In this post, we will see and learn about the Scan all downloaded files and attachments Policy. We will enable the Scan all downloaded files and attachments Policy using Intune. We will make use of Configuration Profiles from Intune to Enable this policy.
In order to ensure maximum protection with an antivirus solution like Microsoft Defender Antivirus, it is important to configure it heuristically to monitor suspicious and known malicious activity in real time. It is required to ensure the protection of your device and the data on it.
The policy setting allows you to configure scanning for all documents and attachments you download. Scanning will be enabled for all downloaded files and attachments, irrespective of whether you enable or disable this setting. The scanning of downloaded files and attachments will be disabled if this setting is disabled.
This policy setting i.e. Scan all downloaded files and attachments Policy configures scanning for all downloaded files and attachments. Whatever files or attachments you download with the help of this policy, everything will be scanned because of this policy. Also, the recommended state for this setting is set to Enabled as per the CIS Document.
- Do not Delete Temp Folders upon Exit Security Policy using Intune
- Limit Local Account Blank Password Use to Console Logon Using Intune Policy
Scan all downloaded files and attachments Policy Using Intune
Follow the steps stated below to Enable the Scan of all downloaded files and attachments Policy Using Intune:
- Sign in to the Intune Admin Center portal https://intune.microsoft.com/.
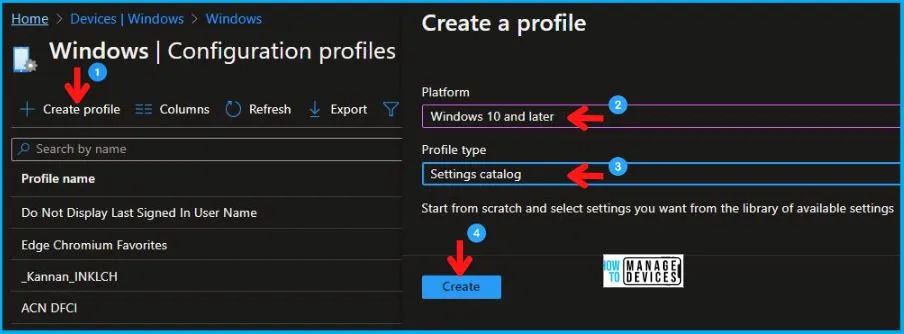
- Select Devices > Windows > Configuration profiles > Create a profile.
In Create Profile, Select Windows 10 and later in Platform, and Select Profile Type as Settings catalog. Click on Create button.
| Platform | Profile Type |
|---|---|
| Windows 10 and later | Settings Catalog |
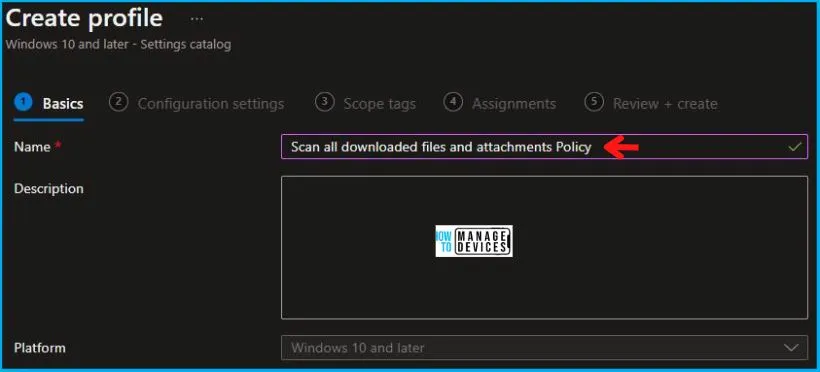
In the Basics tab pane, enter a name for the Policy as Scan all downloaded files and attachments Policy. If you like, you can enter the Description for the Policy, then select Next.
