Let’s check out the SCCM Tenant Attach Step-by-Step Guide. In Configuration Manager, production version 2002, Microsoft introduced a new feature called “Tenant attach.” With this feature, you can synchronize ConfigMgr agents to Intune without enrolling in Intune.
Once synchronized, the ConfigMgr device will be visible in the Microsoft Endpoint Manager Admin Center portal. You can perform remote actions for SCCM clients from the Intune portal. The SCCM tenant attach is helpful for helpdesk and single-pane-of-glass scenarios.
The key point is that the ConfigMgr client is in the Intune console without enrolling in Intune. This means your ConfigMgr-managed device does not need to be co-managed to avail of some Cloud benefits.
The blog post Tenant Attach Background Process Walkthrough via Logs provides more details on tenant attach troubleshooting.
- SCCM 2002 Installation Step By Step Guide | MEMCM | ConfigMgr
- PowerShell Script To Enable Opt-In Version Of SCCM 2002 Early Update Ring
What is SCCM Tenant Attach Vs Co-Management
What is SCCM Cloud Attach Tenant Attach Client Attach Vs. Co-Management? I hope you have already heard about SCCM Cloud Attach (wait, MECM Cloud Attach) many times before.
Let me tell you, Cloud Attachment is a bit different now! All the details are taken from Jason Githens and Rob York’s session at MS Ignite 2019. More information about the Ignite session is below.
Co-management is the bridge between traditional management and modern management. Microsoft renamed the co-management node in the SCCM admin console to Cloud Attach.
Windows 10 or Windows 11 co-management is dual management (with SCCM and Intune) capability available with Windows 10 1709 version (Fall Creators Update) and later.
- Co-managed device = SCCM agent + Intune enrolled
- Tenant attach device = SCCM agent synced to MEM (Not Intune enrolled)
Related Post
- Tenant Attach Guide for SCCM Logs Data Flow Troubleshooting Intune
- SCCM Tenant Attach Troubleshooting Issues via Logs | ConfigMgr
- Fix ConfigMgr Tenant Attach Error 401 403 | Missing Config| SCCM
SCCM Tenant Attach Step-by-Step Guide
Yes, you are correct! SCCM cloud attachment is not new here. Microsoft mentioned the SCCM cloud-attached features in the last MS Ignite. The following was Microsoft’s offering.
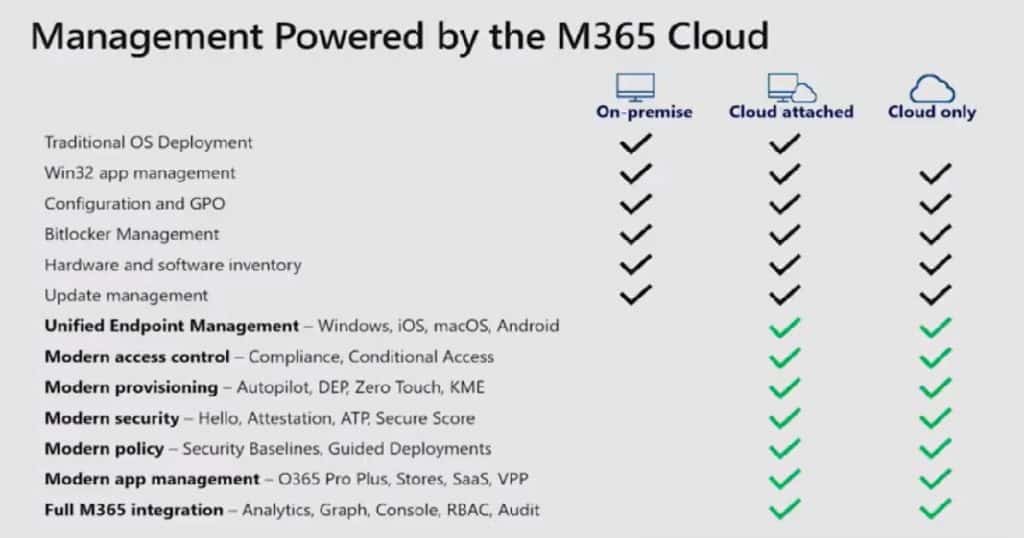
Microsoft did a great job of evolving to the new vision of cloud attach with the following options. With the Microsoft Endpoint Manager announcement, Microsoft is trying to help organizations reduce the friction in Modern Management strategies.
