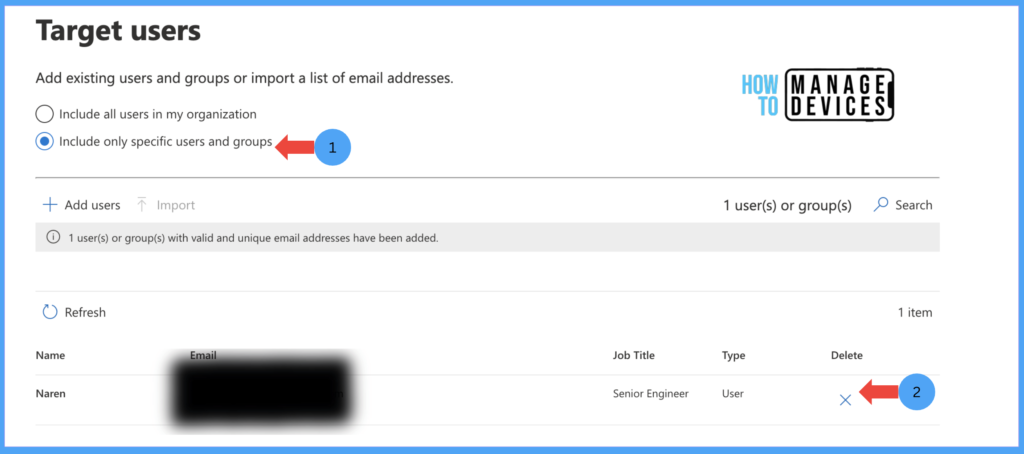
I have selected “Include only specific users and groups” and selected a user. Now click Next to exclude specific users or groups if you want to exclude them from the attack simulation on the Exclude Users page. I don’t have users to Exclude, so I proceeded further without excluding any users.
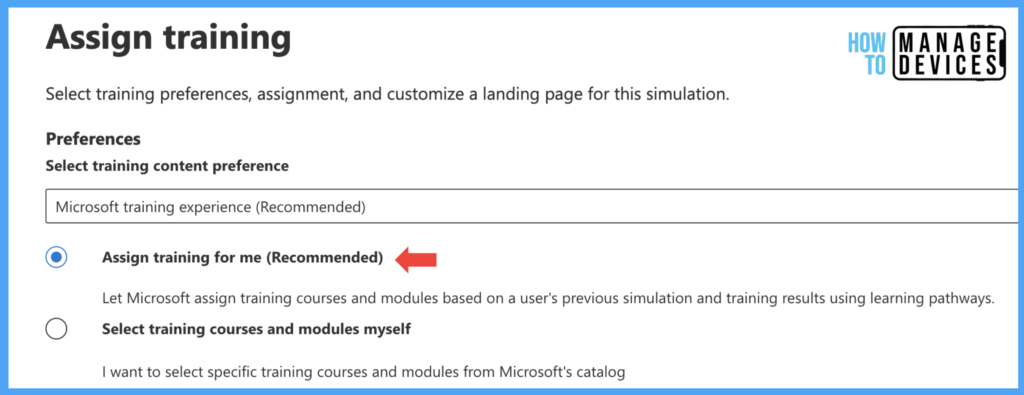
We can educate users by providing training to the end users if they click on URLs. Microsoft provides various pieces of training to provide awareness among users. Now, on the Assign Training page, We need to choose whether Microsoft provides or suggests training based on the simulation type, or we can choose training for end users if they click on the URLs. I have chosen the default value Microsoft suggested training.
We can also choose training modules by ourselves. Just Select Training Courses and Modules Myself. This will enable us to choose the training module and assign it to users if they get phished.
