Let’s quickly check the list of security baselines settings for Cloud PC (Windows 365 service). Microsoft Endpoint manager (a.k.a Intune) provides an out of box baseline security configuration for Cloud PC. In this post, you will see the configuration settings that are covered in the baseline policies.
The following are the default recommended baseline from Microsoft. I would recommend running it with your organization’s security team to compare this baseline with your standard baseline configurations for Windows 365.
I have a post where I explained how to implement Windows 365 security baseline policies from Intune. You can refer to that post to get more details about the implementation of these policies. You are allowed to edit the existing baseline and make changes in each configuration as per your requirements.
List of Security Baselines Settings for Cloud PC
Let’s have a quick check what are the basic list of configurations that is coming from Microsoft. This is very useful, and I miss this kind of configuration for Azure Virtual Desktop or AVD. I think this can be used for AVD as well.
| RPC unauthenticated client options |
| Account Logon Audit Credential Validation (Device) |
| Audit Changes to Audit Policy (Device) |
| Internet Explorer restricted zone updates to the status bar via script |
| Internet Explorer internet zone drag and drop or copy and paste files |
| Block user control over installations |
| Disable inbound notifications |
| Internet Explorer restricted zone .NET Framework reliant components |
| Internet Explorer local machine zone do not run antimalware against Active X controls |
| Prevent bypassing Microsoft Defender SmartScreen prompts for sites |
| Internet Explorer internet zone access to data sources |
| System Audit Security State Change (Device) |
| Turn on Microsoft Defender Firewall for domain networks |
| Internet Explorer restricted zone drag content from different domains within windows |
| Restrict anonymous access to named pipes and shares |
| Minimum session security for NTLM SSP based servers |
| Internet Explorer certificate address mismatch warning |
| Object Access Audit Detailed File Share (Device) |
| Internet Explorer restricted zone less privileged sites |
You can configure the Toast notification and block run as credentials using the default recommendation from Microsoft policies.
| Block display of toast notifications |
| Internet Explorer restricted zone automatic prompt for file downloads |
| Automatic sample submission |
| Internet Explorer internet zone .NET Framework reliant components |
| Block storing run as credentials |
| Internet Explorer internet zone allows only approved domains to use tdc ActiveX controls. |
| Internet Explorer restricted zone script initiated windows |
| Apply UAC restrictions to local accounts on network logon |
| Internet Explorer internet zone include local path when uploading files to the server |
| Internet Explorer disable processes in enhanced protected mode |
| Minutes of lock screen inactivity until screen saver activates |
| Turn on Microsoft Defender Firewall for private networks |
| Internet Explorer internet zone loading of XAML files |
| Internet Explorer internet zone automatic prompt for file downloads |
| Autoplay default autorun behavior |
| Internet Explorer restricted zone security warning for potentially unsafe files |
| Policy Change Audit MPSSVC Rule Level Policy Change (Device) |
| Internet Explorer internet zone cross-site scripting filter |
| Network IP source routing protection level |
| Internet Explorer fallback to SSL3 |
I don’t know how many of you still use Internet Explorer in an office environment. I know there could be some internal apps that are dependent on IE. You can also block saving passwords using this Cloud PC security baseline.
| Internet Explorer encryption support |
| Require the client always digitally to sign communications |
| Account Logon Logoff Audit Logon (Device) |
| Internet Explorer locked down internet zone smart screen |
| Block password saving |
| Authentication level |
| System Audit Other System Events (Device) |
| Ink Workspace |
| Audit Authentication Policy Change (Device) |
| Internet Explorer restricted zone launch applications and files in an iFrame |
| Disable indexing encrypted items |
| System boot-start driver initialization |
| Prevent clients from sending unencrypted passwords to third-party SMB servers |
| Internet Explorer internet zone popup blocker |
| Internet Explorer processes consistent MIME handling. |
| Microsoft accounts optional for Windows Store apps |
| Scan type |
| Scan all downloaded files and attachments |
| Privilege Use Audit Sensitive Privilege Use (Device) |
| Secure RPC communication |
You can also set policies for SmartScreen warning with the security baseline for Windows 365. I have implemented this policy, and it works ok.
