Key Takeaways
- May 2026 Patch Tuesday fixes several Critical security vulnerabilities in Windows, Office, SharePoint, DNS, and WiFi components.
- Many vulnerabilities are related to Elevation of Privilege, which attackers can use to gain higher access on compromised devices.
- Microsoft Office, Word, Excel, and SharePoint received important Remote Code Execution security fixes and should be patched quickly.
- Windows networking components like TCP/IP, SMB, DNS Client, and Netlogon also received important security updates.
- No zero-day vulnerabilities are currently reported as exploited, but admins should deploy updates as soon as possible to reduce security risks.
2026 May Security Update! Microsoft released the May 2026 Patch Tuesday security updates with fixes for 120 vulnerabilities and no publicly disclosed zero-day vulnerabilities. This month’s release includes 17 Critical vulnerabilities, including 14 Remote Code Execution (RCE) flaws, 2 Elevation of Privilege vulnerabilities, and 1 Information Disclosure vulnerability.
Table of Content
Table of Contents
2026 May Security Update | Critical and High-Risk Vulnerabilities You Must Patch Immediately
The updates also address multiple security issues across Windows, Microsoft Office, SharePoint, SQL Server, Hyper-V, TCP/IP, DNS Client, and other core Microsoft products and services. Organisations are recommended to prioritise testing and deploying these updates quickly to reduce potential security risks.
| Critical and High-Risk Vulnerabilities |
|---|
| 61 Elevation of Privilege Vulnerabilities |
| 6 Security Feature Bypass Vulnerabilities |
| 31 Remote Code Execution Vulnerabilities |
| 14 Information Disclosure Vulnerabilities |
| 8 Denial of Service Vulnerabilities |
| 13 Spoofing Vulnerabilities |
- April 2026 Security Update | Critical and High-Risk Vulnerabilities You Must Patch Immediately
- Windows 11 Version Numbers Build Numbers Major Minor Build Rev
- Updated Windows 11 End-of-Life Dates
- Top 83 Windows 11 Desktop Admin Interview Questions
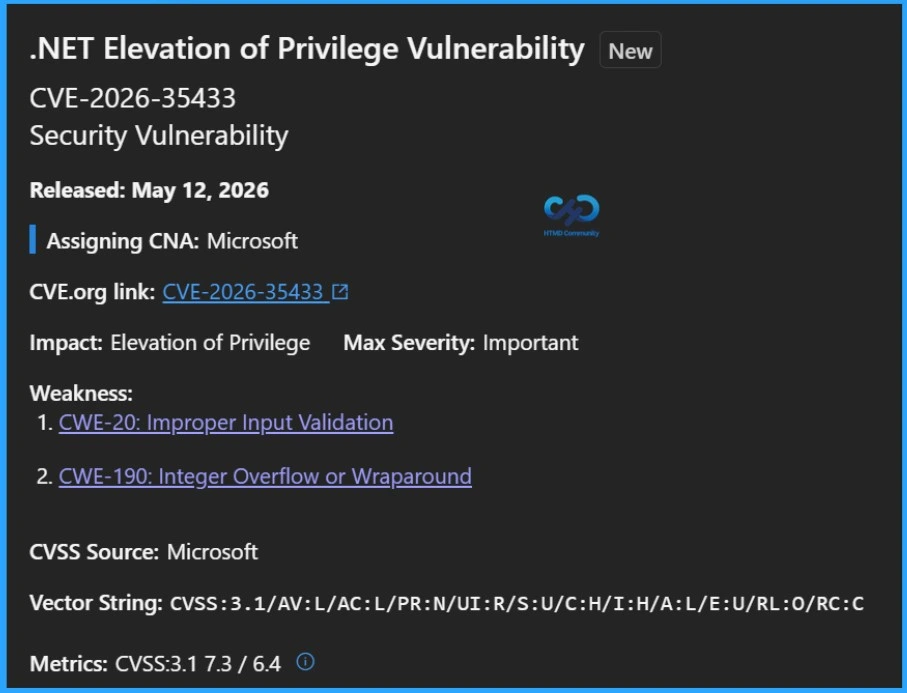
Elevation of Privilege Vulnerabilities
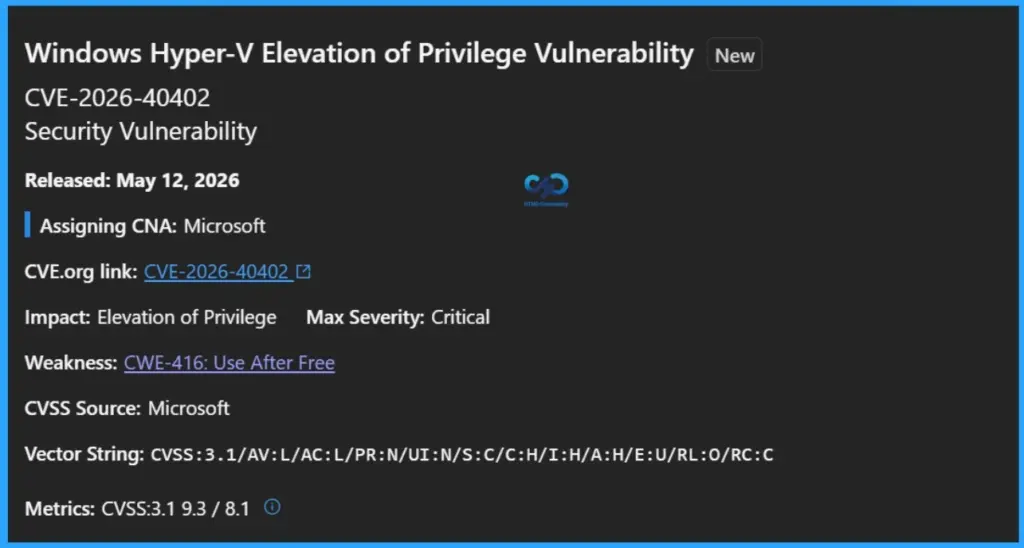
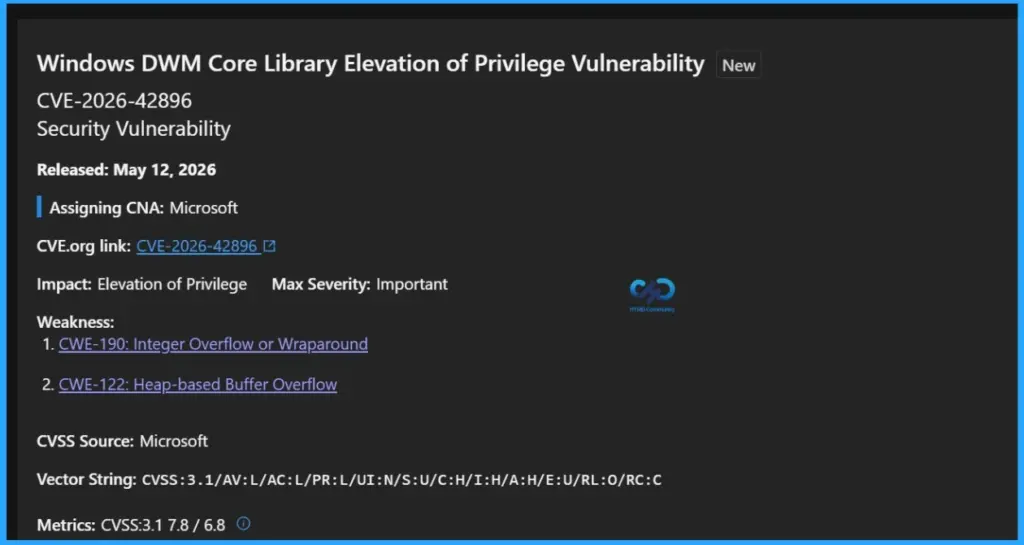
The May 2026 Patch Tuesday release includes a large number of Elevation of Privilege (EoP) vulnerabilities affecting Windows Kernel, Win32k, TCP/IP, Hyper-V, SMB, Telephony Service, Office Click-To-Run, Azure services, .NET, Visual Studio Code, and other core Microsoft components. These vulnerabilities could allow attackers to gain higher system privileges after initially accessing a device or environment.
- CVE-2026-42896 Windows DWM Core Library Elevation of Privilege Vulnerability
- CVE-2026-42830 Azure Monitor Agent Metrics Extension Elevation of Privilege Vulnerability
- CVE-2026-42825 Windows Telephony Service Elevation of Privilege Vulnerability
