Let’s check how you can enable Audit mode for potentially unwanted applications PUA Detection in SCCM Antimalware policy settings. PUA protection in audit mode is useful to detect potentially unwanted applications without blocking them.
Starting in Configuration Manager version 2107, An Audit option for potentially unwanted applications (PUA) was added in the Antimalware policy settings.
Potentially unwanted applications (PUA) are a category of software that can cause your machine to run slowly, display unexpected ads, or at worst, install other software that might be unexpected or unwanted.
PUA is not considered a virus, malware, or other type of threat, but it might perform actions on endpoints that adversely affect endpoint performance or use.
PUA protection in audit mode is also useful if your company is conducting an internal software security compliance check and you’d like to avoid any false positives. The detections are captured in the Windows event log.
- Enable PUA protection in Chromium-based Microsoft Edge
- How to Disable SCCM Application Deployment | ConfigMgr | MEMCM
- The best method to Find Custom Client Settings for a Collection in SCCM ConfigMgr
Enable Audit Mode for PUA Detection in SCCM
Let’s follow the steps below to enable potentially unwanted applications PUA Detection in sccm for an existing policy –
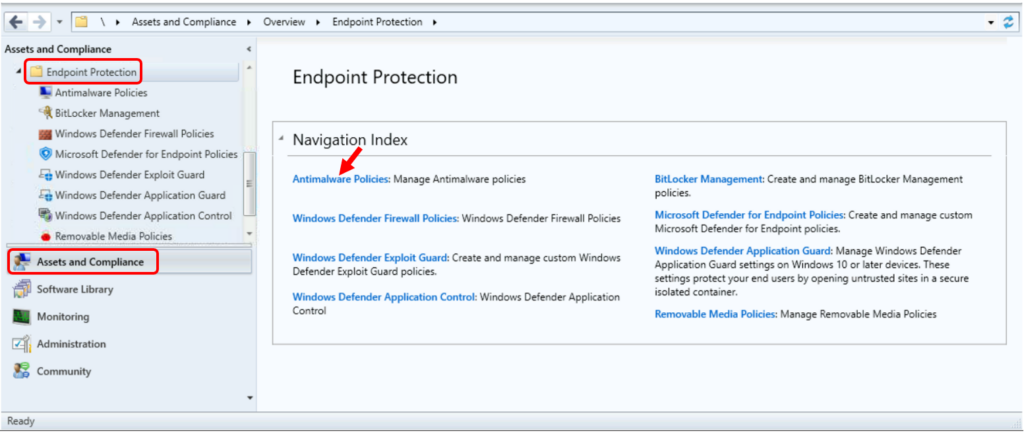
- Launch the Configuration Manager Console. Navigate to Assets and Compliance > Endpoint Protection > Antimalware policy.
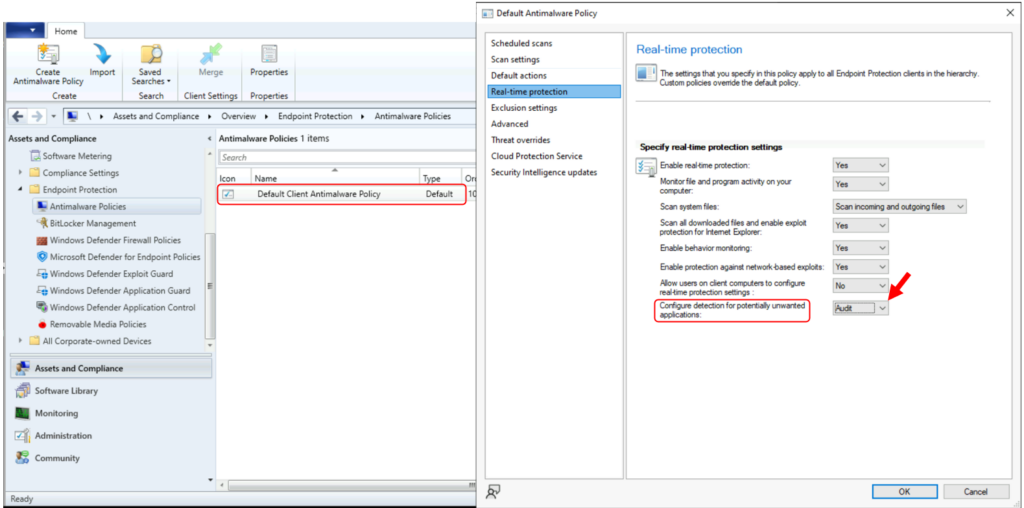
- Choose the set of antimalware policies you want to change, or create a new custom antimalware policy.
- Select the Real-time protection settings page.
- Set the Configure detection for potentially unwanted applications setting to Audit.
Note – This protection policy setting set to Enabled by default.
