Key Takeaways
- Multiple Remote Code Execution (RCE) flaws could allow full system compromise without user interaction.
- High-impact vulnerabilities here can lead to complete domain takeover in enterprise environments.
- Don’t ignore lower-severity issues if they’re actively used in attacks.
- Privilege escalation bugs can combine with RCE to gain full control.
- Microsoft Office and RDP vulnerabilities make phishing and remote attacks highly effective.
April 2026 Security Update | Critical and High-Risk Vulnerabilities You Must Patch Immediately! The April 2026 update includes several Remote Code Execution (RCE) vulnerabilities, which makes it very important to apply patches quickly. These flaws can let attackers run malicious code on your system remotely, sometimes without any action from the user, making them highly dangerous.
Table of Content
Table of Contents
April 2026 Security Update | Critical and High-Risk Vulnerabilities You Must Patch Immediately
Some of the biggest risks are in Active Directory and network-facing components. If these are exploited, attackers could take control of entire systems or even whole networks, leading to serious security breaches if not fixed in time. The below table helps you to show the number of bugs in each vulnerability category is listed below.
| Vulnerabilities |
|---|
| 93 Elevation of Privilege Vulnerabilities |
| 13 Security Feature Bypass Vulnerabilities |
| 20 Remote Code Execution Vulnerabilities |
| 21 Information Disclosure Vulnerabilities |
| 10 Denial of Service Vulnerabilities |
| 9 Spoofing Vulnerabilities |
- Windows 11 KB5083769 KB5082052 April 2026 Patch and 2 Zero Day Vulnerabilities and 167 Flaws
- Windows 11 Version Numbers Build Numbers Major Minor Build Rev
- Updated Windows 11 End-of-Life Dates
- Top 83 Windows 11 Desktop Admin Interview Questions
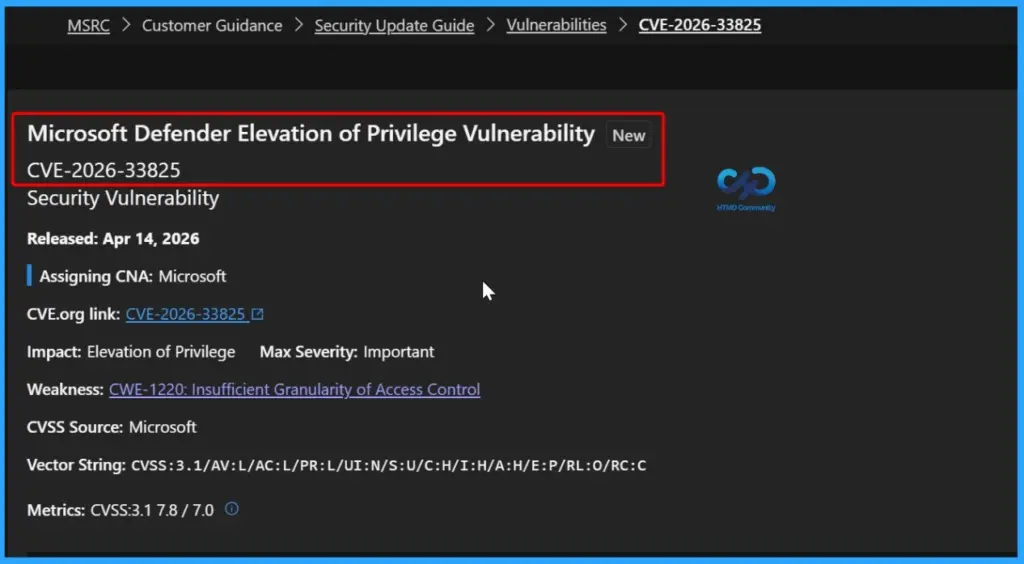
93 Elevation of Privilege Vulnerabilities
A total of 93 Elevation of Privilege vulnerabilities have been identified across a range of Microsoft products and services. These vulnerabilities could allow attackers with limited access to gain higher-level permissions, potentially compromising system integrity and sensitive data.
- CVE Title
- Microsoft Defender Elevation of Privilege Vulnerability
- Win32k Elevation of Privilege Vulnerability
- Windows Print Spooler Elevation of Privilege Vulnerability
- Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
- Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
- Windows Container Isolation FS Filter Driver Elevation of Privilege Vulnerability
- Windows Server Update Service (WSUS) Elevation of Privilege Vulnerability
- Windows USB Printing Stack (usbprint.sys) Elevation of Privilege Vulnerability
- Windows Win32k Elevation of Privilege Vulnerability
- Microsoft Brokering File System Elevation of Privilege Vulnerability
- Windows Kernel Elevation of Privilege Vulnerability
- Azure Monitor Agent Elevation of Privilege Vulnerability
- Microsoft High Performance Compute (HPC) Pack Elevation of Privilege Vulnerability
- SQL Server Elevation of Privilege Vulnerability
- Azure Logic Apps Elevation of Privilege Vulnerability
- Azure Monitor Agent Elevation of Privilege Vulnerability
- SQL Server Elevation of Privilege Vulnerability
- Windows User Interface Core Elevation of Privilege Vulnerability
- Windows User Interface Core Elevation of Privilege Vulnerability
- Windows User Interface Core Elevation of Privilege Vulnerability
- Windows COM Elevation of Privilege Vulnerability
- Windows Push Notifications Elevation of Privilege Vulnerability
- Windows Push Notifications Elevation of Privilege Vulnerability
- Windows Push Notifications Elevation of Privilege Vulnerability
- Desktop Window Manager Elevation of Privilege Vulnerability
- Desktop Window Manager Elevation of Privilege Vulnerability
- Windows Speech Runtime Elevation of Privilege Vulnerability
- Desktop Window Manager Elevation of Privilege Vulnerability
- Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability
- Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability
- Microsoft Brokering File System Elevation of Privilege Vulnerability
- Windows Speech Brokered Api Elevation of Privilege Vulnerability
- Windows Speech Brokered Api Elevation of Privilege Vulnerability
- Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability
- Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability
- Windows Simple Search and Discovery Protocol (SSDP) Service Elevation of Privilege Vulnerability
