Hello everyone. Welcome to the HTMD community. Today we will discuss How to Block OS Updates on iOS Devices using Intune. In our previous blog posts, we learned how to add iOS devices to the ABM portal and enroll them in Intune. This post will discuss how to prevent users from updating their devices and force users to install OS updates as per organizational requirements.
Every organization wants to control the OS of the devices to protect corporate data from cyber-attacks. Regularly managing updates for your operating system is crucial. These updates offer new features and improvements while providing important security patches safeguarding your data from potential threats.
Users tend to ignore the OS updates on the devices. With the help of Intune, we can force users to update their devices to the latest version. Every OS update does not promise improvement in features. Sometimes, it may cause bugs that make your device vulnerable to threats. Users might update their devices that the organization does not approve, which may cause app compatibility issues.
With the help of Microsoft Endpoint Manager, we can block OS updates and force OS updates during off-business hours or specific times to reduce the impact on users’ work and the organization’s business. Let’s see below how we can block OS updates and force users to update a specific OS version using Intune.
- New Intune Settings for iOS iPadOS Web Clip App Deployment
- Intune Compliance Report for Device Settings
How to Block OS Updates on iOS Devices using Intune Configuration Policy
We must create a Configuration policy that defers the OS updates on the end user’s device to block OS updates or install any specific OS version. We can restrict users from updating their devices to a maximum of 90 days. Let’s see how to create a device restriction to block OS updates
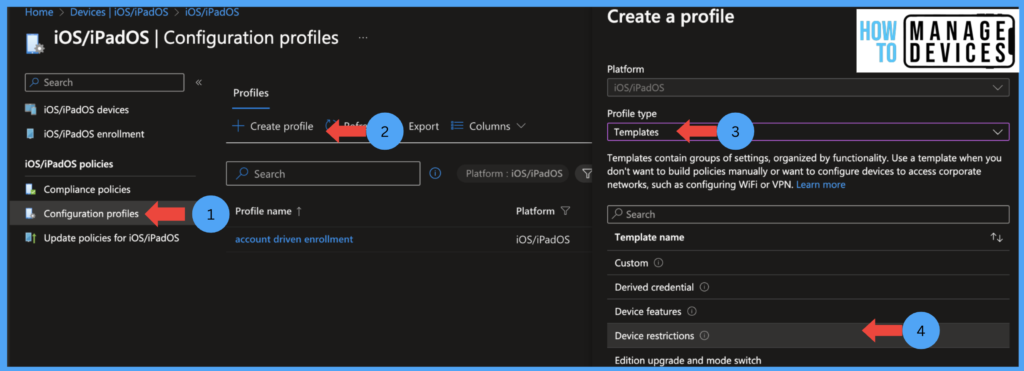
- Sign in to the Microsoft Endpoint Manager Admin Centre https://intune.microsoft.com.
- Click on Devices > iOS/iPadOS > Configuration profiles
- Click on Create Profiles
- Under Profile types, select Template
- Now select Device Restrictions and click Create
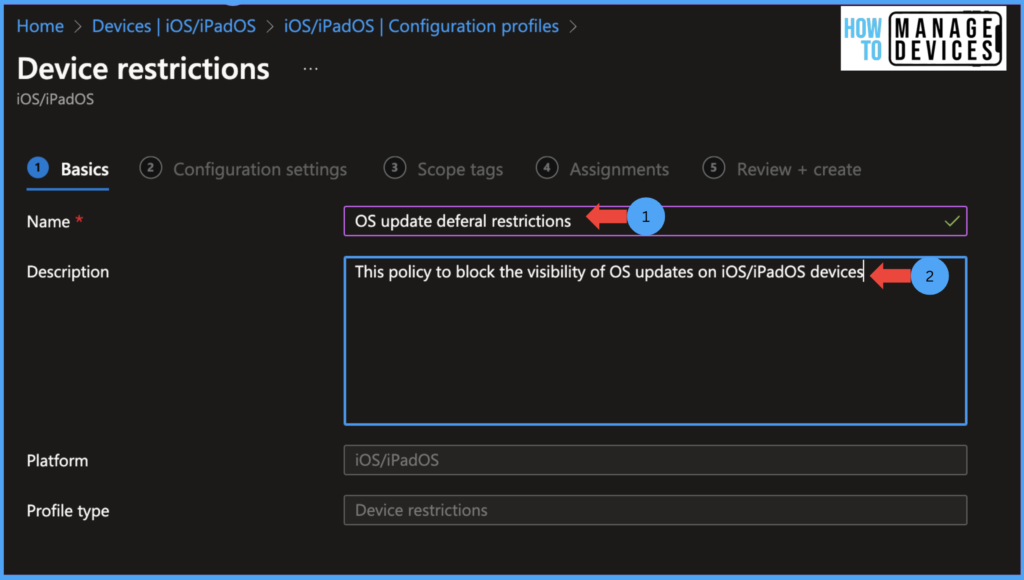
Now on the Basics Page, provide the configuration policy’s Name and Description and click Next.
