This post will help you understand the Allow Cortana Above Lock Screen Policy Using Intune. We are going to use Configuration Profiles of Intune to implement this policy. Our main purpose here is to help you acquire knowledge of how to block the Allow Cortana Above Lock Screen Policy Using Intune.
Introduced in Windows 10, version 1607, this setting determines whether the user can engage with Cortana using speech when the system is locked. Enabling or leaving this setting unconfigured allows the user to interact with Cortana using speech while the system is locked. Conversely, if you disable this setting, the system will require unlocking before the user can use speech to interact with Cortana.
If you enable this setting or leave it unconfigured (which is the default), it allows users to interact with Cortana using speech even when the Windows system is locked. If you disable this setting, it restricts Cortana’s voice interaction capabilities when the system is locked. Users must unlock the computer before they can use voice commands with Cortana. Here we are disabling this policy.
The purpose of this setting is to provide administrators with a way to balance security and convenience. Allowing Cortana to be used while the system is locked can be convenient for users who want quick access to information or perform certain tasks without fully unlocking the computer. However, in some security-conscious environments, administrators may prefer to disable this feature to ensure that sensitive information or actions are not accessible without authentication.
It’s important to note that this setting only affects Cortana’s behaviour when the system is locked. Cortana can typically be used with voice commands when the system is unlocked, regardless of this setting. Additionally, the availability and behaviour of Cortana features may vary depending on the Windows version and updates applied.
- Help Experience Improvement Program Policy using Intune
- Turn Off the Picture Password Sign-In Policy using Intune
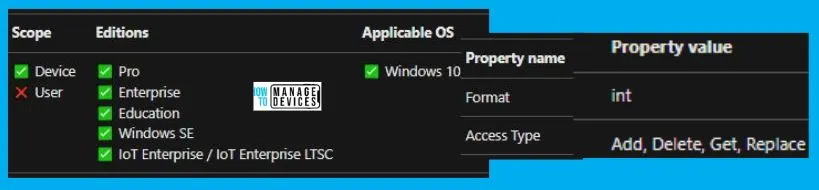
Windows CSP Details AllowCortanaAboveLock
We will see Windows CSP Details for this Policy setting AllowCortanaAboveLock. This setting is part of the Group Policy settings in Windows and is primarily designed for administrators to control the behaviour of Cortana when the system is locked. Cortana is Microsoft’s digital assistant and can be used for various tasks, including voice interactions.
CSP URI – ./Device/Vendor/MSFT/Policy/Config/AboveLock/AllowCortanaAboveLock
Allow Cortana to Above Lock Screen Policy using Intune
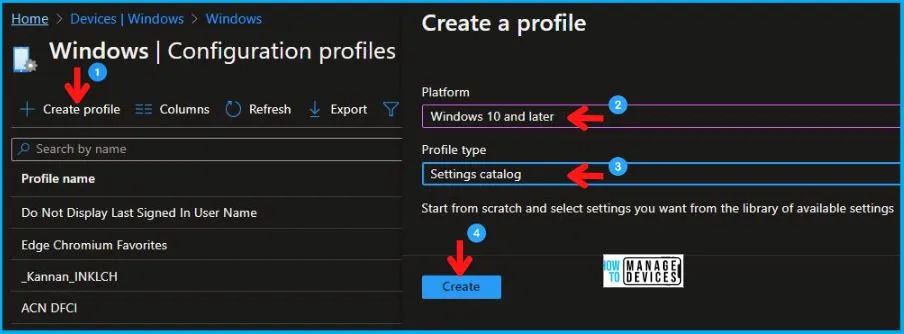
To block the Allow Cortana Above Lock Screen Policy Using Intune, follow the steps stated below:
- Sign in to the Intune Admin Center portal https://intune.microsoft.com/.
- Select Devices > Windows > Configuration profiles > Create a profile.
