Key Takeaways:
- Safely index encrypted stores or items on Windows devices
- Admins can apply Intune policies to manage how encrypted content
- Allows end users to search and access encrypted files seamlessly
- Helps organizations meet data protection standards
Let’s discuss How to Safely Index Encrypted Stores or Items on Windows Devices using Intune. Indexing Encrypted Stores or Items policy controls whether the Windows Search service can “look inside” encrypted files to index their contents.
Table of Contents
Table of Contents
How to Safely Index Encrypted Stores or Items on Windows Devices using Intune
Employees who handle thousands of sensitive spreadsheets or legal documents (using EFS) need to search for specific keywords within those files. Without indexing, they would have to open every file manually.
- How to Allow Adding Non Microsoft Accounts Manually Using Intune Setting Catalog
- Intune Allow Microsoft Accounts to be Optional Policy
- Create Intune Policy to Block Microsoft Accounts
Example Scenario
For example, A law firm uses Encrypting File System (EFS) to protect client case files. Paralegals need to find every document mentioning “Case #8821” across 50,000 encrypted Word docs. If disabled, search returns zero results. The firm enables the policy so that staff can work at a professional speed. They mitigate the risk by ensuring BitLocker is also enforced, so the index itself is encrypted at the disk level.
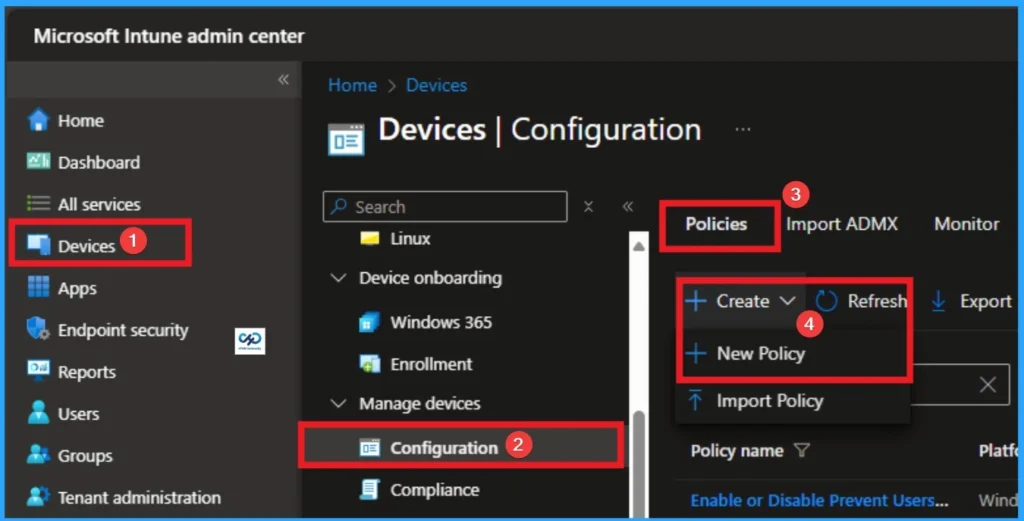
How to Start Policy Creation
As an Admin, you can quickly configure this policy on your organisation. To start the Policy Creation, open the Microsoft Intune Admin center. Then go to Devices > Configuration >+ Create > +New Policy.
