Let’s discuss Windows AutoPilot Devices Azure AD Dynamic Groups Intune. In the previous post, I explained Windows AutoPilot deployment.
In this post, we will see another useful tip for enterprise AutoPilot implementation. We can create Azure AD (AAD) dynamic device groups based on Windows AutoPilot profiles.
Windows AutoPilot Profile AAD Dynamic Device Groups help deploy application and security policies to each department as part of the device enrollment process.
I have a post that discusses the logic of Azure AD dynamic queries in more detail. This post does not cover how to create a Windows AutoPilot Profile AAD Dynamic Device Group.
Table of Contents
Video Tutorial – Windows AutoPilot Profile AAD Dynamic Device Groups
The following video will explain how dynamic security policies and apps can be deployed to Windows AutoPilot devices.
- Beginners Guide Setup Windows AutoPilot
- Where is the AutoPilot Assign Profile Button in Intune Portal
- Windows AutoPilot End to End Process Guide
What are AAD Dynamic Device Groups?
AAD dynamic Device groups are similar to dynamic device collections in the SCCM world. Azure AD (AAD) dynamic device group is a set of devices grouped together based on a common attribute value.
This can be used to target different security policies and applications to a specific group of devices, which is very important in the modern world of device management using Microsoft Intune.
Create a New Windows AutoPilot Deployment Profile
For this post, I will create an AutoPilot Deployment profile to customize the OOBE experience for the end-user. The Windows AutoPilot profile provides only three (3) customization options. As shown in the video tutorial, I have created a new AutoPilot profile called “Sales Team Profile“.
This Sales Team Profile will enroll all the Windows 10 devices from the sales and marketing department. This deployment profile name will be used to create the Windows AutoPilot Profile AAD Dynamic Device Group.
- Navigate via Azure Portal -> Microsoft Intune -> Device Enrollment – Windows Enrollment
- Click on Deployment profiles under Windows Autopilot Deployment Program and select Create a profile.
- In the Create profile blade, set the name to “Sales Team Profile“, click on Out-of-box experience (OOBE) and configure the following:
OOBE Customization Settings
- Privacy Settings >Value > Hide
- End-user license agreement (EULA) >Value> Hide
- User account type Standard or Administrator >Value> Standard User
How to Create Windows AutoPilot Profile AAD Dynamic Device Groups?
Once the Autopilot deployment profile has been created, we can “group” the devices assigned to “Sales Team Profile” dynamically based on the following Azure AD attribute:-
| Azure AD attribute |
|---|
| OrderID |
| PurchaseOrderId |
