In this post, we will how to deploy Windows 365 security baseline policies to Cloud PCs. It’s great news that Microsoft already created baseline security configuration policies for Cloud PCs. However, this type of configuration is missing for Azure Virtual Desktop.
Do you think you can use the same Windows 365 security baseline policies for Azure Virtual Desktop (AVD)? I would surely try the same set of policies for all virtual desktops. Also, you can edit the policy-setting values from this configuration.
The Windows 365 filtering rules can’t be applied to security baseline policies (at writing this post). Hence my recommendation is to use Azure AD dynamic device groups for deploying these security baseline policies for Cloud PCs.
Windows 365 Security Baseline
It’s time to create Windows 365 security baseline policies now. I don’t think the policy deployment will take so much time; however if you have already deployed security policies to Cloud PCs using setting catalog or other policies, that could create policy conflict issues.
Try to check the baseline policies with new Cloud PC deployments without any other security policies. Let’s see how to create Windows 365 security baseline policies for Cloud PCs.
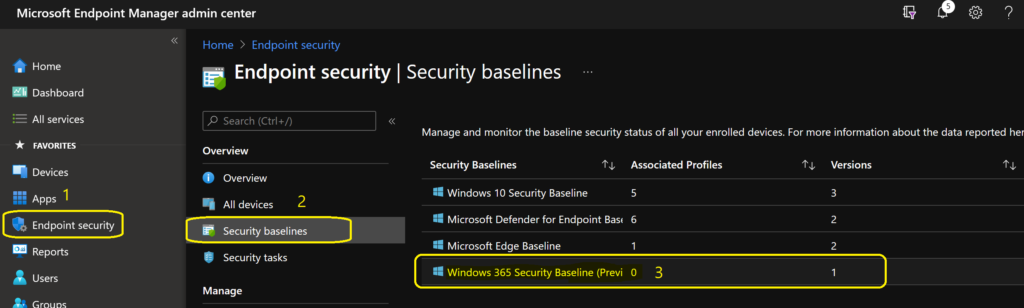
- Launch MEM Admin Center https://endpoint.microsoft.com with appropriate permission.
- Navigate to Endpoint Security node.
- Click on Security Baselines node – You can see several other baseline policies in this node.
- Select Windows 365 Security Baseline policy set.
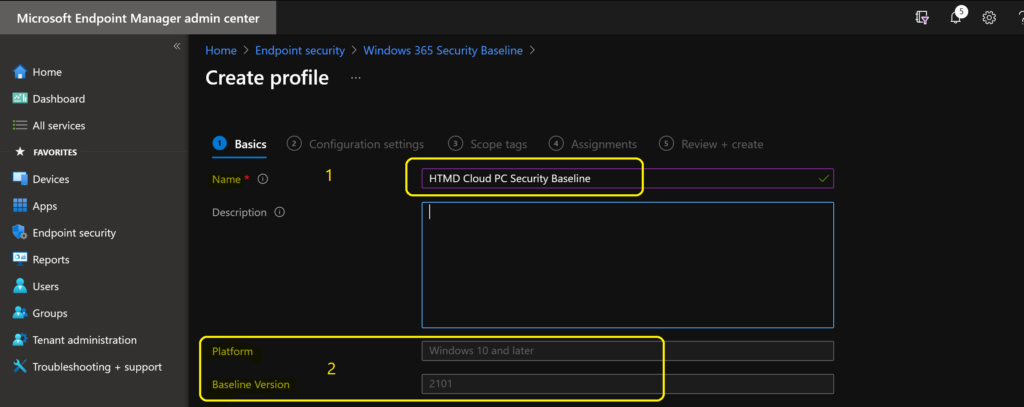
You can now click on + Create Profile to create a Windows 365 security baseline profile for Cloud PCs. You can also check the versions of the baseline available. The one currently available is 2101.
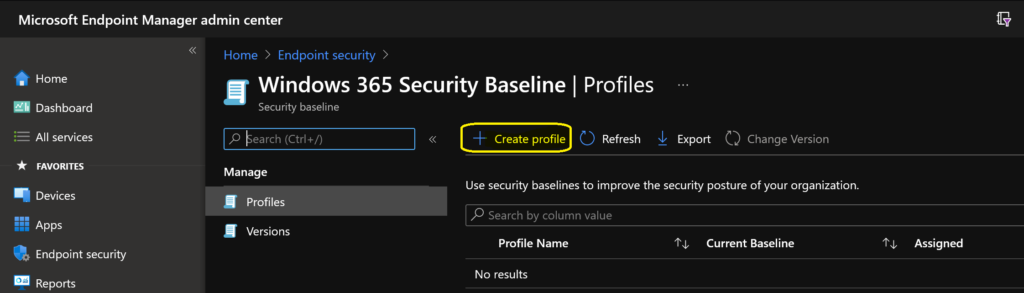
You will have to enter to name and description of the Windows 365 Security Baseline. There are no drop-down options for the platform and Baseline version while writing this post. You can click on the next button to continue.
