Today, I will discuss the Device Configuration Workload Switch ConfigMgr Co-Management | SCCM. Let’s first examine the Device Configuration Workload Switch experience with Windows 10 Co-Management.
The device configuration workload includes settings you manage for Windows 10 devices in your organization.
When you Switch this workload, the other two workloads, Resource Access and Endpoint Protection, are automatically moved.
In the previous post, Co-Management Workload Client Apps, I shared my experience switching client app workloads. In the same post, you can learn more about co-management and Microsoft’s strategy toward modern device management.
Table of Contents
Device Configuration Workload – Complex?
Do you think switching to Intune for the Device Configuration Workload is pretty complex because of the components involved? Before switching to Intune or Pilot Intune, let’s understand the components or sub-workloads you must consider.
- Configuration Manager Technical Preview 2110 New Features
- How to Setup SCCM Co-Management to Offload Workloads to Intune
- SCCM TP 1806 – Upgrade – Offload Office 365 Workload
- SCCM 1805 ConfigMgr Generated Certificate for HTTP Communication
- SCCM Technical Preview 2311 New Features Improvements
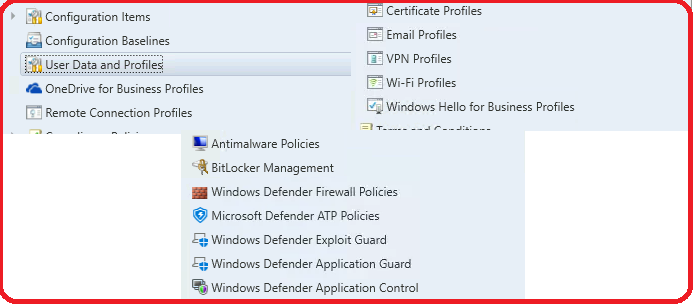
The following is the high-level view of Device Configuration workloads:
| Device Configuration | Resource Access | Endpoint Protection |
|---|---|---|
| > Configuration > Items > Baselines | > VPN > Wi-Fi >Certificate | > WIP – Windows Information Protection (even though this is not part of endpoint protection) > Windows Defender Antimalware > Windows Defender Application Guard > Windows Defender Firewall > Windows Defender SmartScreen > Windows Encryption BitLocker management > Windows Defender Exploit Guard > Windows Defender Application Control > Windows Defender Security Center > Windows Defender Advanced Threat Protection (now known as Microsoft Defender Threat Protection) |
Is the device Configuration Workload NOT Switched to Intune?
In a scenario where the device is already enrolled to Intune using group policy, what if the device workload is not switched to Intune? Per my testing, the Intune policies deployment won’t work on the Windows 10 co-managed device until you switch the device configuration workload to Intune. However, ConfigMgr policy deployments work as expected.
How to Change Co-Management Device Configuration Workload?
Let’s see how to switch the Device Configuration workload to pilot Intune or Intune.
- Navigate to \Administration\Overview\Cloud Services\Co-management
- Click on CoMgmtSettingProd.
- Select the properties option from the ribbon menu.
- Click on the Workloads tab.
- Slide the Device Configuration, Resource Access, and Endpoint Protection switch to Pilot Intune or Intune.
