Let’s discuss Microsoft Security Exposure Management using Defense Techniques. Microsoft Security Exposure Management is a new solution that Microsoft has recently launched. It aims to help organizations find and manage security risks in their digital systems.
This solution can detect and fix vulnerabilities in your network, software, and devices before hackers can exploit them. For you and your organization, this is better protection against cyber-attacks, stronger security practices, and a safer environment for your data and operations.
This post concerns a session Heather Poulsen, a community manager, shared in the Microsoft Tech Community on March 11, 2024. It discusses a new feature called Exposure Management.
This feature helps organizations manage security risks by giving a clear overview of potential attack points. This helps protect your digital environment by reducing the chances of an attack.

- Top 5 Data Security Challenges DLP Productivity eBook Download for Free
- Learn About 8 Common Cyber Security Threats
- Enhanced Security with Windows 365 Customer Lockbox
- 2024 Cybersecurity Certifications for IT Professionals
- 40% of All Incoming emails Pose a Potential Cybersecurity Threat
Microsoft Security Exposure Management using Defense Techniques
By using Exposure Management features, you can limit the chances of an attack and protect your digital environment. With the growing threat world, having a comprehensive understanding of your attack surface is crucial for reducing risk and enhancing security across your organization.
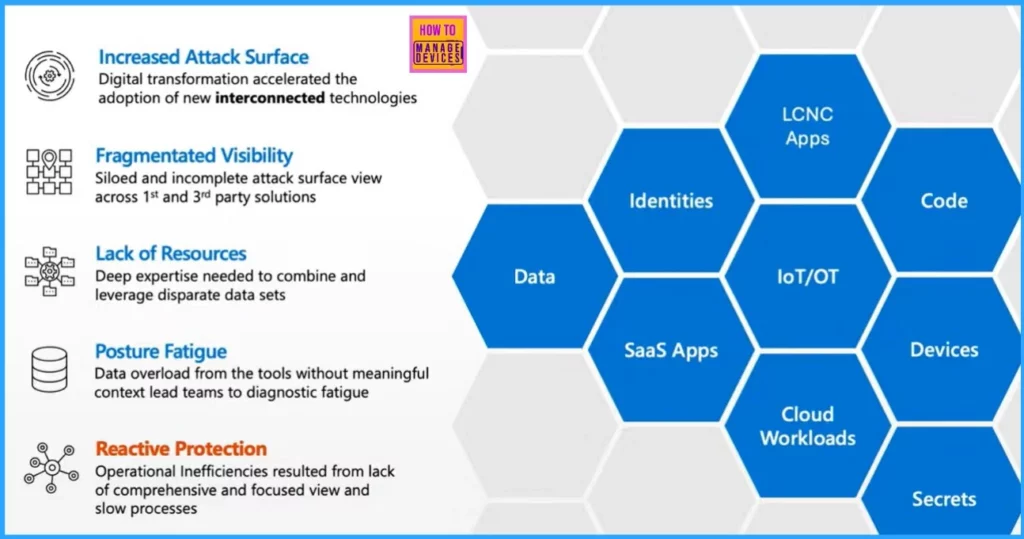
| Security Exposure Management | Details |