Now on the Configuration Settings page, click on the General tab, scroll to the bottom and look for Defer software updates, toggle the button to Yes. This will enable Delay default visibility of the software updates field. Now enter the number of days you want to defer the OS updates for the users. The value must be between 1-90 days.
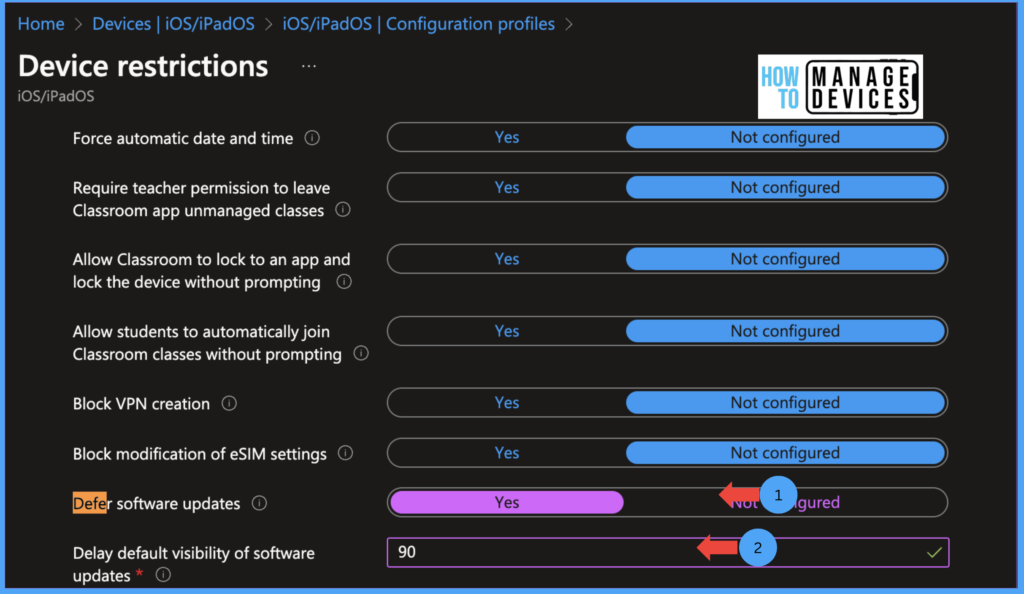
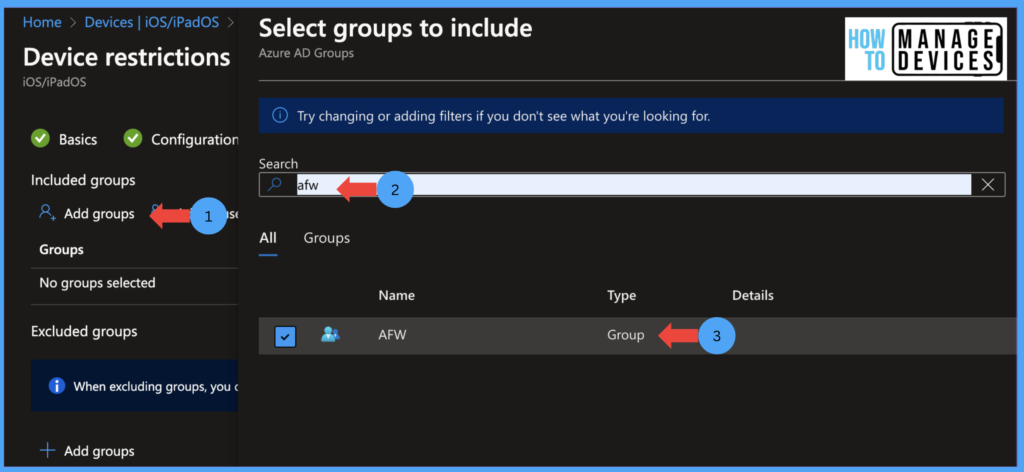
Define the required days and click on the Next to Scope tags page. Select Scope tags if you have any, and click Next to proceed to the Assignment page. Now assign the policy to the targeted user group.
