Learn how to leverage PowerShell Scripts in Intune to uninstall Windows Update. Uninstalling Windows updates is a common task for IT admins, and Intune makes it easy to manage this process across multiple devices.
Intune allows you to utilize PowerShell scripts to remove different types of Windows updates, including feature updates that come through an enablement package. By creating and deploying a PowerShell script in Intune, you can easily uninstall specific updates from a device or a group of devices.
This process offers a straightforward and efficient way to maintain the desired software configuration and ensure the system remains secure and up-to-date. With Intune’s PowerShell script capability, organizations can maintain better control over their IT environment and streamline the management of their Windows devices.
In addition, Intune offers the option to remove quality updates that have been installed on a device. To use this feature, the device must have Windows 10 version 1803 or later installed, paused quality updates, and the most recent quality update based on the device’s quality update deferral settings.
PowerShell scripts can be used to automate the update removal process, making it faster and more efficient. This saves time and allows you to focus on more important tasks.
- Deploy Windows Update Offline Using Intune
- Windows 10 Rollback Uninstall Updates Enhanced Diag Options
Identifying and Preparing Windows Update KB Uninstallation with PowerShell Scripts
Before uninstalling an update from a Windows Image, it is important to identify the specific update that needs to be removed. This initial phase is essential as it ensures that the correct update is being targeted for removal, avoiding any unnecessary changes to the system.
To identify the update, you can use various methods, such as reviewing the Windows 10 or 11 Update history or checking the list of installed updates. It is also essential to ensure that the update to be uninstalled is not a critical security update, as removing it may leave the system vulnerable to security threats.
Once the update has been identified and confirmed to be non-critical, the uninstallation process can proceed. It is important to note that certain updates cannot be uninstalled from a Windows system.
Microsoft provides the following command line as an example for demonstration purposes. This command line can be modified to suit specific requirements or preferences. To use this script, replace the <enter KB number of update to be removed here> placeholder with the KB number of the update you want to remove.
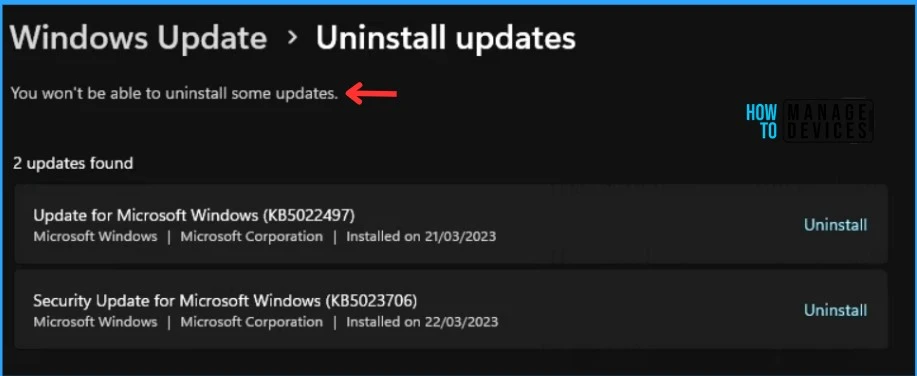
The script will search for all installed Windows updates and check if the specified update is installed. If it is, the script will remove the update. You won’t be able to uninstall some updates.
First, to get the full list of updates installed on the device run:
get-windowspackage -online -PackageName "*KB<NUM>*"
To remove a particular update from the list of installed updates, execute the following command:
Remove-WindowsPackage -Online -PackageName "Package Name"Uninstall Windows Update with Intune PowerShell Scripts
The following steps will help you upload the PowerShell, and modify the run behavior to Intune for uninstalling Windows updates.
- Sign in to the Microsoft Intune admin center https://intune.microsoft.com/.
