In this post, Let’s understand what is Azure Bastion Host is and its configuration details. Here I will be discussing Azure Bastion solution from Microsoft that help us with a more secured remote connection, traffic workflow when we connect Azure VMs and step to configure.
This is my first post in the HTMD community. My name is Abhinash Kumar. I work as a consultant, having more than 5 years of IT experience in Cloud Computing, Azure, and Server Administration.
Let’s check the details here how you can connect the SCCM server hosted in Azure via Bastion; Setup Azure Bastion Connect to SCCM Server | ConfigMgr | MECM
What is Azure Bastion?
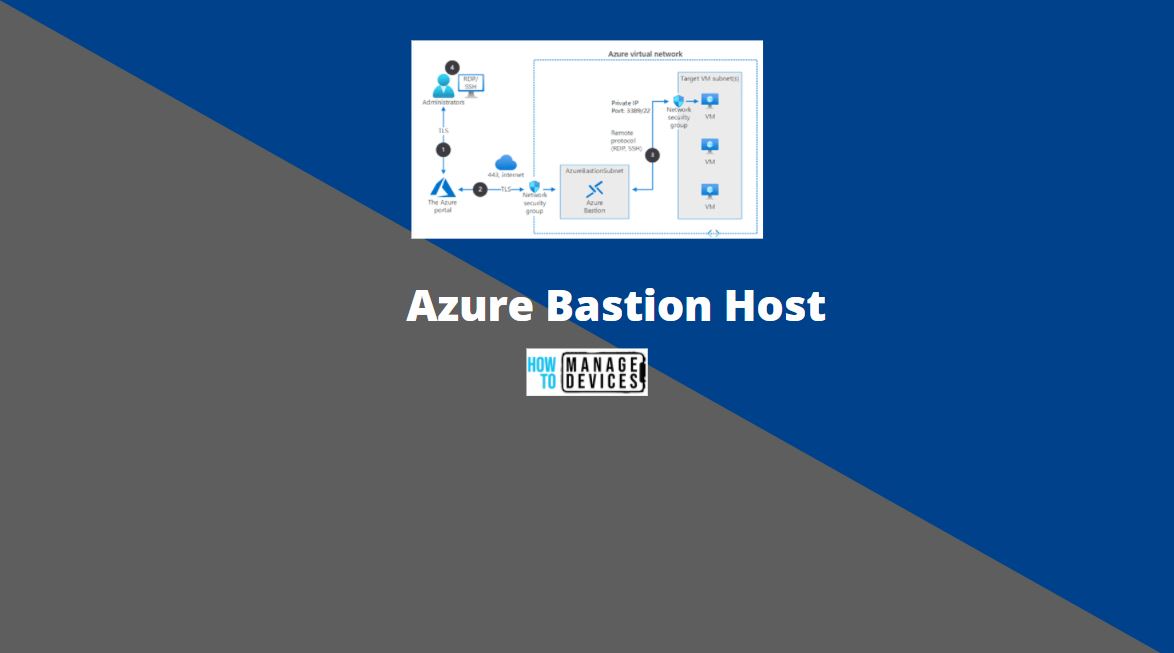
Azure Bastion is a PaaS service that provides a secure RDP/SSH connection to Azure VMs without exposing them over the public internet. Azure Bastion is deployed to a vNet and supports virtual network peering. Specifically, Azure Bastion manages RDP/SSH connectivity to VMs created in the local or peered vNet.
Why we use Azure Bastion?
In general practice there is two way we leverage for connecting Azure VMs which is listed below:
- Connect using Public IP
- Connect using Jump Box
In both modes, we have to do some network hardening and enable Just In time access which involves extra cost. To eliminate all these efforts, we use Azure Bastion, which helps us connect all the Azure VMs without exposing them over the internet.
Traffic workflow when we connect Azure VMs
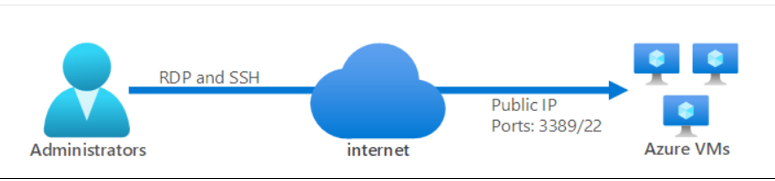
#Scenario 1 – Below is the traffic workflow when we use the public Internet to access VMs –
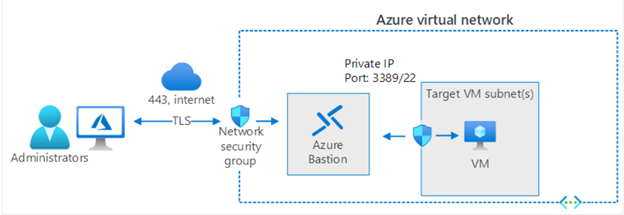
#Scenario 2 – Below is the traffic workflow when we use Azure Bastion to access VMs –
How Azure Bastion work?