- Cloud console
- Tenant attach
- Client attach
- Single pane of glass
User Experience Analytics
As per Jason, user experience analytics has the following components: You can listen to the recorded video of this session to learn more about these topics.
- Startup Performance
- Remediation Scripting
- Recommended Software
- Experience Score
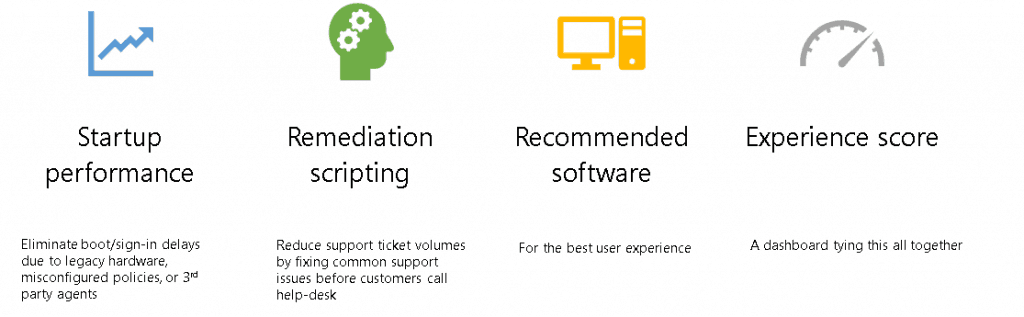
As Jason explained in the presentation, I hope these new options will help customers achieve their organizational goals.
- Employee Experience
- Employee Retention
- Attracting New Talent
- Change Control Dashboard (Change Control with User Experience in a data-driven way)
What is User Experience Analytics?
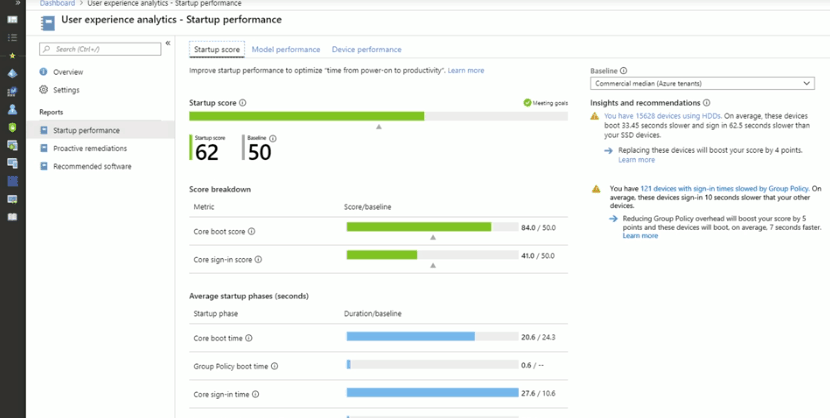
What is SCCM Cloud Attach Tenant Attach Client Attach Vs Co-Management?
As per Rob (check out the recorded session below), the cloud attachment is an option for leveraging the combined power of Microsoft Endpoint Manager by connecting SCCM to Intune.
Cloud Attach
Cloud Attach has two parts, which are very well explained in the slide deck below. More details are in the sub-sections below.