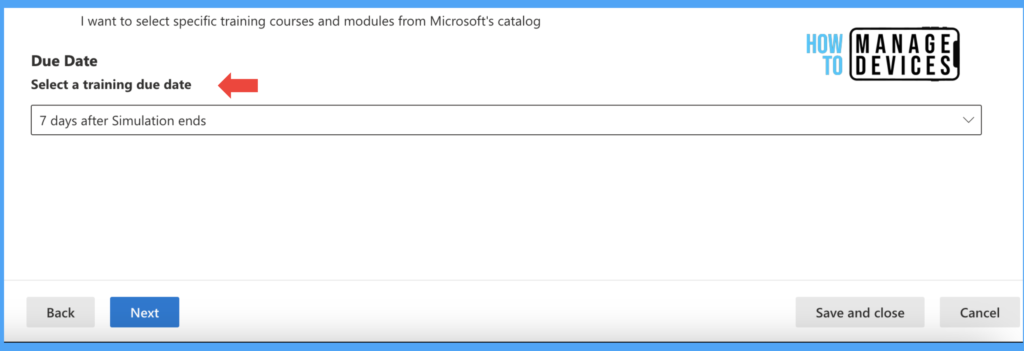
After selecting the training module, we must decide within how many days the user must complete the training under the Due Date section. We can choose 7 days, 15 days and 30 days based on your requirements. Select the days. I have chosen seven days. Now click on Next.
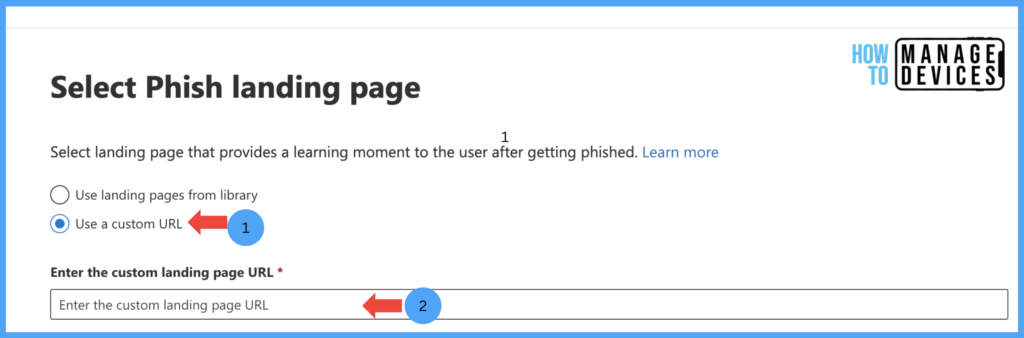
On the Select Phish landing page, we need to choose the landing page where the user will get information about the learning after they get phished. Microsoft provides a few default lading Pages we can choose per our requirements.
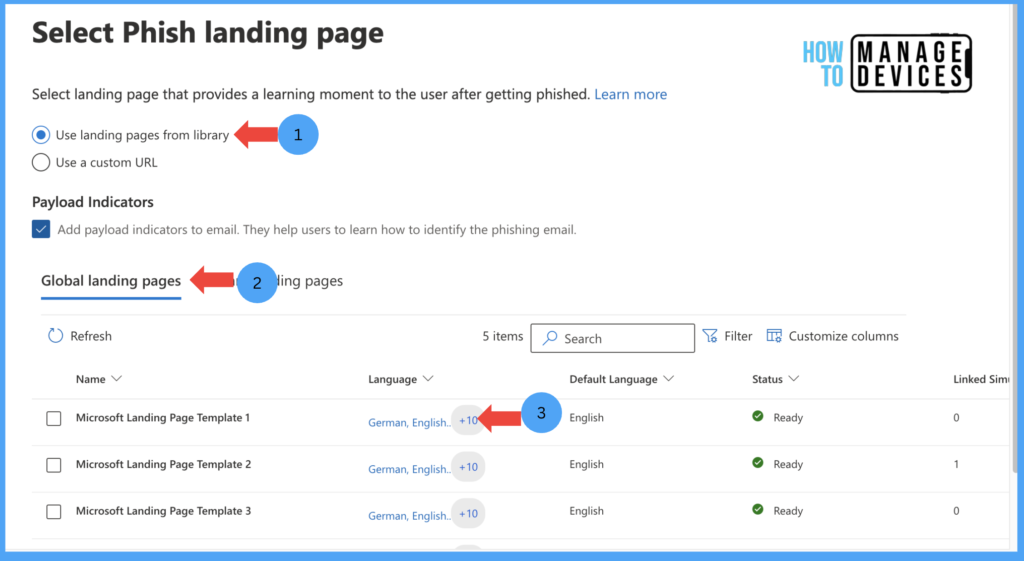