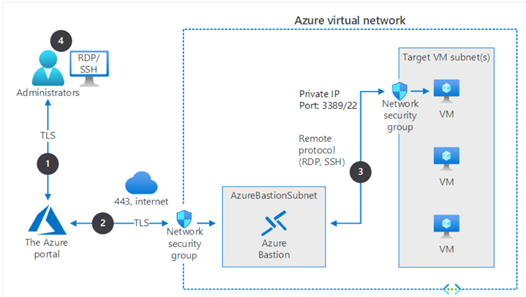
Azure Bastion is configured under the same virtual network where all Azure VMs resides. Still, it has its own NSG protected subnet with the unique name “AzureBastionSubnet,” with a minimum /27 prefix. Bastion subnet only supports communication through TCP post 443 from Azure Portal.
Azure Bastion Architecture Diagram
Prerequisites
Here are the required NSG rules that need to be taken care of for proper traffic flow from the internet to bastion subnet and bastion subnet to VMs subnet –
- Inbound –
- RDP and SSH connections from the Azure Bastion subnet to the target VM subnet
- TCP port 443 access from the internet to the Azure Bastion public IP
- TCP access from Azure Gateway Manager on ports 443 or 4443
- Outbound –
- TCP access from the Azure platform on port 443 to support diagnostic logging.
Minimum access required for the user to leverage bastion for VMs connection –
User required Reader access on below Azure resources:
- The target VM.
- The network interface with private IP on the target VM.
- The Azure Bastion resource.
Azure Bastion requires a Public IP address which must have the following configuration –
- The Public IP address SKU must be Standard.
- The Public IP address assignment/allocation method must be Static.
- The Public IP address name is the resource name by which you want to refer to this public IP address.
- You can choose to use a public IP address that you already created, as long as it meets the criteria required by Azure Bastion and is not already in use.
Types of Azure Bastion Host SKU
SKU is also known as Tier. Azure Bastion support two types of SKU: Basic and Standard.
Here’s the details-
| Features | Basic SKU | Standard SKU |
| Access Linux VM Private Keys in Azure Key Vault (AKV) | Available | Available |
| Host scaling | N/A | Available |
What is Instance and Host Scaling?
An Instance is an optimized Azure VM that will create when we configure the Azure bastion in the backend. It is fully managed by Azure and run all required process needed for Azure Bastion. We connect to Azure VMs using the Azure Bastion instance. For Basic SKU, two examples are created, and by using Standard SKU, we can specify the number of Instances between 2-50. This is called host scaling.
Note: – Each instance can support 10-12 concurrent RDP/SSH connections.
How to Configure Azure Bastion Host?
To configure Azure Bastion Administrator requires Contributor access to create it. In this section, you can learn how to Configure Azure Bastion Host?
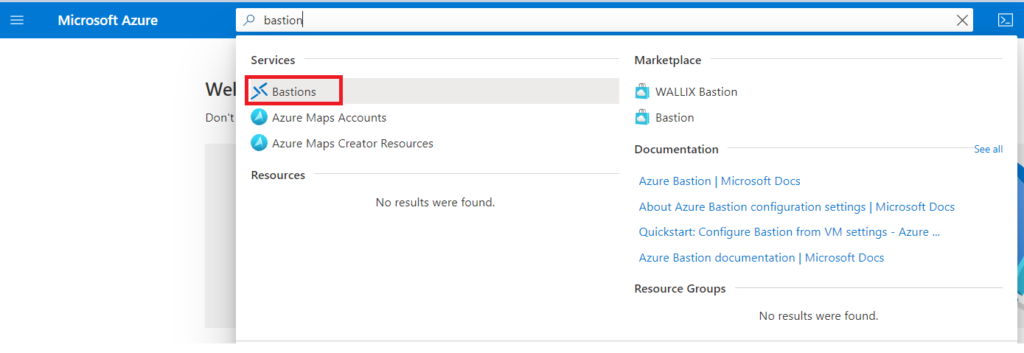
- Login to the Azure portal
- Search “Bastion” in global search box.
- Under services, click Bastions.