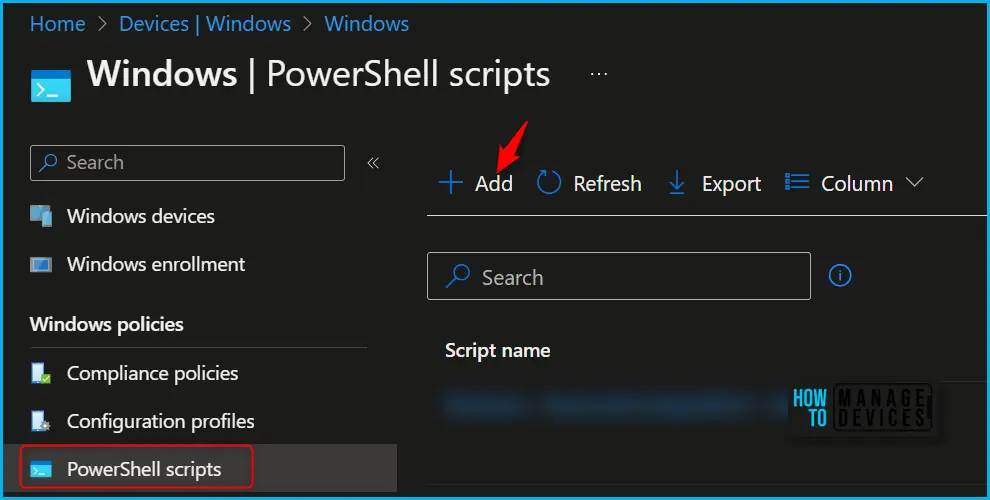
- Navigate to Devices > Scripts. This will take you to the Powershell Script wizard. Alternatively, if you want to add Powershell scripts, you can also select Devices > Windows > PowerShell Scripts.

In the PowerShell scripts tab, Click on Add. This will open the Add PowerShell Script wizard in Intune.
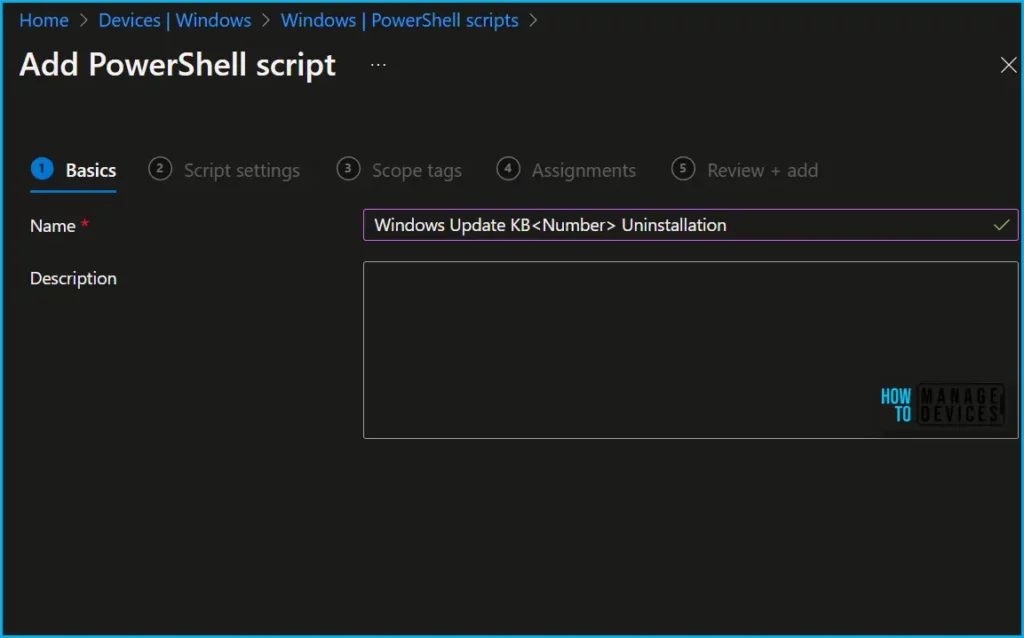
In Basics, You need to type the descriptive name (For Example, Uninstall Windows Update KB <Number>) for the script or a description to get it more clear for other references and Select Next.
