Key Takeaways
- PQC is designed to protect data from future quantum computer attacks
- Cryptographic agility is essential for future-proof security
- Governments are setting early deadlines for PQC implementation
- Hybrid cryptography is the best approach during transition
In this post we are discussing Adoption of Quantum Safe Algorithms and Hybrid Cryptography in Windows. Post Quantum Cryptography is introduced to protect data from future threats caused by powerful quantum computers. Introducing recently standardized quantum safe algorithms, organizations can now begin preparing for this major shift. New algorithms such as ML KEM for key exchange and ML DSA for digital signatures are designed to replace current methods and provide stronger protection.
Table of Contents
Table of Contents
Adoption of Quantum Safe Algorithms and Hybrid Cryptography in Windows
Post-Quantum Cryptography refers to cryptographic algorithms that are secure against both classical and quantum computing attacks. Unlike traditional methods such as RSA and elliptic curve cryptography, PQC is built using complex mathematical problems that quantum computers cannot easily solve.
- Advancing Windows 11 Security with In-Memory Patching and Zero Trust DNS
- 8 Ways to Know Security Identifier SID of User in Windows 11
- TPM 2.0 Transition to Windows 11 For Better Security
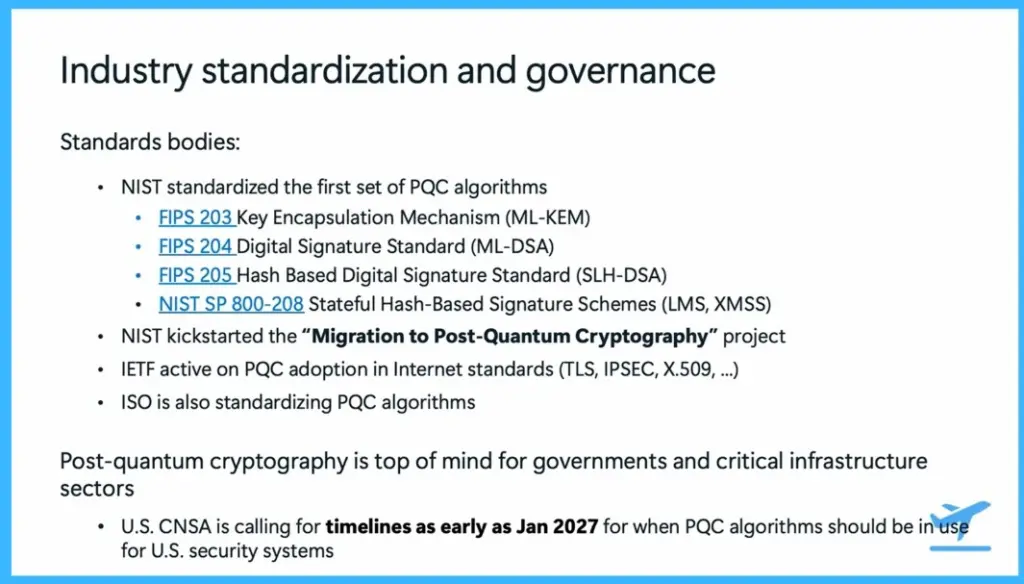
Industry Standardization and Governance
Post Quantum Cryptography is being actively standardized across the world. The National Institute of Standards and Technology has released the first set of PQC standards, including ML KEM for key exchange, ML DSA for digital signatures, and SLH DSA for hash-based signatures. It has also introduced stateful hash-based signature schemes like LMS and XMSS.