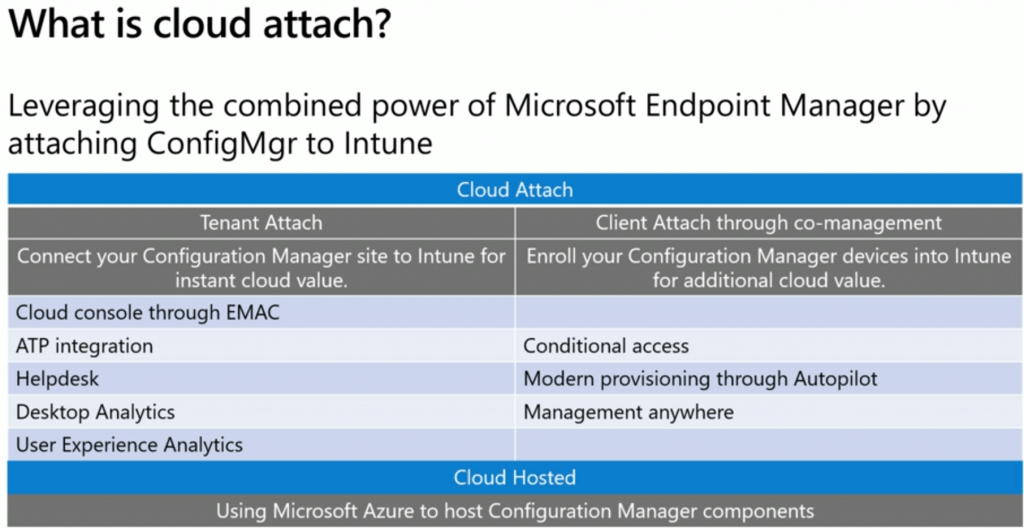
Leveraging the combined power of Microsoft Endpoint Manager by attaching ConfigMgr to Intune
| Tenant Attach (Connect your SCCM site to Microsoft Intune for instant cloud value) | Client Attach through co-management (Enroll your ConfigMgr devices into Intune for additional cloud value) |
|---|---|
| Cloud console through EMAC | Conditional access |
| ATP integration | Modern provisioning through Autopilot |
| Desktop Analytics | Management anywhere |
| User experience analytics |
Tenant Attach
Tenant Attach – Connect your SCCM site to Microsoft Intune for instant cloud console and troubleshooting power. The “tenant attach” is an on-demand connected architecture. No, Microsoft is not replicating the entire SCCM DB to Intune!!
The tenant architecture is an on-demand connection when you click on an item in the Microsoft Endpoint Manager portal. This information will also improve the experience of help desk teams.
The following are the features you will be able to enable with the SCCM tenant attached:
- Cloud Console through Microsoft Endpoint Admin Console (EMAC)
- ATP Integration
- Helpdesk
- Desktop Analytics
- User Experience Analytics
- Web front-end CMPivot
Client Attach through Co-Management
SCCM Client attach is nothing but co-management. We have many guides about SCCM co-management. I would recommend going through the latest one, “SCCM CMG Schema Workflow Scenarios.”
Client Attach Features
- Conditional Access
- Modern Provisioning through Autopilot
- Management from Anywhere
How to Attach SCCM to Cloud Tenant?
As per Rob, this tenant attaches option will be coming to future SCCM versions. I shall presume in the 2002 version of SCCM or later!
How do you prepare for the SCCM cloud attach? Start preparing for co-management options.
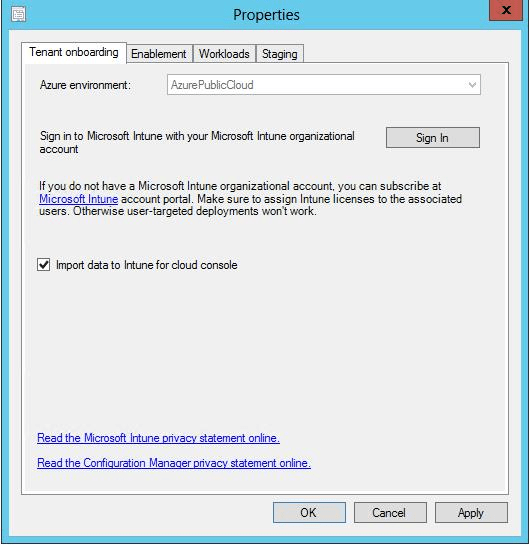
- Enable the option “Import data to Intune for cloud console”
Co-Managed Device and Tenant Attach Device
Both tenants attached and co-managed devices will be visible in a single MEMAC console, but they are not the same.
- Co-managed device = SCCM agent + Intune enrolled
- Tenant attach device = SCCM agent synced to MEM (Not Intune enrolled)
The co-managed device has many more options available in the Microsoft Endpoint Manager Admin Center (MEMAC). However, we can expect many more features for tenant-attached devices in the MEMAC console in the future. Below are some of the cloud benefits ConfigMgr tenants provide:
- Single Microsoft Endpoint Admin Console (MEMAC) to manage ConfigMgr and intune devices.
- ATP Integration
- Helpdesk troubleshooting
- User Experience Analytics
- Web front-end CMPivot
Note: The above-listed benefits announced in Inspire 2019 are not yet available to the public. Only limited features are available at the time of writing. We will discuss some of the features currently available.
Prerequisites
More updated details about prerequisites are given in Microsoft docs.