- CVE-2026-42823 Azure Logic Apps Elevation of Privilege Vulnerability
- CVE-2026-41613 Visual Studio Code Elevation of Privilege Vulnerability
- CVE-2026-41103 Microsoft SSO Plugin for Jira & Confluence Elevation of Privilege Vulnerability
- CVE-2026-41095 Data Deduplication Elevation of Privilege Vulnerability
- CVE-2026-41088 Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
- CVE-2026-41086 Windows Admin Center in Azure Portal Elevation of Privilege Vulnerability
- CVE-2026-40420 Microsoft Office Click-To-Run Elevation of Privilege Vulnerability
- CVE-2026-40419 Microsoft Office Click-To-Run Elevation of Privilege Vulnerability
- CVE-2026-40418 Microsoft Office Click-To-Run Elevation of Privilege Vulnerability
- CVE-2026-40417 Microsoft Dynamics 365 Business Central Elevation of Privilege Vulnerability
- CVE-2026-40410 Windows SMB Client Elevation of Privilege Vulnerability
- CVE-2026-40408 Windows WAN ARP Driver Elevation of Privilege Vulnerability
- CVE-2026-40407 Windows Common Log File System Driver Elevation of Privilege Vulnerability
- CVE-2026-40402 Windows Hyper-V Elevation of Privilege Vulnerability
- CVE-2026-40399 Windows TCP/IP Elevation of Privilege Vulnerability
- CVE-2026-40398 Windows Remote Desktop Services Elevation of Privilege Vulnerability
- CVE-2026-40397 Windows Common Log File System Driver Elevation of Privilege Vulnerability
- CVE-2026-40382 Windows Telephony Service Elevation of Privilege Vulnerability
- CVE-2026-40381 Azure Connected Machine Agent Elevation of Privilege Vulnerability
- CVE-2026-40377 Microsoft Cryptographic Services Elevation of Privilege Vulnerability
- CVE-2026-40369 Windows Kernel Elevation of Privilege Vulnerability
- CVE-2026-35438 Windows Admin Center Elevation of Privilege Vulnerability
- CVE-2026-35436 Microsoft Office Click-To-Run Elevation of Privilege Vulnerability
- CVE-2026-35433 .NET Elevation of Privilege Vulnerability
- CVE-2026-35420 Windows Kernel Elevation of Privilege Vulnerability
- CVE-2026-35418 Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability
- CVE-2026-35417 Windows Win32k Elevation of Privilege Vulnerability
- CVE-2026-35416 Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
- CVE-2026-35415 Windows Storage Spaces Controller Elevation of Privilege Vulnerability
- CVE-2026-34351 Windows TCP/IP Elevation of Privilege Vulnerability
- CVE-2026-34347 Windows Win32k Elevation of Privilege Vulnerability
- CVE-2026-34345 Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
- CVE-2026-34344 Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
- CVE-2026-34343 Windows Application Identity (AppID) Subsystem Elevation of Privilege Vulnerability
- CVE-2026-34342 Windows Print Spooler Elevation of Privilege Vulnerability