- Name -> HTMD Cloud PC Security Baseline
- Platform -> Windows 10 and Later
- Baseline Version -> 2101
Cloud PC Security Baseline Categories
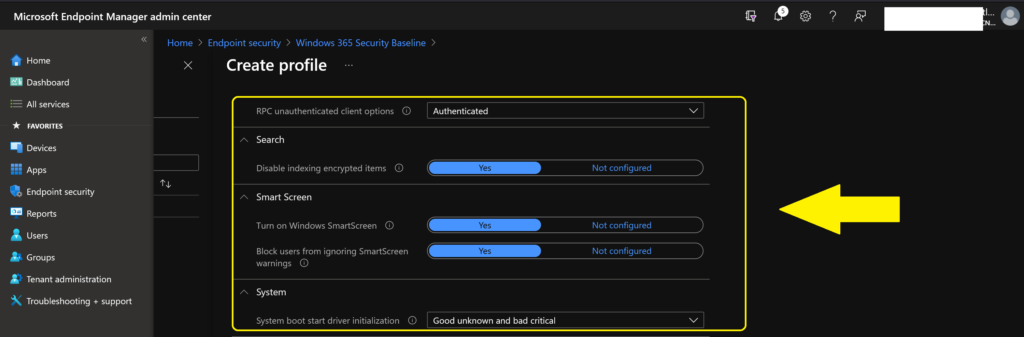
You can get a quick overview of the Windows 365 security baseline categories with default values of these tables. This will help you understand the configurations very quickly and adjust them as per your requirements. However, I would recommend using the default Cloud PC security baseline.
You can check the individual policies in each category from the following blog post – List of Security Baselines Settings for Cloud PC Windows 365.
| Category of Security Baseline | Default Value |
|---|---|
| Above Lock | Disabled |
| App Runtime | Enabled |
| Application management | Enabled |
| Attack Surface Reduction Rules | Some of the settings are Enabled, and Some are Blocked |
| Audit | A mix of Success and Failure |
| Auto Play | Do Not Execute/Disabled/Enabled |
| Browser | Yes |
| Connectivity | Enabled |
| Credentials Delegation | Enabled |
| Credentials UI | Disabled |
| Device Guard | Enabled |
| Device Installation | Enabled |
| DMA Guard | Block All |
| Event Log Service | 32768-196608 |
| Experience | Enabled |
| File Explorer | Disabled |
| Firewall | Configured |
| Internet Explorer | A Lot of options Disabled/Enabled (Use IE?) |
| Local Policies Security Options | Configured a lot of settings |
| Microsoft Defender | Configured a lot of settings |
| Microsoft Defender Antivirus Exclusions | 3/9 Minutes |
| Microsoft Edge | Enabled and Disabled |
| MS Security Guide | Enabled and Disabled |
| MSS Legacy | Highest Protection, Enabled and Disabled for some settings |
| Remote Assistance | Disabled |
| Remote Desktop Services | High and Enabled |
| Remote Management | Enabled and Disabled |
| Remote Procedure Call | Authenticated |
| Search | Configured |
| Smart Screen | Configured |
| System | Good unknown and bad critical |
| Windows Connection Manager | Enabled |
| Windows Ink Workspace | Enabled |
| Windows PowerShell | Enabled |
Once you have checked and verified the values baseline policies for Cloud PCs, you can click on the Next button.
You can select the appropriate scope tags to support proper Intune RBAC scenarios.
- Click on Next continue.
- Click on Add groups to add Cloud PC Azure AD Device group.
NOTE! – You don’t have Intune filter rule for Windows 365 option here with Security baseline deployments. Hence you will have to use AAD dynamic device groups for this type of deployment.
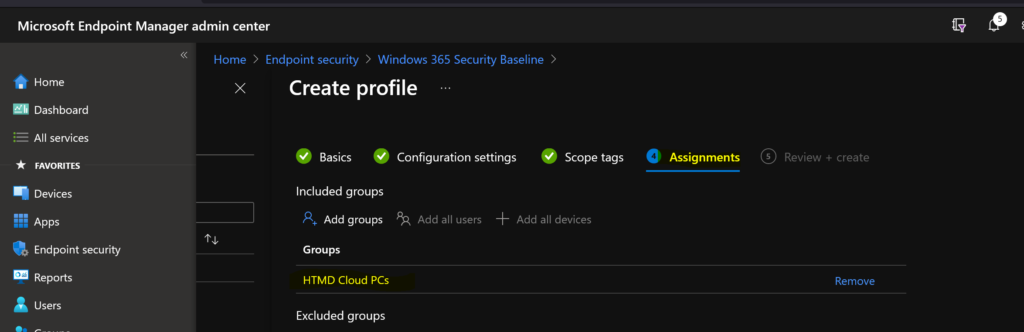
You can now click on CREATE button to complete the Windows 365 security baseline deployment process.
Results
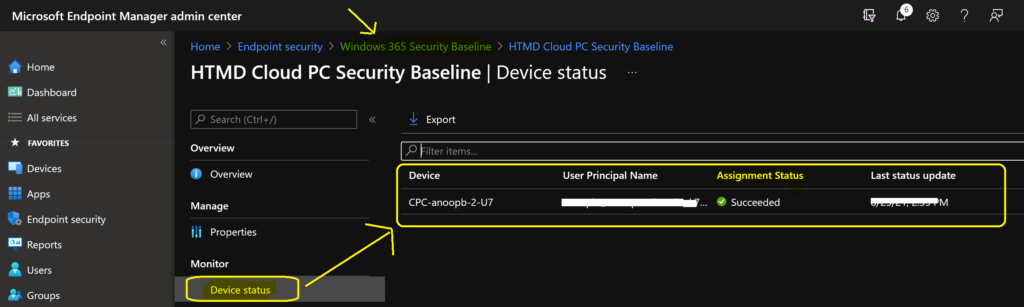
You can look into the default Intune reports to check the status of baseline security policies for Cloud PC. There are two ways to check the default reports.
- Check the report from Windows 365 security baseline policy -> Monitor section -> Device Status and Per Settings option.
- Check the report from Devices -> Endpoint Security Configuration Node.