Let’s learn how to create custom compliance policies for Linux devices in Intune. IT admins can use custom compliance policies in Intune for creating Bash scripts that evaluate the most important attributes of Linux endpoints for the organization.
By creating custom compliance policies for Linux devices in Intune, organizations can ensure that their devices are secure and meet their specific compliance requirements.
Custom compliance policies for Intune offer a number of benefits to organizations that want to ensure their devices meet their specific security and compliance requirements.
These policies enable organizations to enforce stronger device security measures, such as password complexity and encryption requirements. This reduces the risk of data breaches and other security incidents.
Once you have created a custom compliance policy for your Linux devices, you can monitor compliance and take action if devices are out of compliance. For example, you can send notifications to users or block access to company resources until the device is brought back into compliance.
Prerequisites for using Custom Compliance Policies and Settings for Linux
Here are the prerequisites for using custom compliance policies and settings for Linux in Intune, You can refer to the Linux Intune sample scripts and custom configuration profiles repository. There are various situations in which a custom profile or shell script may be needed to complete a particular task.
- Discovery script – A POSIX-compliant shell script for Linux that you create. The script runs on a device to discover the custom settings defined in your JSON file. The script returns the configuration value of those settings to Intune.
- JSON file – The JSON file defines the custom settings and the value to be considered compliant and can contain messages for users on how to restore the device to compliance with the setting.
Custom Compliance Discovery Scripts
Before deploying your script in production, test it in an isolated environment to ensure the syntax you use behaves as expected. Here are the steps to create custom compliance policies for Linux devices in Intune:
- Sign in to the Microsoft Intune admin center https://intune.microsoft.com/.
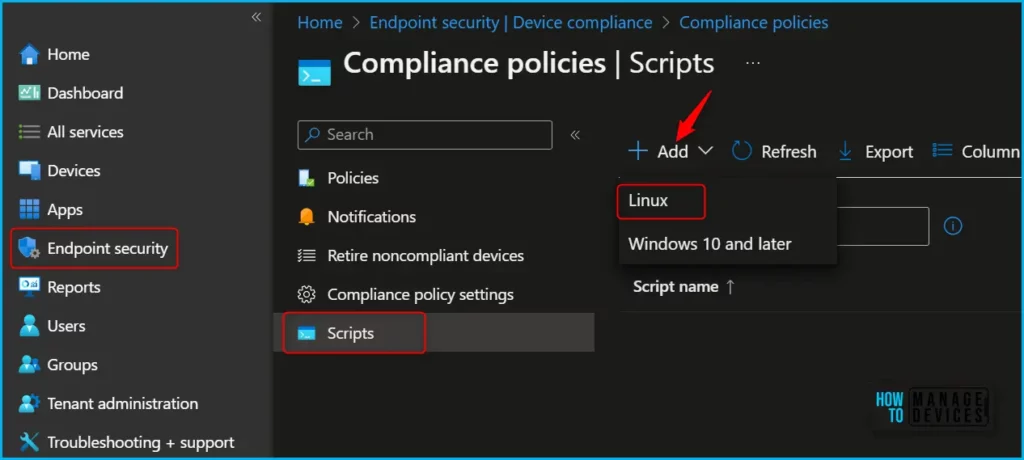
- Next, the four steps lead you to access complication policies creation, Navigate to the Endpoint security > Device compliance > Scripts > Add > Choose Linux as your platform.