- CVE-2026-34341 Windows Link-Layer Discovery Protocol (LLDP) Elevation of Privilege Vulnerability
- CVE-2026-34340 Windows Projected File System Elevation of Privilege Vulnerability
- CVE-2026-34338 Windows Telephony Service Elevation of Privilege Vulnerability
- CVE-2026-34337 Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability
- CVE-2026-34334 Windows TCP/IP Elevation of Privilege Vulnerability
- CVE-2026-34333 Windows Win32k Elevation of Privilege Vulnerability
- CVE-2026-34331 Win32k Elevation of Privilege Vulnerability
- CVE-2026-34330 Win32k Elevation of Privilege Vulnerability
- CVE-2026-33841 Windows Kernel Elevation of Privilege Vulnerability
- CVE-2026-33840 Win32k Elevation of Privilege Vulnerability
- CVE-2026-33839 Win32k Elevation of Privilege Vulnerability
- CVE-2026-33838 Windows Message Queuing (MSMQ) Elevation of Privilege Vulnerability
- CVE-2026-33837 Windows TCP/IP Local Elevation of Privilege Vulnerability
- CVE-2026-33835 Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability
- CVE-2026-33834 Windows Event Logging Service Elevation of Privilege Vulnerability
- CVE-2026-32204 Azure Monitor Agent Elevation of Privilege Vulnerability
- CVE-2026-32177 .NET Elevation of Privilege Vulnerability
- CVE-2026-32170 Windows Rich Text Edit Elevation of Privilege Vulnerability
- CVE-2026-21530 Windows Rich Text Edit Elevation of Privilege Vulnerability
- CVE-2025-54518 AMD: CVE-2025-54518 CPU OP Cache Corruption
Security Feature Bypass Vulnerabilities
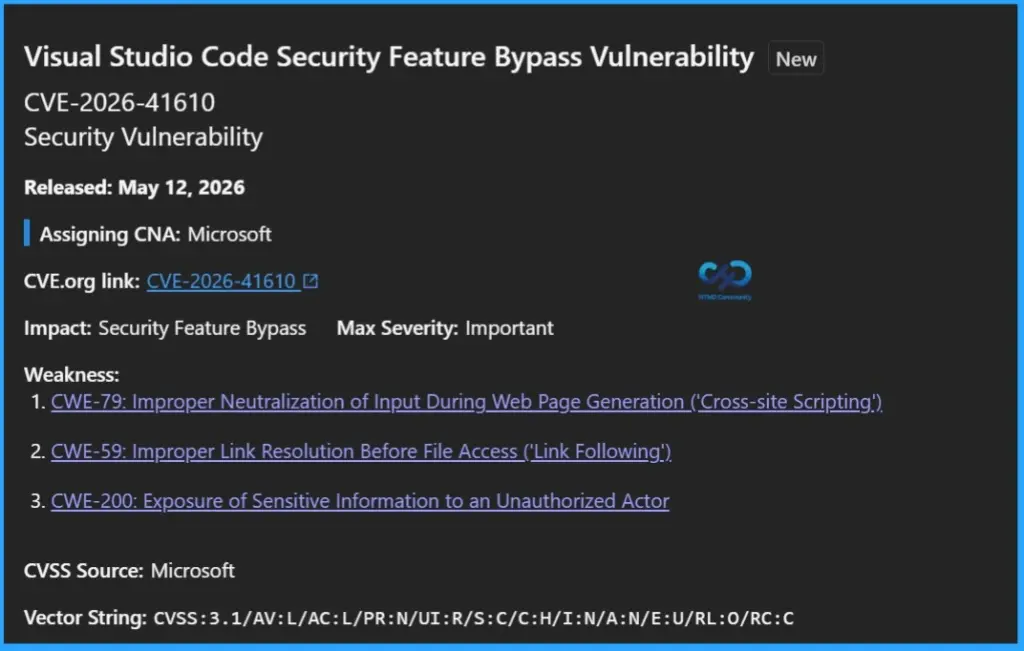
The May 2026 Patch Tuesday updates also fix several Security Feature Bypass vulnerabilities affecting Visual Studio Code, GitHub Copilot, Secure Boot, Windows TCP/IP Driver, Azure SDK for Java, and Windows Filtering Platform (WFP). These vulnerabilities could allow attackers to bypass important security protections and safeguards built into Windows and Microsoft applications.
- CVE-2026-41610 Visual Studio Code Security Feature Bypass Vulnerability
- CVE-2026-41109 GitHub Copilot and Visual Studio Code Security Feature Bypass Vulnerability
- CVE-2026-41097 Secure Boot Security Feature Bypass Vulnerability
- CVE-2026-35422 Windows TCP/IP Driver Security Feature Bypass Vulnerability
- CVE-2026-33117 Azure SDK for Java Security Feature Bypass Vulnerability
- CVE-2026-32209 Windows Filtering Platform (WFP) Security Feature Bypass Vulnerability
Remote Code Execution Vulnerabilities
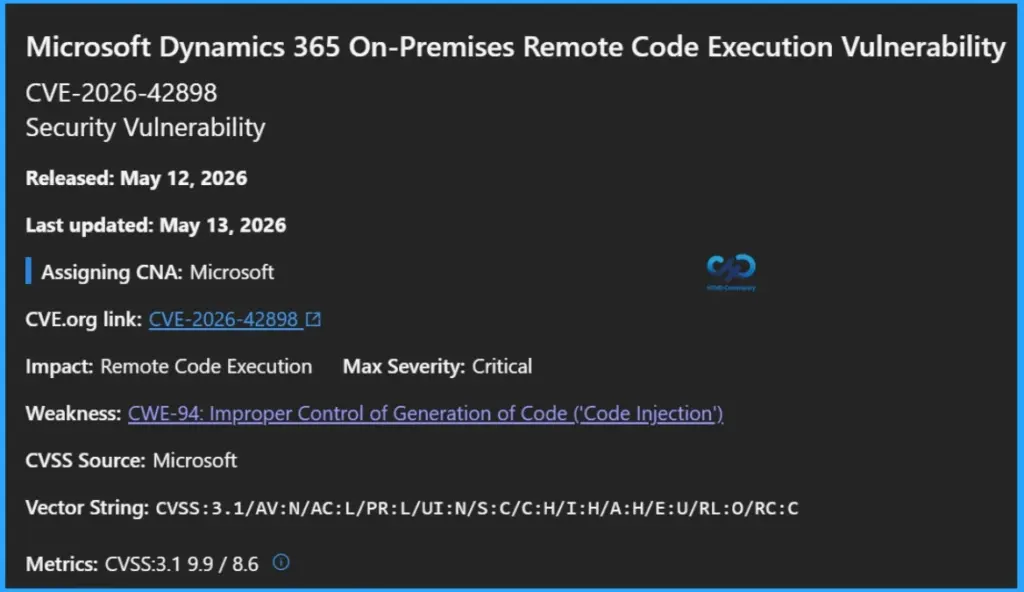
The May 2026 Patch Tuesday release includes multiple Remote Code Execution (RCE) vulnerabilities affecting Microsoft Dynamics 365 On-Premises, Microsoft Office, Visual Studio Code, and Windows DNS Client. These vulnerabilities could allow attackers to run malicious code on affected systems, potentially leading to system compromise, data theft, or further attacks across the network.