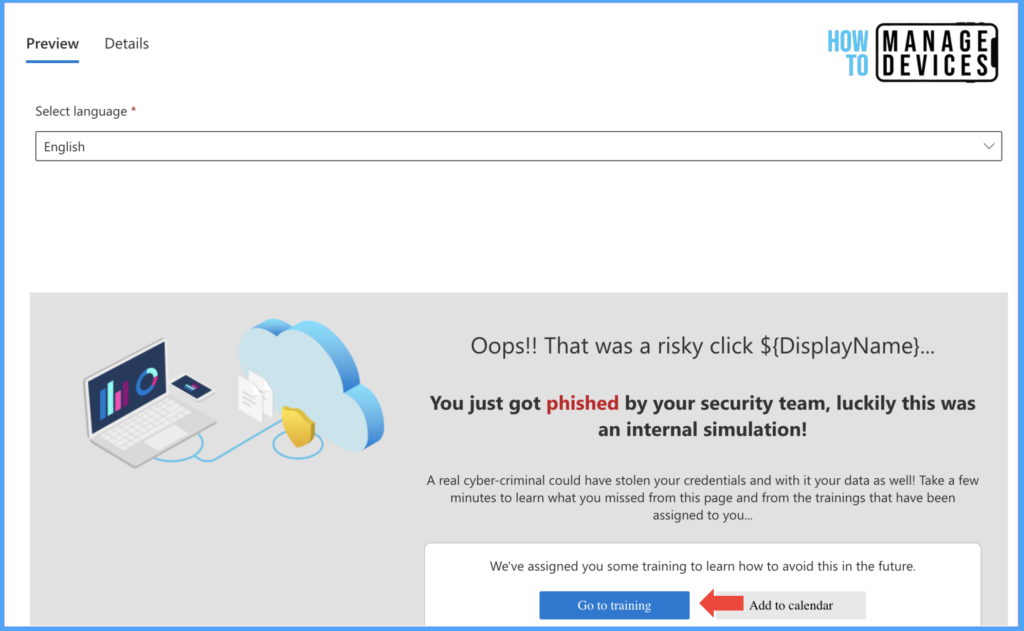
Click on each Landing page to view the landing page and message shown to the end user after they phished. This landing page also includes links to training assigned to them. I have chosen Microsoft Landing Page Template 2 as a Landing page for our discussion.
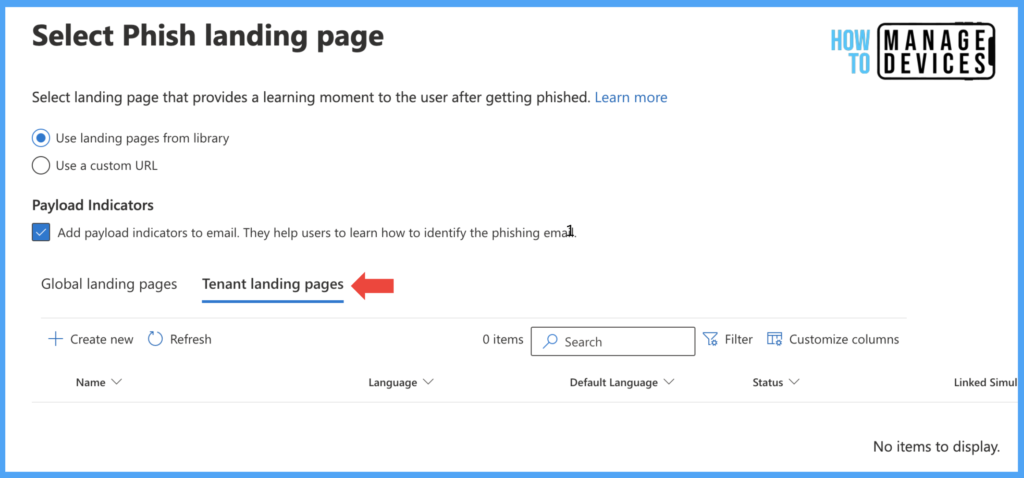
If you don’t like the landing page templates provided by Microsoft, you always have the option to create your organization’s landing page as per your requirement by clicking on Tenant landing pages. I don’t have a landing page for my tenant, so it is blank.