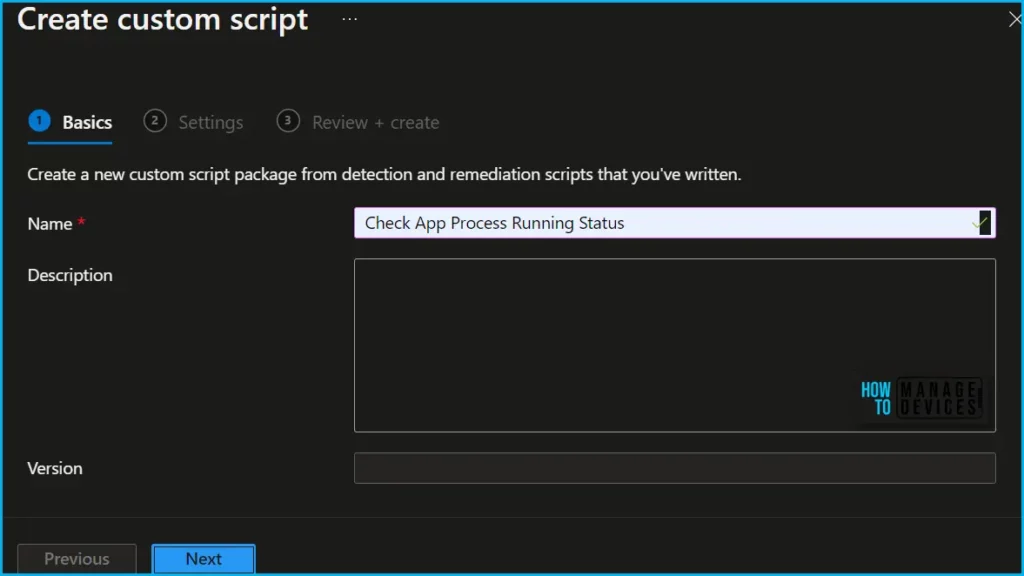
On Basics, provide a Name for the custom script package and click on Next.
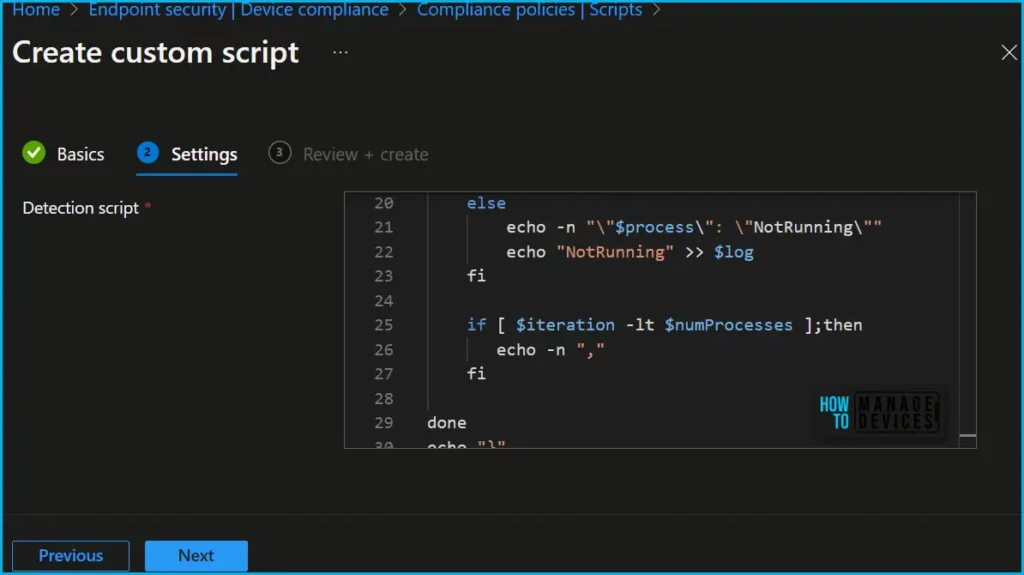
Here you need to upload your script to the Intune admin center before you create a compliance policy, The discovery script runs on a device to discover the custom settings defined.
Important! Review your script carefully. Intune doesn’t validate the script for syntax or programmatic errors.
Now in Review + create, review your settings. When you click on Create, your changes are saved.