|---|---|
| Increased Attack Surface | Digital transformation accelerated the adoption of new interconnected technologies. |
| Fragmentated Visibility | Siloed and incomplete attack surface view across 1st and 3rd party solutions |
| Lack of Resources | Deep expertise needed to combine and leverage disparate data sets |
| Posture Fatigue | Data overload from the tools without meaningful context leads teams to diagnostic fatigue. |
| Reactive Protection | Operational Inefficiencies resulted from a lack of comprehensive and focused view and slow processes. |
Advancements in Managing Vulnerabilities
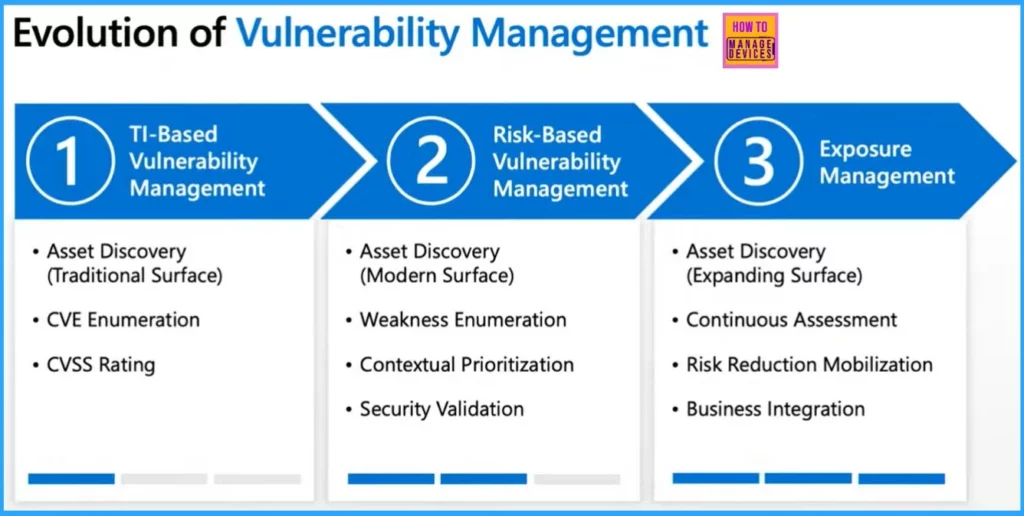
Exposure Management is the best way to manage security risks in 3 main stages. First, it starts with traditional methods like CVE enumeration and CVSS ratings. Then, it moves to a more modern approach, focusing on finding asset weaknesses and prioritizing them based on their importance in your setup.
- Next, it adapts to the expanding digital landscape by continually discovering new assets and assessing risks.
- It also emphasizes mobilizing efforts to reduce risk and integrating security with business operations.
- Exposure Management helps evolve vulnerability management to keep up with changing threats and protect your organization effectively.
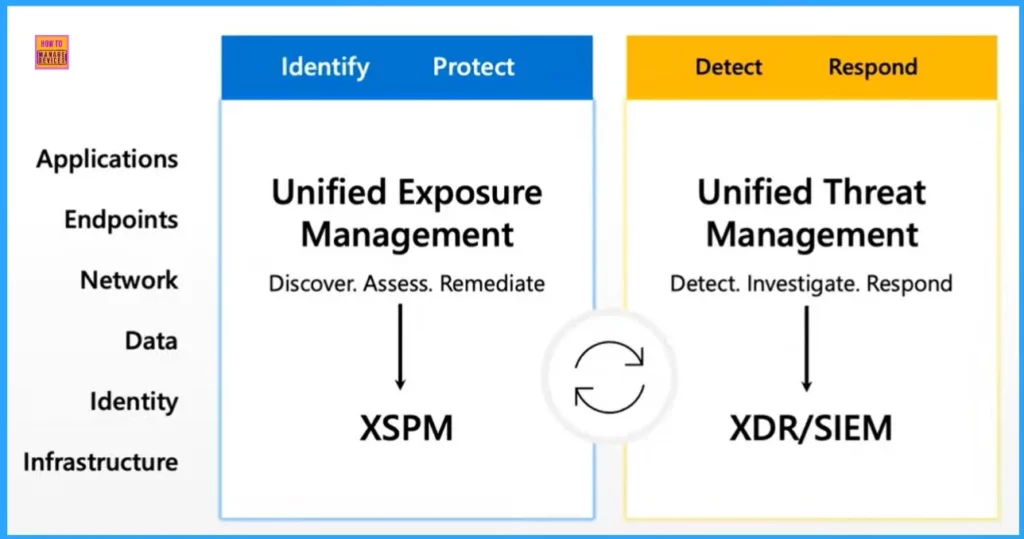
Unified Exposure Management and Unified Threat Management
The screenshot below helps you show the critical aspects of security management, including identifying, protecting, detecting, and responding to threats across various areas such as applications, endpoints, networks, data, identity, and infrastructure.