- CVE-2026-42898 Microsoft Dynamics 365 On-Premises Remote Code Execution Vulnerability
- CVE-2026-42833 Microsoft Dynamics 365 On-Premises Remote Code Execution Vulnerability
- CVE-2026-42831 Microsoft Office Remote Code Execution Vulnerability
- CVE-2026-41611 Visual Studio Code Remote Code Execution Vulnerability
- CVE-2026-41096 Windows DNS Client Remote Code Execution Vulnerability
- CVE-2026-41094 Microsoft Data Formulator Remote Code Execution Vulnerability
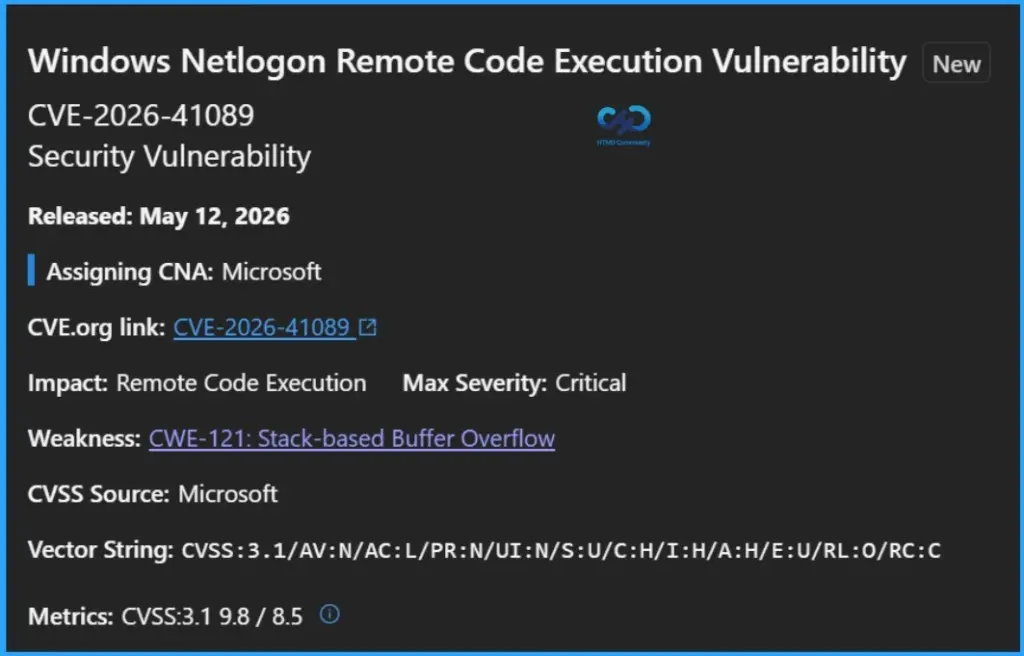
- CVE-2026-41089 Windows Netlogon Remote Code Execution Vulnerability
- CVE-2026-40415 Windows TCP/IP Remote Code Execution Vulnerability
- CVE-2026-40403 Windows Graphics Component Remote Code Execution Vulnerability
- CVE-2026-40380 Windows Volume Manager Extension Driver Remote Code Execution Vulnerability
- CVE-2026-40370 SQL Server Remote Code Execution Vulnerability
- CVE-2026-40368 Microsoft SharePoint Server Remote Code Execution Vulnerability
- CVE-2026-40367 Microsoft Word Remote Code Execution Vulnerability
- CVE-2026-40366 Microsoft Word Remote Code Execution Vulnerability
- CVE-2026-40365 Microsoft SharePoint Server Remote Code Execution Vulnerability
- CVE-2026-40364 Microsoft Word Remote Code Execution Vulnerability
- CVE-2026-40363 Microsoft Office Remote Code Execution Vulnerability