Create a new antimalware policy for PUA Detection in SCCM
Let’s follow the steps below to create a new antimalware policy to enable PUA Detection in sccm –
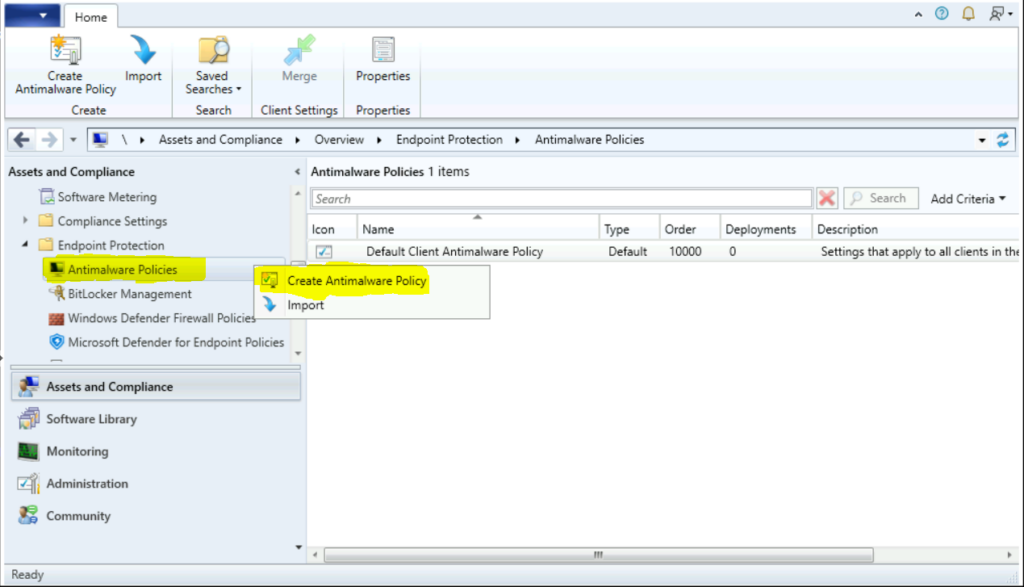
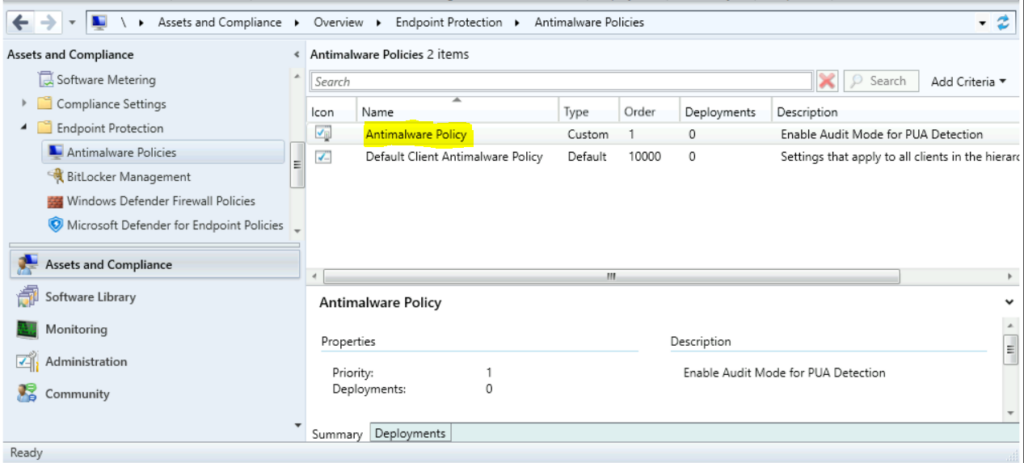
- In the Configuration Manager console, click Assets and Compliance.
- In the Assets and Compliance workspace, expand Endpoint Protection, and then click Antimalware Policies.
- On the Home tab, in the Create group, click Create Antimalware Policy.
In the General section of the Create Antimalware Policy dialog box, enter a name and a description for the policy.