- Windows Simple Search and Discovery Protocol (SSDP) Service Elevation of Privilege Vulnerability
- Windows WalletService Elevation of Privilege Vulnerability
- Windows Projected File System Elevation of Privilege Vulnerability
- Windows UPnP Device Host Elevation of Privilege Vulnerability
- Windows Storage Spaces Controller Elevation of Privilege Vulnerability
- Windows UPnP Device Host Elevation of Privilege Vulnerability
- Windows Projected File System Elevation of Privilege Vulnerability
- Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
- Windows Common Log File System Driver Elevation of Privilege Vulnerability
- Windows Projected File System Elevation of Privilege Vulnerability
- Windows Simple Search and Discovery Protocol (SSDP) Service Elevation of Privilege Vulnerability
- Windows LUA File Virtualization Filter Driver Elevation of Privilege Vulnerability
- Windows Projected File System Elevation of Privilege Vulnerability
- Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability
- Desktop Window Manager Elevation of Privilege Vulnerability
- Desktop Window Manager Elevation of Privilege Vulnerability
- Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
- Windows TDI Translation Driver (tdx.sys) Elevation of Privilege Vulnerability
- Windows UPnP Device Host Elevation of Privilege Vulnerability
- Windows UPnP Device Host Elevation of Privilege Vulnerability
- Windows Shell Elevation of Privilege Vulnerability
- Windows WFP NDIS Lightweight Filter Driver (wfplwfs.sys) Elevation of Privilege Vulnerability
- Windows UPnP Device Host Elevation of Privilege Vulnerability
- Windows UPnP Device Host Elevation of Privilege Vulnerability
- Microsoft Management Console Elevation of Privilege Vulnerability
- Windows Kerberos Elevation of Privilege Vulnerability
- Windows User Interface Core Elevation of Privilege Vulnerability
- Windows Installer Elevation of Privilege Vulnerability
- Windows Search Service Elevation of Privilege Vulnerability
- Windows TDI Translation Driver (tdx.sys) Elevation of Privilege Vulnerability
- Windows Storage Spaces Controller Elevation of Privilege Vulnerability
- Windows Projected File System Elevation of Privilege Vulnerability
- Remote Access Management service/API (RPC server) Elevation of Privilege Vulnerability
- Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
- Microsoft Brokering File System Elevation of Privilege Vulnerability
- Windows Kernel Elevation of Privilege Vulnerability
- Windows Kernel Elevation of Privilege Vulnerability
- Windows Advanced Rasterization Platform Elevation of Privilege Vulnerability
- Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
- Windows Client Side Caching driver (csc.sys) Elevation of Privilege Vulnerability
- Windows Server Update Service (WSUS) Elevation of Privilege Vulnerability
- Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
- Windows Push Notifications Elevation of Privilege Vulnerability
- PowerShell Elevation of Privilege Vulnerability
- Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
- Windows Push Notifications Elevation of Privilege Vulnerability
- Windows Shell Elevation of Privilege Vulnerability
- Windows Shell Elevation of Privilege Vulnerability
- Windows Kernel Elevation of Privilege Vulnerability
- Windows OLE Elevation of Privilege Vulnerability
- Windows Sensor Data Service Elevation of Privilege Vulnerability
- Remote Desktop Licensing Service Elevation of Privilege Vulnerability
- Remote Desktop Licensing Service Elevation of Privilege Vulnerability
- Windows Encrypted File System (EFS) Elevation of Privilege Vulnerability
- Microsoft Cryptographic Services Elevation of Privilege Vulnerability
- Applocker Filter Driver (applockerfltr.sys) Elevation of Privilege Vulnerability
- Windows Management Services Elevation of Privilege Vulnerability
- Windows Admin Centre Elevation of Privilege Vulnerability
- LIBPNG is vulnerable to a heap buffer overflow in
png_combine_rowtriggered viapng_image_finish_read - LIBPNG is vulnerable to a buffer overflow in
png_image_read_compositevia incorrect palette premultiplication
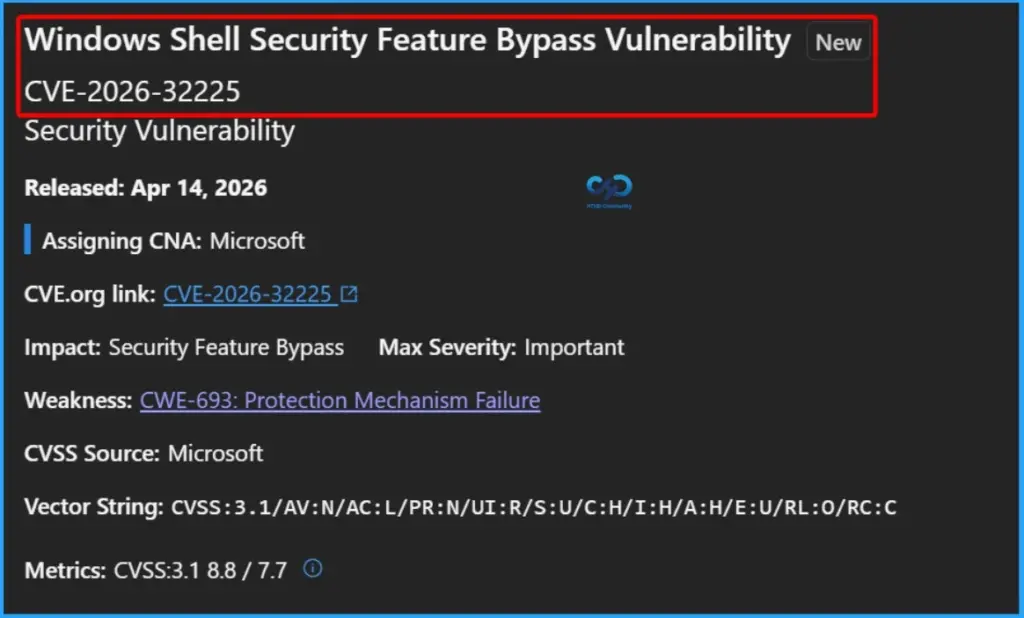
13 Security Feature Bypass Vulnerabilities
A set of security feature bypass vulnerabilities has been identified across multiple Windows components and security mechanisms. These include weaknesses in critical protections such as Windows Shell, UEFI Secure Boot, Windows Hello, BitLocker, Boot Manager, and Virtualisation-Based Security (VBS), as well as services like Windows Biometric Service, Recovery Environment, and Microsoft PowerShell.