In addition, global organizations such as the Internet Engineering Task Force and ISO are working to include PQC in internet protocols and security standards. Governments are taking this seriously, with the National Security Agency setting timelines as early as 2027 for adopting PQC in security systems. Standards bodies:
- NIST standardized the first set of PQC algorithms
- FIPS 203 Key Encapsulation Mechanism (ML-KEM)
- FIPS 204 Digital Signature Standard (ML-DSA)
- FIPS 205 Hash Based Digital Signature Standard (SLH-DSA)
- NIST SP 800-208 Stateful Hash-Based Signature Schemes (LMS, XMSS)
- NIST kickstarted the “Migration to Post-Quantum Cryptography” project
- IETF active on PQC adoption in Internet standards (TLS, IPSEC, X.509, … )
- ISO is also standardizing PQC algorithms
- NIST kickstarted the “Migration to Post-Quantum Cryptography” project
- IETF active on PQC adoption in Internet standards (TLS, IPSEC, X.509, … )
- ISO is also standardizing PQC algorithms
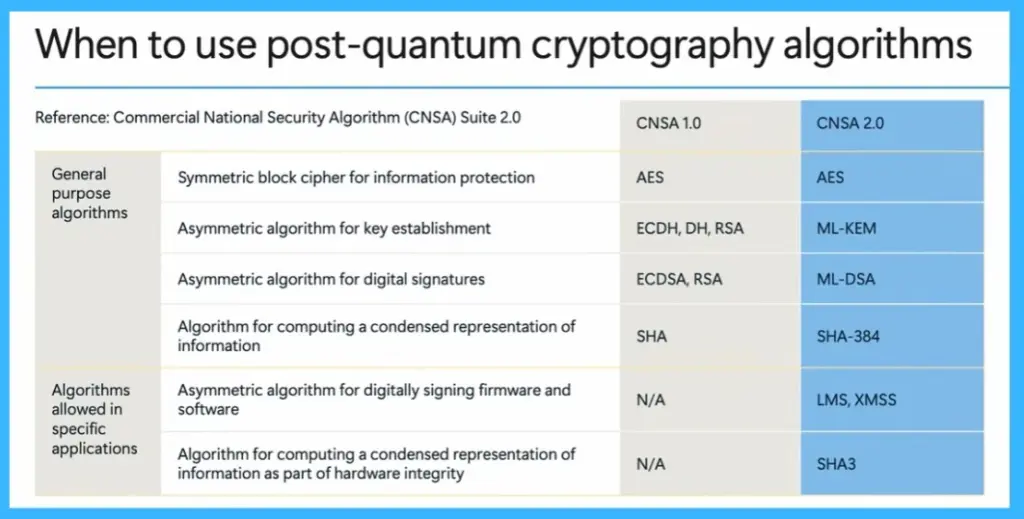
When to Use Post Quantum Cryptography Algorithms
The transition to PQC involves replacing or upgrading existing cryptographic methods. Traditional algorithms like RSA, Diffie Hellman, and elliptic curve cryptography are being replaced with ML KEM for secure key exchange and ML DSA for digital signatures. Some algorithms like AES will continue to be used, while hashing methods are being strengthened to SHA 384 and SHA. New algorithms like LMS and XMSS are introduced for specific use cases such as firmware and software signing. This shows a clear shift toward quantum safe security.
| Category | Description | CNSA 1.0 | CNSA 2.0 |
|---|---|---|---|
| General | Symmetric block cipher for information protection | AES | AES |
| General | Asymmetric algorithm for key establishment | ECDH, DH, RSA | ML-KEM |
| General | Asymmetric algorithm for digital signatures | ECDSA, RSA | ML-DSA |
| General | Algorithm for computing a condensed representation of information | SHA | SHA-384 |
| Specific applications | Asymmetric algorithm for digitally signing firmware and software | N/A | LMS, XMSS |
| Specific applications | Algorithm for computing a condensed representation of information as part of hardware integrity | N/A | SHA3 |
When to use Post Quantum Cryptography Algorithms
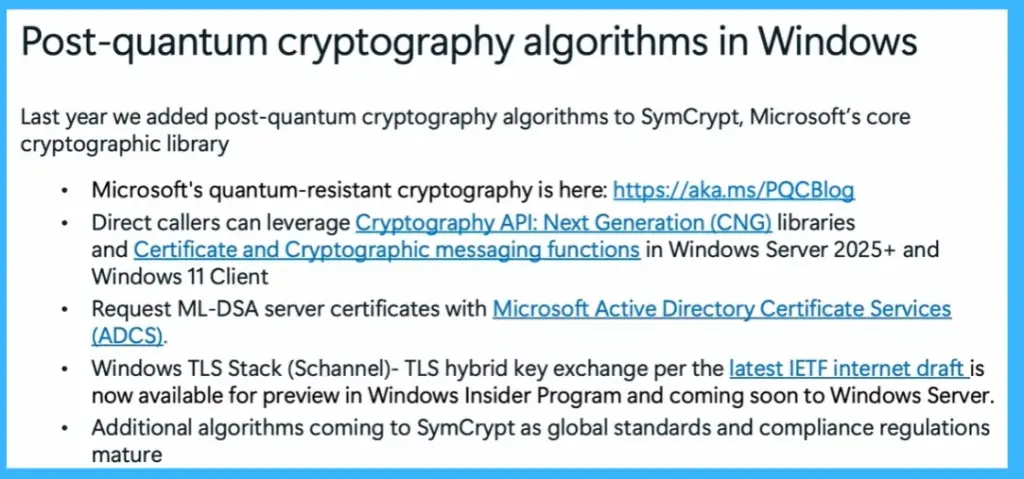
Post Quantum Cryptography is now available in Windows, making it ready for real world use. Microsoft has added PQC algorithms like ML KEM, ML DSA, LMS, and XMSS into its core cryptographic library. Developers can use these through Cryptography API Next Generation and certificate services. Windows also supports hybrid TLS, combining traditional and PQC algorithms for better security. These features are available in Windows 11 and Windows Server 2025, allowing early adoption of quantum safe technologies.