- CVE-2026-40362 Microsoft Excel Remote Code Execution Vulnerability
- CVE-2026-40361 Microsoft Word Remote Code Execution Vulnerability
- CVE-2026-40359 Microsoft Excel Remote Code Execution Vulnerability
- CVE-2026-40358 Microsoft Office Remote Code Execution Vulnerability
- CVE-2026-40357 Microsoft SharePoint Server Remote Code Execution Vulnerability
- CVE-2026-35439 Microsoft SharePoint Server Remote Code Execution Vulnerability
- CVE-2026-35421 Windows GDI Remote Code Execution Vulnerability
- CVE-2026-34332 Windows Kernel-Mode Driver Remote Code Execution Vulnerability
- CVE-2026-34329 Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability
- CVE-2026-33112 Microsoft SharePoint Server Remote Code Execution Vulnerability
- CVE-2026-33110 Microsoft SharePoint Server Remote Code Execution Vulnerability
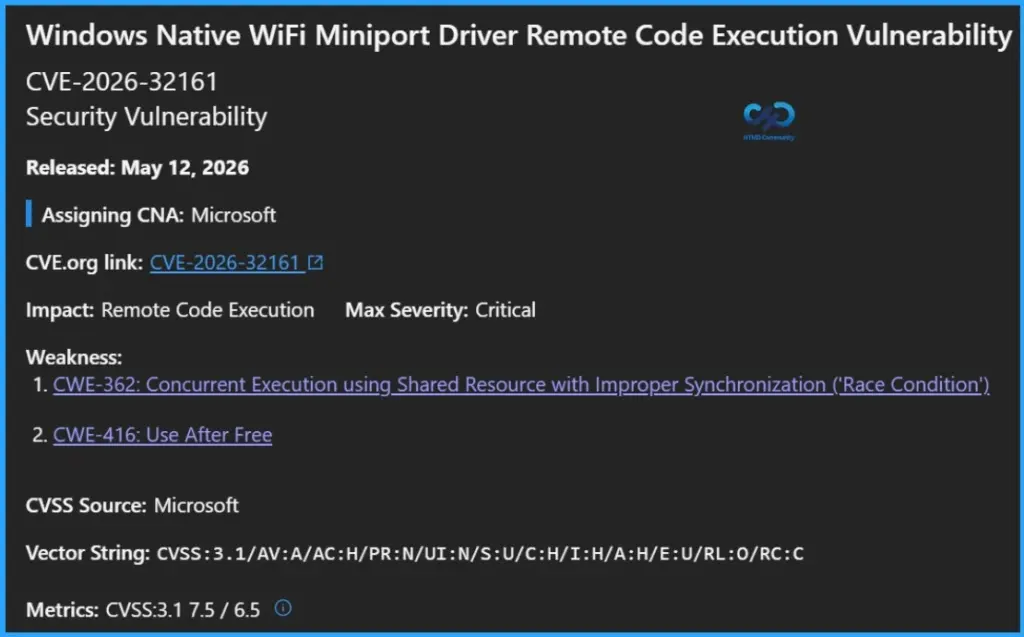
- CVE-2026-32161 Windows Native WiFi Miniport Driver Remote Code Execution Vulnerability
Information Disclosure Vulnerabilities
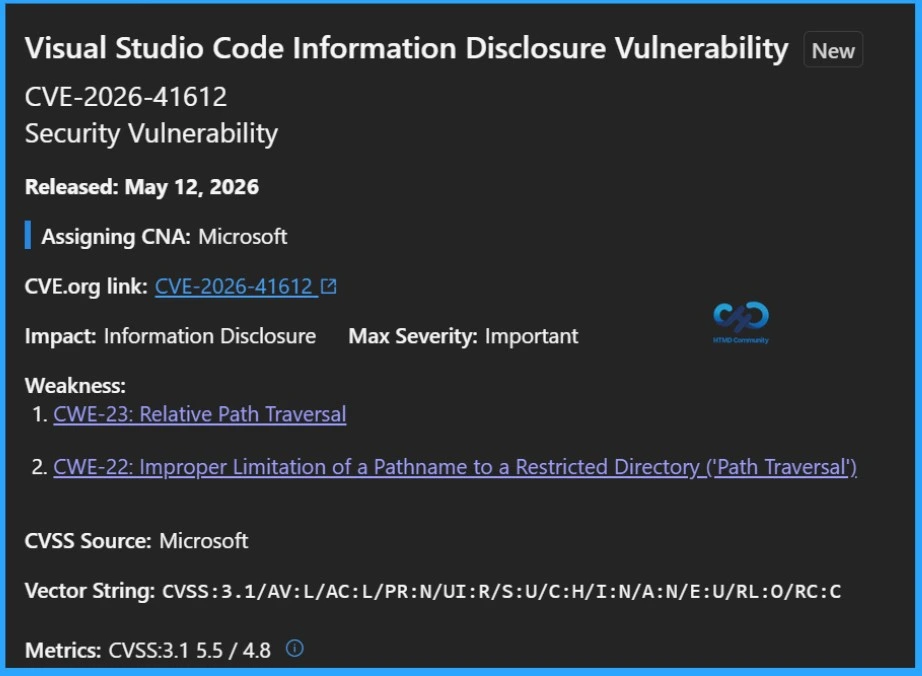
The May 2026 Patch Tuesday updates fix several Information Disclosure vulnerabilities affecting Visual Studio Code, Microsoft Word, Excel, Windows TCP/IP, Power Automate Desktop, Windows 11 Telnet Client, and Windows DWM Core Library.