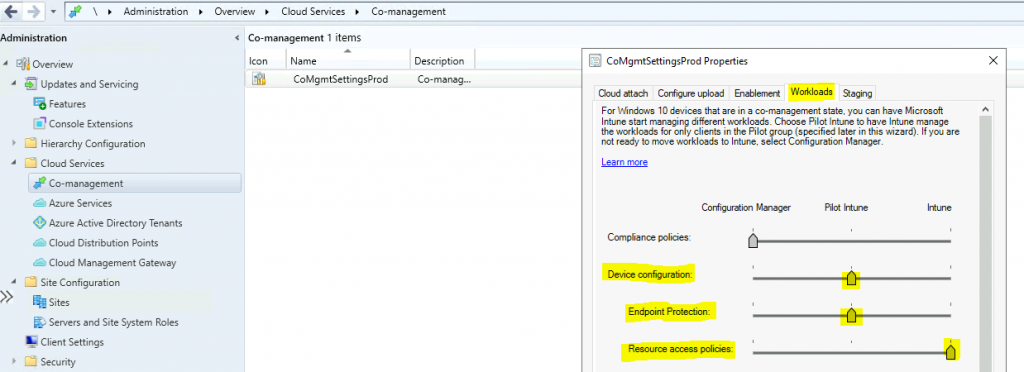
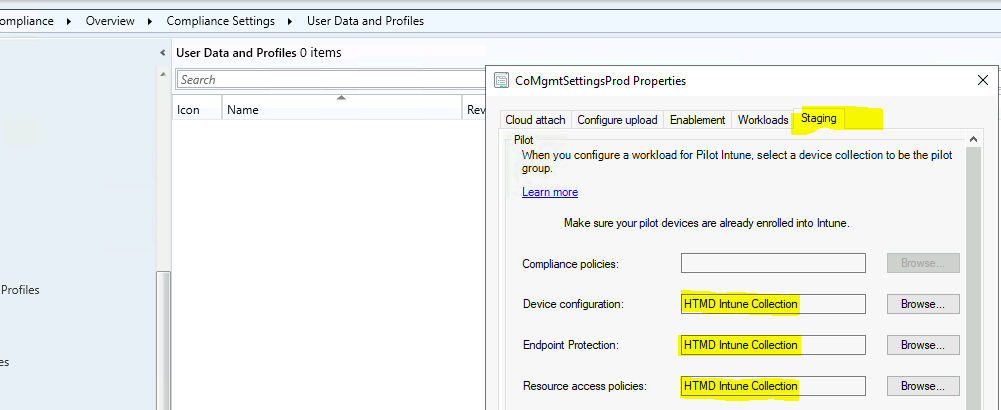
- Click on the Staging tab (Only if you have selected the Pilot Intune option).
- Select the pilot collections for the Device Configuration, Resource Access, and Endpoint Protection workloads.
- Click Apply and OK.
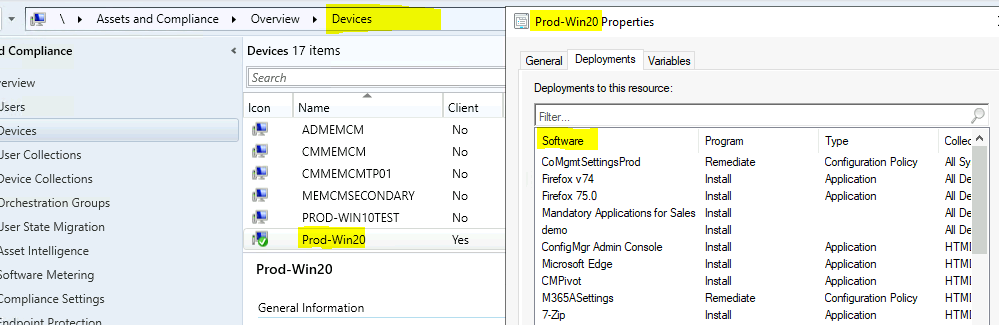
ConfigMgr Deployments
You can check the ConfigMgr (a.k.a. SCCM) deployments from the device properties in the Deployments tab. This helps you get the Configuration policies deployed to Windows 10 devices. I feel the view below could help analyze the ConfigMgr deployment details.
How to Check Co-Management is Enabled
This section helps confirm whether the Windows 10 device is co-managed.
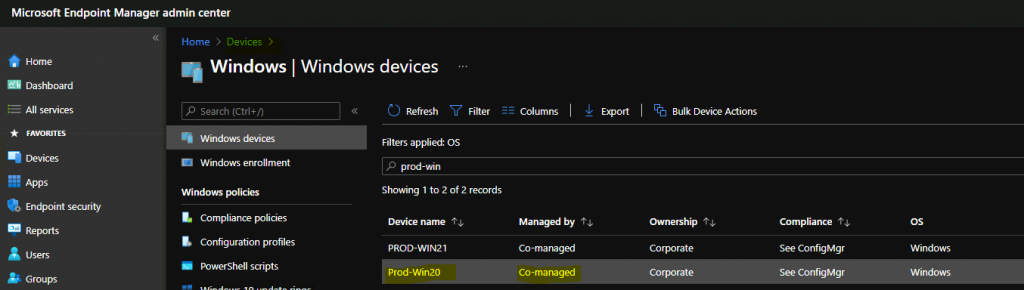
- You can confirm the Windows 10 Client’s co-management status from the Endpoint Manager (a.k.a. Intune) portal: https://endpoint.microsoft.com/.