Last year we added post-quantum cryptography algorithms to SymCrypt, Microsoft’s core cryptographic library.
- Microsoft’s quantum-resistant cryptography is here: https://aka.ms/PQCBlog
- Direct callers can leverage Cryptography API: Next Generation (CNG) libraries and Certificate and Cryptographic messaging functions in Windows Server 2025+ and Windows 11 Client
- Request ML-DSA server certificates with Microsoft Active Directory Certificate Services
- (ADCS).
- Windows TLS Stack (Schannel)- TLS hybrid key exchange per the latest IETF internet draft is now available for preview in Windows Insider Program and coming soon to Windows Server.
- Additional algorithms coming to SymCrypt as global standards and compliance regulations mature.
End to End Security from Hardware to Cloud
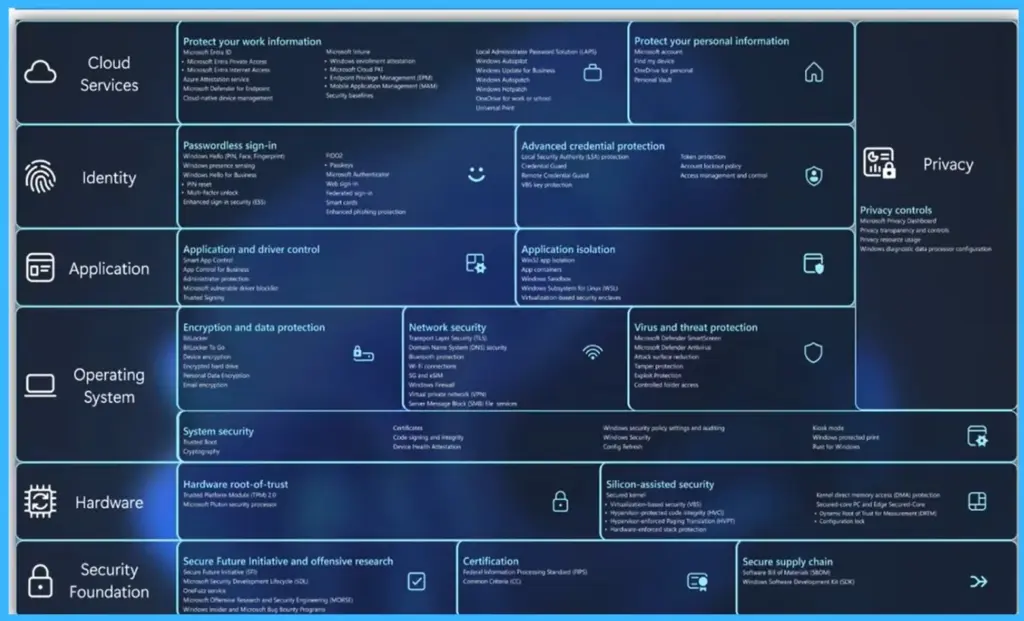
Microsoft follows a complete security approach that covers all layers from hardware to cloud. At the hardware level, technologies like TPM and Pluton provide a strong root of trust. The operating system includes security features like secure boot, virtualization-based security, and encryption tools. Applications are protected using network security protocols like TLS and IPsec. Identity and cloud services ensure secure access through solutions like Windows Hello and Entra ID.
- This layered security model ensures protection across devices, applications, and cloud environments while preparing for future quantum threats.
Need Further Assistance or Have Technical Questions?
Join the LinkedIn Page and Telegram group to get the latest step-by-step guides and news updates. Join our Meetup Page to participate in User group meetings. Also, join the WhatsApp Community and the Whatsapp channel to get the latest news on Microsoft Technologies. We are there on Reddit as well.
Author
Anoop C Nair is a Workplace Technology solution architect with 25+ years of experience. Microsoft Certified Trainer. Microsoft MVP from 2015 onwards for consecutive 11+ years! He is a blogger, Speaker, and Founder of HTMD Community and HTMD Conference. His main focus is on Device Management technologies like Intune, Windows, and Cloud PC. He writes about technologies like Intune, SCCM, Windows, Cloud PC, Entra, and Microsoft Security.