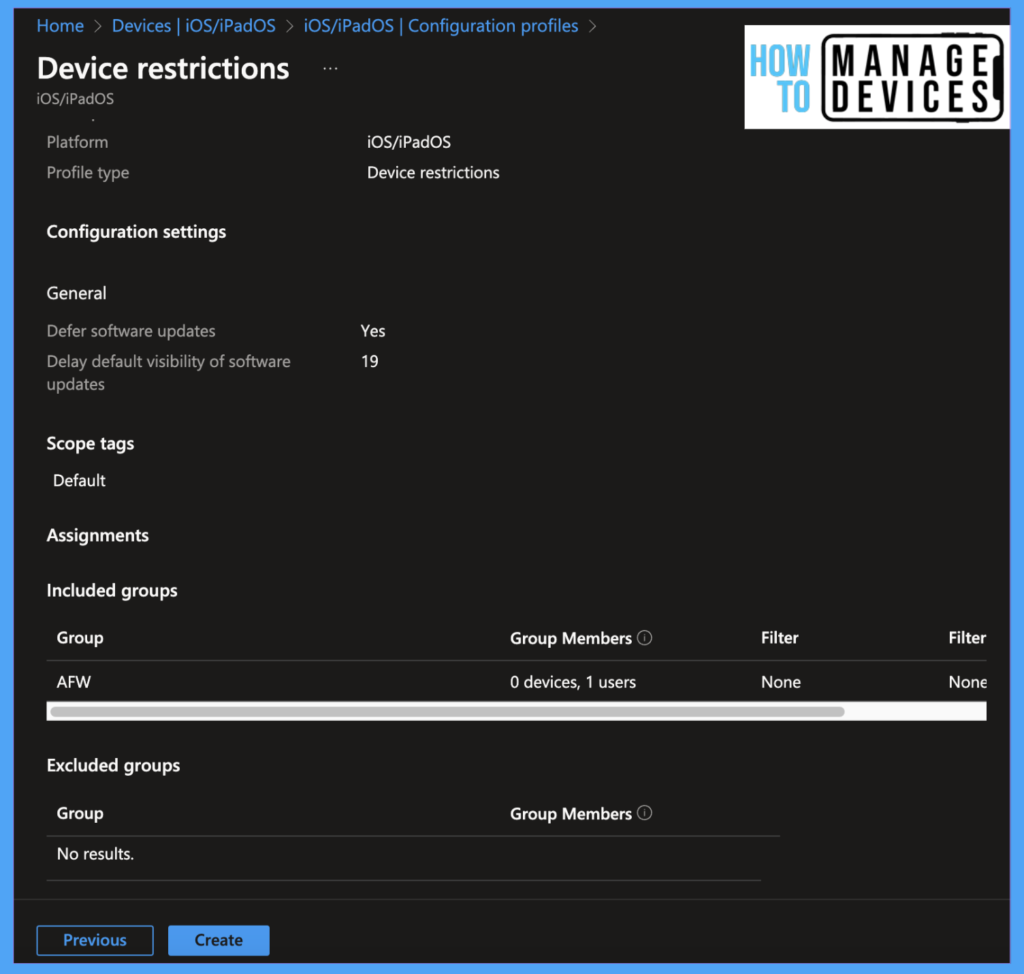
Click on Next to Review and Create screen. Review all the configurations and assignments and click on Create. This will create the required policy and assign it to assignment group users.