- Appropriate access to SCCM infra (Full Admin preferably)
- Recommended to perform this activity from the Tier 1 server in ConfigMgr Hierarchy (CAS) or a standalone primary server
- Global Administrator account for signing in to the Tenant onboarding page (configuration in SCCM).
- An Azure public cloud environment.
- The user account triggering device actions has the following prerequisites after the 2103 version of SCCM:
- Discovered with Azure Active Directory user discovery
- Or Discovered with Active Directory user discovery
- The Notify Resource permission is under the Collections object class in Configuration Manager.
- On-Prem user synchronized to Azure using AADconnect
- SCCM server should have access to the below Internet endpoints
- https://aka.ms/configmgrgateway
- https://gateway.configmgr.manage.microsoft.com
- https://us.gateway.configmgr.manage.microsoft.com
- https://eu.gateway.configmgr.manage.microsoft.com
NOTE! – Permissions for Tenant attached is updated. You don’t need to give permissions to Configuration Manager Microservice https://docs.microsoft.com/en-us/mem/configmgr/tenant-attach/client-details#permissions
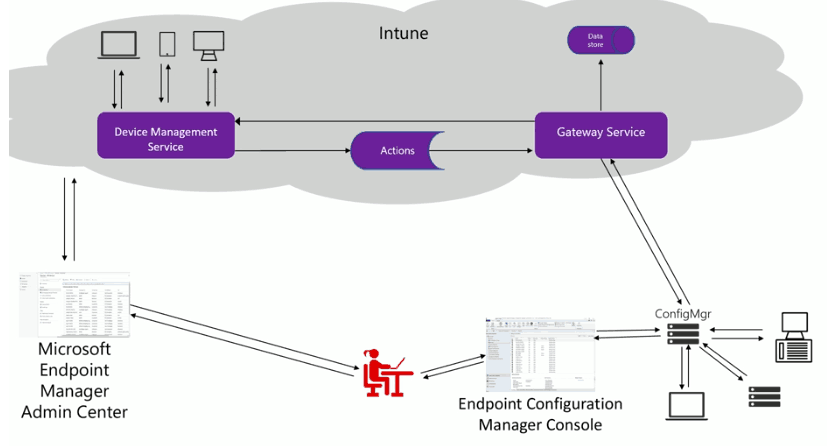
SCCM Tenant attach high-level Architecture
There are three components in Tenant Attachment Architecture.
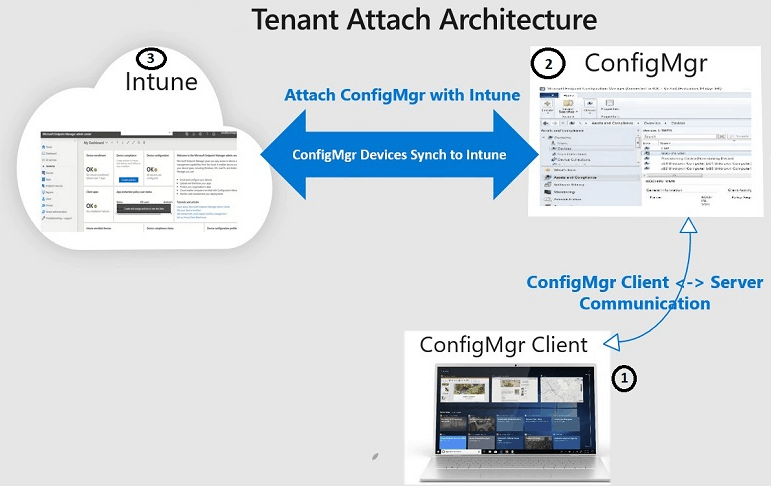
- ConfigMgr agent:
- The ConfigMgr client communicates with the ConfigMgr server as normal.
- There is no change. In addition, there is no need to enrol in Intune.
- ConfigMgr server:
- ConfigMgr synchronizes devices to the Microsoft Endpoint Manager Admin Center (MEMAC).
- ConfigMgr server receives instructions from the Microsoft Endpoint Manager Admin Center (MEMAC) and forwards the instructions to ConfigMgr clients.
- The ConfigMgr server plays a middleman between the Intune and ConfigMgr client.
- Intune:
- MEMAC console shows the SCCM Devices synchronized from the SCCM server to Intune.
This architecture will not synchronise the entire ConfigMgr database to Intune. It is an on-demand architecture. The MEMAC console connects to SCCM only when required or when the admin initiates action.