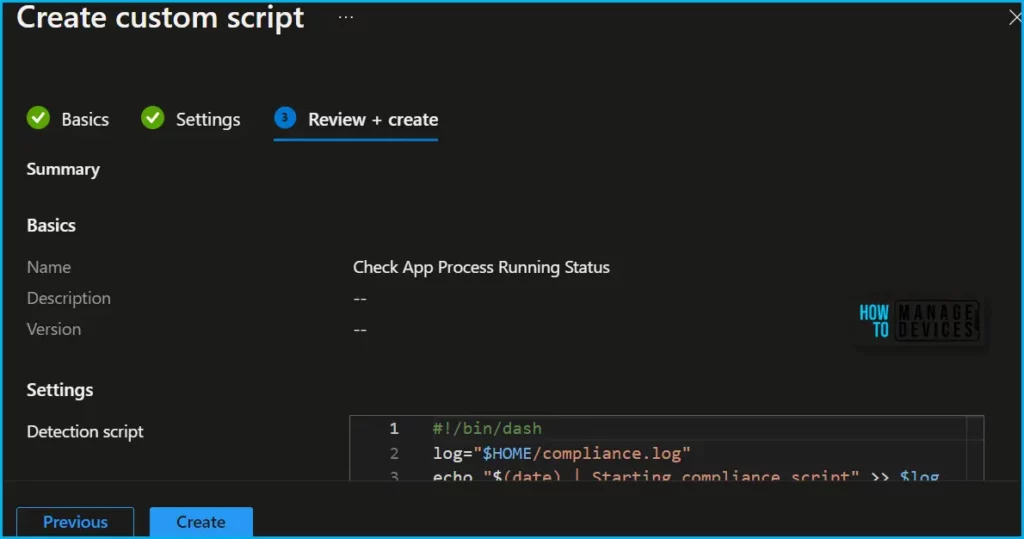
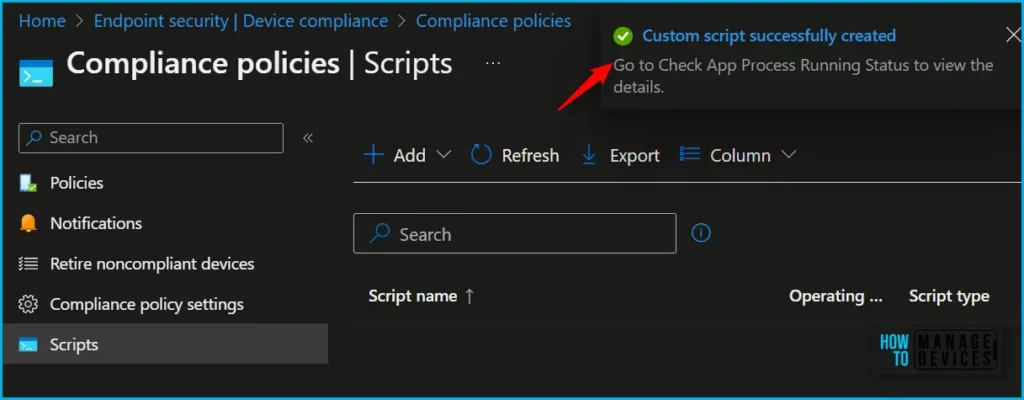
A notification will appear automatically in the top right-hand corner with a message. You can see that the Custom script successfully created. The added script is displayed in the list of Compliance policies scripts and is available to select when configuring compliance policies.
Create Custom Compliance Policy for Linux in Intune
Ensure that you have fulfilled the necessary requirements before creating a policy containing custom settings. These requirements consist of uploading a relevant discovery script to Intune and preparing a JSON file that will be added during the policy creation procedure.
Before you create a Linux compliance policy in Intune, you must enroll the Linux devices in the Intune tenant. Let’s check how you can create compliance policy in Intune for Linux devices.
- Sign in to the Microsoft Intune admin center https://intune.microsoft.com.