- CVE-2026-32225 Windows Shell Security Feature Bypass Vulnerability
- CVE-2026-32220 UEFI Secure Boot Security Feature Bypass Vulnerability
- CVE-2026-32088 Windows Biometric Service Security Feature Bypass Vulnerability
- CVE-2026-27928 Windows Hello Security Feature Bypass Vulnerability
- CVE-2026-27913 Windows BitLocker Security Feature Bypass Vulnerability
- CVE-2026-27906 Windows Hello Security Feature Bypass Vulnerability
- CVE-2026-26175 Windows Boot Manager Security Feature Bypass Vulnerability
- CVE-2026-26143 Microsoft PowerShell Security Feature Bypass Vulnerability
- CVE-2026-23670 Windows Virtualization-Based Security (VBS) Security Feature Bypass Vulnerability
- CVE-2026-20928 Windows Recovery Environment Security Feature Bypass Vulnerability
- CVE-2026-0390 UEFI Secure Boot Security Feature Bypass Vulnerability
- CVE-2026-25250 MITRE: CVE-2026-25250 Secure Boot disable Eazy Fix
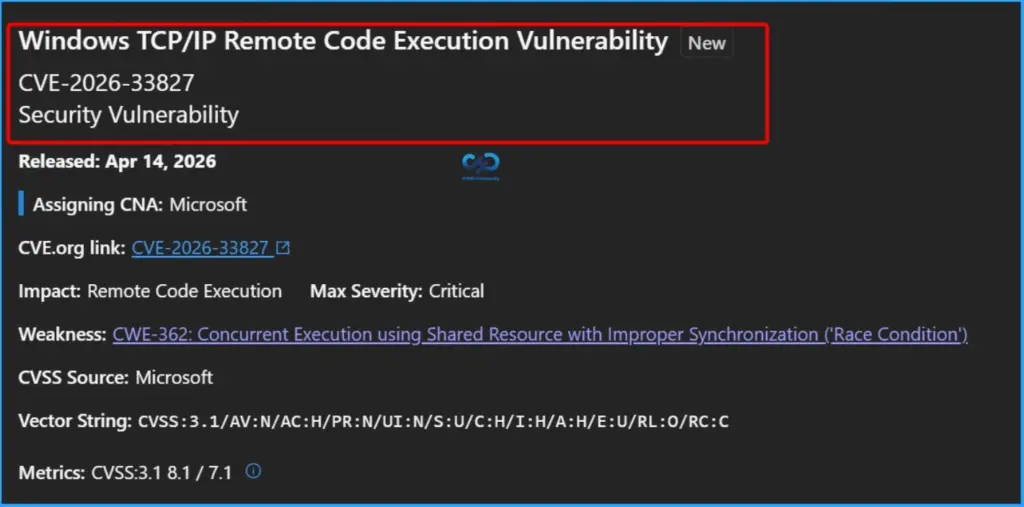
20 Remote Code Execution Vulnerabilities
Several remote code execution (RCE) vulnerabilities have been identified across a wide range of Microsoft products and services. These include critical components such as Windows TCP/IP, Active Directory, Internet Key Exchange (IKE), and Hyper-V, as well as widely used applications like Microsoft Word, Excel, PowerPoint, and the broader Microsoft Office suite.
- CVE-2026-33827 Windows TCP/IP Remote Code Execution Vulnerability
- CVE-2026-33826 Windows Active Directory Remote Code Execution Vulnerability
- CVE-2026-33824 Windows Internet Key Exchange (IKE) Service Extensions Remote Code Execution Vulnerability
- CVE-2026-33120 Microsoft SQL Server Remote Code Execution Vulnerability
- CVE-2026-33115 Microsoft Word Remote Code Execution Vulnerability