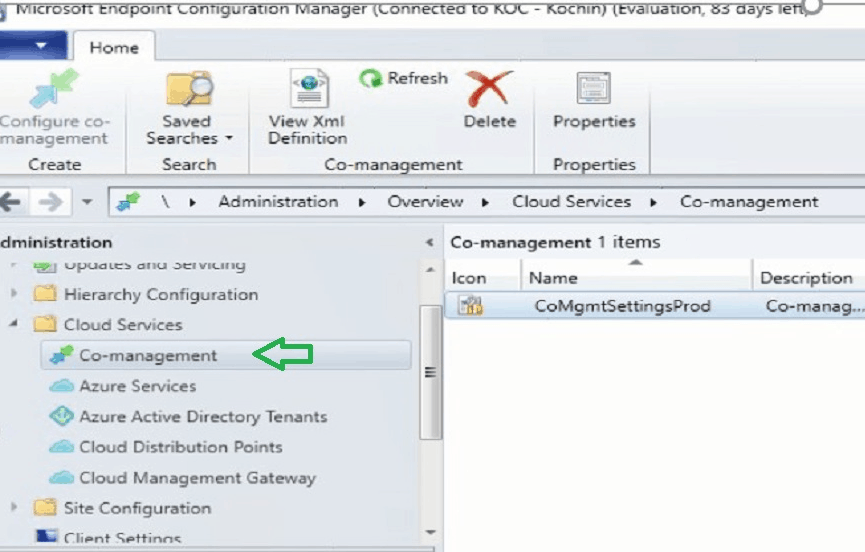
How to configure SCCM Tenant Attach?
The configuration required for the tenant is attached to the co-management wizard. If you have not enabled the co-management wizard, follow the steps mentioned here.
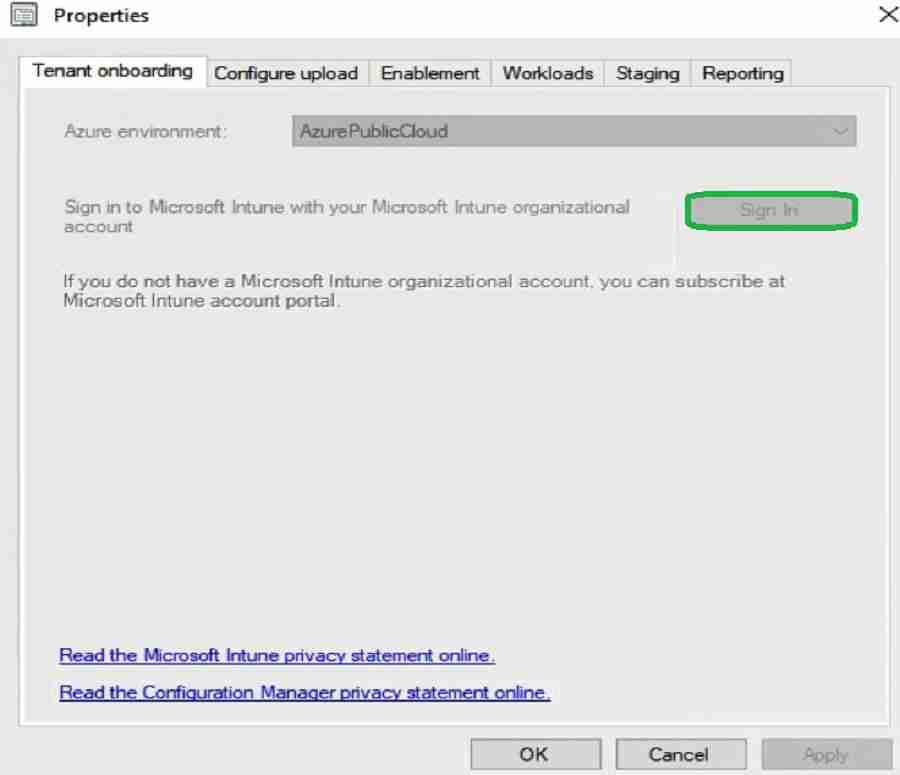
Go to Administration > Overview > Cloud Services > Co-management in the Configuration Manager Admin console.
Ensure your Azure environment is AzurePublicCloud. The tenant is boarded to Azure by signing in using your Global Administrator account.