If you didn’t like the landing page options, Microsoft also allows you to redirect users to a custom URL, where you can provide awareness to the users who Attack Simulation phishes. To provide a custom URL, select the “Use a Custome URL” option and provide the URL.
Now click on Next and Select end user notification. In this screen, we need to define Training assignment notifications, Training reminder notifications or Positive reinforcement notifications. As an admin, we have 3 options to choose
- Do not deliver notifications: When we choose the option, users will not receive any Notification about training.
- Microsoft default notification (recommended): We will get options for delivering the notifications when selected.
- Customized end-user notifications: If you have a customized notification, select customized ed-user notifications.
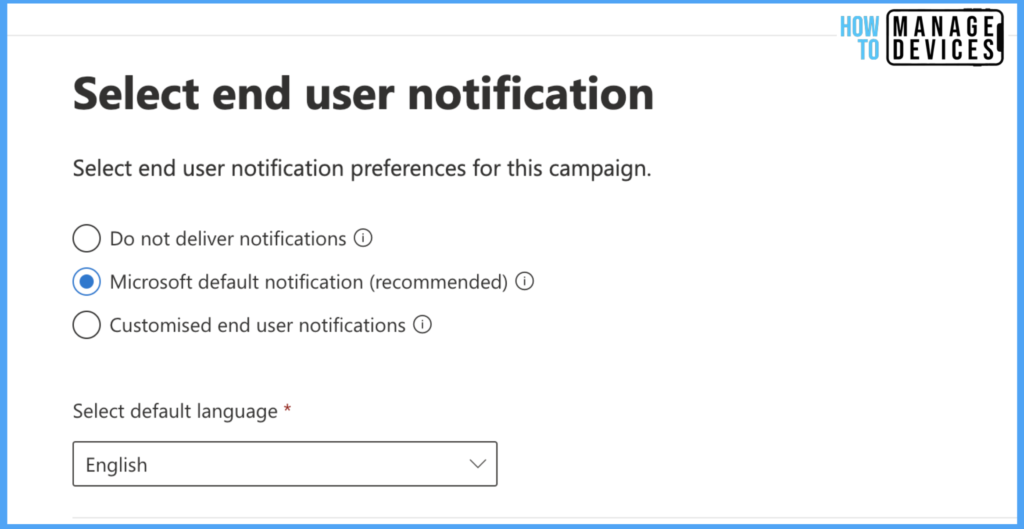
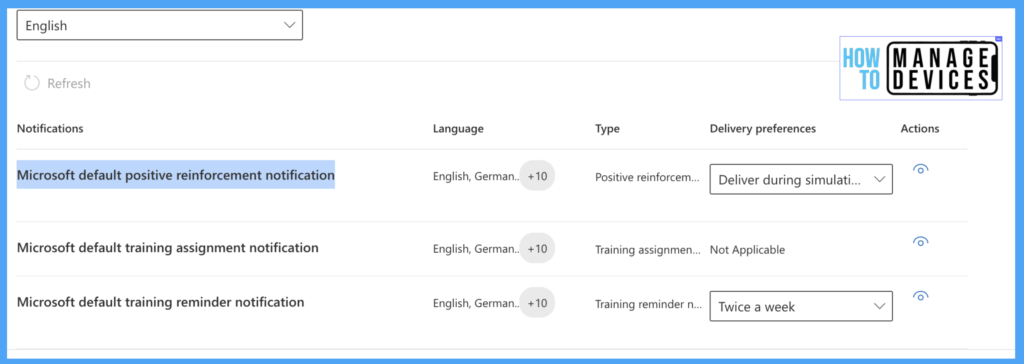
I have selected Microsoft default notification, and Now we need to select when to deliver Positive reinforcement notifications, Training reminder notifications, and training assignment notifications. I have chosen the below values as shown in the screenshot.