Now, after the policy is pushed to user devices, users won’t be able to update the devices until defined days, as the iOS update will not be visible to the users.
User Experience
Now let’s see the user experience on the rolled devices. To check the Software update, open settings on iPhone/iPad. Click on General > Software update. As I have defined it as deferral, the user will get a message under software update, “Your Phone is running the latest software update allowed by your administrator.”

Thus we can restrict users from installing the latest updates on iOS/iPad devices. For this post, I have restricted users only for 19 days from the OS release date.
NOTE! We can defer any software update for a maximum of 90 days, as Apple supports only 90 days. We can use Intune to push new updates to the devices, but we cannot downgrade the OS of the device using Intune update policies.
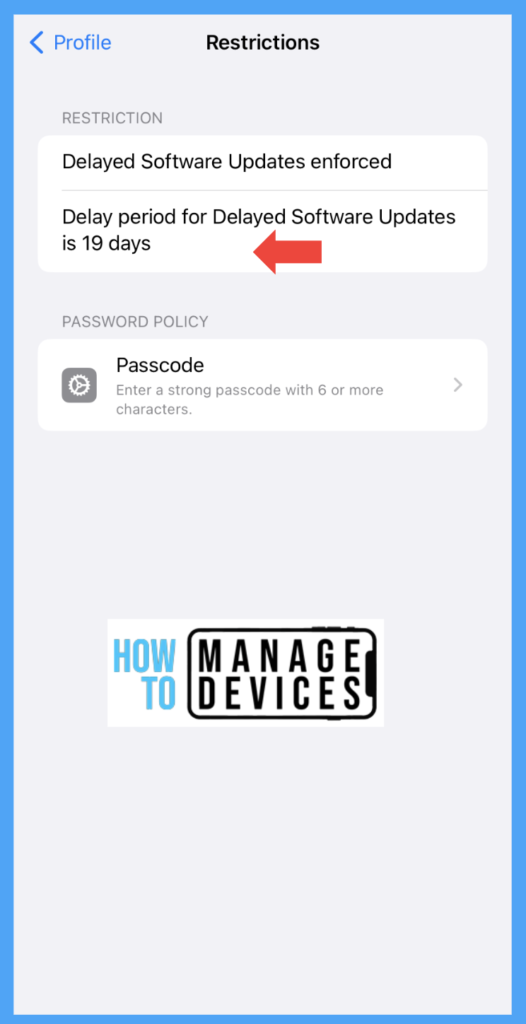
To check whether the restrictions are applied on the device or not, please open Settings > General > Scroll down to the bottom > Click on VPN & Device Management > Click on Management Profile > Click on Restrictions. Now we can view all the restrictions applied on the device by Intune.