| devicePhysicalIDs |
So all the devices assigned to the Windows AutoPilot deployment profile will automatically get added to the Azure AD dynamic device group. Let’s see how to create Windows AutoPilot Profile AAD Dynamic Device Groups.
- Navigate via Azure Portal -> Azure Active Directory -> Groups – All Groups –>
- Click on “+ New Group“
- Select Security as Group Type
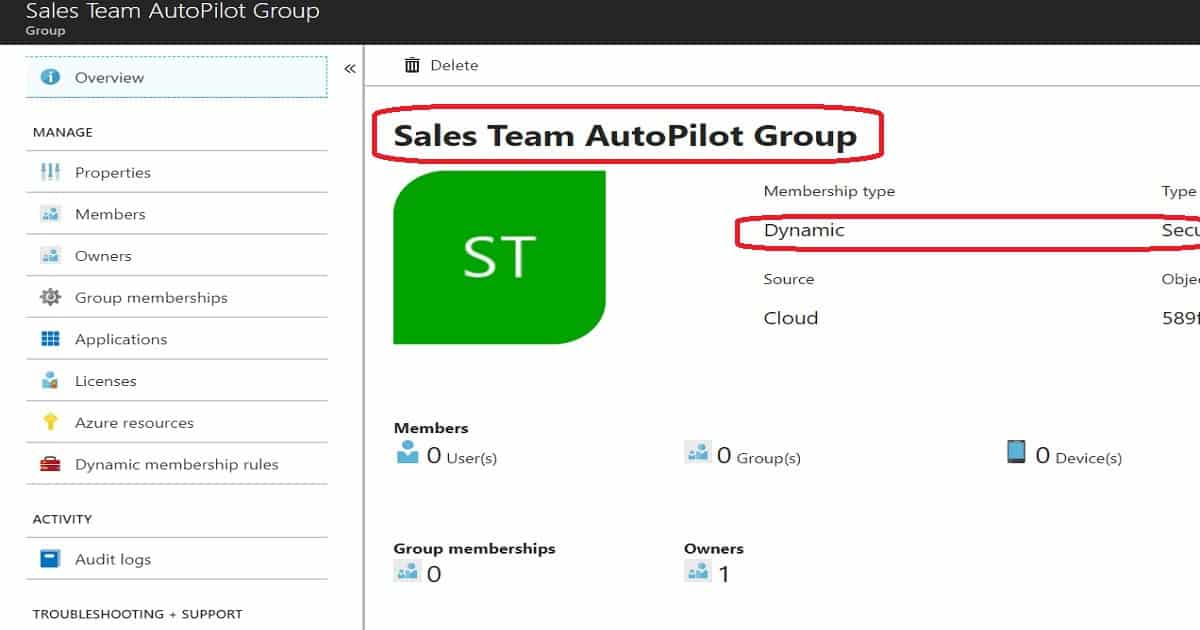
- Enter the Group Name “Sales Team AutoPilot Group” (any name is fine)
- Enter Group Description “Windows AutoPilot Profile AAD group for Sales Dept” (any description is fine)
- Select Dynamic Device as the Membership type
- Click on Add Dynamic Query under Dynamic Device Members
- On the Dynamic Membership Rules blade, select OrderID from the “Add Devices Where” column
- Select the operator as Equals
- Enter OderID for the profile and its “Sales Team Profile“
- Click on add query button
- Click on the Create button to create an AAD Dynamic device group based on the AutoPilot Profile
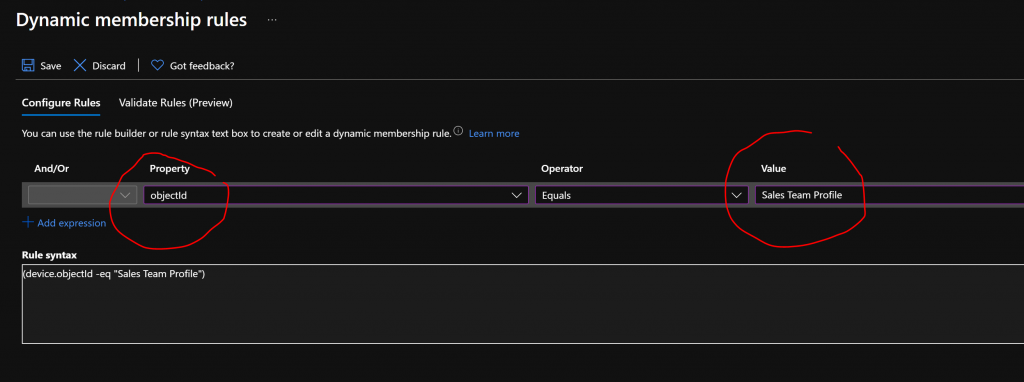
Autopilot Azure AD Dynamic Query ==> I recommend using the device.devicePhysicalIds.
- (device.devicePhysicalIds -any _ -contains “Sales Team Profile”)
- (device.devicePhysicalIds -any _ -contains “Sales Team”)
How to Dynamically Deploy Security Policies & Apps to Windows AutoPilot Profile
We have now created an Azure AD dynamic device group associated with the Windows AutoPilot profile. Whenever a device gets assigned to the Windows AutoPilot profile, you can use the AAD dynamic device group to deploy security policies or applications.
Assign an application to the Azure AD dynamic device group associated with the Windows Autopilot profile. Dynamically deploy security policies & apps to Windows AutoPilot devices.
- Navigate via Azure Portal –> Microsoft Intune –> Microsoft Endpoint Manager – Applications
- Select the application called “MBCA“
- Select Assignments from the App blade
- Click on “Add Group” from Group blame
- Select Assigned Type “Required” from Add Group blame
- Select AAD dynamic Group “Sales Team AutoPilot Group” from “Included Groups”
- Click on the Select button
- Click the OK – OK button
- Click Save button
We are on WhatsApp. To get the latest step-by-step guides and news updates, Join our Channel. Click here –HTMD WhatsApp.
Author
Anoop C Nair is Microsoft MVP! He is a Device Management Admin with more than 20 years of experience (calculation done in 2021) in IT. He is a Blogger, Speaker, and Local User Group HTMD Community leader. His primary focus is Device Management technologies like SCCM 2012, Current Branch, and Intune. He writes about ConfigMgr, Windows 11, Windows 10, Azure AD, Microsoft Intune, Windows 365, AVD, etc.



How to create a dynamic device group for all compliant devices?