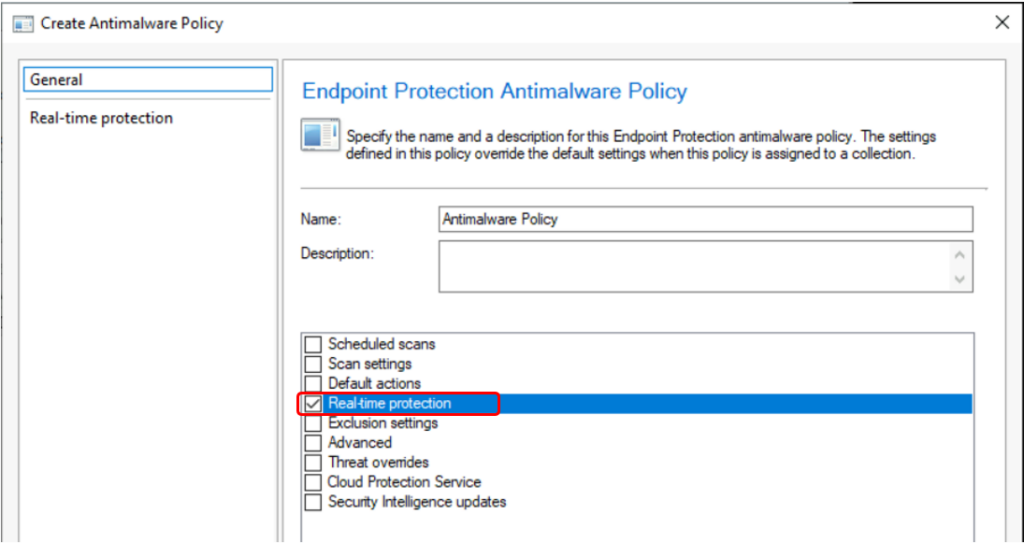
- In the Create Antimalware Policy dialog box, configure the Real-time protection settings, Enable Audit mode for PUA detection.
- Set Configure detection for potentially unwanted applications to Audit and then click OK.
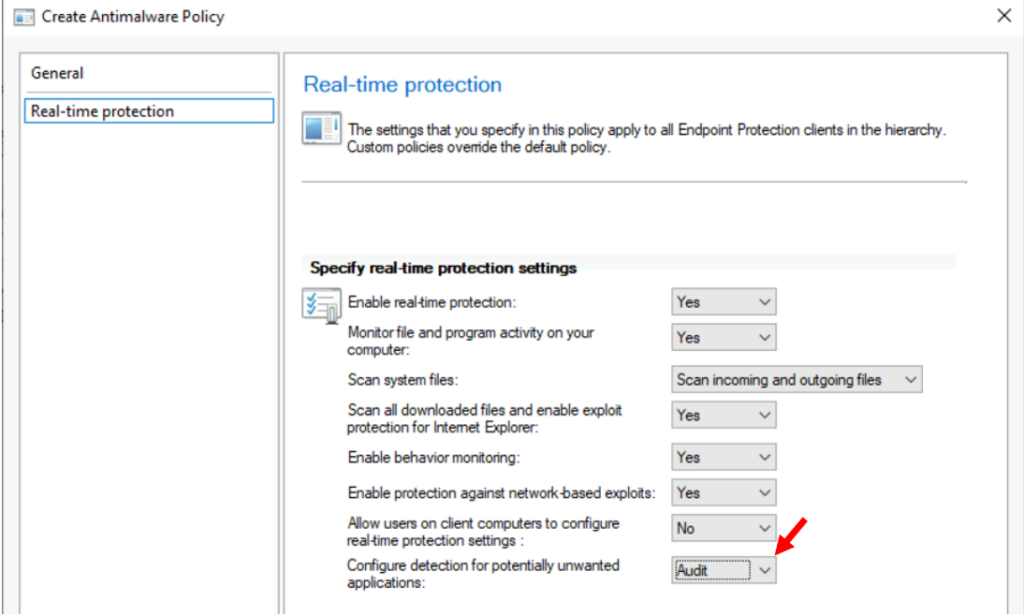
Additionally list of settings that you can configure – Real-time Protection Settings –
| Setting name | Description |
|---|---|
| Enable real-time protection | Set to Yes to configure real-time protection settings for client computers. We recommend that you enable this setting. |
| Monitor file and program activity on your computer | Set to Yes if you want Endpoint Protection to monitor when files and programs start to run on client computers and to alert you about any actions that they perform or actions taken on them. |
| Scan system files | This setting lets you configure whether incoming, outgoing, or incoming and outgoing system files are monitored for malware. For performance reasons, you might have to change the default value of Scan incoming and outgoing files if a server has high incoming or outgoing file activity. |
| Enable behavior monitoring | Enable this setting to use computer activity and file data to detect unknown threats. When this setting is enabled, it might increase the time required to scan computers for malware. |
| Enable protection against network-based exploits | Enable this setting to protect computers against known network exploits by inspecting network traffic and blocking any suspicious activity. |
| Enable script scanning | For Configuration Manager with no service pack only. Enable this setting if you want to scan any scripts that run on computers for suspicious activity. |
| Block Potentially Unwanted Applications at download and prior to installation | Starting in Configuration Manager version 2107, you can select to Audit this setting. Use PUA protection in audit mode to detect potentially unwanted applications without blocking them. |
- Verify that the new antimalware policy is displayed in the Antimalware Policies list.
Once you completed, You can deploy an antimalware policy to client computers. The Deploy option cannot be used with the default client malware policy.