Enforce Users to Install OS Updates
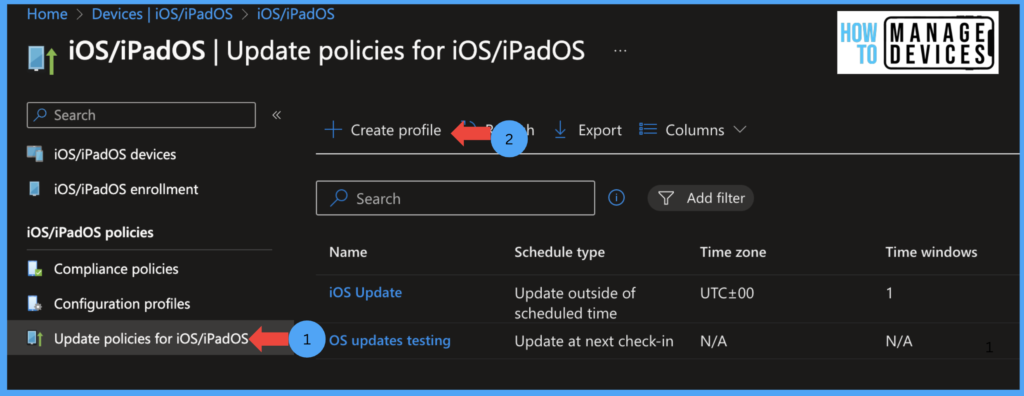
We have seen how to block users from installing the latest OS updates in the above. Now let’s see how we can force users to install a particular version of iOS/iPad. To push the OS version, we need to create “Update policies for iOS/iPadOS” Let’s see below the steps to create the update policies.
- Sign in to the Microsoft Endpoint Manager admin centre https://intune.microsoft.com.
- Click on Devices > iOS/iPadOS > Update policies for iOS/iPadOS
- Click on Create Profile
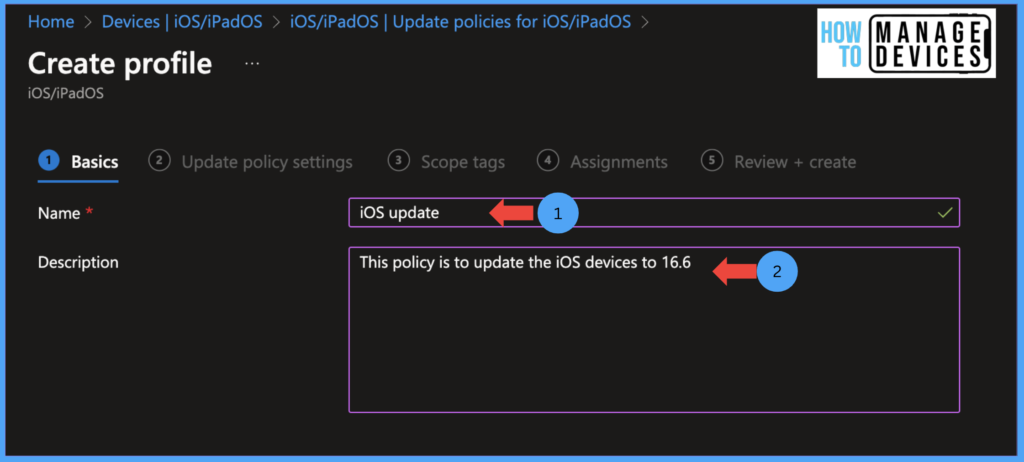
Now on the Basics Page, provide the updated policy’s Name and Description and click Next to the Update Settings page.
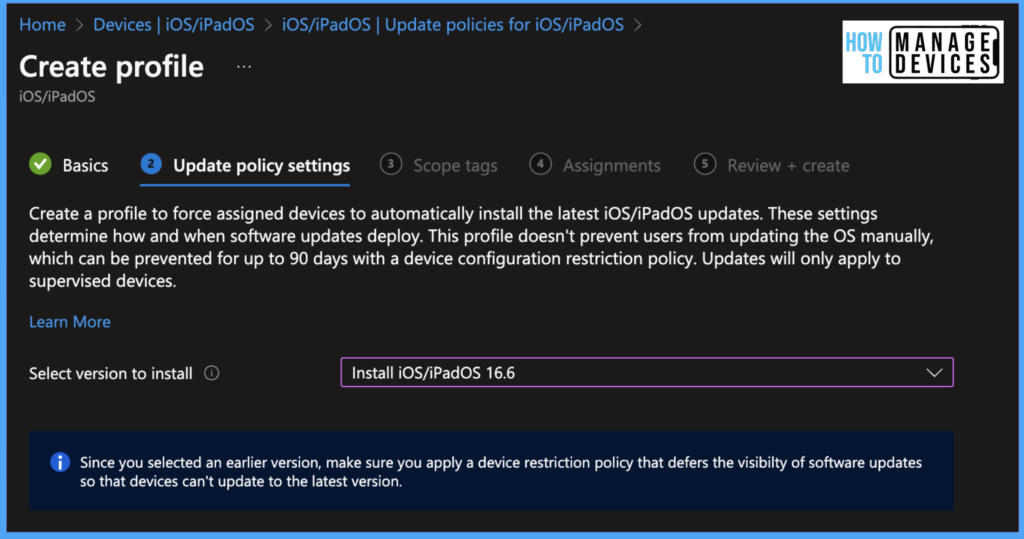
On the Update Settings page, select “Select version to install” Intune provides various iOS/iPadOS versions to update the device. Please select the required version, for our testing, I have chosen 16.6 as my iPhone is running on 16.5.1
We have selected the required OS version. Now we must select when the OS will be installed on the user’s device. We can schedule the time periods to avoid blocking users’ work. Intune provides us with options to schedule the OS installation.
