Most of you are already prepared for the upcoming holiday season, While DDoS attacks happen all year round, the holidays are one of the most popular times and when some of the most high-profile attacks occur. Don’t let DDoS attacks ruin your holidays, protect yourself.
DoS attack is a malicious attempt to disrupt the normal traffic of a targeted server or service and affect the availability of a targeted system, such as a website or application, to legitimate end users.
Cyber attackers also look forward to this time of year to celebrate an emerging holiday tradition of distributed denial-of-service (DDoS) attacks. Typically, attackers generate large volumes of packets or requests, ultimately overwhelming the target system.
In the case of a DDoS attack, the attacker uses multiple compromised or controlled sources to generate the attack. Last October through December, there was an increase in DDoS attacks targeting services frequently used, such as online games and media streaming during the festive season.
Microsoft mitigated several large-scale DDoS attacks, including one of the largest attacks in history from approximately 10,000 sources spanning multiple countries. There is a wide range of motives behind DDoS attacks, including financial, competitive advantage, or political.
- 2022 holiday DDoS protection guide – Microsoft Security
- Best Antivirus For Windows 11 Microsoft Defender | App Browser Protection | Firewall Protection
What is Distributed Denial-of-service DDoS Attack?
A DDoS attack targets websites and servers by disrupting network services and attempting to overwhelm an application’s resources. Attackers will flood a site or server with large traffic, resulting in poor website functionality or knocking it offline altogether.
DDoS attacks are carried out by individual devices (bots) or networks of devices (botnet) infected with malware and used to flood websites or services with high traffic volumes. DDoS attacks can last a few hours or even days.

Organizations typically have reduced resources dedicated to monitoring their networks and applications—providing easier opportunities for threat actors to execute attacks. Traffic volume is at an all-time high, especially for e-commerce websites and gaming providers, making it harder for IT staff to distinguish between legitimate and illegitimate traffic.
For attackers seeking financial gain, the opportunity for more lucrative payouts can be higher during the holidays as revenues are at the highest and service uptime is critical. Organizations are more willing to pay to stop an attack to minimize loss of sales, customer dissatisfaction, or damage to their reputation.
Azure DDoS Protection
Let’s see here how Azure DDoS Protection Standard can protect your applications against targeted DDoS attacks and why it is critical for every business running in Azure to use the service to enhance their security posture. If your protected applications are under attack, Azure DDoS Protection Standard provides an SLA guarantee and cost protection.
Azure DDoS Protection, combined with application design best practices, provides enhanced DDoS mitigation features to defend against DDoS attacks. It’s automatically tuned to help protect your specific Azure resources in a virtual network, and offers two tiers – IP Protection and Network Protection – to meet your security and cost needs.
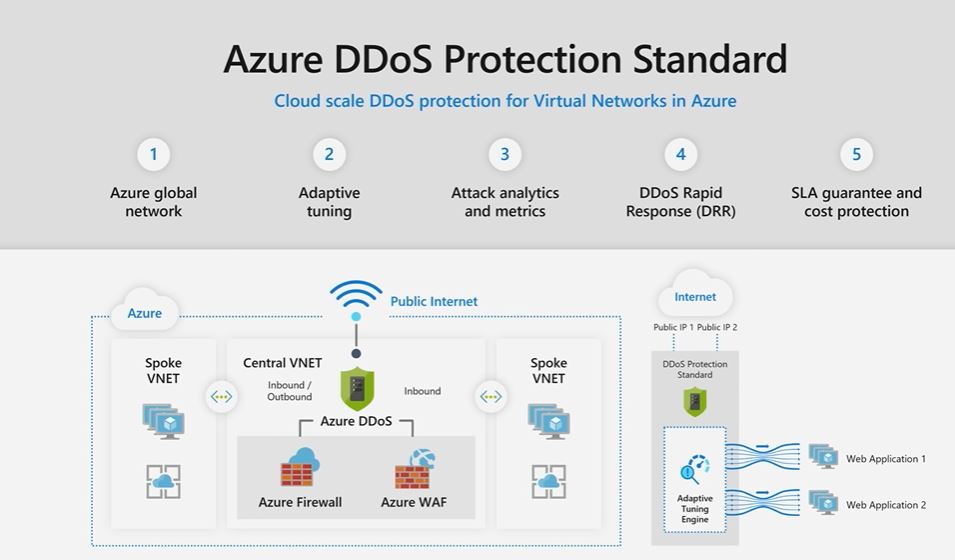
Services running on Azure are inherently protected by the default infrastructure-level DDoS protection. However, the protection that safeguards the infrastructure has a much higher threshold than most applications have the capacity to handle and does not provide telemetry or alerting, so while a traffic volume may be perceived as harmless by the platform, it can be devastating to the application that receives it.
By onboarding to the Azure DDoS Protection Service, the application gets dedicated monitoring to detect attacks and application specific thresholds. A service will be protected with a profile tuned to its expected traffic volume, providing a much tighter defense against DDoS attacks.
Tips for Protecting against DDoS Attacks
Don’t wait until after an attack to protect yourself. While you cannot completely avoid being a target of a DDoS attack, proactive planning and preparation can help you defend against an attack more effectively.
- Identify the applications within your organization exposed to the public internet and evaluate potential risks and vulnerabilities.
- You must understand the normal behavior of your application so that you’re prepared to act if the application is not behaving as expected. Azure provides monitoring services and best practices to help you gain insights into the health of your application and diagnose issues.
- We recommend running attack simulations to test how your services respond to attacks. You can simulate a DDoS attack on your Azure environment with services from our testing partners—BreakingPoint Cloud and RedButton.

Make sure you’re protected – With DDoS attacks at an all-time high during the holidays, you need a DDoS protection service with advanced mitigation capabilities that can handle attacks at any scale.
- We recommend enabling Azure DDoS Protection, which provides always-on traffic monitoring to automatically mitigate an attack when detected, adaptive real-time tuning that compares your actual traffic against predefined thresholds, and full visibility on DDoS attacks with real-time telemetry, monitoring, and alerts.
- Azure DDoS Protection should be enabled for virtual networks with applications exposed over the public internet. Resources in a virtual network that require protection against DDoS attacks include Azure Application Gateway, Azure Load Balancer, Azure Virtual Machines, and Azure Firewall.
- For comprehensive protection against different DDoS attacks, set up a multi-layered defense by deploying Azure DDoS Protection with Azure Web Application Firewall (WAF). Azure DDoS Protection protects the network layer (Layers 3 and 4), and Azure WAF protects the application layer (Layer 7).
- Azure DDoS Protection identifies and mitigates DDoS attacks without any user intervention. To get notified when there’s active mitigation for a protected public IP resource, you can configure alerts
Create a DDoS response strategy – This is critical to help you identify, mitigate, and quickly recover from DDoS attacks. A key part of the strategy is a DDoS response team with clearly defined roles and responsibilities. This DDoS response team should understand how to identify, mitigate, and monitor an attack and be able to coordinate with internal stakeholders and customers.
Reach out for help during an attack – If you are experiencing an attack, you should contact the appropriate technical professionals for help. Azure DDoS Protection customers have access to the DDoS Rapid Response (DRR) team, who can help with attack investigation during an attack as well as post-attack analysis.
Learn and adapt after an attack – While you’ll likely want to move on as quickly as possible if you’ve experienced an attack, it’s important to continue to monitor your resources and conduct a retrospective after an attack. You should apply any learnings to improve your DDoS response strategy.
Author
HTMD Admin Account to provide news and latest updates on the known issue from Microsoft world. We cover Windows, Intune, Azure, AVD, and Windows 365 news.



Informative !