Let’s discuss AVD Auto Feed Registration Intune Policy Setup and Default Connection URL Options. I have already shared a manual way of subscribing to AVD feeds. You can read Azure Virtual Desktop RD Client Subscription Options For AVD.
Microsoft recently announced AVD auto registration policies for the insider version of RD client using Microsoft Endpoint Management (MEM) Intune policies. However, while writing this post, I couldn’t find more detailed documentation from Microsoft.
AVD ARM-based solution uses the following URL Auto Feed Registration for a subscription. This information is https://rdweb.wvd.microsoft.com/api/arm/feeddiscovery (for AVD). This is required in a particular scenario where your subscribe option is working.
You can learn MEM Intune from the following video series – 63 Episodes of Free Intune Training for Device Management Admins.
Table of Contents
AVD Auto Feed Registration Intune Policy Setup
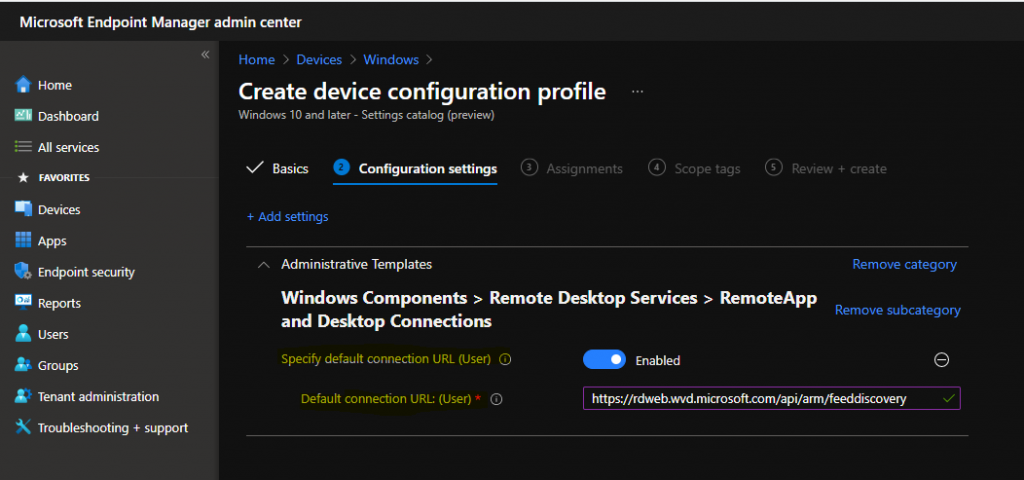
Now, it’s time to look into the actual Intune policy configuration for AVD Auto Feed Registration Intune Policy Setup and the Default Connection URL (user) policy.
NOTE! – I assumed you already have appropriate access rights to Endpoint Manager (Intune). Otherwise, you won’t be able to complete the following activity.
- Login to the Endpoint Manager Intune portal https://endpoint.microsoft.com/#home
- Try to navigate through Devices -> Windows -> Configuration profiles.
- Click on +Create Profile.
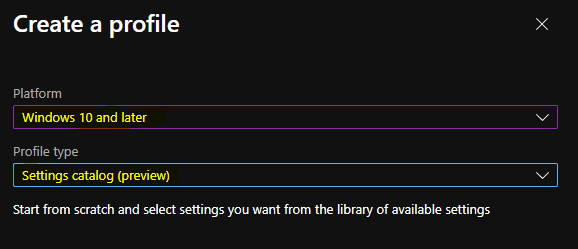
- Select Windows 10 and Later as platforms.
- Select Settings Catalog from Profile Type.
- Click on the Create button.