- Update at next check-in: Updates the device at the next Check-in with Intune, this is the default value. We can schedule the timings with other options if you want to schedule during some intervals.
- Update during scheduled time: If we choose to update the device during a certain time period, Intune tries to update the device during that period.
- Update outside of scheduled time: When we chose this option, Intune tried to update the device outside the scheduled time
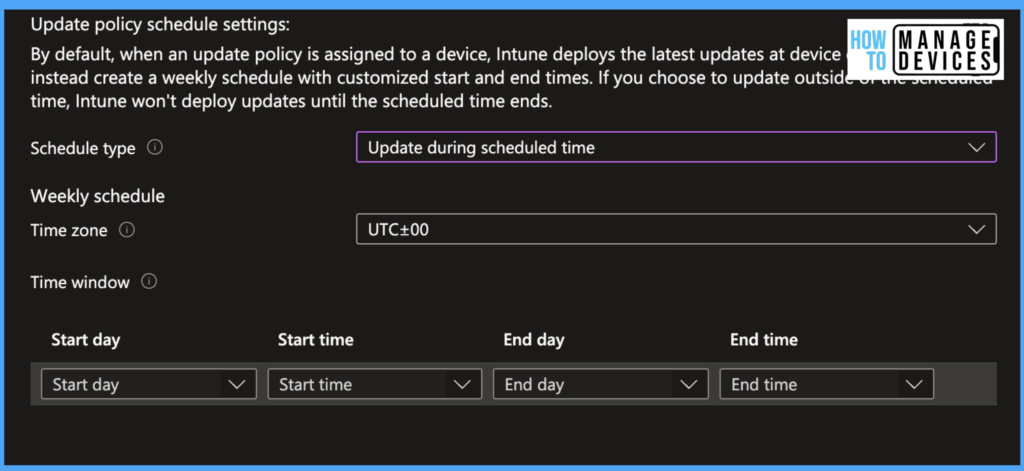
When we choose to update the divide during a scheduled time or outside the scheduled time, We should define the time interval when the device should be updated. Intune allows us to choose the various time zones. Select the time Zone and provide the Time Window, we can choose the Start and End day, Start Time and End Time to install the OS on the devices.
When you select the update during the Schedule time, Intune tries to install the OS update between the scheduled Start and end times. If we have chosen to update after the Schedule time, Intune installs OS updates after the Schedule Start and End Time. We can have multiple Start days and times. For our testing, I have selected Update at Next Check-in.