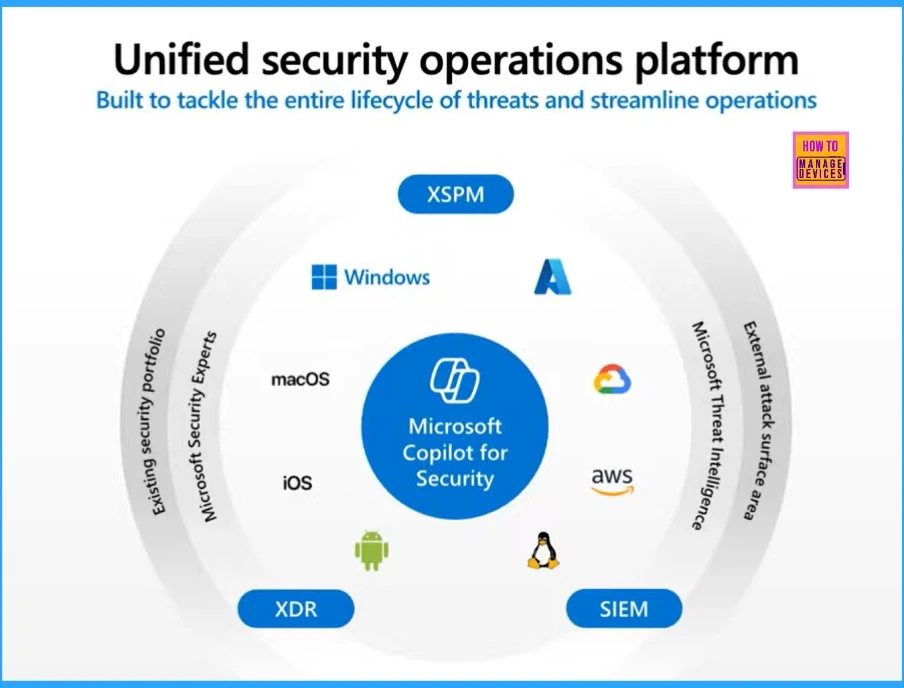
- Unified Exposure Management – XSPM – Discover, Assess and Remediate
- Unified Threat Management – XDR/SIEM – Detect, Investigate and Respond
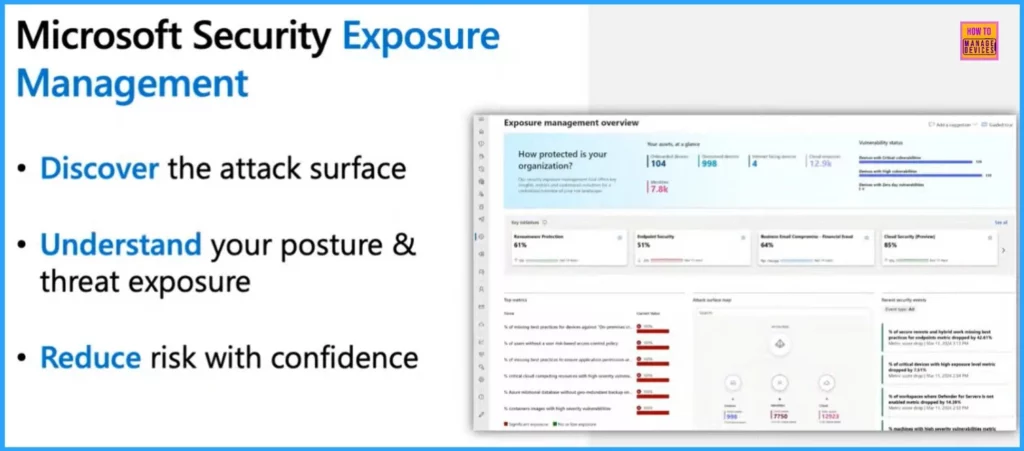
Safeguarding your Digital Space with Microsoft Security Exposure Management
Microsoft Security Exposure Management helps you keep your digital world safe in 3 easy steps. The first step is to discover where your system might be vulnerable to attacks. The second step is it helps you understand how secure or exposed you are to threats.
Finally, it gives you the tools to confidently lower your risks, making your digital space safer for everyone.
The screenshot below shows continuous Exposure Management. On the Right, it shows the 3 key features: Attack Surface Discovery, Attack Path Analysis, and Unified Exposure Insights.