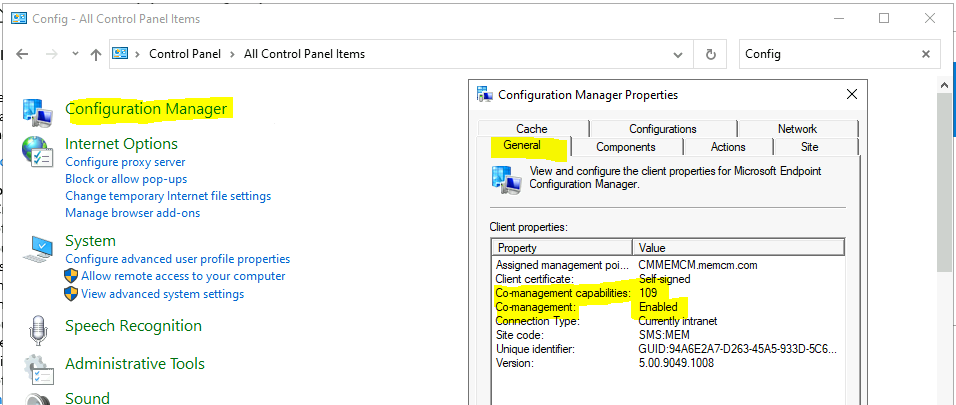
You can also confirm the co-management status from ConfigMgr Applet on Windows 10 devices.
- Co-management = Enabled.
Device Configuration Policy Switch Experience
When you switch device configuration workloads, the SCCM policies stay on the device until the Intune policies overwrite them. The policies can be further deployed only via the Intune management channel.
I have heard requirements for having more granular control over some policies, like Bitlocker management, etc., similar to the control we have with Configuration Baselines explained below.
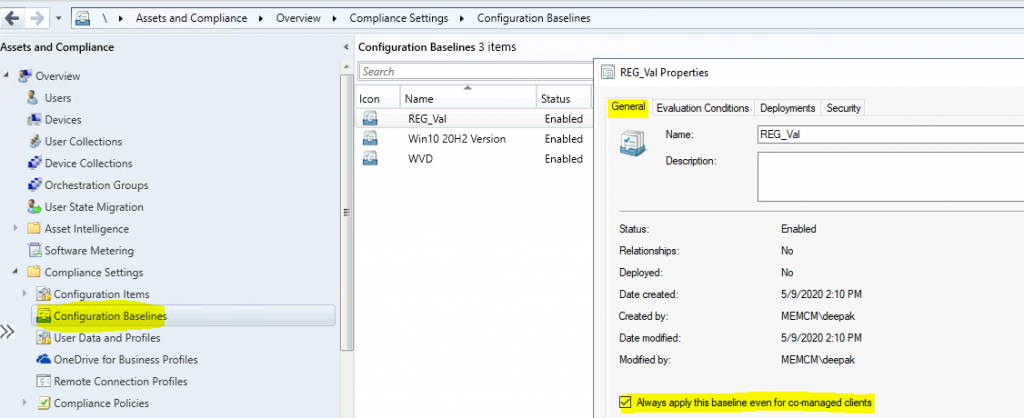
Even though Intune is the device configuration authority, you can still deploy some settings (Configuration Baselines) from SCCM to co-managed devices. When creating the baseline, you can enable the option to always apply it, even for co-managed clients.
Check Intune Policies
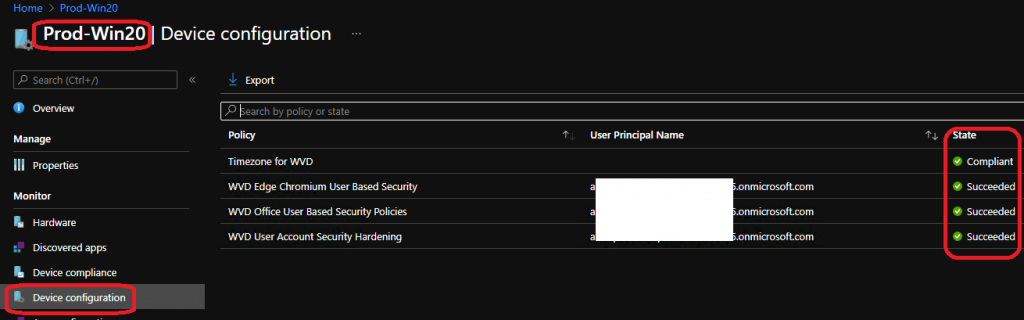
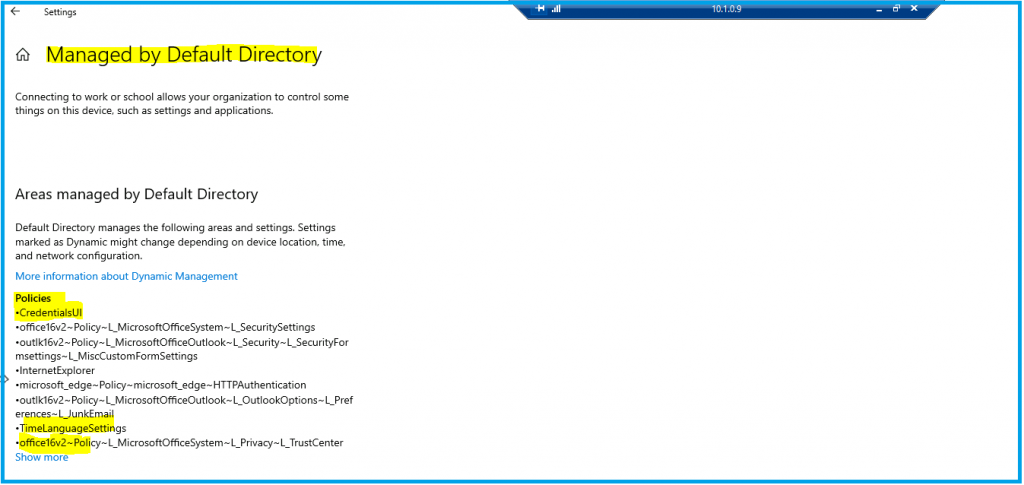
The screenshots below show that you can check whether Intune delivers policies to Windows 10 co-managed devices from the Endpoint Manager (a.k.a. Intune) portal and settings apps.
- A search of the co-managed device on the Endpoint Manager portal (https://endpoint.microsoft.com/).
Let’s head over to the Windows 10 Settings app.
- Navigate to Accounts – Access work or school. (Access resources like email., apps, and the network.)
- Click on Connected Account.
- Click on the Info button.
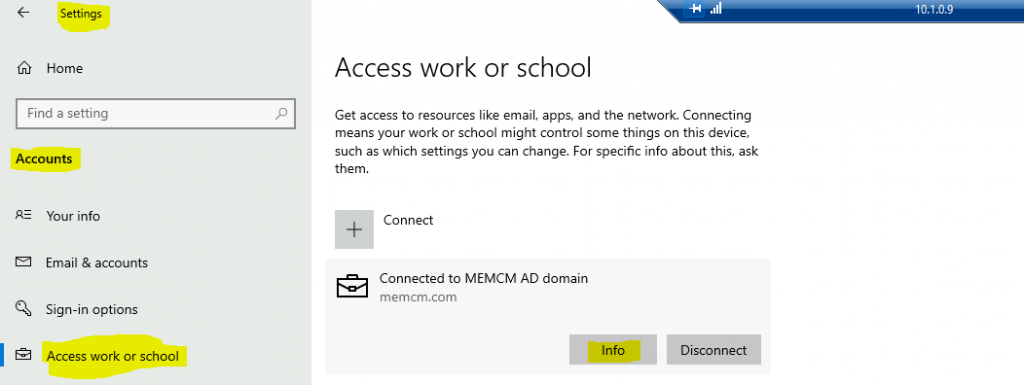
You can see the Intune policies deployed to the Windows 10 co-managed device.