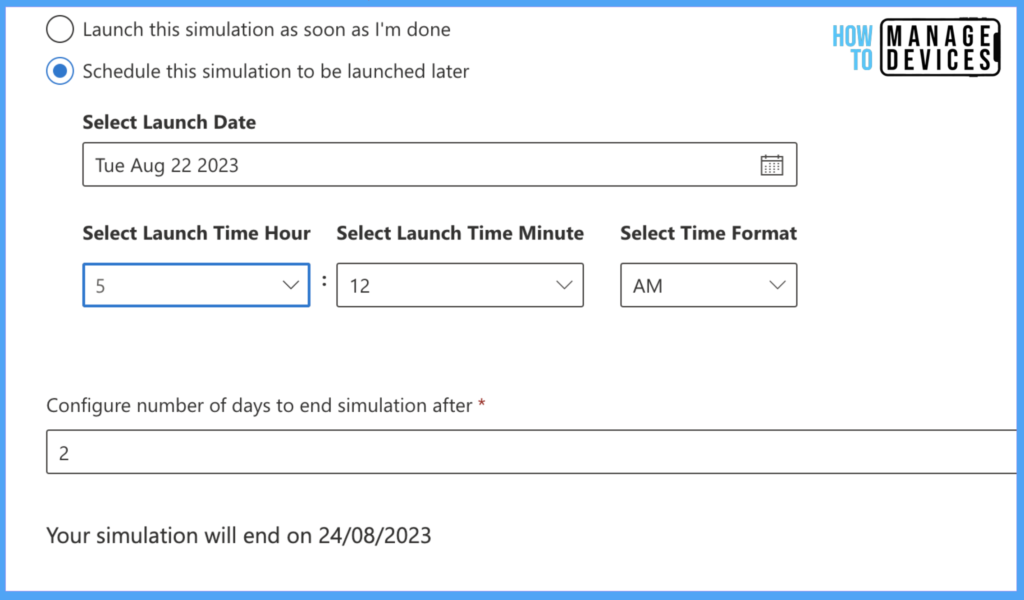
Now click on Next to Launch details screen, where we need to configure when we need to launch this Simulation. We can choose to Launch the Simulation immediately by selecting “Launch this simulation as soon as I’m done” and configure the number of days to end the Simulation after.
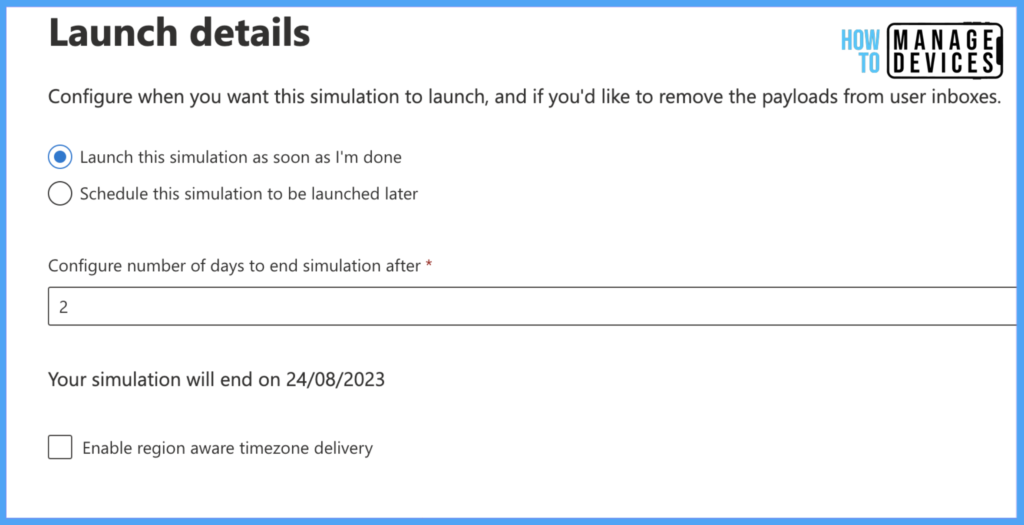
I have chosen two days to end the Simulation after launching it. We can Schedule the Simulation Launch date by selecting “Schedule this simulation to be launched later“. When selected, we must choose Launch Start date, Launch Start Hours, Minutes and Time Format(AM or PM).