| Block users from ignoring SmartScreen warnings |
| Block inbound connections |
| Internet Explorer restricted zone java permissions. |
| Block connection to non-domain networks |
| Internet Explorer restricted zone loading of XAML files |
| Internet Explorer processes scripted window security restrictions |
| Enable network protection |
| Internet Explorer restricted zone run Active X controls and plugins |
| Internet Explorer restricted zone script Active X controls marked safe for scripting |
| Require server digitally signing communications always |
| Administrator elevation prompt behavior |
| SMB v1 client driver start configuration |
| Audit Other Logon Logoff Events (Device) |
| Block outbound connections |
| Internet Explorer restricted zone logon options |
| Block drive redirection |
| Scheduled scan start time |
| Defender schedule scan day |
| Block Internet download for web publishing and online ordering wizards |
| Block app installations with elevated privileges |
Well, you can also configure the policies related to Attach Surface redirection rules, Autoplay mode, and defender potentially unwanted app action, etc…
| Internet Explorer trusted zone initialize and script Active X controls not marked as safe. |
| SMB v1 server |
| Turn on cloud-delivered protection |
| Attack surface reduction rules |
| Autoplay mode |
| Defender potentially unwanted app action |
| Turn on Credential Guard |
| Ignore connection security rules |
| Internet Explorer check server certificate revocation |
| Internet Explorer internet zone less privileged sites |
| Security log maximum file size in KB |
| Internet Explorer restricted zone file downloads |
| Configure secure access to UNC paths |
| Block data execution prevention |
| Internet Explorer internet zone runs .NET Framework reliant components signed with Authenticode. |
| Internet Explorer prevents per-user installation of Active X controls |
| Scan removable drives during a full scan |
| Require SmartScreen for Microsoft Edge Legacy |
| Minimum session security for NTLM SSP based clients |
| Enumeration of external devices incompatible with Kernel DMA Protection |
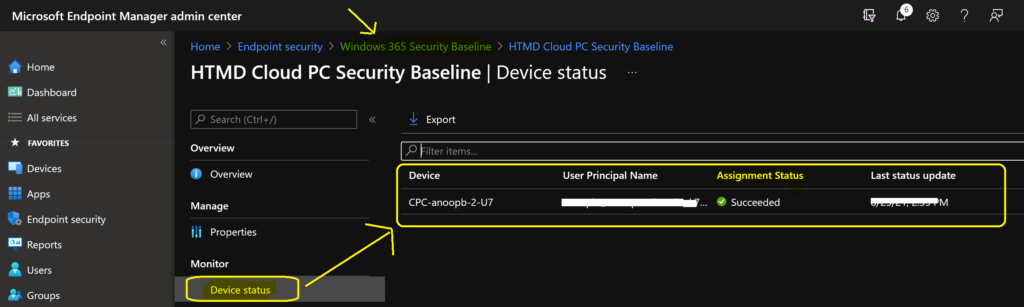
List of Security Baselines Settings for Cloud PC helps understand the set of policies and figure out which configuration you want to change for Windows 365 cloud PC solution.
| Internet Explorer prevent managing smart screen filter |
| An additional amount of time (0-50 seconds) to extend cloud protection timeout |
| Internet Explorer processes MIME sniffing safety feature |
| Internet Explorer restricted zone download signed Active X controls |
| Block anonymous enumeration of SAM accounts and shares |
| Internet Explorer internet zone allow VBscript to run |
| Internet Explorer restricted zone allow only approved domains to use tdc Active X controls |
| Ignore all local firewall rules |
| Internet Explorer trusted zone does not run antimalware against Active X controls. |
| Internet Explorer local machine zone java permissions |
| Defender Processes to exclude |
| Internet Explorer intranet zone does not run antimalware against Active X controls. |
| Disable inbound notifications |
| Block inbound connections |
| Turn on Microsoft Defender Firewall for public networks |
| Internet Explorer restricted zone scriptlets |
| System log maximum file size in KB |
| Internet Explorer processes notification bar |
| Internet Explorer internet zone download signed ActiveX controls |
| Internet Explorer restricted zone smart screen |
| Internet Explorer removes the run this time button for outdated Active X controls. |
| Internet Explorer internet zone launch applications and files in an iframe |
| Defender system scan schedule |
| Prompt for password upon connection |
| Audit Security Group Management (Device) |
| Policy Change Audit Other Policy Change Events (Device) |
| Block remote logon with a blank password |
| Internet Explorer restricted zone navigates windows and frames across different domains. |
| Digest authentication |
| Internet Explorer internet zone smart screen |
| Disable inbound notifications |
| Internet Explorer locked down trusted zone java permissions |
| Internet Explorer checks signatures on downloaded programs |
| Block malicious site access |
| Audit Special Logon (Device) |
| Internet Explorer restricted zone scripting of web browser controls |
| Internet Explorer restricted zone cross-site scripting filter |
| Internet Explorer restricted zone binary and script behaviors |
| Detailed Tracking Audit Process Creation (Device) |
| Standard user elevation prompt behavior |
In this security baseline list, you can also find remote desktop services and RDP client connection encryption level policies related to Windows 365 Cloud PC.