- CVE-2026-33114 Microsoft Word Remote Code Execution Vulnerability
- CVE-2026-33095 Microsoft Word Remote Code Execution Vulnerability
- CVE-2026-32221 Windows Graphics Component Remote Code Execution Vulnerability
- CVE-2026-32200 Microsoft PowerPoint Remote Code Execution Vulnerability
- CVE-2026-32199 Microsoft Excel Remote Code Execution Vulnerability
- CVE-2026-32198 Microsoft Excel Remote Code Execution Vulnerability
- CVE-2026-32197 Microsoft Excel Remote Code Execution Vulnerability
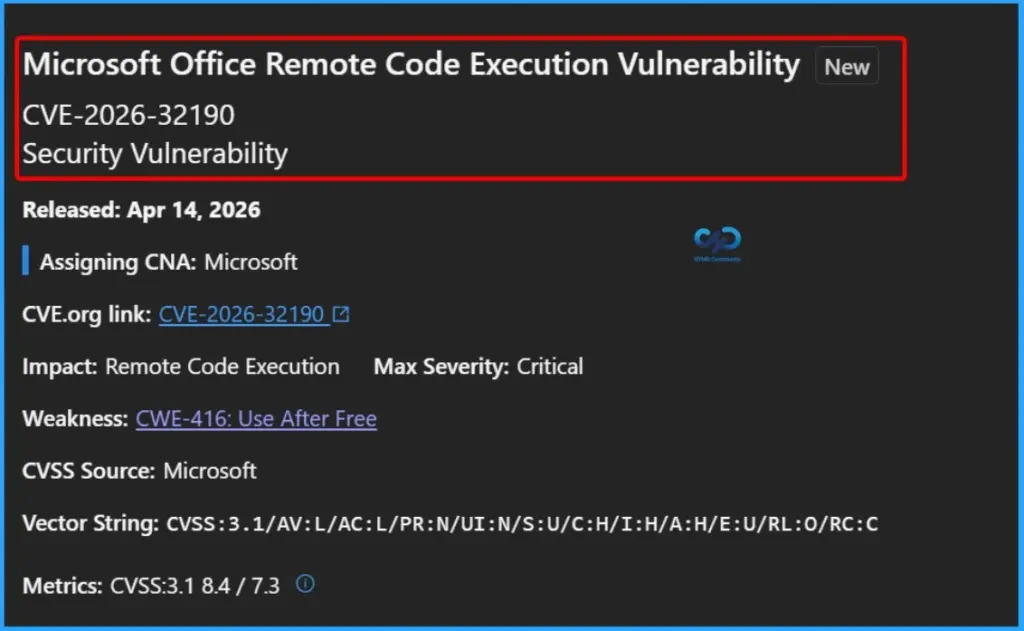
- CVE-2026-32190 Microsoft Office Remote Code Execution Vulnerability
- CVE-2026-32189 Microsoft Excel Remote Code Execution Vulnerability
- CVE-2026-32183 Windows Snipping Tool Remote Code Execution Vulnerability
- CVE-2026-32157 Remote Desktop Client Remote Code Execution Vulnerability
- CVE-2026-32156 Windows UPnP Device Host Remote Code Execution Vulnerability
- CVE-2026-32149 Windows Hyper-V Remote Code Execution Vulnerability
- CVE-2026-26156 Windows Hyper-V Remote Code Execution Vulnerability
- CVE-2026-23657 Microsoft Word Remote Code Execution Vulnerability
- CVE-2026-21523 GitHub Copilot and Visual Studio Code Remote Code Execution Vulnerability
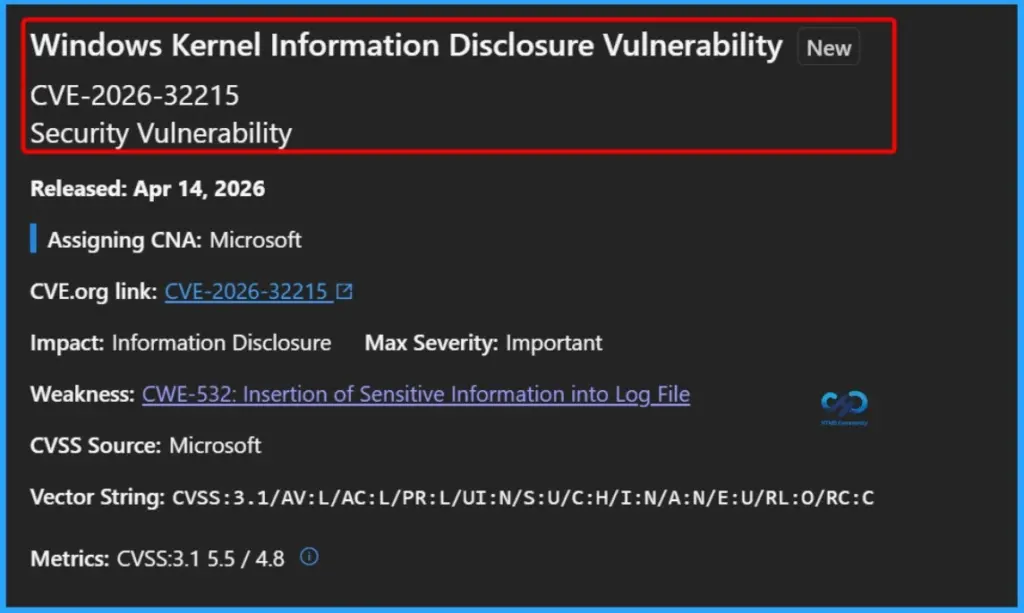
21 Information Disclosure Vulnerabilities
A total of 21 information disclosure vulnerabilities have been identified across various Microsoft components and services. These vulnerabilities affect critical areas such as the Windows Kernel, Remote Procedure Call (RPC), Windows Shell, Print Spooler, Web Account Manager, and Windows GDI, as well as applications like Microsoft Excel and development tools including GitHub Copilot and Visual Studio Code.