- Enhanced Reporting Multi-Administrative Approval Microsoft Home Page via Intune August 2024 Update
- Enable or Disable the Built-in Administrator Account in Windows using Intune Policy
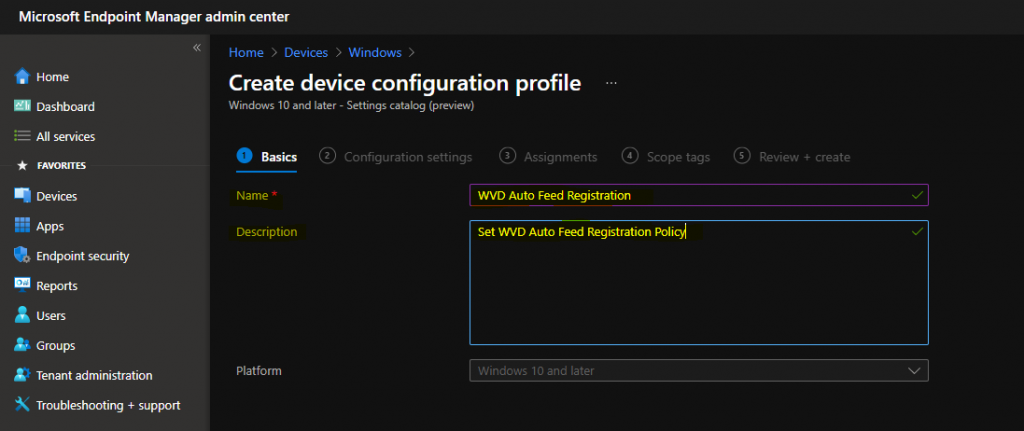
Enter the name of the policy, which is AVD Auto Feed Registration.
- Enter the Description – Set AVD Auto Feed Registration Policy.
- Click on the Next button.
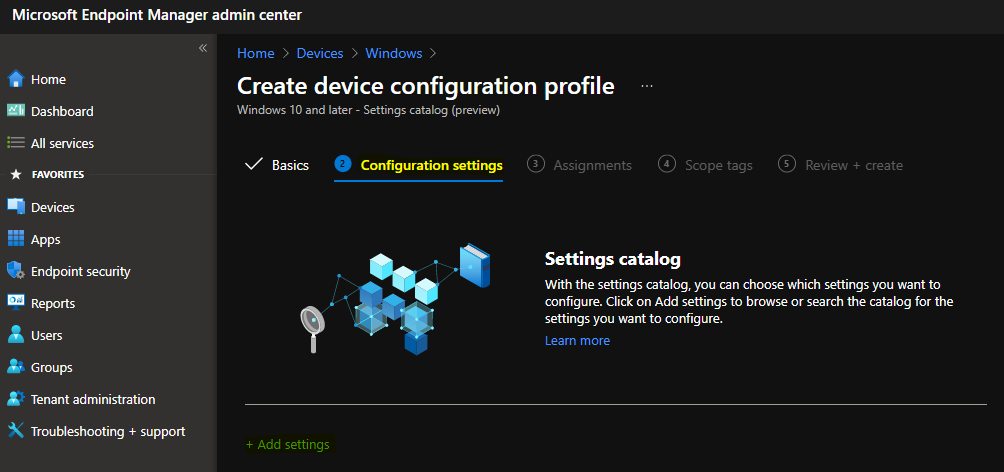
NOTE! – Settings catalog – You can choose which settings to configure in the settings catalog. Click on Add settings to browse or search the catalog for the settings you want to configure.
Click on the +Settings button to continue.
Enter “remote desktop” in the search field and click on the search button.
Click on RemoteApp and Desktop Connections from Browser by category.
Select the Specify default connection URL (user) option from the Setting name.