| Policy Details |
|---|
| This policy setting is ignored (and Basic is always forbidden) if the ‘AuthSchemes’ (Supported authentication schemes) policy is set and does not include Basic. |
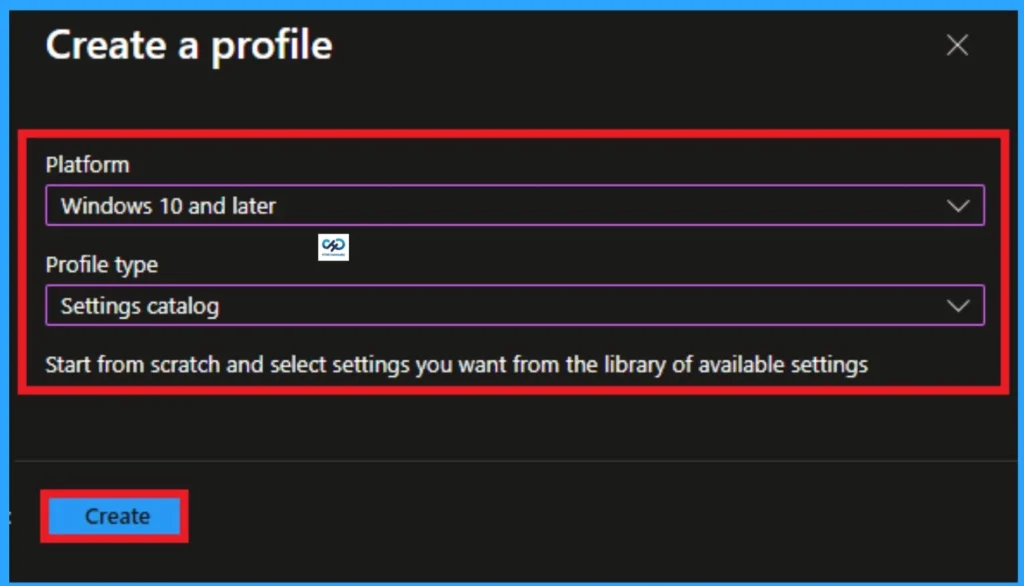
Profile Creation
Profile creation is the necessary step that helps you to assign the policy to appropriate platform and Profile. Here I would like to configure the policy to Windows 10 and later platform and settings catalog profile. Then click on the Create button.
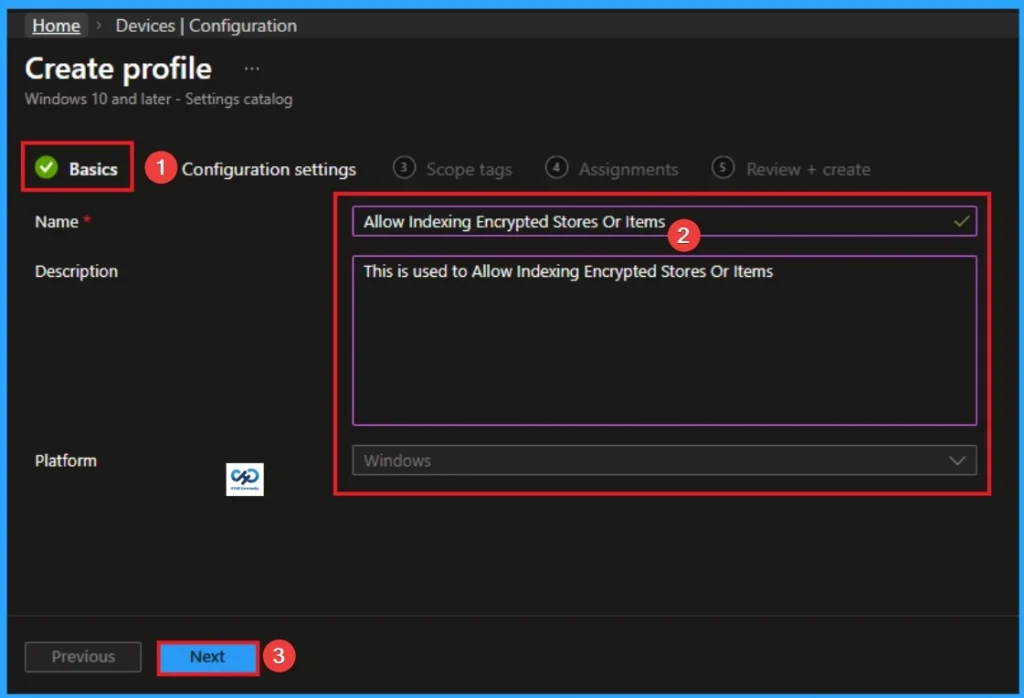
Filling the Basic Tab
Naming the policy is the primary step that help admins to identify the policy later. This is important and necessary step that allows you to know the purpose of the policy. Here is Name is mandatory and description is optional. After adding this click on the Next button.