- CVE-2026-41612 Visual Studio Code Information Disclosure Vulnerability
- CVE-2026-40421 Microsoft Word Information Disclosure Vulnerability
- CVE-2026-40406 Windows TCP/IP Information Disclosure Vulnerability
- CVE-2026-40374 Microsoft Power Automate Desktop Information Disclosure Vulnerability
- CVE-2026-40360 Microsoft Excel Information Disclosure Vulnerability
- CVE-2026-35440 Microsoft Word Information Disclosure Vulnerability
- CVE-2026-35423 Windows 11 Telnet Client Information Disclosure Vulnerability
- CVE-2026-35419 Windows DWM Core Library Information Disclosure Vulnerability
- CVE-2026-34336 Windows DWM Core Library Information Disclosure Vulnerability
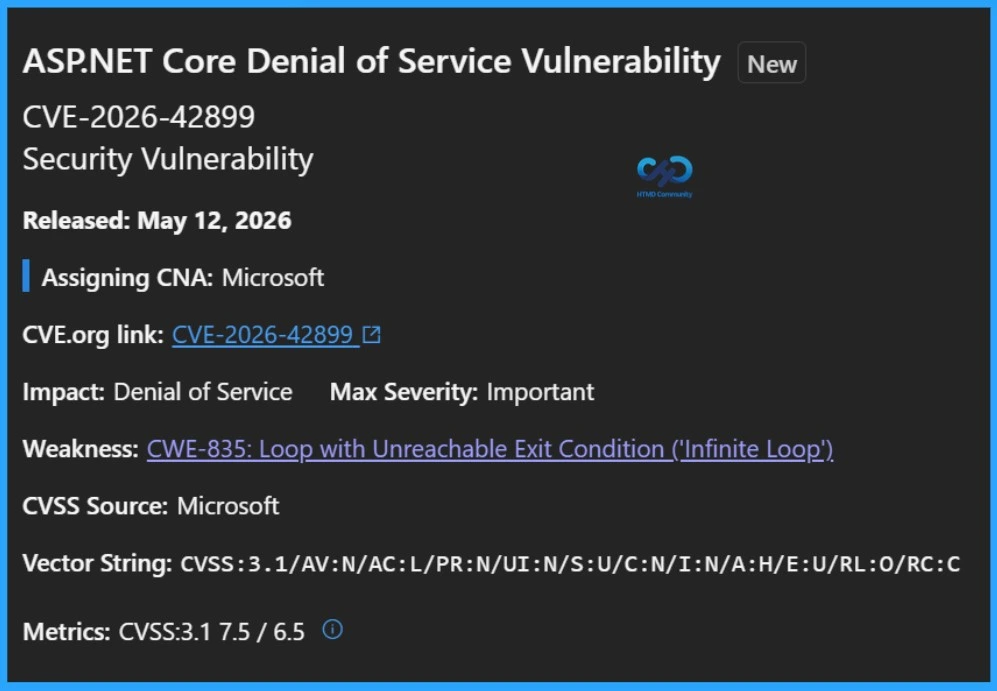
Denial of Service Vulnerabilities
The May 2026 Patch Tuesday release includes several Denial of Service (DoS) vulnerabilities affecting ASP.NET Core, Windows TCP/IP, Internet Key Exchange (IKE), LDAP, and Windows storage drivers. These vulnerabilities could allow attackers to disrupt services, crash systems, or make applications and network services temporarily unavailable.
- CVE-2026-42899 ASP.NET Core Denial of Service Vulnerability
- CVE-2026-40414 Windows TCP/IP Denial of Service Vulnerability
- CVE-2026-40413 Windows TCP/IP Denial of Service Vulnerability
- CVE-2026-40405 Windows TCP/IP Denial of Service Vulnerability
- CVE-2026-40401 Windows TCP/IP Denial of Service Vulnerability
- CVE-2026-35424 Internet Key Exchange (IKE) Protocol Denial of Service Vulnerability
- CVE-2026-34350 Windows Storport Miniport Driver Denial of Service Vulnerability
- CVE-2026-34339 Windows Lightweight Directory Access Protocol (LDAP) Denial of Service Vulnerability
Spoofing Vulnerabilities
The May 2026 Patch Tuesday updates also address several Spoofing vulnerabilities affecting Microsoft Office, Microsoft Teams, Microsoft 365 Copilot, PowerPoint for Android, Word for Android, and Azure Machine Learning Notebook. These vulnerabilities could allow attackers to impersonate trusted users, applications, or services to trick users into opening malicious content or sharing sensitive information.
- CVE-2026-42832 Microsoft Office Spoofing Vulnerability
- CVE-2026-41614 M365 Copilot for Desktop Spoofing Vulnerability
- CVE-2026-41102 Microsoft PowerPoint for Android Spoofing Vulnerability
- CVE-2026-41101 Microsoft Word for Android Spoofing Vulnerability
- CVE-2026-41100 Microsoft 365 Copilot for Android Spoofing Vulnerability
- CVE-2026-33833 Azure Machine Learning Notebook Spoofing Vulnerability
- CVE-2026-32185 Microsoft Teams Spoofing Vulnerability

May 2026 Patch Tuesday Security Updates
Microsoft released the May 2026 Patch Tuesday security updates with fixes for multiple vulnerabilities affecting Windows, Microsoft Office, SharePoint, SQL Server, Azure services, and other Microsoft products. The list below includes all resolved vulnerabilities covered in this month’s security release.