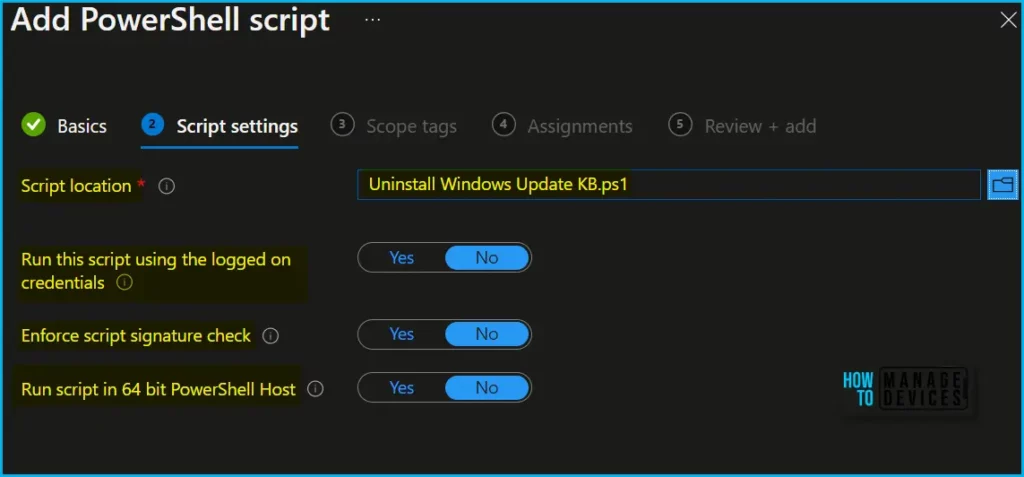
Provide the necessary information in the “Script Settings” section as per your requirements, and then click “Next.” Proceed to follow the steps to upload uninstall Windows update PowerShell script.
- Script Location: Browse the PowerShell script (uninstall Windows update) where you placed it, and the script must be less than 200 KB.
- Run the script using the logged-on credentials: Select Yes to run the script on the user credential. Else, select No (default); it will run in a system context. The administrator must decide on this setting according to the requirements.
- Enforce script signature check: Select Yes if the script is signed by a trusted publisher, else, select No (default) if there is no requirement.
- Run the script in a 64-bit PowerShell host: Select Yes to run the script in a 64-bit PowerShell host on a 64-bit client. Select No (default) to run the script in a 32-bit PowerShell host.
When setting to Yes or No to Run the script in a 64-bit PowerShell host, use the following table for new and existing policy behavior:
| Run script in 64-bit host | Client architecture | New script | Existing policy script |
|---|---|---|---|
| No | 32-bit | 32-bit PowerShell host supported | Runs only in 32-bit PowerShell host, which works on 32-bit and 64-bit architectures. |
| Yes | 64-bit | Runs script in 64-bit PowerShell host for 64-bit architectures. When ran on 32-bit, the script runs in a 32-bit PowerShell host. | Runs script in 32-bit PowerShell host. If this setting changes to 64-bit, the script opens (it doesn’t run) in a 64-bit PowerShell host, and reports the results. When ran on 32-bit, the script runs in 32-bit PowerShell host. |
You can optionally select “Scope tags.” If needed, choose an existing scope tag from a list you created earlier that meets your requirements. Once you’ve made your selection, click “Next” to proceed.
To assign the script, Navigate to “Assignments” and choose “Included groups.” Click on “Add groups” and select the appropriate group or groups you wish to deploy the policy to. You can choose multiple groups. Finally, click “Next” to proceed.