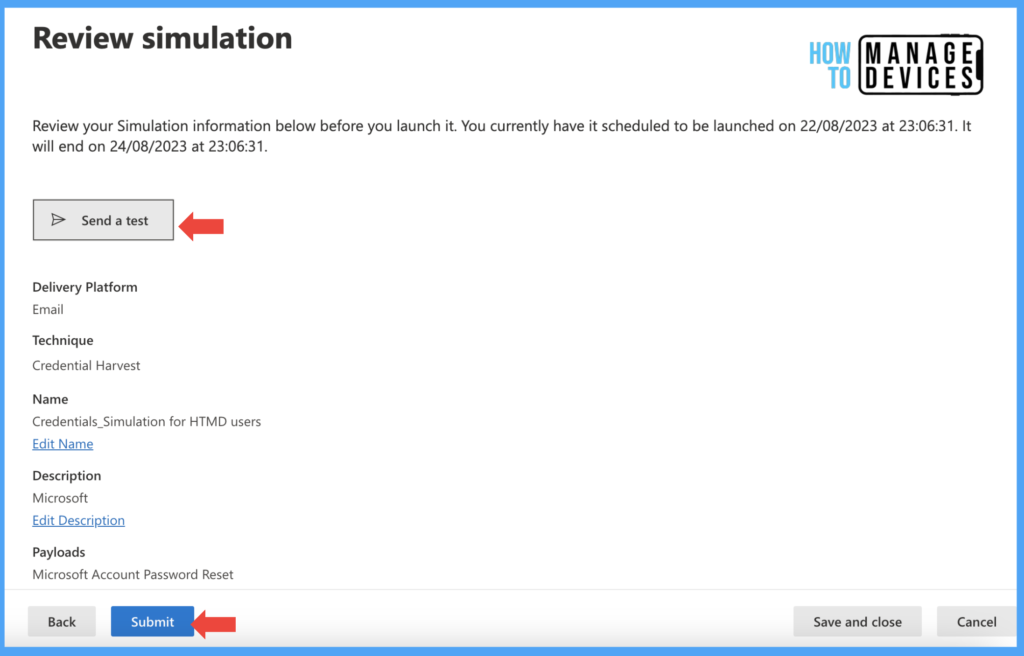
Now, Review the Simulation and click Submit. This will create an Attack Simulation. We can send a test by clicking the Send a test button on Review Simulation before creating the Simulation. This test Simulation will not be captured as it is just a test. After reviewing, Click Submit.
As we have chosen to launch Simulation immediately, users will receive an email notification after some time. The Defender captures and records the user details when the user clicks on the URL, and respective training will be assigned to them.
Conclusion
So this is how we can Launch a quick Attack Simulation within the organization to bring awareness among users related to Phishing Emails. In another post, we will discuss the end-user experience and Insights and monitoring of Attack simulations. Till then, have a happy learning.
Author
About Author – Narendra Kumar Malepati (Naren) has 11+ years of experience in IT, working on different MDM tools. Over the last seven years, Naren has been working on various features of Intune, including migration from different MDMs to Intune. Naren mainly focuses on Android, iOS, and MacOS.

Thanks for sharing, we have tested during implementation Ms Defender, But we should educate the user and continue this practice
Yes, totally agree. We can schedule these kind of Simulations in M365 Defender portal
Is there a way you can setup automated simulations that occur monthly for users?
I’d like to setup a simulation that is ongoing and requires minimal maintenance.
Yes, we can create a automation which can be scheduled Monthly or Weekly for a year under Attack Simulations > Automation