| CVE ID | CVE Title | Severity |
|---|---|---|
| CVE-2026-35433 | .NET Elevation of Privilege Vulnerability | Important |
| CVE-2026-32177 | .NET Elevation of Privilege Vulnerability | Important |
| CVE-2026-32175 | .NET Core Tampering Vulnerability | Important |
| CVE-2025-54518 | AMD: CVE-2025-54518 CPU OP Cache Corruption | Important |
| CVE-2026-42899 | ASP.NET Core Denial of Service Vulnerability | Important |
| CVE-2026-40381 | Azure Connected Machine Agent Elevation of Privilege Vulnerability | Important |
| CVE-2026-42823 | Azure Logic Apps Elevation of Privilege Vulnerability | Important |
| CVE-2026-33833 | Azure Machine Learning Notebook Spoofing Vulnerability | Important |
| CVE-2026-32204 | Azure Monitor Agent Elevation of Privilege Vulnerability | Important |
| CVE-2026-42830 | Azure Monitor Agent Metrics Extension Elevation of Privilege Vulnerability | Important |
| CVE-2026-33117 | Azure SDK for Java Security Feature Bypass Vulnerability | Important |
| CVE-2026-41095 | Data Deduplication Elevation of Privilege Vulnerability | Important |
| CVE-2026-40417 | Microsoft Dynamics 365 Business Central Elevation of Privilege Vulnerability | Important |
| CVE-2026-41109 | GitHub Copilot and Visual Studio Code Security Feature Bypass Vulnerability | Important |
| CVE-2026-41100 | Microsoft 365 Copilot for Android Spoofing Vulnerability | Important |
| CVE-2026-42893 | Microsoft Outlook for iOS Tampering Vulnerability | Important |
| CVE-2026-26164 | M365 Copilot Information Disclosure Vulnerability | Critical |
| CVE-2026-41614 | M365 Copilot for Desktop Spoofing Vulnerability | Important |
| CVE-2026-41094 | Microsoft Data Formulator Remote Code Execution Vulnerability | Important |
| CVE-2026-42898 | Microsoft Dynamics 365 On-Premises Remote Code Execution Vulnerability | Critical |
| CVE-2026-42833 | Microsoft Dynamics 365 On-Premises Remote Code Execution Vulnerability | Important |
| CVE-2026-42832 | Microsoft Office Spoofing Vulnerability | Important |
| CVE-2026-42831 | Microsoft Office Remote Code Execution Vulnerability | Critical |
| CVE-2026-40363 | Microsoft Office Remote Code Execution Vulnerability | Critical |
| CVE-2026-40419 | Microsoft Office Click-To-Run Elevation of Privilege Vulnerability | Important |
| CVE-2026-40358 | Microsoft Office Remote Code Execution Vulnerability | Critical |
| CVE-2026-35436 | Microsoft Office Click-To-Run Elevation of Privilege Vulnerability | Important |
| CVE-2026-40420 | Microsoft Office Click-To-Run Elevation of Privilege Vulnerability | Important |
| CVE-2026-40418 | Microsoft Office Click-To-Run Elevation of Privilege Vulnerability | Important |
| CVE-2026-40360 | Microsoft Excel Information Disclosure Vulnerability | Important |
| CVE-2026-40362 | Microsoft Excel Remote Code Execution Vulnerability | Important |
| CVE-2026-40359 | Microsoft Excel Remote Code Execution Vulnerability | Important |
| CVE-2026-41102 | Microsoft PowerPoint for Android Spoofing Vulnerability | Important |
| CVE-2026-40368 | Microsoft SharePoint Server Remote Code Execution Vulnerability | Important |
| CVE-2026-35439 | Microsoft SharePoint Server Remote Code Execution Vulnerability | Important |
| CVE-2026-33112 | Microsoft SharePoint Server Remote Code Execution Vulnerability | Important |
| CVE-2026-40365 | Microsoft SharePoint Server Remote Code Execution Vulnerability | Critical |
| CVE-2026-40357 | Microsoft SharePoint Server Remote Code Execution Vulnerability | Important |
| CVE-2026-33110 | Microsoft SharePoint Server Remote Code Execution Vulnerability | Important |
| CVE-2026-40361 | Microsoft Word Remote Code Execution Vulnerability | Critical |
| CVE-2026-40367 | Microsoft Word Remote Code Execution Vulnerability | Critical |
| CVE-2026-35440 | Microsoft Word Information Disclosure Vulnerability | Important |
| CVE-2026-40421 | Microsoft Word Information Disclosure Vulnerability | Important |
| CVE-2026-41101 | Microsoft Word for Android Spoofing Vulnerability | Important |
| CVE-2026-40366 | Microsoft Word Remote Code Execution Vulnerability | Critical |
| CVE-2026-40364 | Microsoft Word Remote Code Execution Vulnerability | Critical |
| CVE-2026-41103 | Microsoft SSO Plugin for Jira & Confluence Elevation of Privilege Vulnerability | Critical |
| CVE-2026-32185 | Microsoft Teams Spoofing Vulnerability | Important |
| CVE-2026-41096 | Windows DNS Client Remote Code Execution Vulnerability | Critical |
| CVE-2026-40374 | Microsoft Power Automate Desktop Information Disclosure Vulnerability | Important |
| CVE-2026-40370 | SQL Server Remote Code Execution Vulnerability | Important |
| CVE-2026-35423 | Windows 11 Telnet Client Information Disclosure Vulnerability | Important |
| CVE-2026-41613 | Visual Studio Code Elevation of Privilege Vulnerability | Important |
| CVE-2026-41612 | Visual Studio Code Information Disclosure Vulnerability | Important |
| CVE-2026-41610 | Visual Studio Code Security Feature Bypass Vulnerability | Important |
| CVE-2026-41611 | Visual Studio Code Remote Code Execution Vulnerability | Important |
| CVE-2026-41086 | Windows Admin Center in Azure Portal Elevation of Privilege Vulnerability | Important |
| CVE-2026-35438 | Windows Admin Center Elevation of Privilege Vulnerability | Important |
| CVE-2026-35416 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Important |
| CVE-2026-41088 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Important |
| CVE-2026-34345 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Important |
| CVE-2026-34344 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Important |
| CVE-2026-34343 | Windows Application Identity (AppID) Subsystem Elevation of Privilege Vulnerability | Important |
| CVE-2026-34337 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | Important |
| CVE-2026-35418 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | Important |
| CVE-2026-33835 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | Important |
| CVE-2026-40397 | Windows Common Log File System Driver Elevation of Privilege Vulnerability | Important |
| CVE-2026-40407 | Windows Common Log File System Driver Elevation of Privilege Vulnerability | Important |
| CVE-2026-40377 | Microsoft Cryptographic Services Elevation of Privilege Vulnerability | Important |