Ensure you select the option “upload to MEM admin center.”
Please make sure you select a collection for which you want devices to synchronize. It’s recommended that you start with a test device collection. Also, ensure you exclude the servers managed by ConfigMgr.
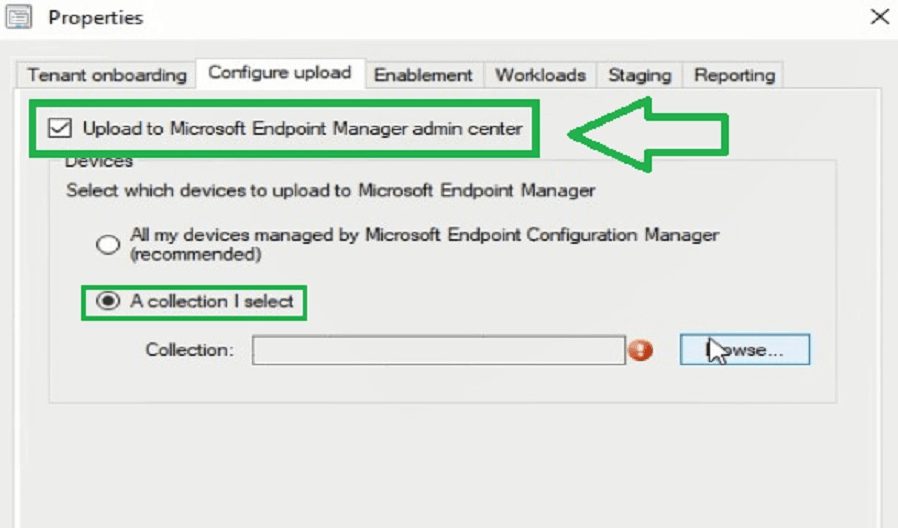
Tenant attach sync setting has nothing to do with co-management. However, tenant attaches settings are available within the co-management wizard.
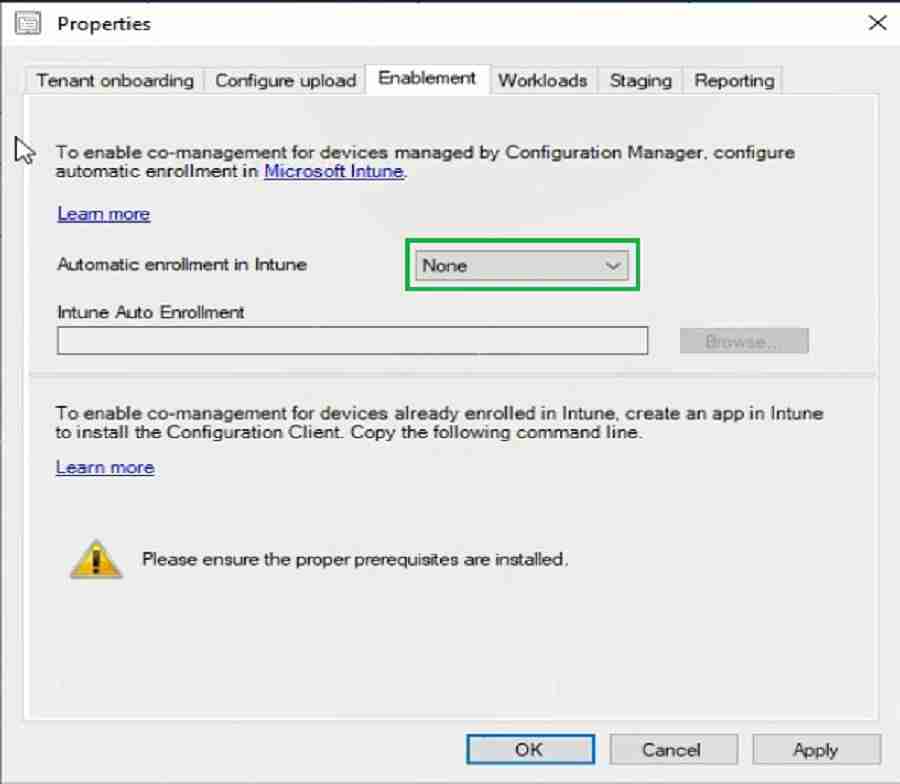
Note: Since my scenario does not have any co-managed devices, I configured it as none for Intune enrollment. It would help if you decided on the configuration based on your scenario.