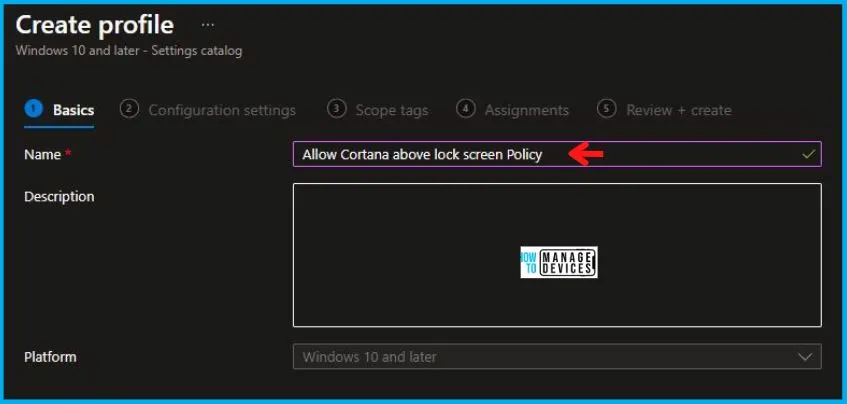
In Create Profile, I select Windows 10 and later in Platform and select Profile Type as Settings catalog. Click on the Create button.
| Platform | Profile Type |
|---|---|
| Windows 10 and later | Settings Catalog |
On the Basics tab pane, I provide a name for the policy as “Allow Cortana Above Lock Screen Policy.” Optionally, if you want, you can enter a policy description and proceed by selecting “Next.
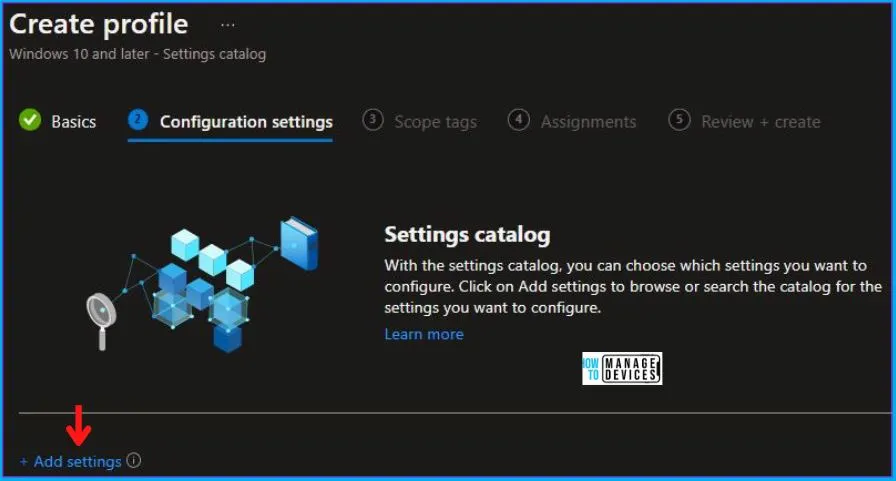
Now in Configuration Settings, click Add Settings to browse or search the catalog for the settings I want to configure.
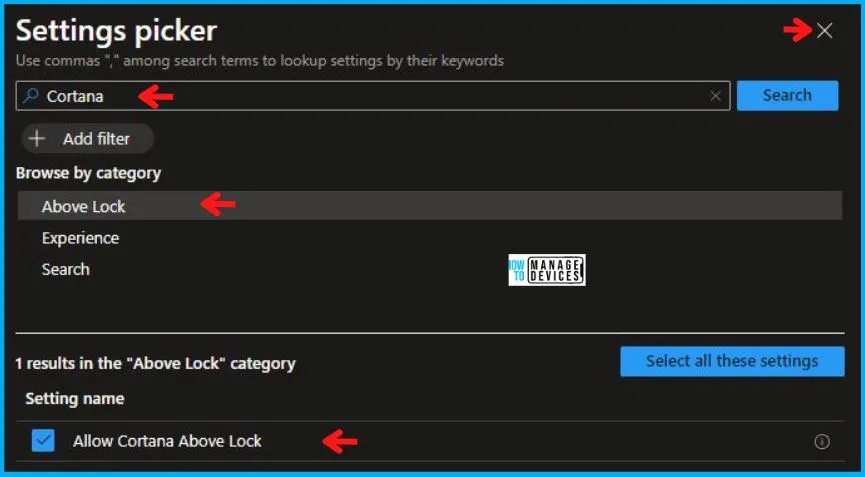
In the Settings Picker windows, I searched for the keyword Cortana, I found the category Above lock and selected this.
When I select that option as stated above, I see the sub-category, Allow Cortana Above Lock. After selecting that, click the cross mark at the right-hand corner, as shown below.