| Remote desktop services client connection encryption level |
| Internet Explorer internet zone security warning for potentially unsafe files |
| LOC NEEDED: deviceConfiguration__windows10GeneralConfiguration_defenderPotentiallyUnwantedAppActionPcl_DisplayName |
| Internet Explorer intranet zone java permissions |
| Internet Explorer restricted zone popup blocker |
| Block unverified file download |
| Block Password Manager |
| Audit File Share Access (Device) |
| Application log maximum file size in KB |
| Internet Explorer processes MK protocol security restriction |
| Remote host delegation of non-exportable credentials |
| Internet Explorer trusted zone java permissions |
| Internet Explorer restricted zone scripting of java applets |
| Internet Explorer locked down restricted zone java permissions |
| Prevent anonymous enumeration of SAM accounts |
| Audit User Account Management (Device) |
| Block outbound connections |
| Object Access Audit Removable Storage (Device) |
| Internet Explorer internet zone allows only approved domains to use ActiveX controls. |
| Block Windows Spotlight |
| Internet Explorer includes all network paths |
| Voice activate apps from the locked screen |
| Allow remote calls to the security accounts manager |
| Internet Explorer internet zone protected mode |
| Internet Explorer internet zone initializes, and script Active X controls not marked as safe. |
| System Audit System Integrity (Device) |
| Basic authentication |
| Internet Explorer locked down restricted zone smart screen |
| Account Logon Logoff Audit Group Membership (Device) |
| Structured exception handling overwrite protection |
| PowerShell script block logging |
| File extensions to exclude from scans and real-time protection |
| Internet Explorer internet zone java permissions |
| Internet Explorer restricted zone active scripting. |
| Internet Explorer internet zone logon options |
| Internet Explorer restricted zone allow VBScript to run |
| Network ignore NetBIOS name release requests except WINS servers |
| Internet Explorer internet zone drag content from different domains across windows |
| Internet Explorer intranet zone initialize and script Active X controls not marked as safe |
| Remote Assistance solicited |
The following list of Security Baselines Settings for Cloud PC helps deploy the Microsoft recommended security policies for Windows 365 products.
| Internet Explorer restricted zone download unsigned Active X controls |
| Internet Explorer internet zone drag content from different domains within windows |
| Internet Explorer processes restrict Active X install |
| Use admin approval mode |
| Block inbound connections |
| Only allow UI access applications for secure locations |
| Cloud-delivered protection level |
| Detect application installations and prompt for elevation |
| Internet Explorer internet zone scriptlets |
| Internet Explorer restricted zone drag and drop or copy and paste files |
| Internet Explorer software when the signature is invalid |
| Detailed Tracking Audit PNP Activity (Device) |
| Block downloading of print drivers over HTTP |