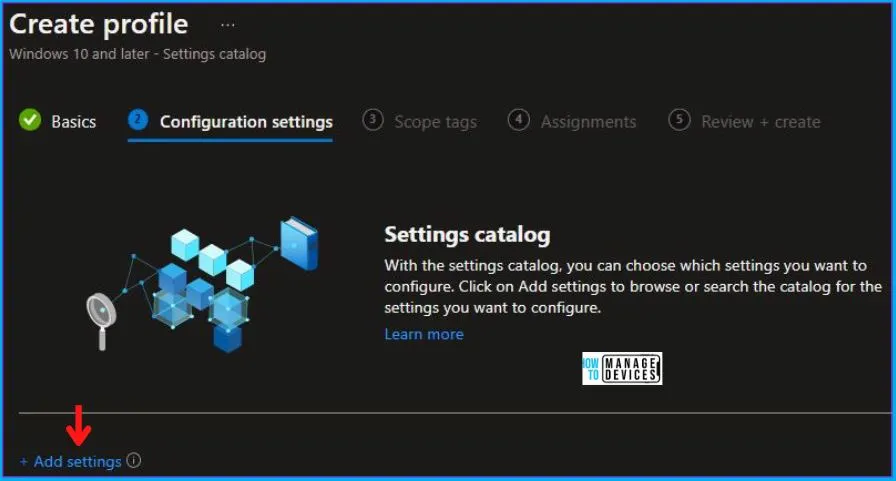
Now in Configuration settings, click Add settings to browse or search the catalog for the settings you want to configure.
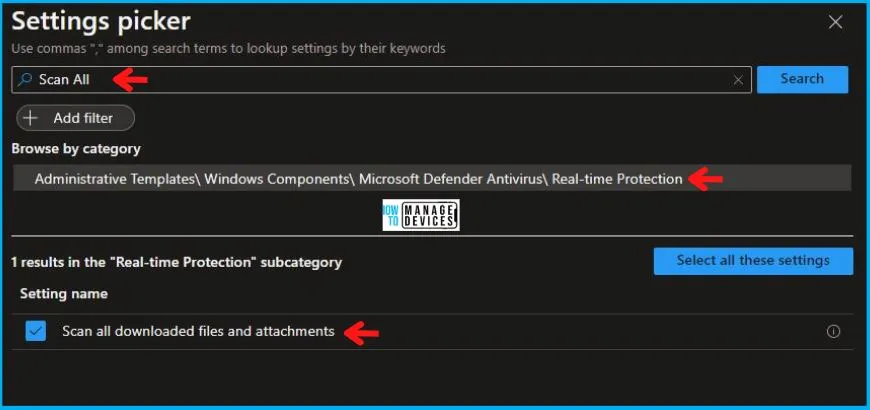
On the Settings Picker windows, if you search by the keyword Scan All, you will see Administrative Templates\ Windows Components\ Microsoft Defender Antivirus\ Real-time Protection, as shown below in the image, select this.
On selecting the option as shown below in the image, you will see one setting name, which is Scan all downloaded files and attachments. After adding your setting, click the cross mark at the right-hand corner, as shown below.
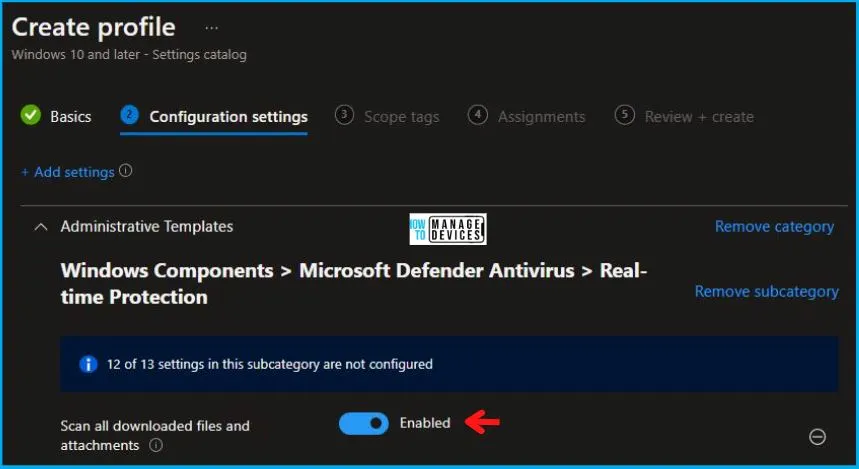
After this, in the Administrative Templates, set the Scan all downloaded files and attachments to Enabled, as shown below in the image.