Resources
We are on WhatsApp now. To get the latest step-by-step guides, news, and updates, Join our Channel. Click here – HTMD WhatsApp.
Author
Anoop C Nair has been Microsoft MVP from 2015 onwards for 10 consecutive years! He is a Workplace Solution Architect with more than 22+ years of experience in Workplace technologies. He is also a Blogger, Speaker, and Local User Group Community leader. His main focus is on Device Management technologies like SCCM and Intune. He writes about technologies like Intune, SCCM, Windows, Cloud PC, Windows, Entra, Microsoft Security, Career, etc..


Hey Anoop,
Great article! I wanted to know if you can revert the workload management from Intune back to ConfigMgr?
yes you can.
I m in a middle of project co managed windows update i moved the pilot for windows update then device with bitloacker cannot work any more
Any specific errors that you notice windowsupdate.log try https://www.anoopcnair.com/sccm-collect-windows-update-logs-cmpivot-config/
Great article but what about moving from MBAM to SCCM Bitlocker? Get the same error from Bitlockermanagementhandler.log. Security workload is not SCCM managed; ignoring policy.
I have removed the GPO but do I need to remove the MBAM agent as well?
Hi, I’ve set all this up as described above (all sliders moved to Intune) but want Intune to show Compliant/ non complaint rather than See Configmgr. Is there a way to do that?. It’s easier to see it at a glance than having to click on all devices and then compliance to see the state.
Thanks