| CVE-2026-34336 | Windows DWM Core Library Information Disclosure Vulnerability | Important |
| CVE-2026-42896 | Windows DWM Core Library Elevation of Privilege Vulnerability | Important |
| CVE-2026-35419 | Windows DWM Core Library Information Disclosure Vulnerability | Important |
| CVE-2026-33834 | Windows Event Logging Service Elevation of Privilege Vulnerability | Important |
| CVE-2026-32209 | Windows Filtering Platform (WFP) Security Feature Bypass Vulnerability | Important |
| CVE-2026-35421 | Windows GDI Remote Code Execution Vulnerability | Critical |
| CVE-2026-40402 | Windows Hyper-V Elevation of Privilege Vulnerability | Critical |
| CVE-2026-35424 | Internet Key Exchange (IKE) Protocol Denial of Service Vulnerability | Important |
| CVE-2026-40369 | Windows Kernel Elevation of Privilege Vulnerability | Important |
| CVE-2026-33841 | Windows Kernel Elevation of Privilege Vulnerability | Important |
| CVE-2026-35420 | Windows Kernel Elevation of Privilege Vulnerability | Important |
| CVE-2026-34332 | Windows Kernel-Mode Driver Remote Code Execution Vulnerability | Important |
| CVE-2026-40408 | Windows WAN ARP Driver Elevation of Privilege Vulnerability | Important |
| CVE-2026-34339 | Windows Lightweight Directory Access Protocol (LDAP) Denial of Service Vulnerability | Important |
| CVE-2026-34341 | Windows Link-Layer Discovery Protocol (LLDP) Elevation of Privilege Vulnerability | Important |
| CVE-2026-34329 | Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability | Important |
| CVE-2026-33838 | Windows Message Queuing (MSMQ) Elevation of Privilege Vulnerability | Important |
| CVE-2026-32161 | Windows Native WiFi Miniport Driver Remote Code Execution Vulnerability | Critical |
| CVE-2026-41089 | Windows Netlogon Remote Code Execution Vulnerability | Critical |
| CVE-2026-34342 | Windows Print Spooler Elevation of Privilege Vulnerability | Important |
| CVE-2026-34340 | Windows Projected File System Elevation of Privilege Vulnerability | Important |
| CVE-2026-40398 | Windows Remote Desktop Services Elevation of Privilege Vulnerability | Important |
| CVE-2026-21530 | Windows Rich Text Edit Elevation of Privilege Vulnerability | Important |
| CVE-2026-32170 | Windows Rich Text Edit Elevation of Privilege Vulnerability | Important |
| CVE-2026-41097 | Secure Boot Security Feature Bypass Vulnerability | Important |
| CVE-2026-40410 | Windows SMB Client Elevation of Privilege Vulnerability | Important |
| CVE-2026-35415 | Windows Storage Spaces Controller Elevation of Privilege Vulnerability | Important |
| CVE-2026-34350 | Windows Storport Miniport Driver Denial of Service Vulnerability | Important |
| CVE-2026-34351 | Windows TCP/IP Elevation of Privilege Vulnerability | Important |
| CVE-2026-33837 | Windows TCP/IP Local Elevation of Privilege Vulnerability | Important |
| CVE-2026-40406 | Windows TCP/IP Information Disclosure Vulnerability | Important |
| CVE-2026-40414 | Windows TCP/IP Denial of Service Vulnerability | Important |
| CVE-2026-34334 | Windows TCP/IP Elevation of Privilege Vulnerability | Important |
| CVE-2026-40399 | Windows TCP/IP Elevation of Privilege Vulnerability | Important |
| CVE-2026-35422 | Windows TCP/IP Driver Security Feature Bypass Vulnerability | Important |
| CVE-2026-40413 | Windows TCP/IP Denial of Service Vulnerability | Important |
| CVE-2026-40415 | Windows TCP/IP Remote Code Execution Vulnerability | Important |
| CVE-2026-40401 | Windows TCP/IP Denial of Service Vulnerability | Important |
| CVE-2026-40405 | Windows TCP/IP Denial of Service Vulnerability | Important |
| CVE-2026-40382 | Windows Telephony Service Elevation of Privilege Vulnerability | Important |
| CVE-2026-34338 | Windows Telephony Service Elevation of Privilege Vulnerability | Important |
| CVE-2026-42825 | Windows Telephony Service Elevation of Privilege Vulnerability | Important |
| CVE-2026-40380 | Windows Volume Manager Extension Driver Remote Code Execution Vulnerability | Important |
| CVE-2026-33839 | Win32k Elevation of Privilege Vulnerability | Important |
| CVE-2026-40403 | Windows Graphics Component Remote Code Execution Vulnerability | Critical |
| CVE-2026-34347 | Windows Win32k Elevation of Privilege Vulnerability | Important |
| CVE-2026-34333 | Windows Win32k Elevation of Privilege Vulnerability | Important |
| CVE-2026-34330 | Win32k Elevation of Privilege Vulnerability | Important |
| CVE-2026-34331 | Win32k Elevation of Privilege Vulnerability | Important |
| CVE-2026-35417 | Windows Win32k Elevation of Privilege Vulnerability | Important |
| CVE-2026-33840 | Win32k Elevation of Privilege Vulnerability | Important |
Windows Native WiFi Miniport Driver Remote Code Execution Vulnerability
CVE-2026-32161 is a Critical Remote Code Execution vulnerability affecting the Windows Native WiFi Miniport Driver. Microsoft released the security update on May 12, 2026, as part of Patch Tuesday. This vulnerability could allow an attacker to execute malicious code on a vulnerable system through specially crafted wireless network interactions.
Critical Windows Netlogon Remote Code Execution Vulnerability CVE-2026-41089
Microsoft has released a security update for CVE-2026-41089, a Critical Remote Code Execution vulnerability affecting Windows Netlogon. The vulnerability was disclosed as part of the May 2026 Patch Tuesday updates and carries a high CVSS score of 9.8.
Need Further Assistance or Have Technical Questions?
Join the LinkedIn Page and Telegram group to get the latest step-by-step guides and news updates. Join our Meetup Page to participate in User group meetings. Also, join the WhatsApp Community and the Whatsapp channel to get the latest news on Microsoft Technologies. We are there on Reddit as well
Author
Anoop C Nair has been Microsoft MVP for 10 consecutive years from 2015 onwards. He is a Workplace Solution Architect with more than 22+ years of experience in Workplace technologies. He is a Blogger, Speaker, and Local User Group Community leader. His primary focus is on Device Management technologies like SCCM and Intune. He writes about technologies like Intune, SCCM, Windows, Cloud PC, Windows, Entra, Microsoft Security, Career, etc.