- We have to fill option which has Asterisk (*) sign on below screenshot then fill Tags and click on “Review+Create”:
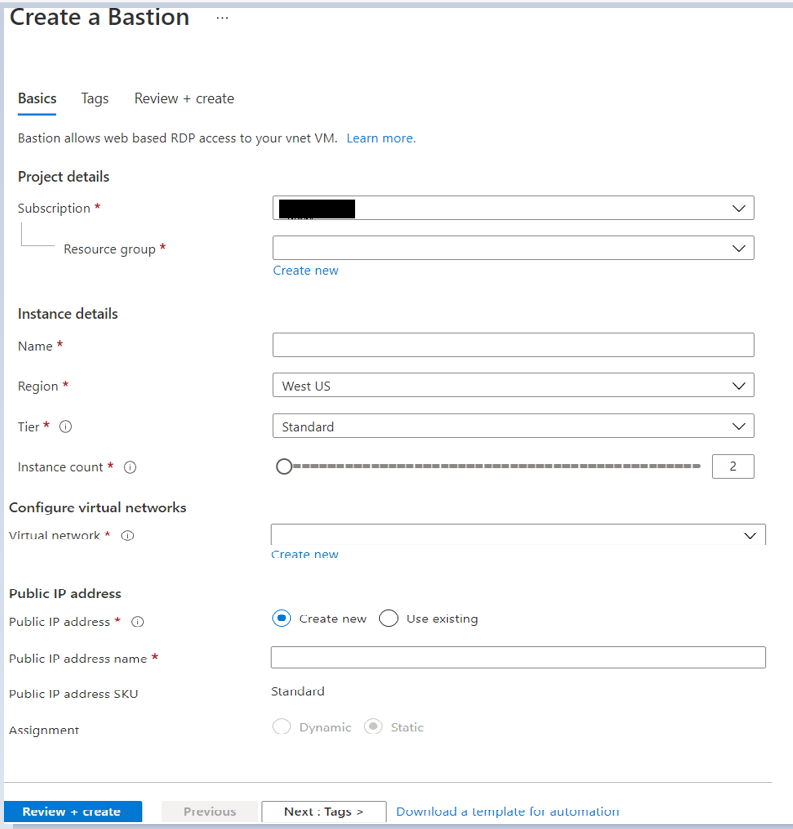
Note: After we selected the required Virtual Network, it shows the subnet, then we have to choose or create the subnet named “AzureBastionSubnet,” and that subnet must be at least /27 or larger. For the Standard SKU, we recommend /26 or larger to accommodate future additional host scaling instances.
Connect to a VM using Bastion
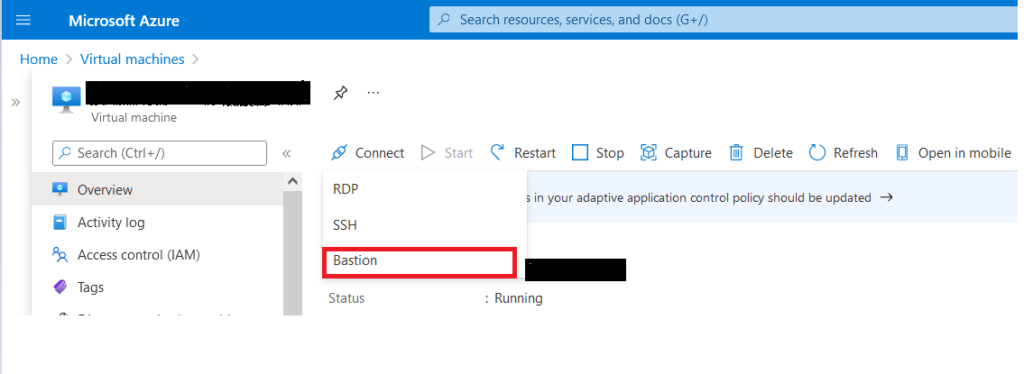
- Login to Azure portal and navigate to Azure VM that you want to connect.
- On the overview page select Connect. Then select Bastion from the dropdown.
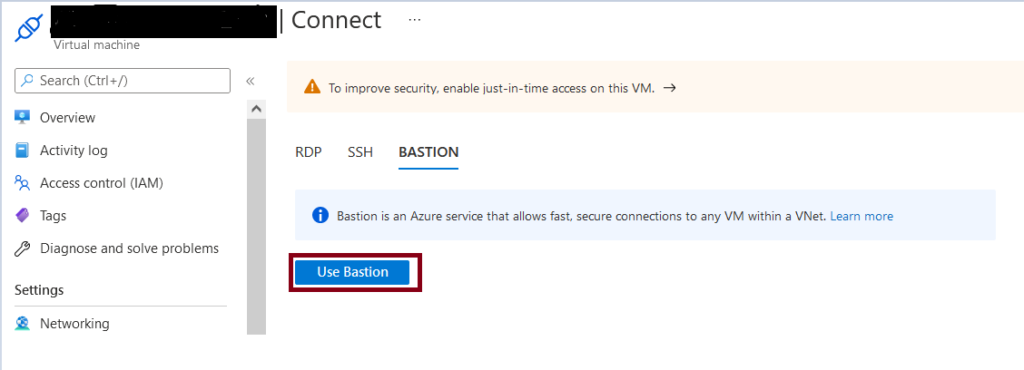
- Click on “Use Bastion” button.