- CVE-2026-32215 Windows Kernel Information Disclosure Vulnerability
- CVE-2026-32214 Universal Plug and Play (upnp.dll) Information Disclosure Vulnerability
- CVE-2026-32212 Universal Plug and Play (upnp.dll) Information Disclosure Vulnerability
- CVE-2026-32188 Microsoft Excel Information Disclosure Vulnerability
- CVE-2026-32151 Windows Shell Information Disclosure Vulnerability
- CVE-2026-32085 Remote Procedure Call Information Disclosure Vulnerability
- CVE-2026-32084 Windows Print Spooler Information Disclosure Vulnerability
- CVE-2026-32081 Package Catalog Information Disclosure Vulnerability
- CVE-2026-32079 Web Account Manager Information Disclosure Vulnerability
- CVE-2026-27931 Windows GDI Information Disclosure Vulnerability
- CVE-2026-27930 Windows GDI Information Disclosure Vulnerability
- CVE-2026-27925 Windows UPnP Device Host Information Disclosure Vulnerability
- CVE-2026-26169 Windows Kernel Memory Information Disclosure Vulnerability
- CVE-2026-26155 Microsoft Local Security Authority Subsystem Service Information Disclosure Vulnerability
- CVE-2026-23653 GitHub Copilot and Visual Studio Code Information Disclosure Vulnerability
- CVE-2026-20806 Windows COM Server Information Disclosure Vulnerability
- CVE-2026-32631 GitHub: CVE-2026-32631 ‘git clone’ from manipulated repositories can leak NTLM hashes
10 Denial of Service Vulnerabilities
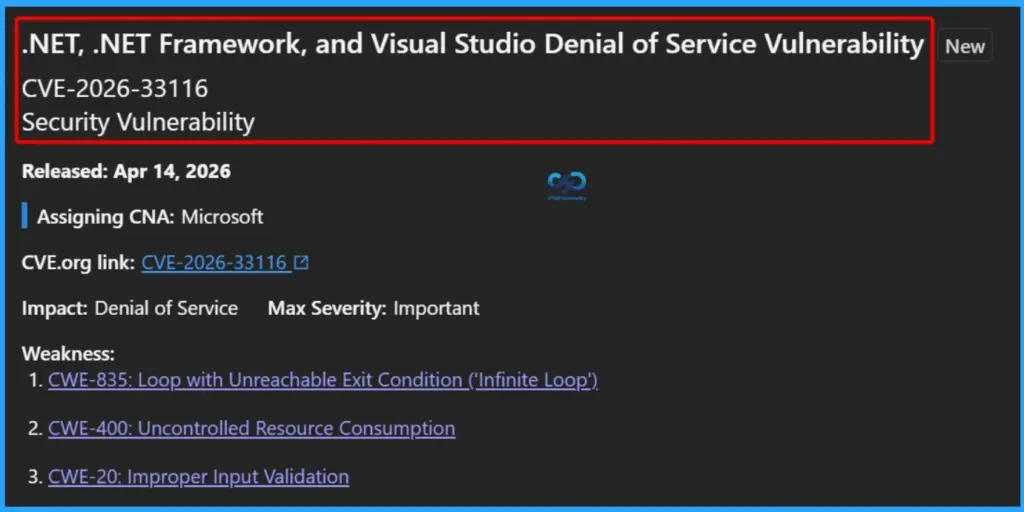
A total of 10 denial of service (DoS) vulnerabilities have been identified across multiple Microsoft technologies and services. These include components such as .NET, .NET Framework, and Visual Studio, as well as core Windows services like HTTP.sys, LSASS, and the Windows Redirected Drive Buffering System. Additional affected areas include the Connected User Experiences and Telemetry Service.
- CVE-2026-33116 .NET, .NET Framework, and Visual Studio Denial of Service Vulnerability
- CVE-2026-33096 HTTP.sys Denial of Service Vulnerability
- CVE-2026-32226 .NET Framework Denial of Service Vulnerability
- CVE-2026-32216 Windows Redirected Drive Buffering System Denial of Service Vulnerability
- CVE-2026-32203 .NET and Visual Studio Denial of Service Vulnerability
- CVE-2026-32181 Connected User Experiences and Telemetry Service Denial of Service Vulnerability
- CVE-2026-32071 Windows Local Security Authority Subsystem Service (LSASS) Denial of Service Vulnerability
- CVE-2026-26171 .NET Denial of Service Vulnerability
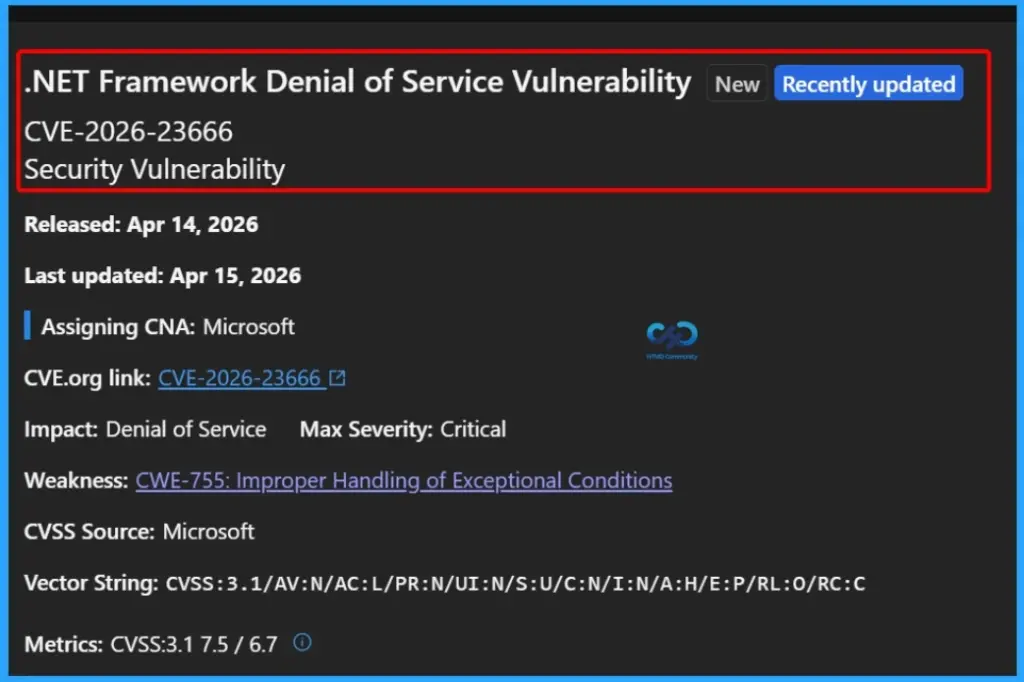
- CVE-2026-23666 .NET Framework Denial of Service Vulnerability
