Windows 11 new LSA Local Security Authority policies are released as part of the insider build. I have checked the Intune Settings Catalog and these new policies are unavailable there. A few months before, Microsoft introduced the LAPS policies for Azure AD joined devices as part of the Insider build.
One of the new group policies controls the configuration under LSASS loads custom SSPs and APs. Windows 11 added support to disable custom Windows Security Support Providers (SSPs) and Authentication Packages (APs) to be loaded into LSASS.
The new Local Security Authority (LSA) group policy controls the configuration under which LSASS is run. This policy allows admins to configure LSA to run as a protected process. For example, If the admin configures and sets this policy setting to “Disabled,” LSA will not run as a protected process.
September 2022 Patch Tuesday Cumulative Update addresses a race condition that causes the Local Security Authority Subsystem Service (LSASS) to stop working on Active Directory domain controllers.
- Azure AD LAPs Group Policy Settings for Windows 11 | Intune Policy for LAPs
- List of Windows 11 Group Policy Settings
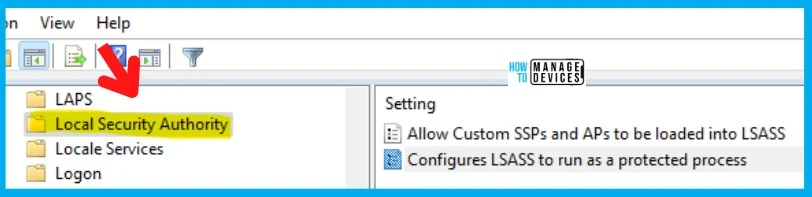
Allow Custom SSPs and APs to be loaded into LSASS Policy
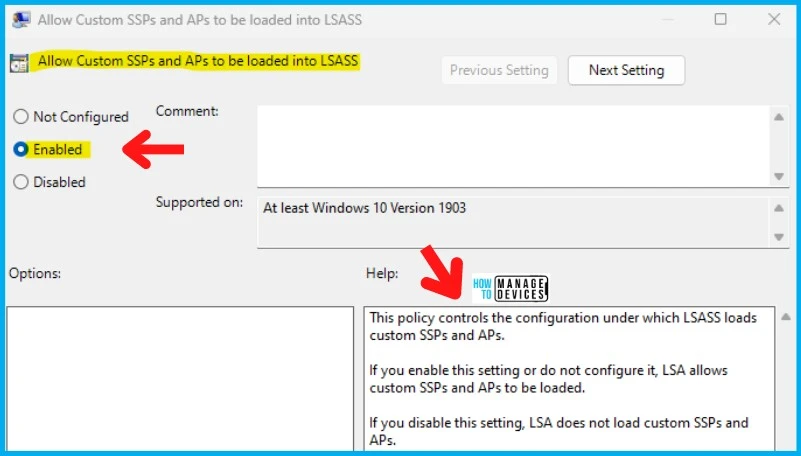
Allow Custom SSPs and APs to be loaded into LSASS Policy is one of the new group policies introduced to the Windows Insider build recently. Microsoft has not released any documentation about this new group policy setting yet.
This policy controls the configuration under which LSASS loads custom SSPs and APs. If you enable this setting or do not configure it, LSA allows custom SSPs and APs to be loaded. If you disable this setting, LSA does not load custom SSPs and APs.
- Policy Path -> Computer Configuration > Administrative Templates > System > Local Security Authority
| Enable/Not Configure | Disable |
|---|---|
| Local Security Authority allows custom SSPs and APs to be loaded | Local Security Authority does not load custom SSPs and APs |
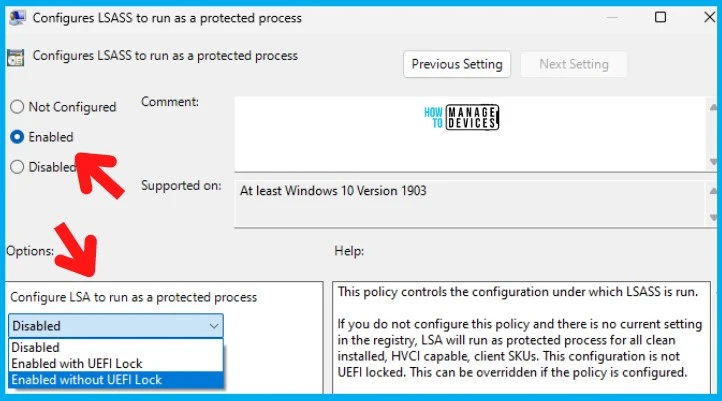
Configure LSASS to run as protected process Group Policy
Let’s check the details of the 2nd policy Configure LSASS to run as a protected process. Learn how this policy protects the Local Security Authority Subsystem Service (LSASS) as a process. Admins can enable protection with or without UEFI Lock.
If the admin doesn’t configure this policy and there is no current setting in the registry, LSA will run as a protected process for all clean installed, HVCI capable, client SKUs. This configuration is not UEFI locked. This can be overridden if the policy is configured.
If the admin configures and sets this policy setting to “Disabled,” LSA will not run as a protected process. If the admin configures and sets this policy setting to “EnabledWithUEFILock,” LSA will run as a protected process, and this configuration is UEFI locked.
NOTE! – If the admin configures and sets LSASS to run as a protected process Group Policy setting to “EnabledWithoutUEFILock,” LSA will run as a protected process, and this configuration is not UEFI locked.
- Policy Path -> Computer Configuration > Administrative Templates > System > Local Security Authority
| Not Configured | Disabled | EnabledWithUEFILock | EnabledWithoutUEFILock |
|---|---|---|---|
| LSA will run as a protected process & this process won’t be UEFI locked | LSA will not run as a protected process | LSA will run as a protected process, and this configuration is UEFI locked | LSA will run as a protected process, and this configuration is not UEFI locked |
Resource -> Configuring Additional LSA Protection | Microsoft Docs
Author
Anoop C Nair is Microsoft MVP! He is a Device Management Admin with more than 20 years of experience (calculation done in 2021) in IT. He is Blogger, Speaker, and Local User Group HTMD Community leader. His main focus is on Device Management technologies like SCCM 2012, Current Branch, and Intune. He writes about ConfigMgr, Windows 11, Windows 10, Azure AD, Microsoft Intune, Windows 365, AVD, etc.


I’m running with LSA activated (the Local Security Authority process is in my task manager list of running processes as lsass.exe, so I know it is active.
I have device guard under my gpedit, and credential guard is on in my system information screen.
But why do I not see the “Local Security Authority” folder on my local group policy editor? It is missing from there, so I would like some way to get it back.
Cheers