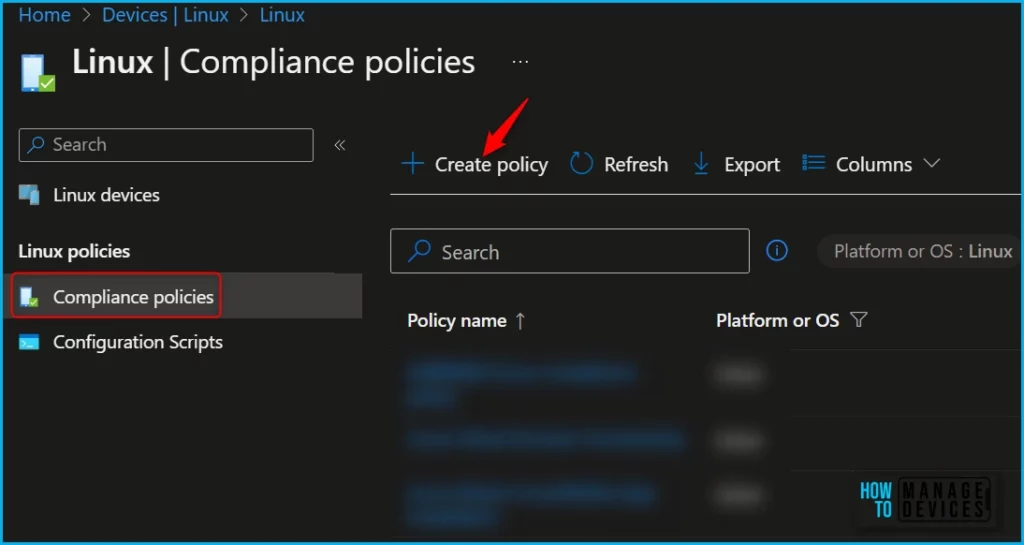
- Select Devices > Linux > Compliance policies > Create Policy.
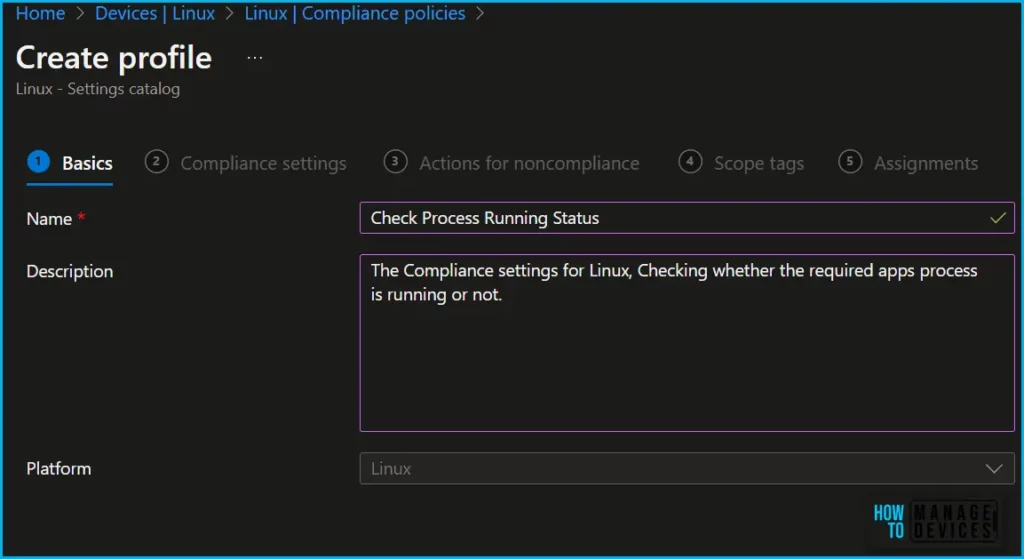
On the Basics tab, specify a Name that helps you identify them later. For example, Check App Process Running Status for Linux devices. You can also choose to specify a Description and click on Next.
On the Compliance settings tab, select Add settings. Click on Custom Compliance, Expand the available categories, and configure settings for your policy. The profile type uses settings from the Settings catalog.