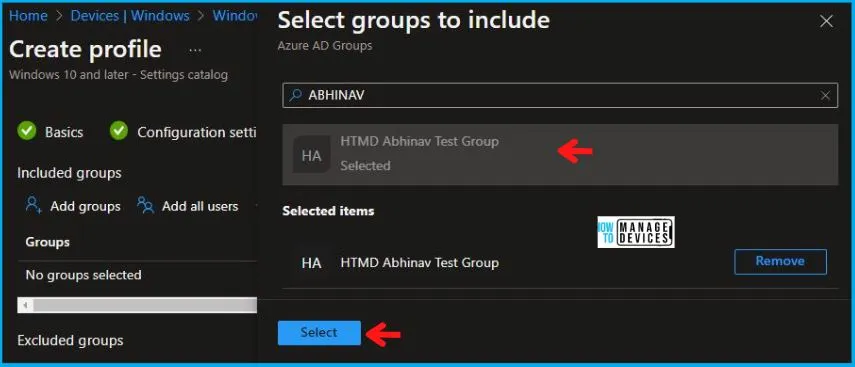
In Scope tags, you can assign a tag to filter the profile to specific IT groups. Add scope tags (if required) and click Next. Under Assignments, In Included groups, click Add groups, and then choose Select groups to include one or more groups. Click Next to continue.
Now in Review + create, review your settings. When you click on Create, your changes are saved, and the profile is assigned.
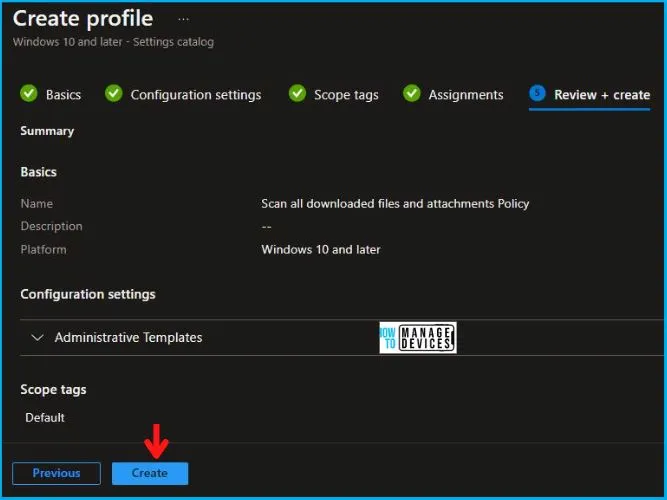
A notification will appear automatically in the top right-hand corner with a message. You can see that the Policy “Scan all downloaded files and attachments Policy” was created successfully. If you check, the Policy is available in the Configuration profiles list.
Your groups will receive your profile settings when the devices check in with the Intune service. The Policy applies to the device.
Intune Reporting
From Intune Portal, you can view the Intune settings catalog profile report, which provides an overview of device configuration policies and deployment status.
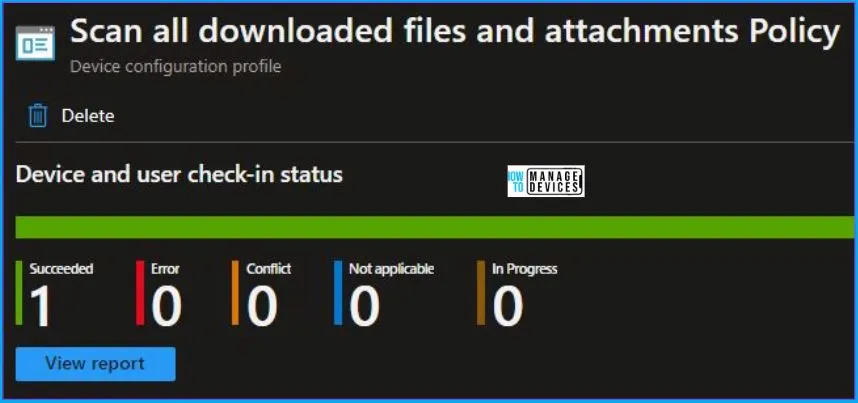
To monitor the policy assignment, from the list of Configuration Profiles, select the Policy, and here you can check the device and user check-in status. If you click View Report, additional details are displayed.