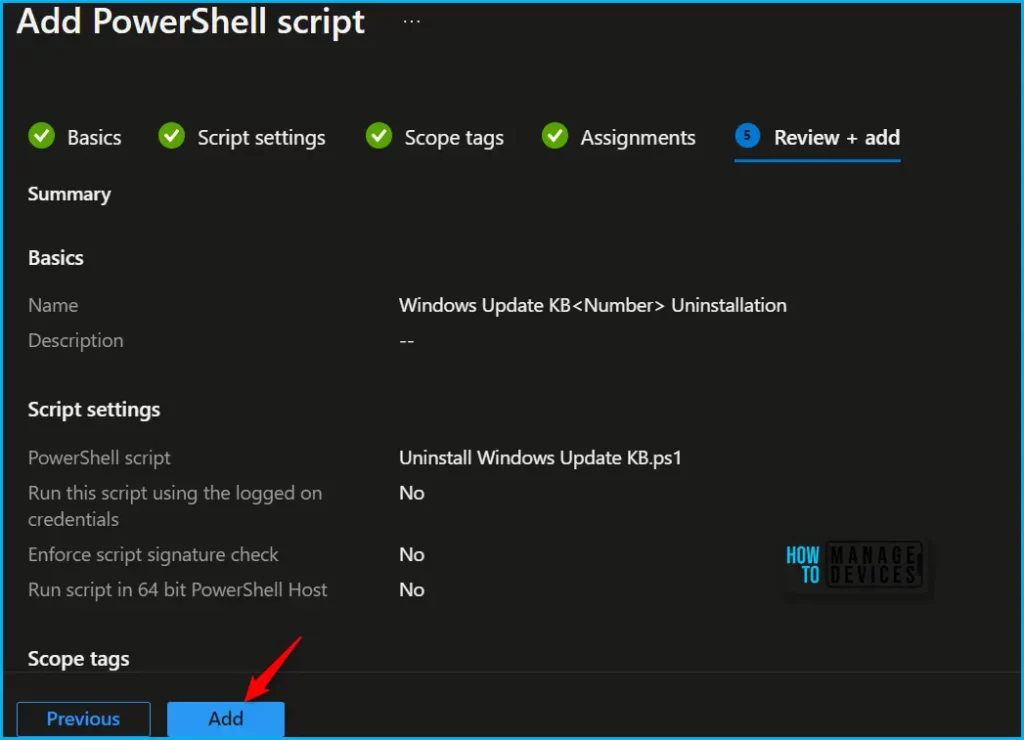
After reviewing, click on “Add” to save the script and view the configured settings. Once saved, the script will be deployed to the assigned device groups.
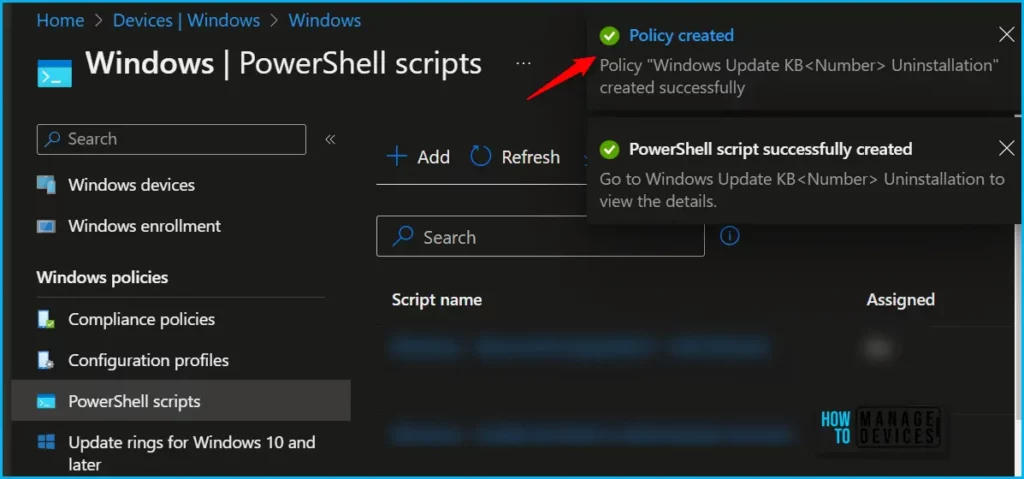
A notification will appear automatically in the top right-hand corner with a message. You can see that the PoweShell script successfully created. If you check, the script is available in the PowerShell scripts list for uninstalling Windows update.