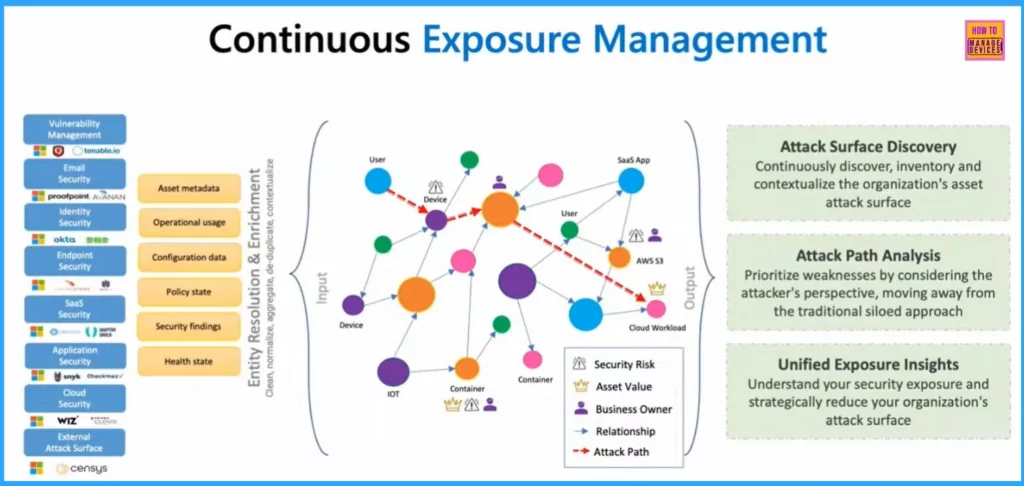
Attack Surface Management
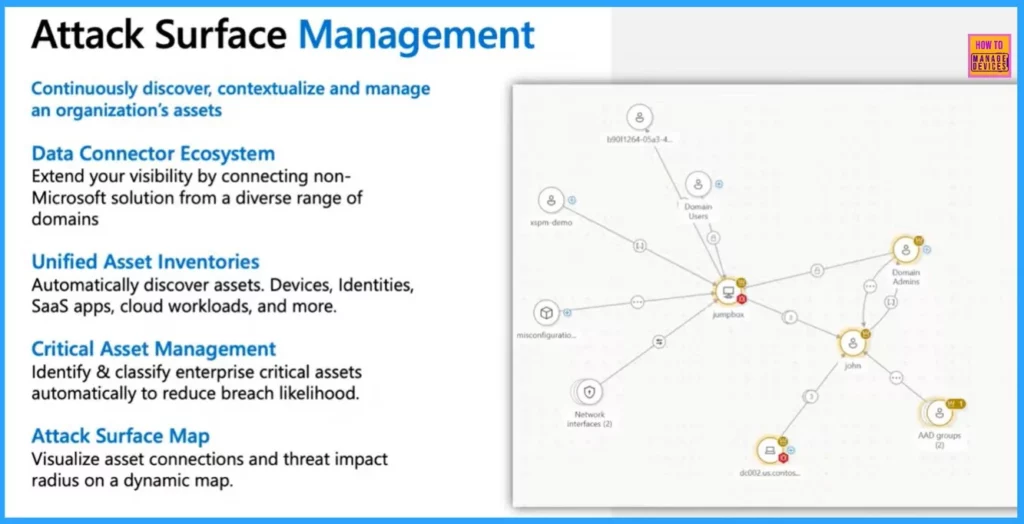
Attack Surface Management helps you track your organization’s digital assets and regularly check and manage them to stay secure. Microsoft Security Exposure Management simplifies keeping your digital world safe with five important features.
- Data Connector Ecosystem – This feature helps you connect various tools from different areas to give you a complete view of your security. It is not just a Microsoft solution.
- Unified Asset Inventories -It helps automatically discover and track all your assets, including devices, identities, apps, and cloud workloads.
- Critical Asset Management – This feature automatically identifies and classifies your most essential assets to lower the risk of a breach.
- Attack Surface Map – This feature shows how assets are connected and visualize the potential impact of threats on a dynamic map, helping you prioritize your security plans.