| Internet Explorer restricted zone copy and pasted via script |
| Internet Explorer restricted zone drag content from different domains across windows |
| Audit Security System Extension (Device) |
| Enable virtualization-based security |
| Internet Explorer internet zone script initiated windows |
| Internet Explorer security zones use only machine settings |
| Prevent storing LAN Manager hash value on next password change |
| Prevent users from overriding certificate errors |
| Internet Explorer locked down local machine zone java permissions |
| Internet Explorer restricted zone do not run antimalware against Active X controls |
| Internet Explorer restricted zone run .NET Framework reliant components signed with Authenticode |
| Enumerate administrators |
| Internet Explorer restricted zone access to data sources |
| Internet Explorer internet zone do not run antimalware against ActiveX controls |
| Internet Explorer internet zone copy and paste via script |
| Internet Explorer uses Active X installer service |
| Enable secure boot with DMA |
| Internet Explorer processes protection from zone elevation |
| Internet Explorer internet zone download unsigned ActiveX controls |
| Internet Explorer internet zone navigate windows and frames across different domains |
| Object Access Audit Other Object Access Events (Device) |
| Internet Explorer internet zone updates to the status bar via script |
| Turn on real-time protection |
| Internet Explorer restricted zone include local path when uploading files to the server |
| Block client digest authentication |
| Internet Explorer processes restrict file download. |
| Network IPv6 source routing protection level |
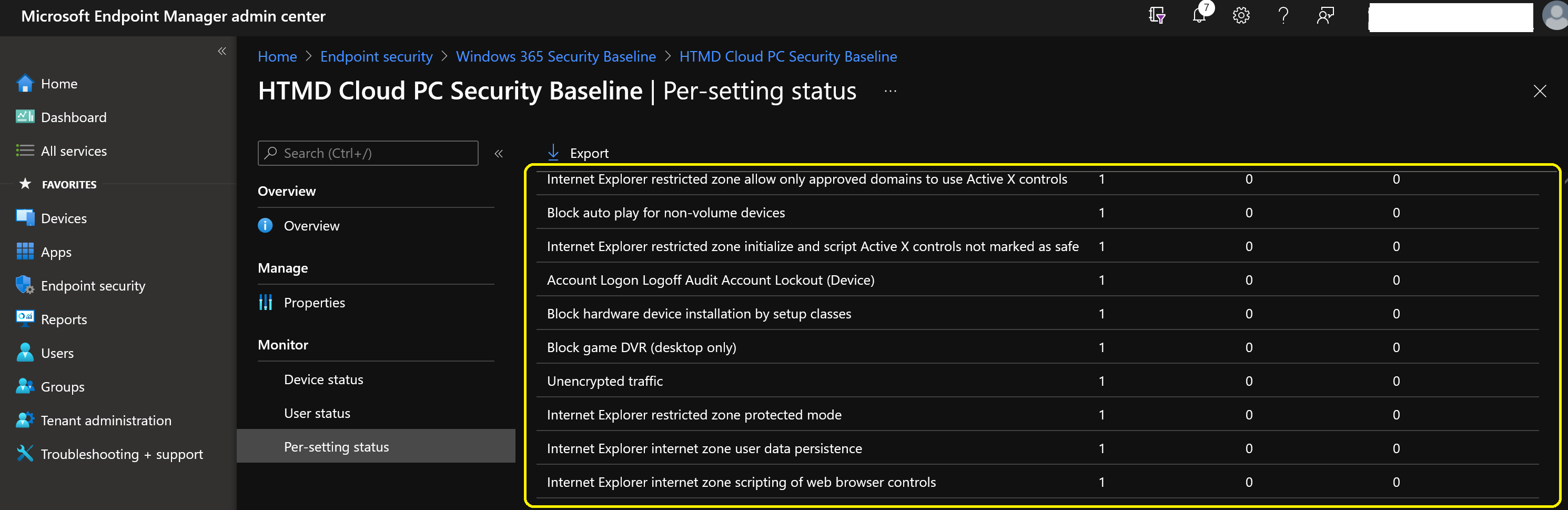
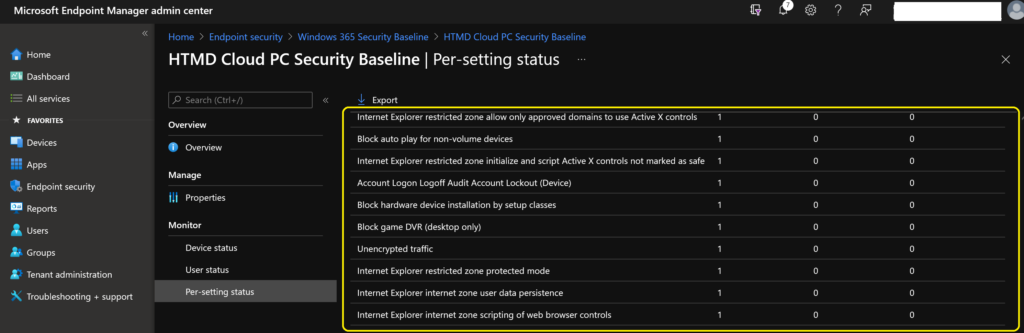
| Internet Explorer restricted zone allows only approved domains to use Active X controls. |
| Block autoplay for non-volume devices |
| Internet Explorer restricted zone initializes, and script Active X controls not marked as safe. |
| Account Logon Logoff Audit Account Lockout (Device) |
| Block hardware device installation by setup classes |
| Block game DVR (desktop only) |
| Unencrypted traffic |
| Internet Explorer restricted zone protected mode |
| Internet Explorer internet zone user data persistence |
| Internet Explorer internet zone scripting of web browser controls |
| Turn on Windows SmartScreen |
| Internet Explorer restricted zone user data persistence |
| Network ICMP redirects override OSPF generated routes |
| Client unencrypted traffic |
| Internet Explorer locked down intranet zone java permissions |
| Internet Explorer enhanced protected mode |
| Internet Explorer restricted zone meta refresh |
| Client basic authentication |
| Block outbound connections |
| Block heap termination on corruption |
| Launch system guard |
I hope the above list of Security Baselines Settings for Cloud PC helps you to decide whether to deploy these policies to Cloud PCs or not. This List of Security Baselines Settings for Cloud PC helps identify the standard security configurations with Windows 365 products. Also, this will help to prepare you with the PEN test for Cloud PC (Windows 365).