Monitor Deployment
If you’re looking to monitor the run status of a PowerShell script, you can easily do so in the Intune portal. This feature allows you to track the script’s run status for both users and devices.
To monitor the run status of a PowerShell script, simply navigate to the Intune portal and select the “Devices” or “Users” option from the left-hand menu. From there, select the group or individual you wish to monitor and click on the “Scripts” tab.
Here, you’ll be able to see a list of all the scripts that have been run for the selected group or user, along with their run status. The run status can be one of the following:
- Succeeded: The script ran successfully.
- Error: The script encountered an error during execution.
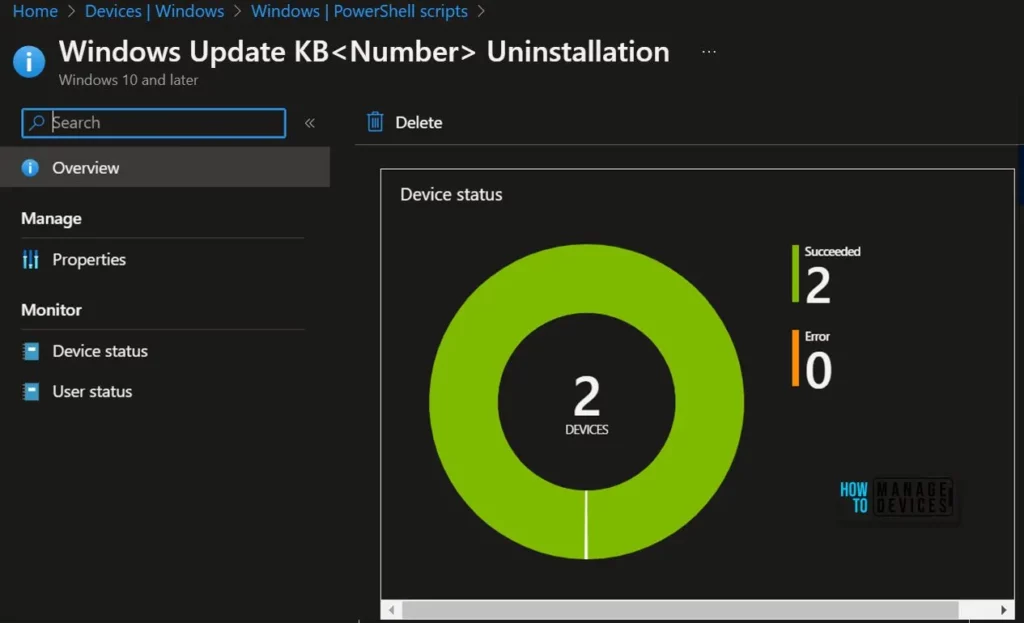
This information can be invaluable when it comes to troubleshooting and ensuring that your scripts are running as intended. By regularly monitoring the run status of your PowerShell scripts, you can quickly identify any issues and take appropriate action to address them.
Author
About Author – Jitesh, Microsoft MVP, has over six years of working experience in the IT Industry. He writes and shares his experiences related to Microsoft device management technologies and IT Infrastructure management. His primary focus is Windows 10/11 Deployment solution with Configuration Manager, Microsoft Deployment Toolkit (MDT), and Microsoft Intune.



Interesting. Deployed as a proactive remediation script you could monitor your all fleet.
Just remember that proactive remediation means additional licenses. https://www.anoopcnair.com/intune-proactive-remediation-scripts-powershell/