Attack Path Analysis
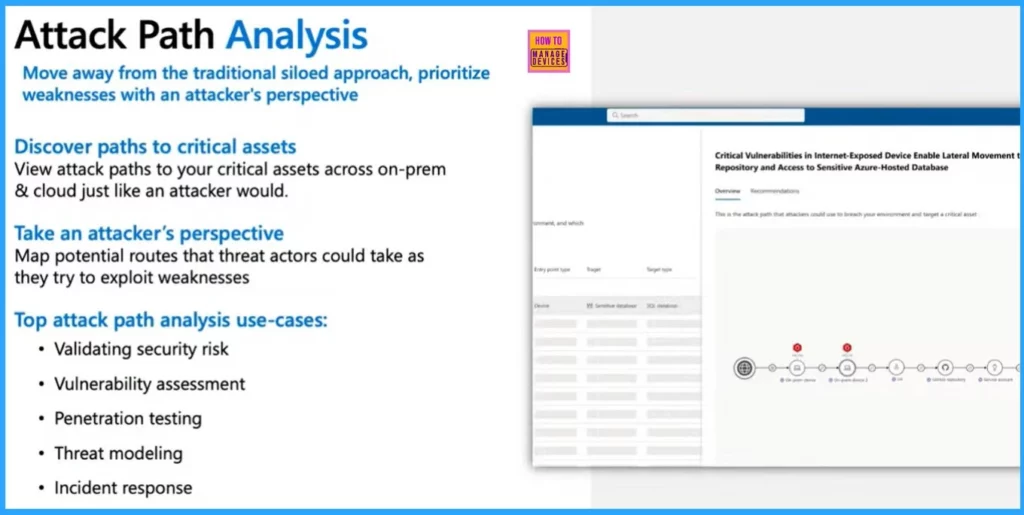
Attack path analysis is a way to think like an attacker and identify potential paths a hacker could take to access your most important assets, whether on-site or in the cloud. Instead of focusing on separate areas of security, this approach looks at the entire system to find possible vulnerabilities.
- Top attack path analysis use cases
- Validating security risk
- Vulnerability assessment
- Penetration testing
- Threat modeling
- Incident response
Unified Exposure Insights
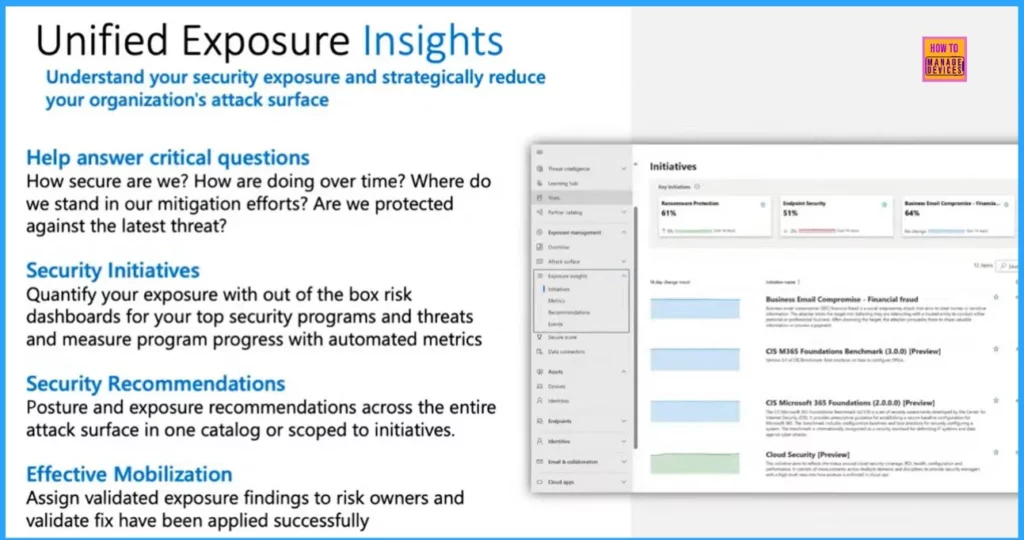
Let’s discuss Unified exposure insights. They help you provide a clear picture of your security risks, enabling you to effectively manage and reduce your organization’s attack surface.