- Require Custom Compliance
- Select your discovery script
- Select your rules file
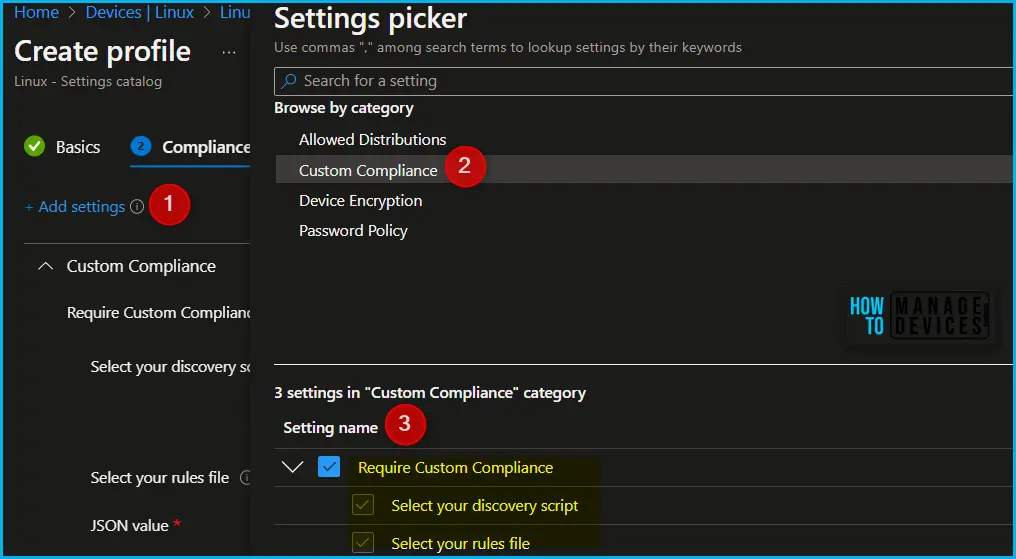
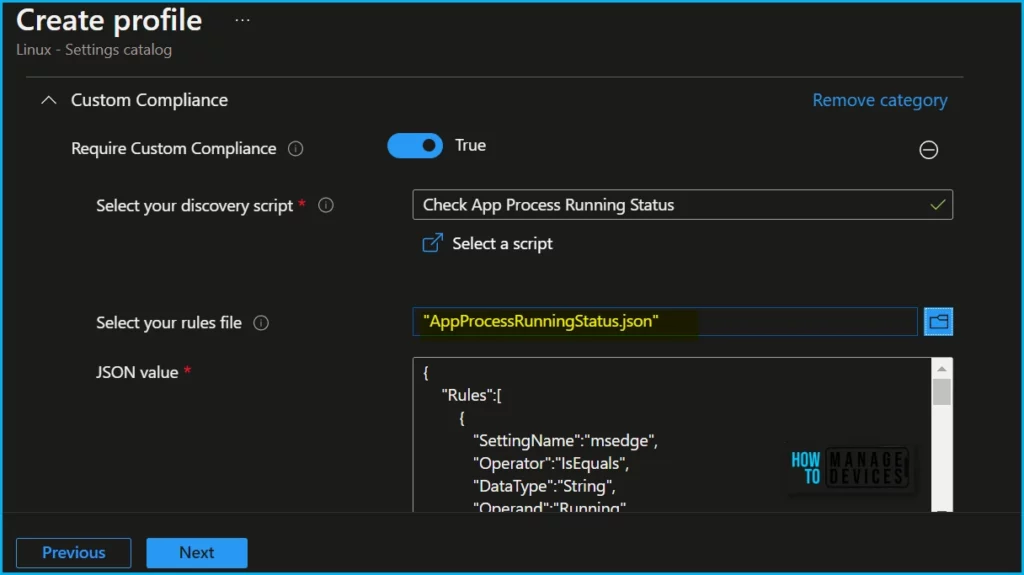
In the Compliance settings, select the toggle for Require Custom Compliance to change it to True.
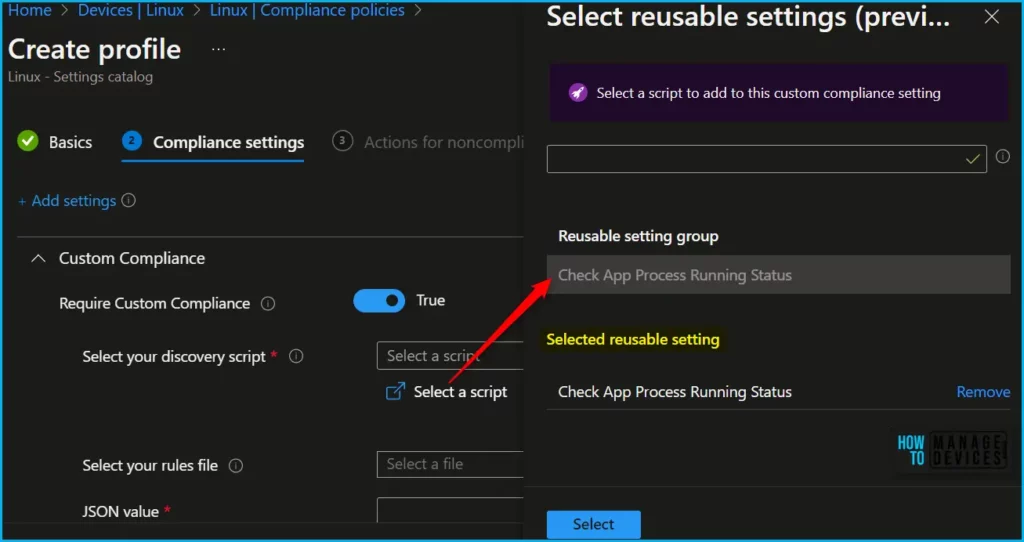
Select your discovery script, select Set reusable settings, and then specify a script that’s been previously added to the Intune. This script must have been uploaded before you begin to create the policy.