- On the Connect using Azure Bastion page, enter the username and password for your virtual machine and select the check box “Open in new window” this will open our VM in new tab .
- Click on Connect.
Note – When you click on the “Connect” button, A popup will appear in your browser that we have to allow it.
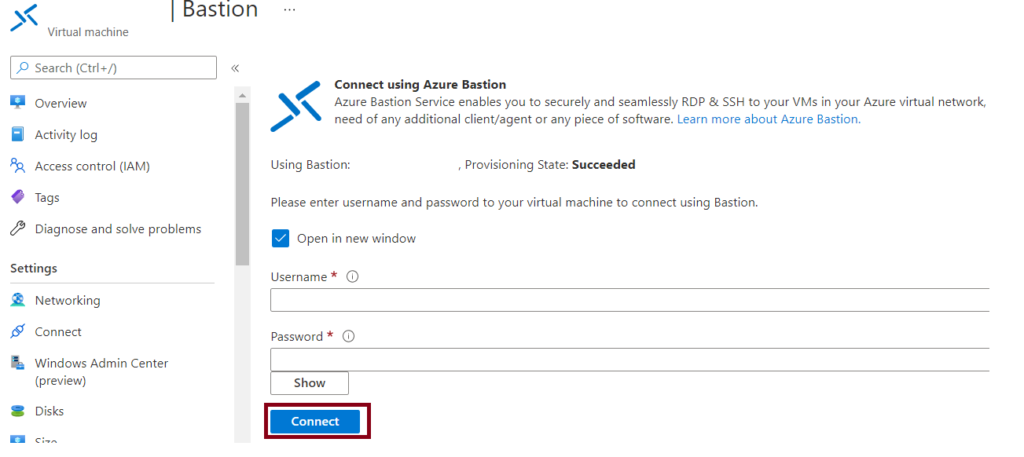
- Here you can see RDP connection for this VM will open in a new tab via Bastion that allow you to perform all the actions, This is using port 443 and the Bastion service.
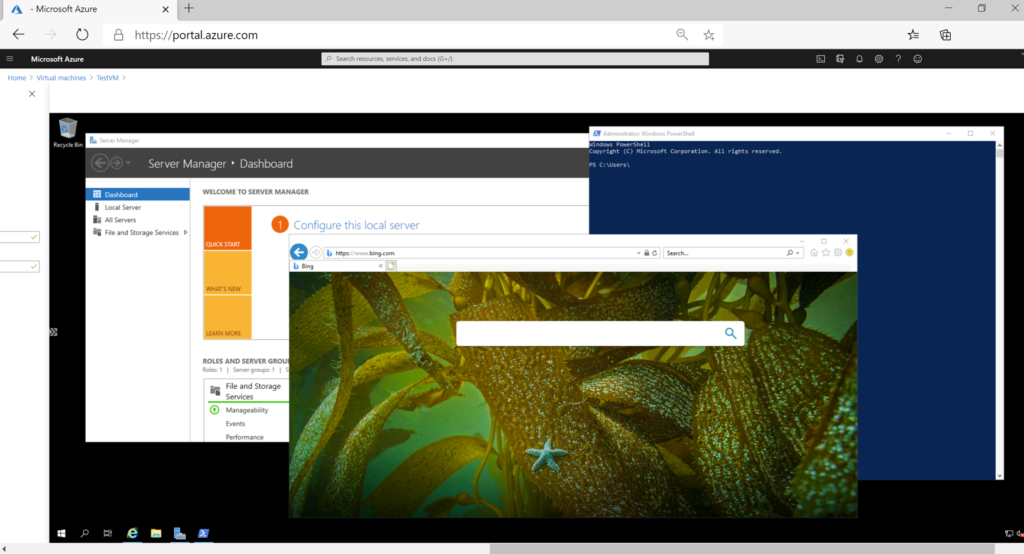


This is really great feature. The only drawback is if you need to copy some files or softwares, those you can’t copy to the VM as we can in RDP connection.
Yeah, but we can leverage many alternate options like OneDrive, google drive, etc.
New thing learned. This means to take RDP, do we have to login to azure portal every time?
Yes, Minimum access required for user to connect VM is mentioned on blog.
Good, highly secure.
New thing learned. So to take RDP, do we have to login to Azure portal every time?