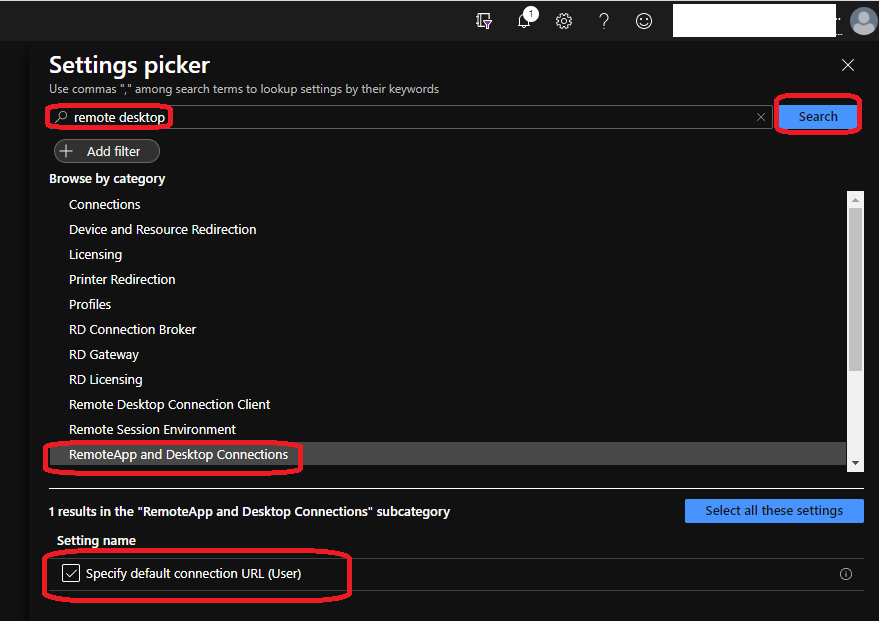
This policy comes from the Windows Components > Remote Desktop Services > RemoteApp and Desktop Connections administrative template.
Specify default connection URL (user) – Click the toggle button to Enable the policy.
You need to AVD RDS feed in the option – specify the Default Connection URL: (User).
NOTE! These text details are coming from previous group policy settings, so I don’t think this is very accurate in terms of AVD. This policy setting specifies the default connection URL for RemoteApp and Desktop Connections.
The default connection URL is a specific connection that can only be configured by using Group Policy. In addition to the capabilities standard to all connections, the default connection URL allows document file types to be associated with RemoteApp programs.
NOTE! – RemoteApp programs installed through RemoteApp and Desktop Connections from an untrusted server can compromise the security of a user’s account. This setting is only available to Windows Insiders.
- Default Connection URL (Users) ->
https://rdweb.wvd.microsoft.com/api/arm/feeddiscovery
Assignment of AVD Intune Policy for Auto Feed Subscription
In this phase, you must decide which set of users or devices this policy should go to. I think deploying this policy to the user’s group is better because it is a user-based policy.
Click on +Add groups and select the Azure AD user Group to deploy the Intune policy for the AVD feed auto subscription. In this example, I have added TestUserGroup, as shown in the screenshot below.
You can proceed further by clicking Next and Next (scope page).
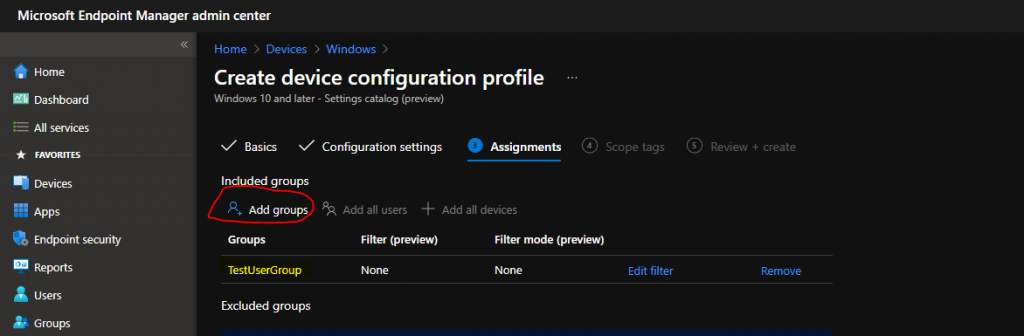
Click on Review + Create to complete the creation and assignment process of the AVD Auto Feed Registration Intune Policy.