Select your rules file, select the folder icon, and then locate and add the JSON file for Linux that you want to use with this policy.
Once you input the JSON, it undergoes validation, and any issues are displayed for you to address. After successful validation of the JSON content, the rules contained within the JSON are presented in a tabular format. The sample scripts are collected from Custom Compliance/Running Process Example/ CheckForProcessRunning.json
{
"Rules":[
{
"SettingName":"msedge",
"Operator":"IsEquals",
"DataType":"String",
"Operand":"Running",
"MoreInfoUrl":"https://www.microsoftedgeinsider.com/en-us/download/?platform=linux",
"RemediationStrings":[
{
"Language": "en_US",
"Title": "Microsoft Edge Not Running",
"Description": "Please ensure that Microsoft Edge is running at all times"
}
]
},
]
}
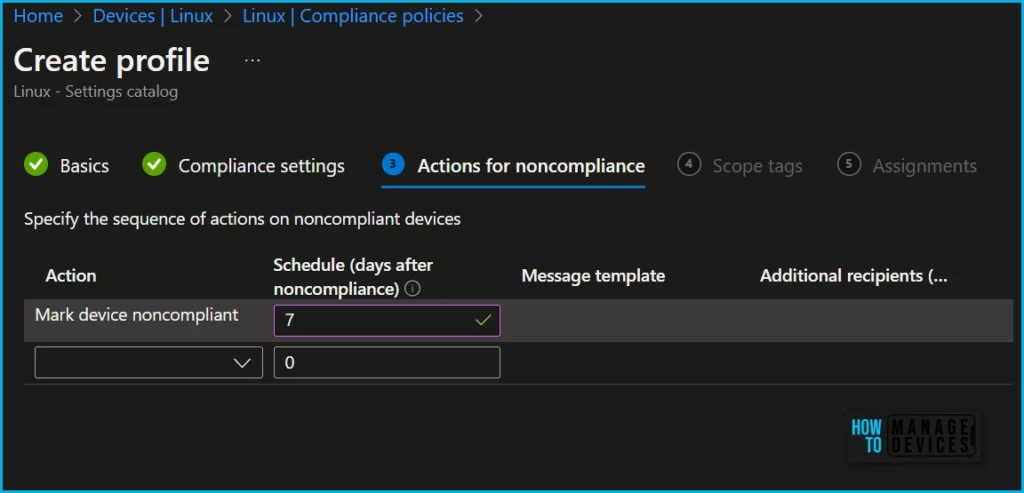
Actions of Noncompliance Policy, Here you can specify the sequence of actions on noncompliant devices. The default schedule is set to Zero (0). Here I set up, Mark device noncompliance, and click Next.