- CVE-2026-21637 HackerOne: CVE-2026-21637 TLS PSK/ALPN Callback Exceptions Bypass Error Handlers
9 Spoofing Vulnerabilities
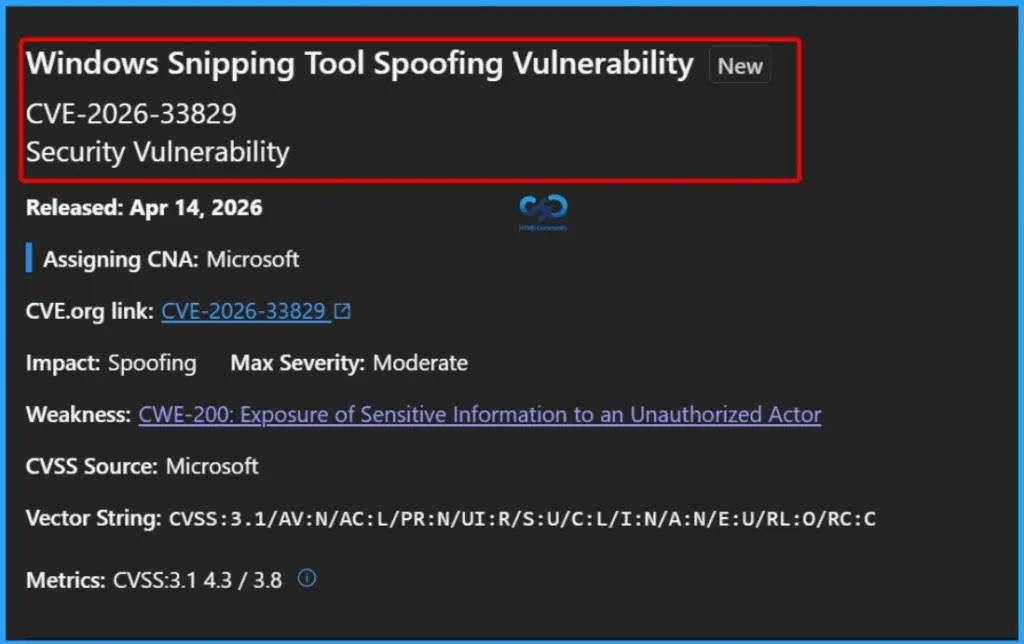
A set of 9 spoofing vulnerabilities has been identified across several Microsoft products and services, affecting components such as Windows Snipping Tool, Windows Shell, Active Directory, and Remote Desktop, along with platforms like Microsoft SharePoint Server, Windows Admin Center, .NET, and Microsoft Power Apps. These vulnerabilities may enable attackers to impersonate legitimate users, services, or systems, thereby undermining trust mechanisms and potentially leading to unauthorized access or social engineering attacks.
- CVE-2026-33829 Windows Snipping Tool Spoofing Vulnerability
- CVE-2026-32202 Windows Shell Spoofing Vulnerability
- CVE-2026-32201 Microsoft SharePoint Server Spoofing Vulnerability
- CVE-2026-32196 Windows Admin Center Spoofing Vulnerability
- CVE-2026-32178 .NET Spoofing Vulnerability
- CVE-2026-32072 Active Directory Spoofing Vulnerability
- CVE-2026-26151 Remote Desktop Spoofing Vulnerability
- CVE-2026-26149 Microsoft Power Apps Spoofing Vulnerability
- CVE-2026-20945 Microsoft SharePoint Server Spoofing Vulnerability
Critical .NET Framework Denial of Service Vulnerability (CVE-2026-23666)
CVE-2026-23666 is a critical denial of service vulnerability in the .NET Framework, disclosed on April 14, 2026. It is not currently known to be exploited and is considered less likely to be attacked. However, it could still allow attackers to make applications or systems crash or stop responding. Due to its critical severity, organizations should apply updates quickly and monitor systems to avoid disruptions.
Critical Microsoft Office Remote Code Execution Vulnerability (CVE-2026-32190)
CVE-2026-32190 is a critical remote code execution vulnerability in Microsoft Office, disclosed on April 14, 2026. It is not currently being exploited and is considered less likely to be attacked. However, it could allow attackers to run malicious code on a system, potentially leading to full compromise. Organisations should apply updates as soon as possible to stay protected.
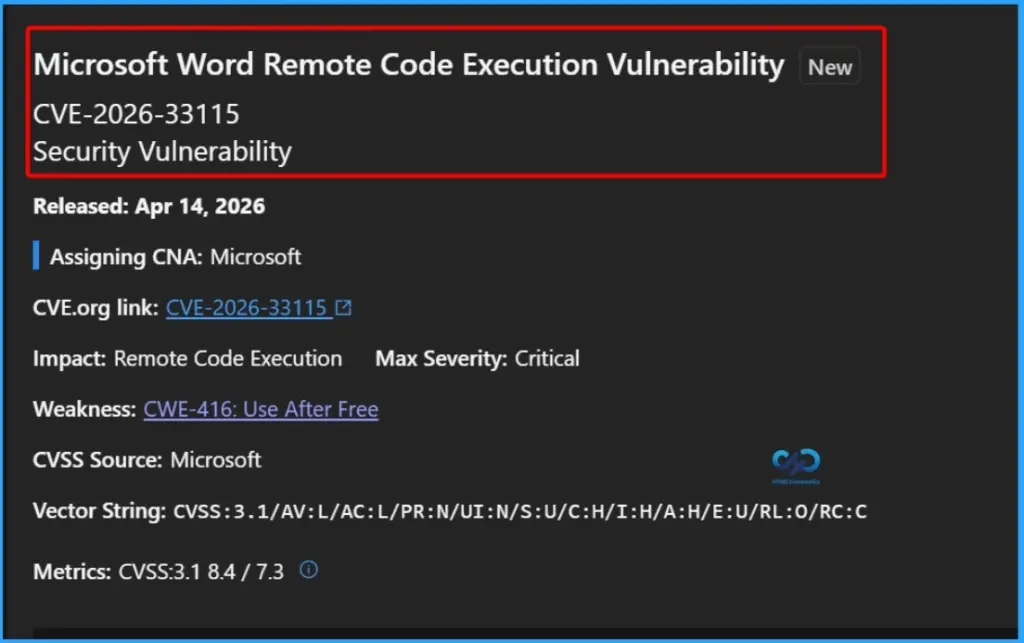
Critical Microsoft Word Remote Code Execution Vulnerability (CVE-2026-33115)
CVE-2026-33115 is a critical remote code execution vulnerability in Microsoft Word, disclosed on April 14, 2026. It is not currently known to be exploited and is considered less likely to be targeted. However, it could allow attackers to run malicious code on affected systems. Organizations should apply security updates quickly to reduce risk.