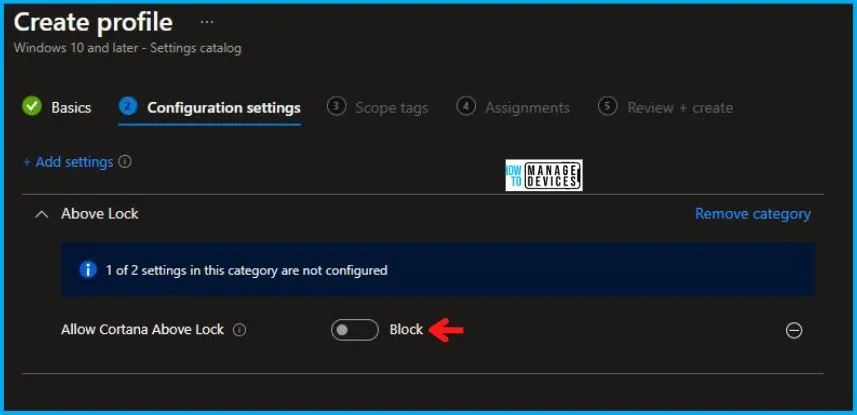
I kept the Allow Cortana Above Lock as Block and clicked on Next to continue.
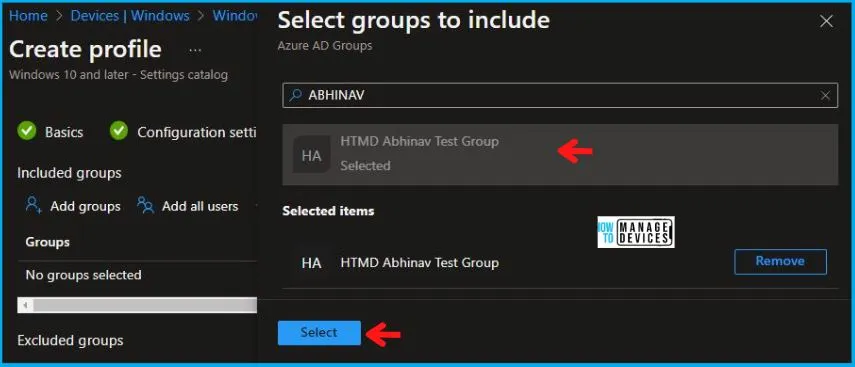
Using Scope tags, you can assign a tag to filter the profile to specific IT groups. One can add scope tags (if required) and click Next to continue. Now in Assignments, in Included Groups, you need to click on Add Groups, choose Select Groups to include one or more groups, and click Next to continue.
In the Review + Create tab, I review settings. After clicking on Create, changes are saved, and the profile is assigned.
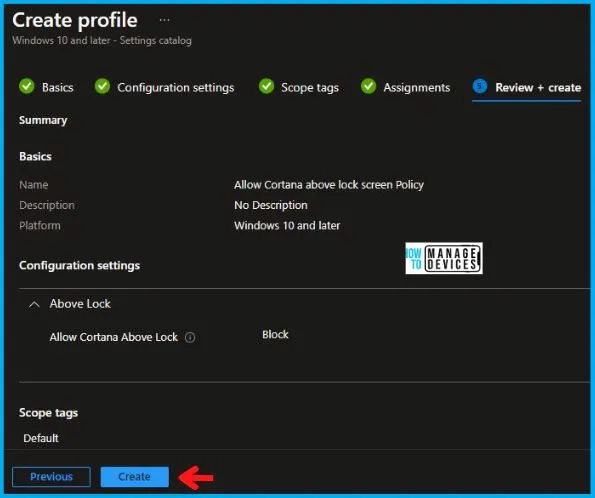
Upon successfully creating the “Allow Cortana Above Lock Screen Policy,“ notification will appear in the top right-hand corner, confirming the action. You can also verify the policy’s existence by navigating to the Configuration Profiles list, where it will be prominently displayed.
Your groups will receive your profile settings when the devices check in with the Intune service. The Policy applies to the device.