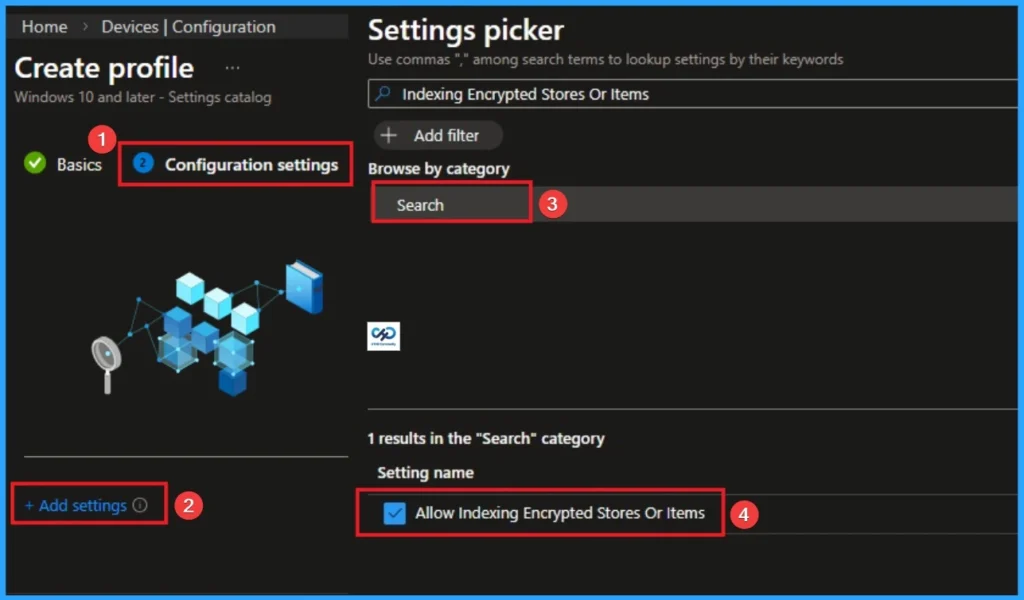
Configure Index Encrypted Stores or Items
With Settings Picker, you can use the Configuration Settings Tab. On this tab, you can click on the +Add Settings hyperlink to get the Settings Picker. The settings picker shows huge number of settings. Here, I would like to select the settings by browsing by Category. I choose System. Then, I choose Search\Allow Indexing Encrypted Stores Or Items.
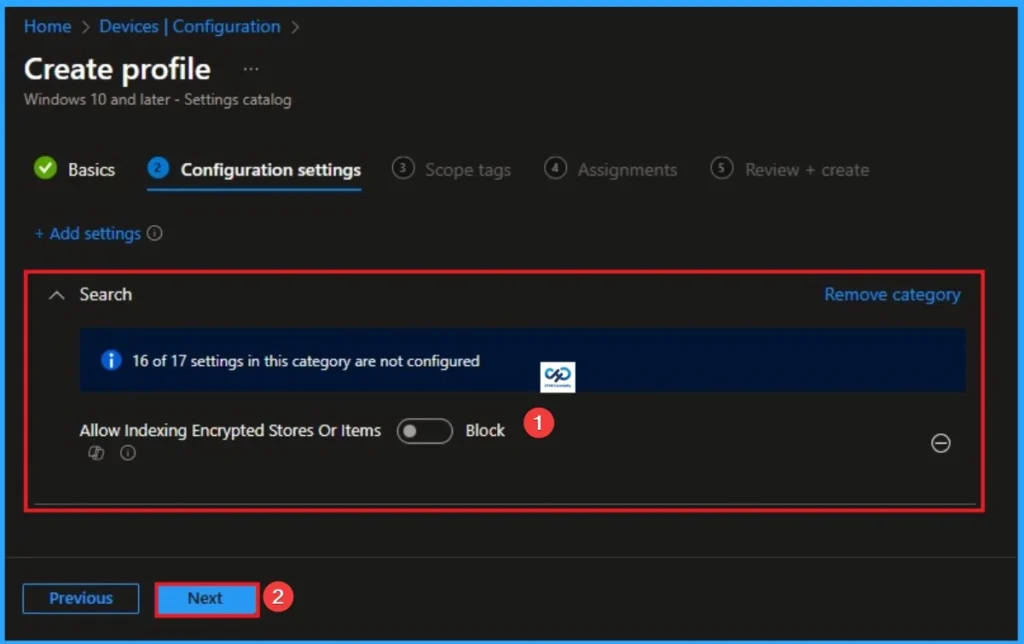
Disable Index Encrypted Stores or Items
If you disable this policy setting, the search service components (including non-Microsoft components) are expected not to index encrypted items or encrypted stores. This policy setting isn’t configured by default. Click on the Next button.