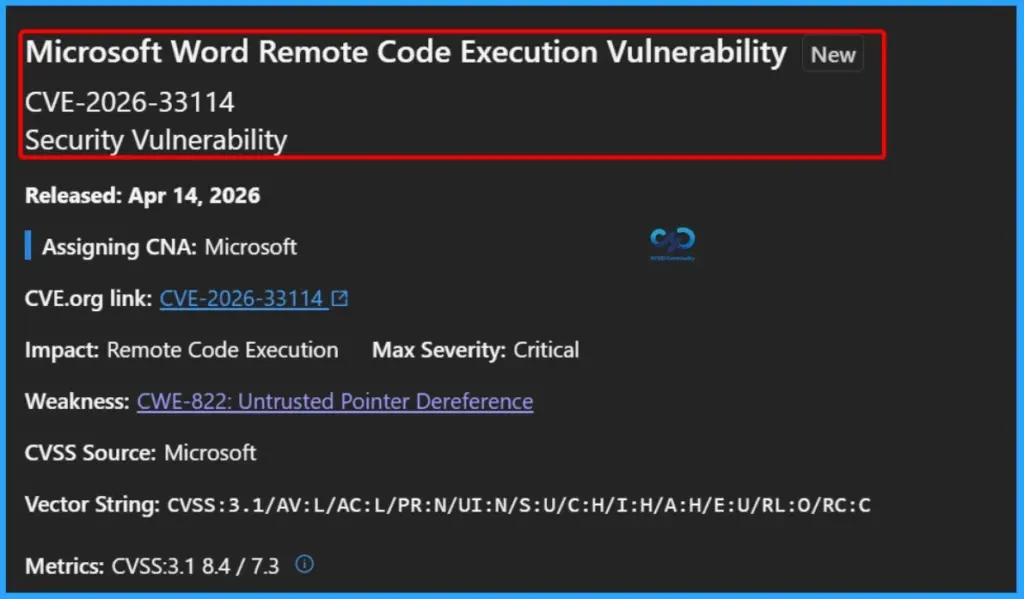
Critical Microsoft Word Remote Code Execution Vulnerability (CVE-2026-33114)
CVE-2026-33114 is a critical remote code execution vulnerability in Microsoft Word, released on April 14, 2026. It is caused by an untrusted pointer dereference issue (CWE-822), which could allow attackers to execute malicious code on affected systems. The vulnerability has a high impact on confidentiality, integrity, and availability, with a CVSS score of 8.4. Although exploitation details are not widely available, organizations should apply security updates promptly to reduce potential risk.
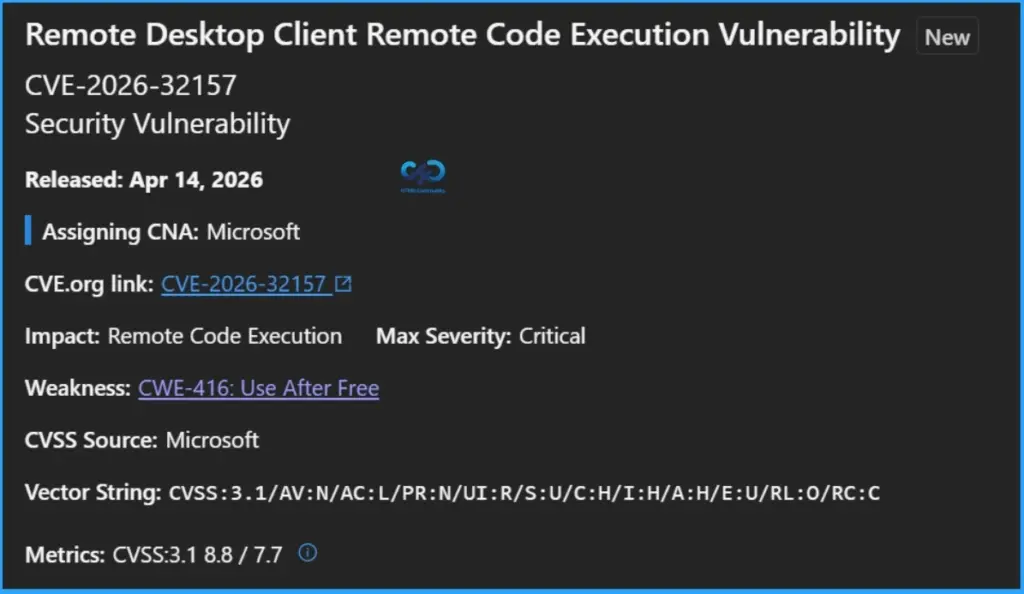
Critical Remote Desktop Client Remote Code Execution Vulnerability (CVE-2026-32157)
CVE-2026-32157 is a critical remote code execution vulnerability in the Remote Desktop Client, released on April 14, 2026. It is caused by a memory issue and could allow attackers to run malicious code on a system. The vulnerability has a high severity score of 8.8. Organizations should apply updates quickly to reduce the risk.