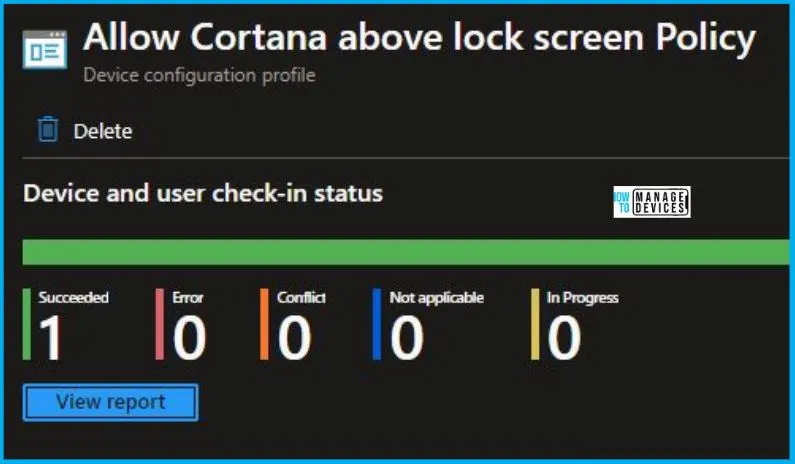
Intune Report for Allow Cortana Above Lock Screen Policy
From Intune Portal, you can view the Intune settings catalog profile report, which provides an overview of device configuration policies and deployment status.
To track the assignment of the policy, you need to select the relevant policy from the Configuration Profiles list. Reviewing the device and user check-in status lets you determine if the policy has been successfully applied. If you require more detailed information, you can click on “View Report” to access additional insights.
Intune MDM Event Log
To verify the successful implementation of String or integer policies on Windows 10 or 11 devices through Intune, you can leverage event IDs 813 and 814. These event IDs provide valuable insights into the application status of the policy as well as the specific value assigned to the policy on those devices. In the case of this particular policy, the value is an Integer and is linked to the event ID 813.
By analyzing these event IDs, you can gain a clear understanding of the policy’s application status and the corresponding value associated with it on the devices in question.
To confirm this, you can check the Event log path – Applications and Services Logs – Microsoft – Windows – Devicemanagement-Enterprise-Diagnostics-Provider – Admin.
MDM PolicyManager: Set policy string, Policy: (AllowCortanaAboveLock), Area: (AboveLock), EnrollmentID requesting merge: (5B88AEF1-09E8-43BB-B144-7254ACBBDF3E), Current User: (Device), Int: (0x0), Enrollment Type: (0x6), Scope: (0x0).
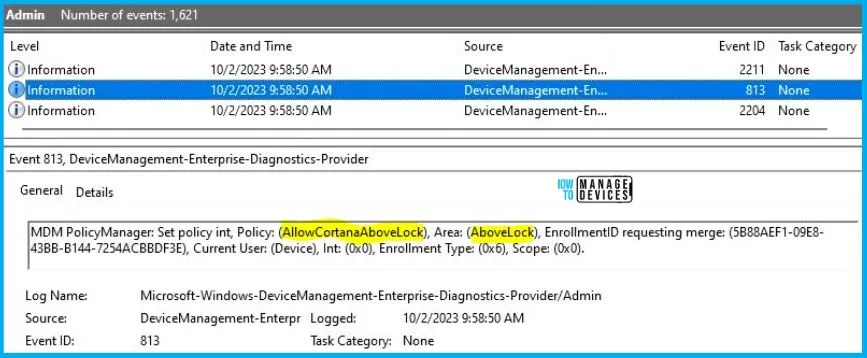
When I opened the above Event log, I found that the policy I have applied to the device has been successfully implemented. By reviewing the log entry shown in the above image, the Event Viewer, I came across essential information, including the Area and Enrollment ID. These details play a significant role in identifying the corresponding registry path. To locate the specific information, please consult the table provided below:
| Area | Policy | Integer | Scoped | Event ID |
|---|---|---|---|---|
| AboveLock | AllowCortanaAboveLock | Disabled | Device | 813 |
The details presented in the table above for the Allow Cortana Above Lock Screen Policy Using Intune can be employed to access the registry settings that hold the group policy configurations on a specific computer. To accomplish this, you can execute “REGEDIT.exe” on the target computer and navigate to the precise registry path where these settings are stored.
- Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PolicyManager\providers\5B88AEF1-09E8-43BB-B144-7254ACBBDF3E\default\Device\AboveLock
When you navigate the above path in the Registry Editor, you will find the registry key named