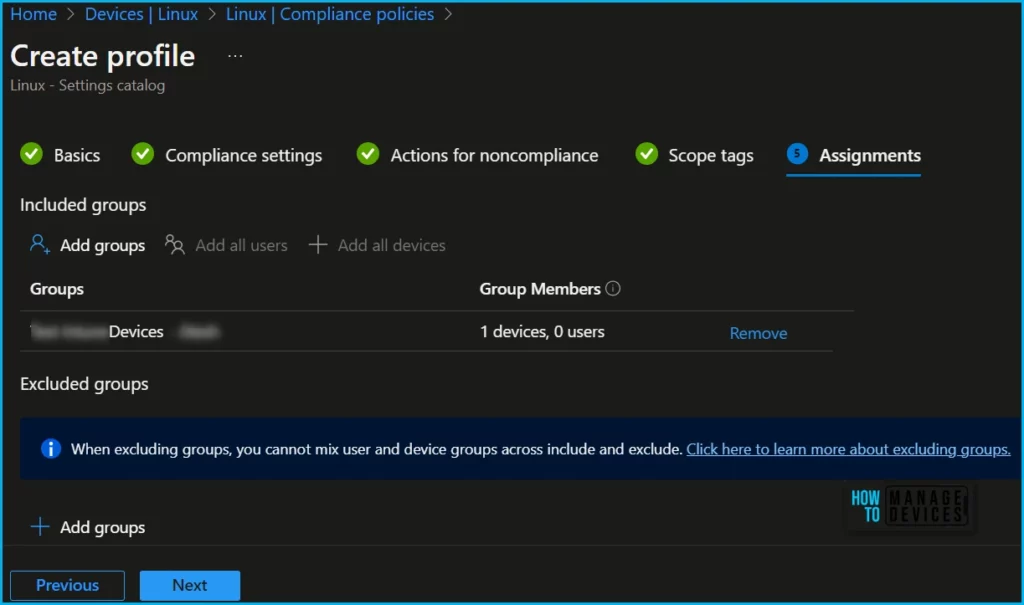
To filter the profile to specific IT groups, you can assign a tag in Scope tags. If necessary, add scope tags and proceed to the next step.
Under Assignments, click “Add groups” in “Included groups,” then select one or more groups to include by choosing “Select groups.” Finally, click “Next” to proceed.
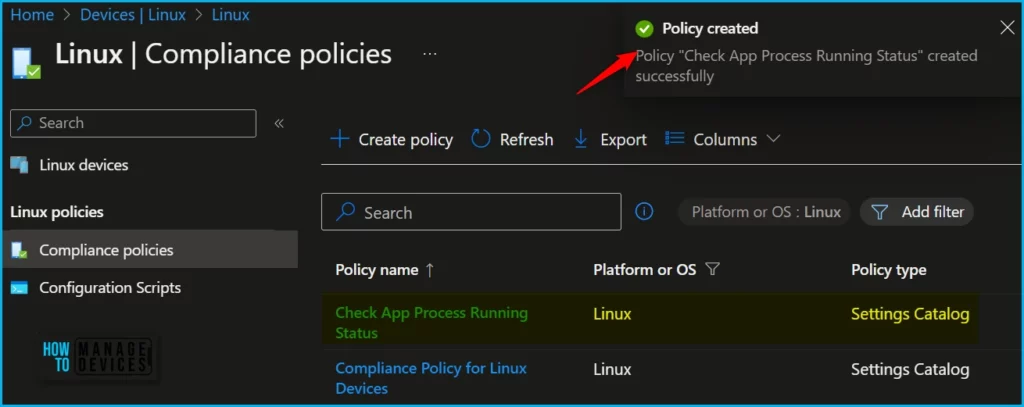
A notification will appear automatically in the top right-hand corner with a message. You can see that the Policy Check App Process Running Status successfully created. The policy is displayed in the list of Compliance policies.
Once a policy is assigned to a device, custom compliance can make it successful by ensuring that the device adheres to the requirements outlined in the policy. This involves a few key steps:
- Custom compliance should monitor the device to ensure that it is meeting the requirements outlined in the policy.
- If the device is found to be non-compliant, custom compliance should take steps to remediate the issue. This may involve updating the device configuration, installing security patches, or taking other actions to bring the device back into compliance.
Author
About Author – Jitesh, Microsoft MVP, has over six years of working experience in the IT Industry. He writes and shares his experiences related to Microsoft device management technologies and IT Infrastructure management. His primary focus is Windows 10/11 Deployment solution with Configuration Manager, Microsoft Deployment Toolkit (MDT), and Microsoft Intune.