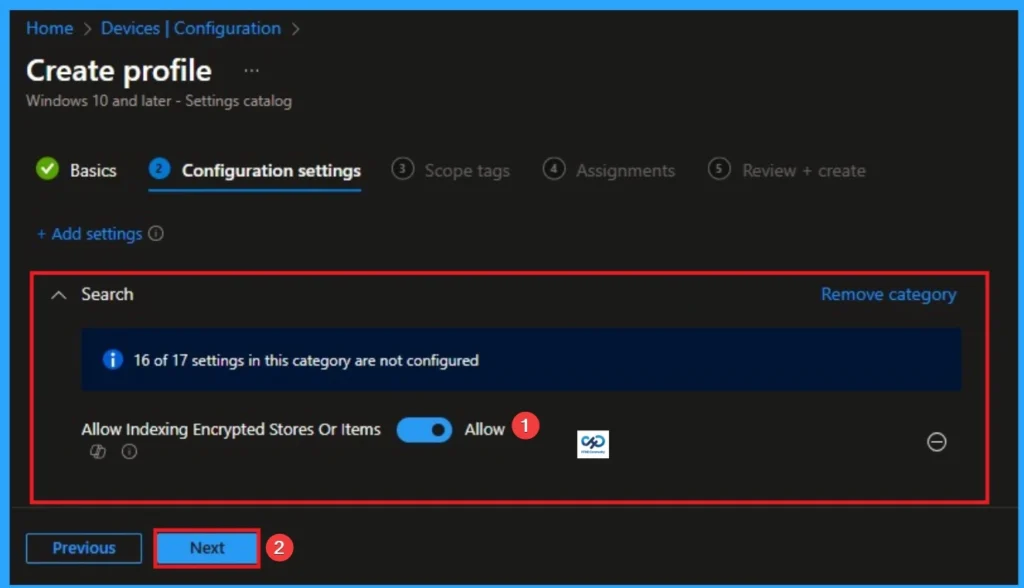
Enable Index Encrypted Stores or Items
If you enable this policy setting, indexing will attempt to decrypt and index the content (access restrictions will still apply). Click on the Next button.
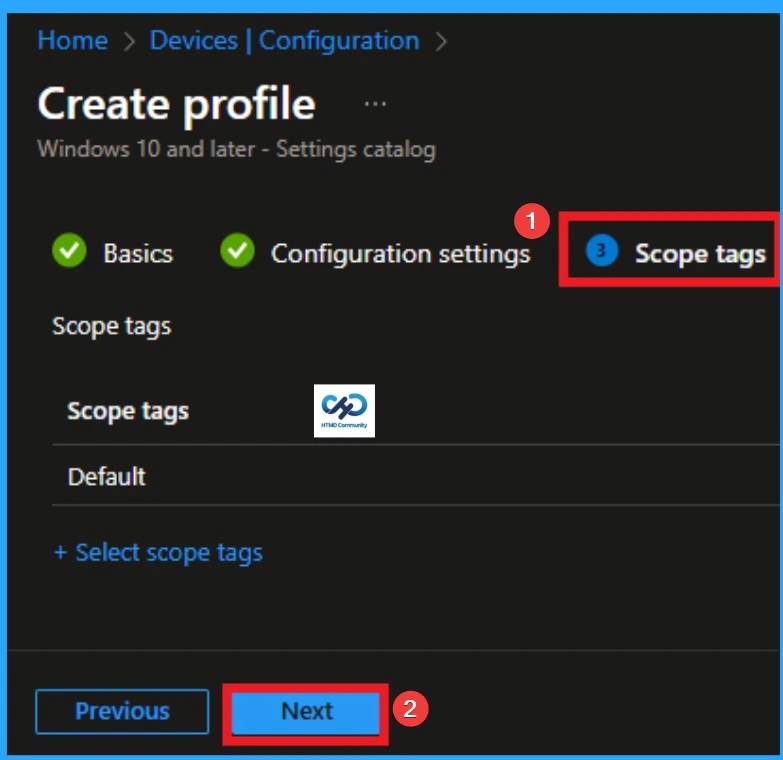
Scope Tags
With scope tags, you create a restriction to the visibility of the Index Encrypted Stores or Items. It helps to organise resources as well. Here, I would like to skip this section, because it is not mandatory. Click on the Next button.