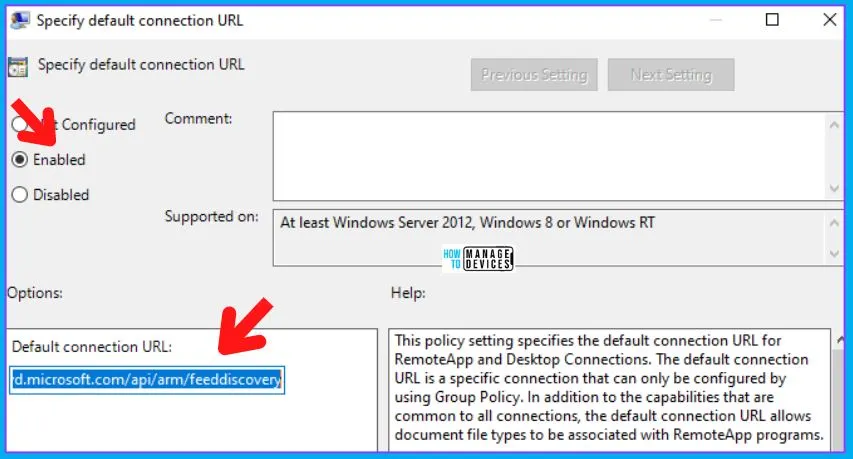
AD Group Policy Details for AVD Auto Subscription
You can also use the AD Group Policy for AVD Auto Subscription. The following is the AD group policy you must use for this. If you disable or do not configure this policy setting, the user will not have a default connection URL.
The Group Policy path that you want to look for is -> User Configuration -> Administrative Templates -> Windows Components -> Remote Desktop Services -> RemoteApp and Desktop Connectons.
This policy setting specifies the default connection URL for RemoteApp and Desktop Connections. The default URL is a specific connection that can only be configured using Group Policy. In addition to the capabilities common to all connections, the default connection URL allows document file types to be associated with RemoteApp programs.
The default connection URL must be configured in the form of Users -> https://rdweb.wvd.microsoft.com/api/arm/feeddiscovery
If you enable this policy setting, the specified URL is configured as the default connection URL for the user and replaces any existing connection URL. The user cannot change the default connection URL. The user’s default login credentials are used when setting up the default connection URL.
RemoteApp programs that are installed through RemoteApp and Desktop Connections from an untrusted server can compromise the security of a user’s account.
Client Side
I have not tested the client-side scenario. Are this scenario and policy supported for any existing RD client versions? If you have tested this, let me know in the comments.
With the auto-subscription option, users don’t have to add a feed. Instead, they might need to add the required details when enabling MFA.
Troubleshooting Options
The following posts might help you troubleshoot issues related to the Intune Settings catalog (and, in general, Intune troubleshooting).
- How to Start Troubleshooting Intune Issues
- Windows 10 MDM Log Checklist
- MDM Diagnostics Tool – Tips & Tricks
- Learn How to Collect Windows 10 Diagnostics Information from Intune Portal | Endpoint Manager
We are on WhatsApp. To get the latest step-by-step guides and news updates, Join our Channel. Click here –HTMD WhatsApp.
Author
Anoop C Nair has been Microsoft MVP for 10 consecutive years from 2015 onwards. He is a Workplace Solution Architect with more than 22+ years of experience in Workplace technologies. He is a Blogger, Speaker, and Local User Group Community leader. His primary focus is on Device Management technologies like SCCM and Intune. He writes about technologies like Intune, SCCM, Windows, Cloud PC, Windows, Entra, Microsoft Security, Career, etc.



Hello
Does it mean there is no need to add _msradc DNS record anymore following https://docs.microsoft.com/en-us/windows-server/remote/remote-desktop-services/rds-email-discovery
?
Thanks
Hello – I have seen this working (the manual way) without any DNS changes for an enterprise. But you need to use two-factor authentication if you have enabled the same. I think the referenced document is basically for RD Server components?
Adding _Msradc record gives u the possbility to have your assigned wvd resources (desktops & apps) when using your corp mail for authentication on windows remote desktop client. So i am curious if it is still needed for the scenarios described in your article
Unfortunately, I have not tested all the scenarios with this policy as I updated them in the client-side section. I will wait for the supported version of RD client to test this. But I don’t think you have to go through any of these DNS changes .. it might work directly. I think Ryan tested this option with Group policy https://ryanmangansitblog.com/2019/11/14/windows-virtual-desktop-configuring-the-rdp-feed/
Helo
What about adding _msradc record to DNS? That is still required?