Intune MDM Event Log
Intune event ID 813 or 814 indicates that a string policy has been applied to Windows 10 or 11 devices. In addition, you can view the exact value of the Policy that is being applied to those devices.
You can check the Event log path to confirm this – Applications and Services Logs – Microsoft – Windows – Devicemanagement-Enterprise-Diagnostics-Provider – Admin.
The log states the following – MDM PolicyManager: Set policy string, Policy: (RealtimeProtection_DisableIOAVProtection), Area: (ADMX_MicrosoftDefenderAntivirus), EnrollmentID requesting merge: (4009A089-4FBA-482B-9D17-9E5A8428CB98), Current User: (Device), String: (), Enrollment Type: (0xD), Scope: (0x0).
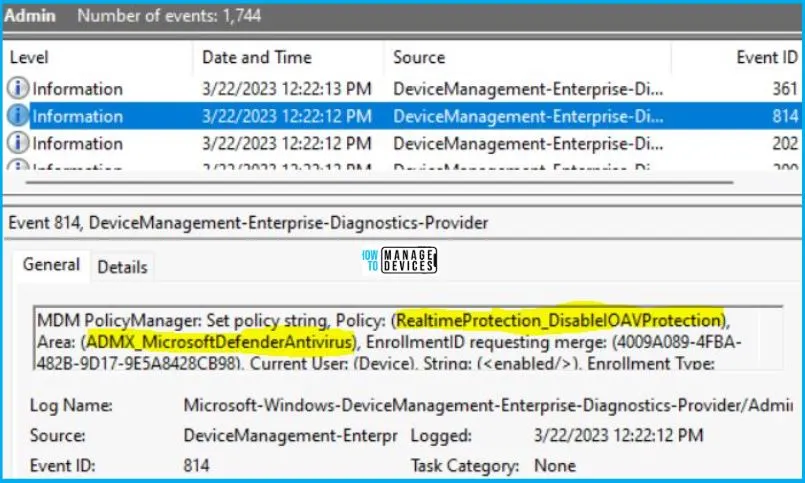
If you look in the event viewer log shown above, you will get some important information like Area and Enrollment ID that will help you in detecting the registry path. Please refer to the below for this information:
| Area | Policy | String Value | Scoped | Event ID |
|---|---|---|---|---|
| ADMX_MicrosoftDefenderAntivirus | RealtimeProtection_DisableIOAVProtection | Enabled | Device | 814 |
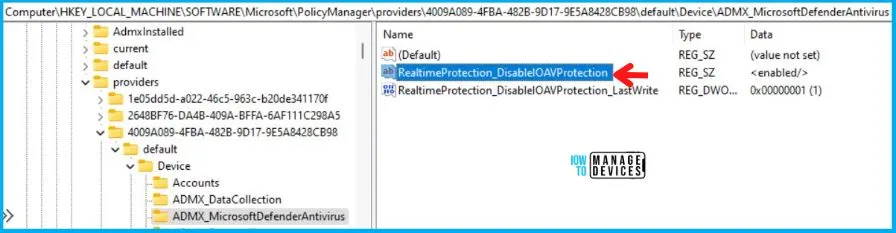
You can use information from the above table to REGEDIT.exe on a target computer to view the registry settings that store group policy settings. These settings are located in the registry path.
- Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PolicyManager\providers\4009A089-4FBA-482B-9D17-9E5A8428CB98\default\Device\ADMX_MicrosoftDefenderAntivirus
After you navigate to the above path in the Registry Editor, you will find the registry with the name RealtimeProtection_DisableIOAVProtection. Refer to the table and image as shown below.
| Registry Name | Data |
|---|---|
| RealtimeProtection_DisableIOAVProtection | Enabled |
Author
Abhinav Rana is working as an SCCM Admin. He loves to help the community by sharing his knowledge. He is a B.Tech graduate in Information Technology.