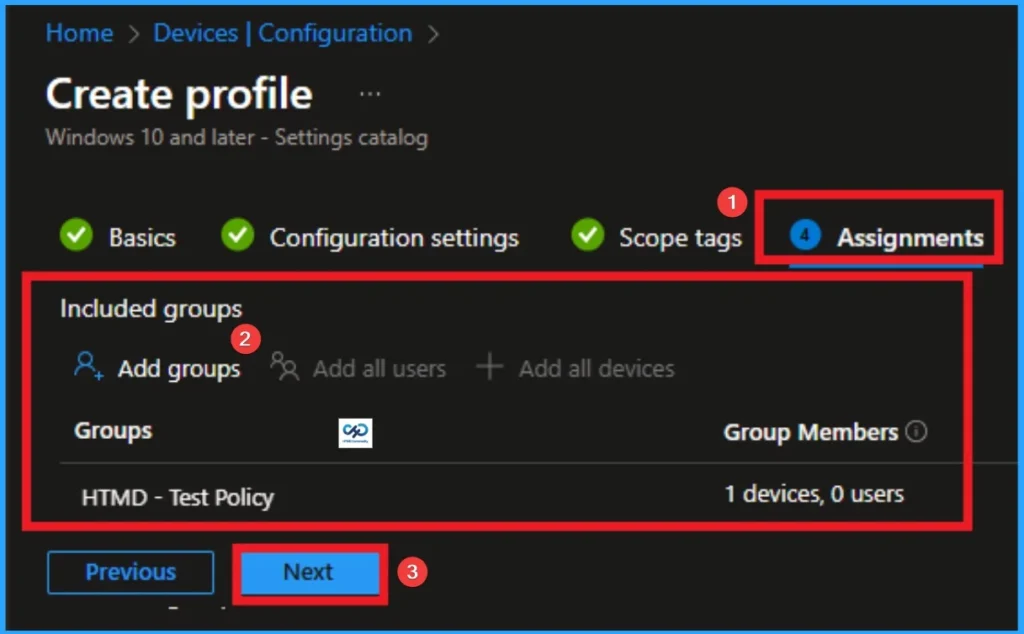
Assignments Tab for Selecting Group
To assign the policy to specific groups, you can use the Assignment Tab. Here I click, +Add groups option under Included groups. I choose a group from the list of groups and click on the Select button. Again, I click on the Select button to continue.
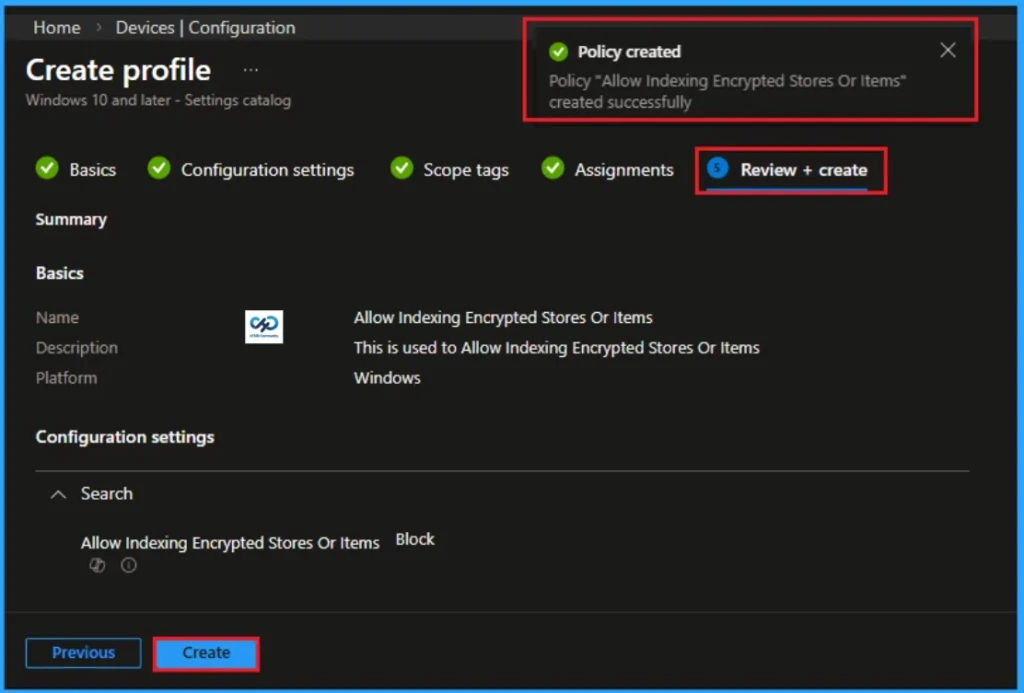
Review + Create Tab
Before completing the policy creation, you can review each tab to avoid misconfiguration or policy failure. After verifying all the details, click on the Create Button. After creating the policy, you will get a success message.