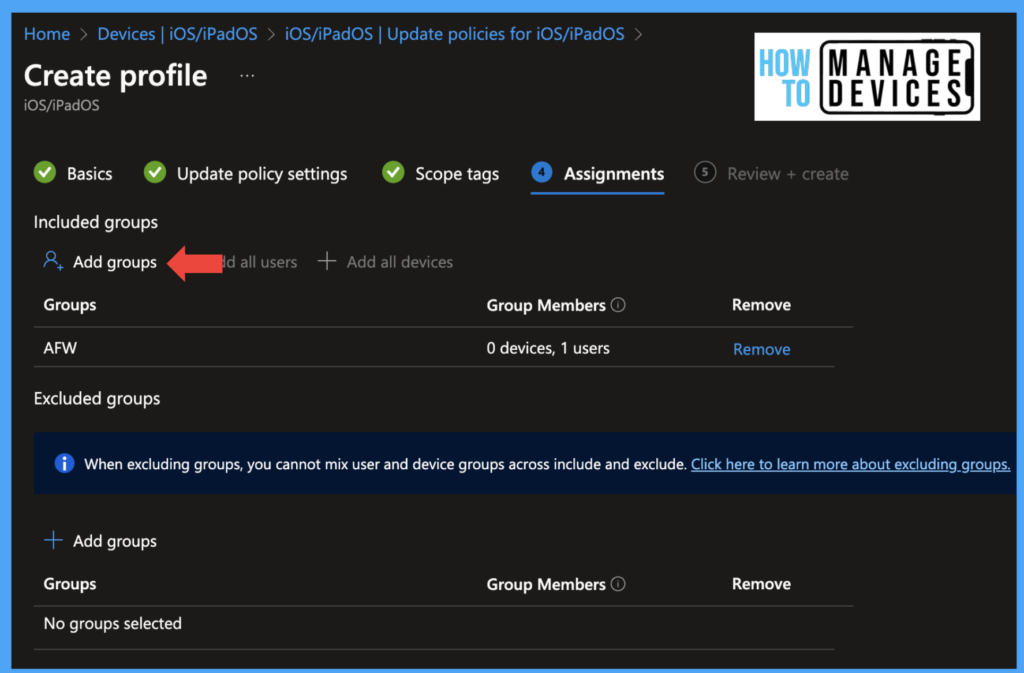
Now Click on Next to move the Scope tags screen, Select Scope tags if you have any, and click Next to proceed to the Assignment page. Now assign the policy to the targeted user group.
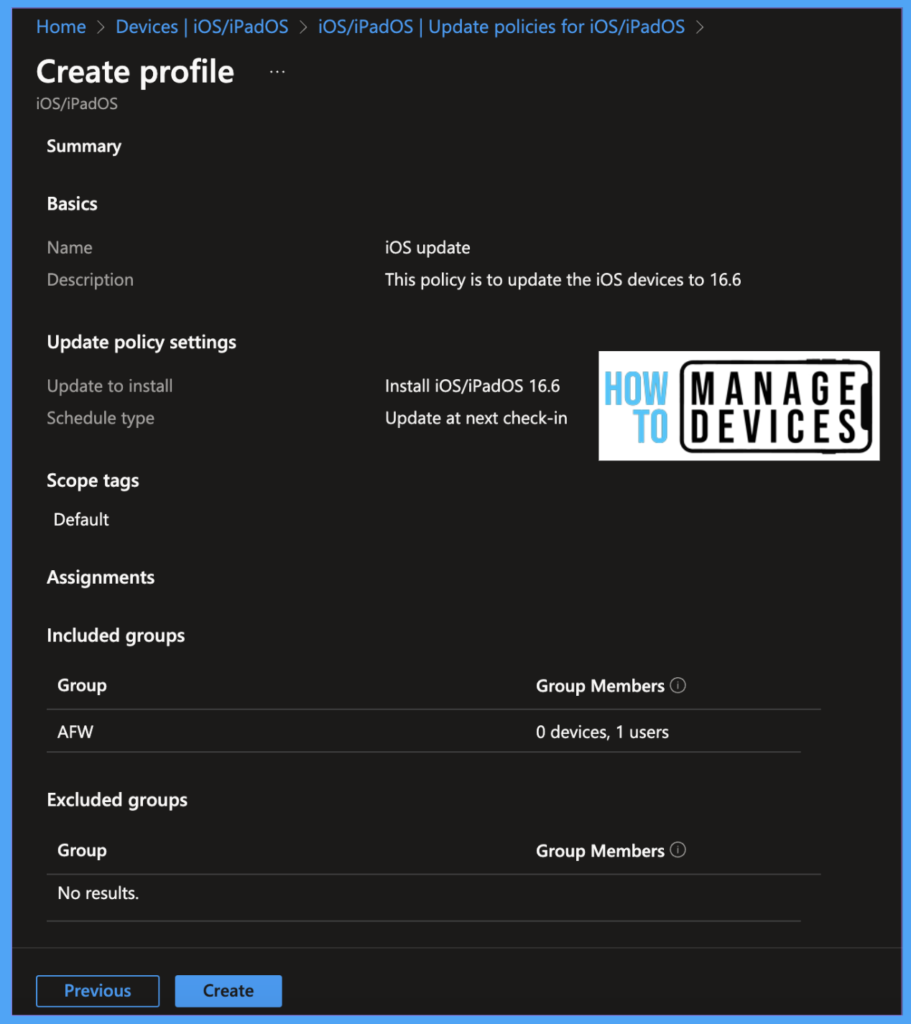
Click Next to the Review and Create screen, review your selected settings, and click Create. For our testing, I have selected update on Next Check-In. Once the policy is assigned, the device tries to download the software in the next check-in (usually, it is 8 hrs).
User Experience
Once the software update policy is pushed onto the device, based on your update policy, the user will get a notification to install the OS during the scheduled time. If an update is available through the updated policy, the device will download the update and install the update at the next check-in time of your scheduled time.
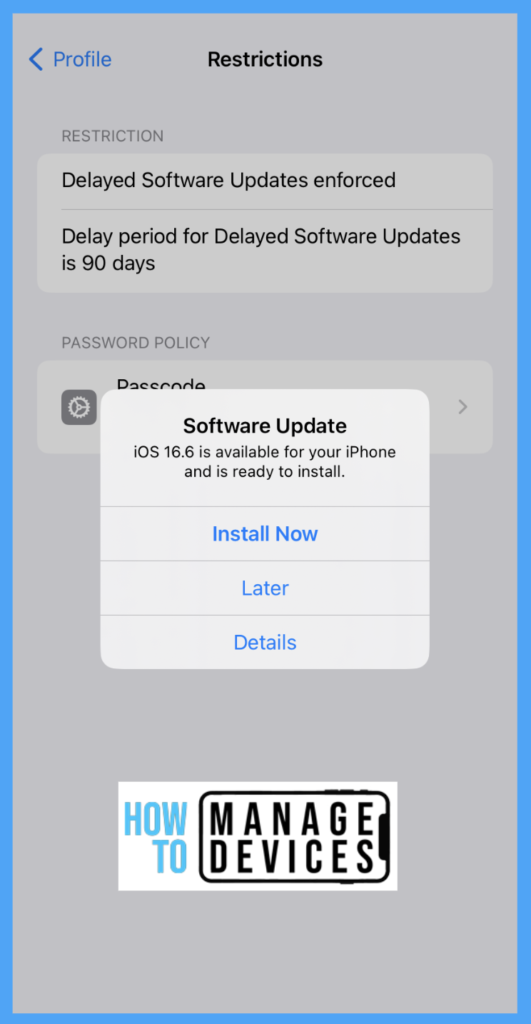
If the device has a passcode, the user must enter the passcode in order to install the update. Else the device will be updated without user intervention.
NOTE! The Software update policy overrides the Device Restrictions. If the device has software update and Software deferred restrictions, the software update policy takes precedence and updates the device.
Conclusion
So with the help of Device restriction policies, we can block software updates, and with the update policies, we can push the required OS to the devices and force users to update their devices as per organizational requirements. I hope this will help you to plan OS upgrades for your organization’s iPhone and iPad devices. We will catch up in another post till then… Bye……………..
Author
About Author – Narendra Kumar Malepati (Naren) has 11+ years of experience in IT, working on different MDM tools. Over the last seven years, Naren has been working on various features of Intune, including migration from different MDMs to Intune. Naren mainly focuses on Android, iOS, and MacOS.