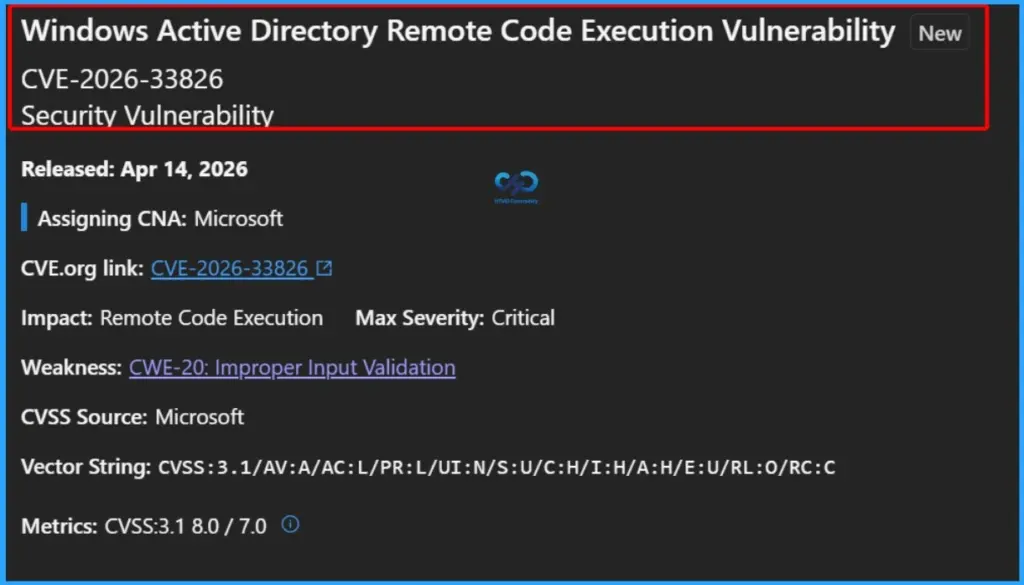
Critical Windows Active Directory Remote Code Execution Vulnerability (CVE-2026-33826)
CVE-2026-33826 is a critical remote code execution vulnerability in Windows Active Directory, released on April 14, 2026. It is caused by improper input validation (CWE-20), which could allow attackers to run malicious code on affected systems. Due to its critical severity, organizations should apply security updates as soon as possible to reduce risk.
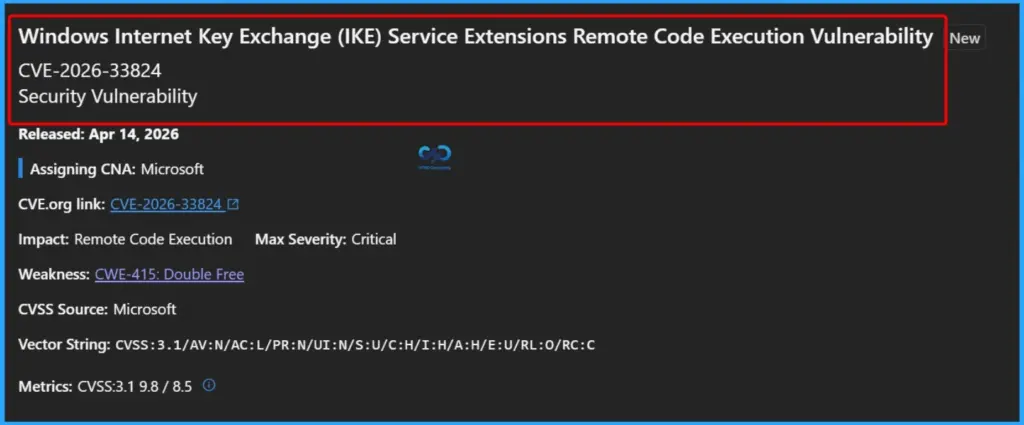
Critical Windows IKE Service Extensions Remote Code Execution Vulnerability (CVE-2026-33824)
CVE-2026-33824 is a critical remote code execution vulnerability in Windows Internet Key Exchange (IKE) Service Extensions. It could allow attackers to run malicious code on affected systems if exploited. Due to its critical severity, organizations should install security updates as soon as possible to stay protected.
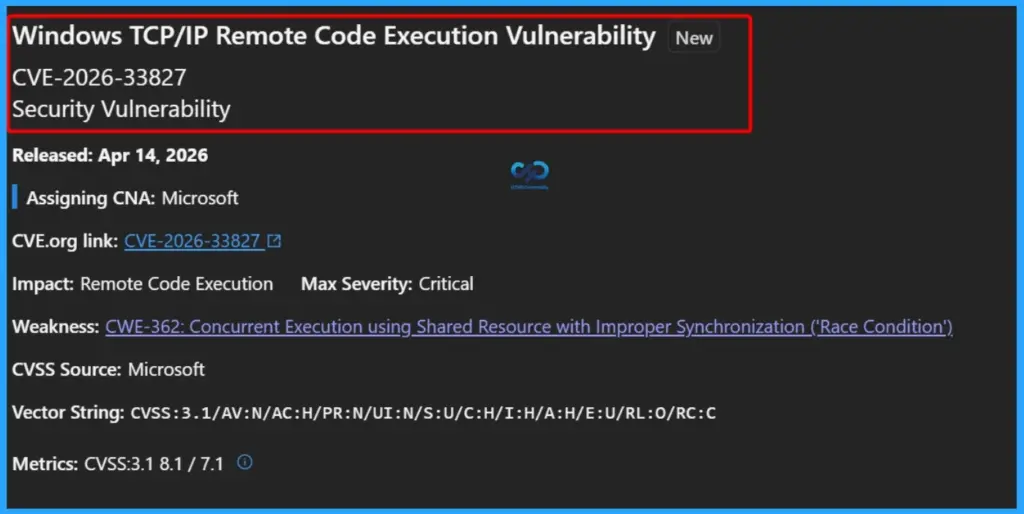
Critical Windows TCP/IP Remote Code Execution Vulnerability (CVE-2026-33827)
CVE-2026-33827 is a critical remote code execution vulnerability in the Windows TCP/IP component. It could allow attackers to run malicious code on affected systems. Due to its critical severity, organizations should apply security updates quickly to reduce risk.
Need Further Assistance or Have Technical Questions?
Join the LinkedIn Page and Telegram group to get the latest step-by-step guides and news updates. Join our Meetup Page to participate in User group meetings. Also, join the WhatsApp Community and the Whatsapp channel to get the latest news on Microsoft Technologies. We are there on Reddit as well
Author
Anoop C Nair has been Microsoft MVP for 10 consecutive years from 2015 onwards. He is a Workplace Solution Architect with more than 22+ years of experience in Workplace technologies. He is a Blogger, Speaker, and Local User Group Community leader. His primary focus is on Device Management technologies like SCCM and Intune. He writes about technologies like Intune, SCCM, Windows, Cloud PC, Windows, Entra, Microsoft Security, Career, etc.