Monitoring Status
The Monitoring Status page shows whether the policy has succeeded or not. To quickly configure the policy and take advantage of the policy sync the assigned device on Company Portal. Open the Intune Portal. Go to Devices > Configuration > Search for the Policy. Here, the policy shows as successful.

Removing the Assigned Group from Index Encrypted Stores or Items Settings
If you want to remove the Assigned group from the policy, it is possible from the Intune Portal. To do this, open the Policy on Intune Portal and edit the Assignments tab and the Remove Policy.
To get more detailed information, you can refer to our previous post – Learn How to Delete or Remove App Assignment from Intune using by Step-by-Step Guide.

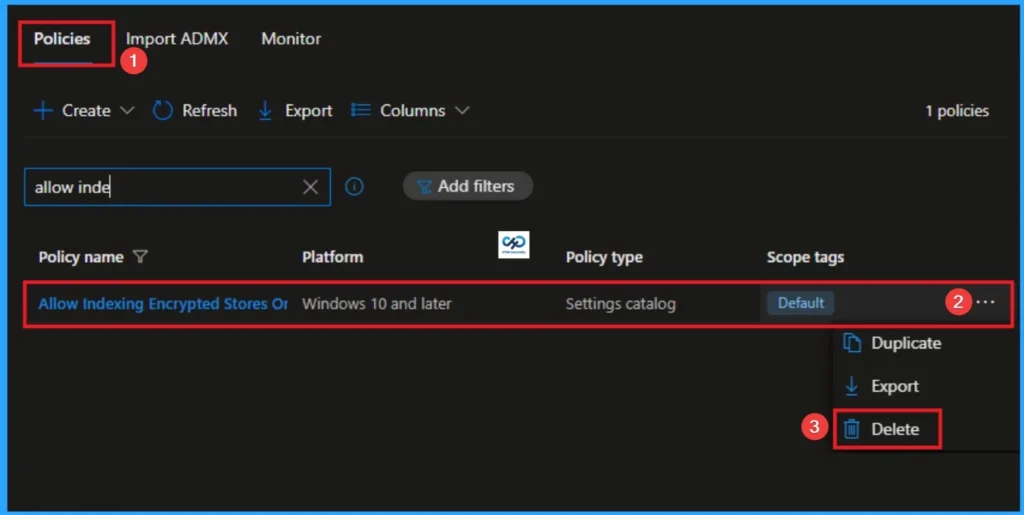
How to Delete Index Encrypted Stores or Items
You can easily delete the Policy from the Intune Portal. From the Configuration section, you can delete the policy. It will completely remove it from the client devices.
For detailed information, you can refer to our previous post – How to Delete Allow Clipboard History Policy in Intune Step by Step Guide.
Windows CSP Detials
If an organization uses Windows Information Protection (WIP), corporate files are automatically encrypted. If this policy is disabled, users cannot search for their own work documents via the Start menu or File Explorer, leading to high frustration and “lost” files.
Need Further Assistance or Have Technical Questions?
Join the LinkedIn Page and Telegram group to get the step-by-step guides and news updates. Join our Meetup Page to participate in User group meetings. Also, Join the WhatsApp Community to get the latest news on Microsoft Technologies. We are there on Reddit as well.
Author
Anoop C Nair has been Microsoft MVP for 10 consecutive years from 2015 onwards. He is a Workplace Solution Architect with more than 22+ years of experience in Workplace technologies. He is a Blogger, Speaker, and Local User Group Community leader. His primary focus is on Device Management technologies like SCCM and Intune. He writes about technologies like Intune, SCCM, Windows, Cloud PC, Windows, Entra, Microsoft Security, Career, etc.