- Help answer critical questions
- Security Initiatives
- Security Recommendations
- Effective Mobilization
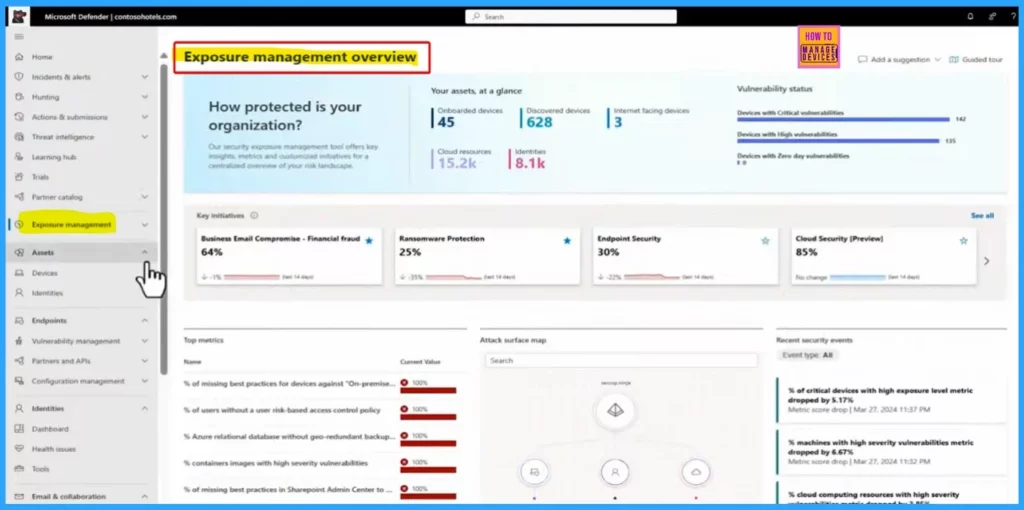
Exposure Management Overview
Microsoft has introduced a new section called Security Exposure Management in the Security and Compliance Center at security.microsoft.com. This section gathers all your security assets in one place, giving you a quick overview.
It shows essential initiatives that are crucial for your security teams’ progress, making tracking and managing them easier.
The unified security operations platform is designed to handle the complete lifecycle of security threats and make your operations smoother. The screenshot below shows the unified security operations platform.
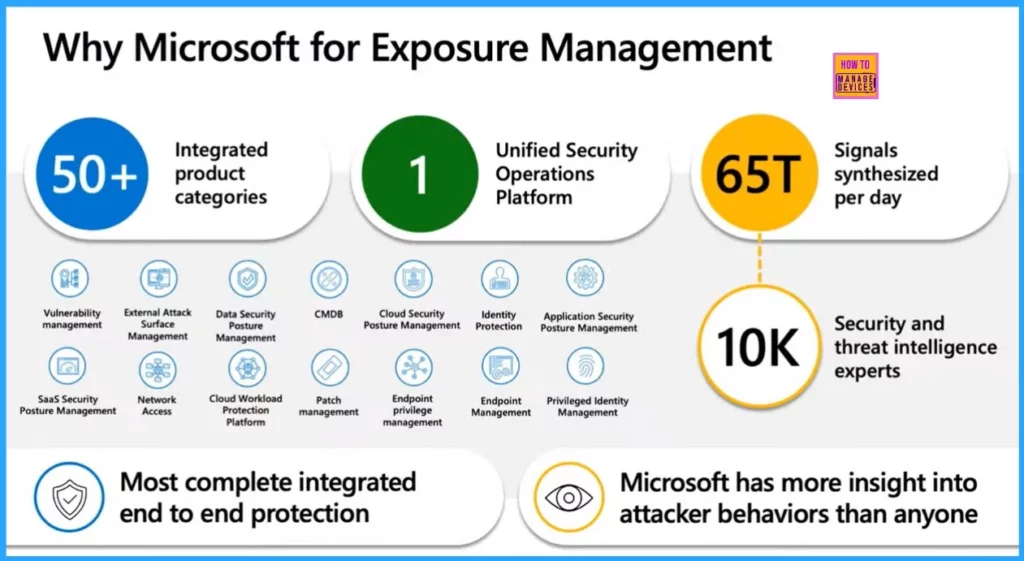
Why Microsoft for Exposure Management
Microsoft offers a complete and connected security experience for exposure management. The following screenshot and list show why Microsoft is a top choice for exposure management.
- 50 PLUS Integrated product categories
- 1 Unified Security OperationsPlatform
- 65T Signals synthesized per day
- 10K Security and threat intelligence experts
- Most complete integrated end-to-end protection
- Microsoft has more insight into attacker behaviors than anyone
We are on WhatsApp now. To get the latest step-by-step guides, news, and updates, Join our Channel. Click here. HTMD WhatsApp.
Author
About the Author: Vidya is a computer enthusiast. She is here to share quick tips and tricks with Windows 11 or Windows 10 users. She loves writing about Windows 11 and related technologies. She is also keen to find solutions and write about day-to-day tech problems.