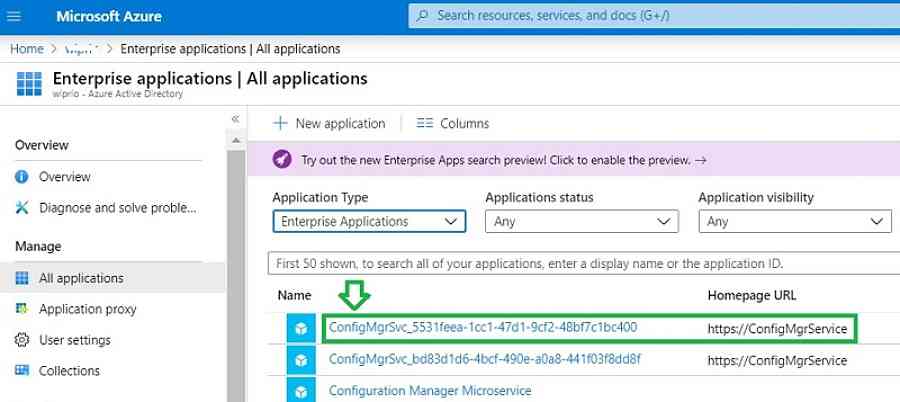
The Azure AD application below is created automatically after configuring ConfigMgr. Troubleshooting events are in the SmsAdminUI.log log.
You can see the application name starts with “ConfigMgrSVC_… “
The ConfigMgr server communicates with the cloud using this Azure AD Web application.
We completed the configuration. Let us discuss how the ConfigMgr server connects to Intune and uploads the devices.
NOTE! – Let’s add your admin user to this (Configuration Manager Microservice) enterprise app to get appropriate permissions to initiate SCCM actions from the Intune portal.
- CMPivot
- Run Script
- Collections
- etc.
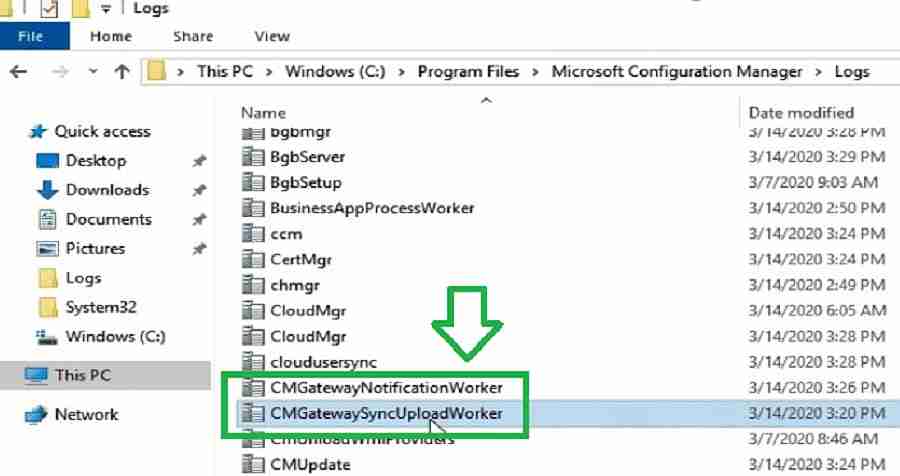
Log Files – Troubleshooting
Let’s see how log files can help troubleshoot the issue with device sync and tenant attach.
ConfigMgr Device Upload to Intune Workflow
GatewaySyncUploadWorker.log :
This log tracks the connectivity between ConfigMgr and Intune. You can use this log to troubleshoot if ConfigMgr devices do not upload to the MEMAC console.
- ConfigMgr server selects the gateway to upload the device based on the location.
- For the US the gateway URL is https://us.gateway.configmgr.manage.microsoft.com
- For Europe gateway URL is https://eu.gateway.configmgr.manage.microsoft.com
- Next, the ConfigMgr server will authenticate and establish the connection.
- Once succeeded, the ConfigMgr agent uploads to Intune through the gateway.
- You can see the ConfigMgr client records uploaded in batch
If you enable verbose logging, a log will tell the bytes written to the network for upload. Based on my testing, this network traffic is less. Moreover, the follow-up device synch will be delta only.
- The default upload sync interval is 15 min (delta)
- Response code 200 states the connection between ConfigMgr and Intune is successful
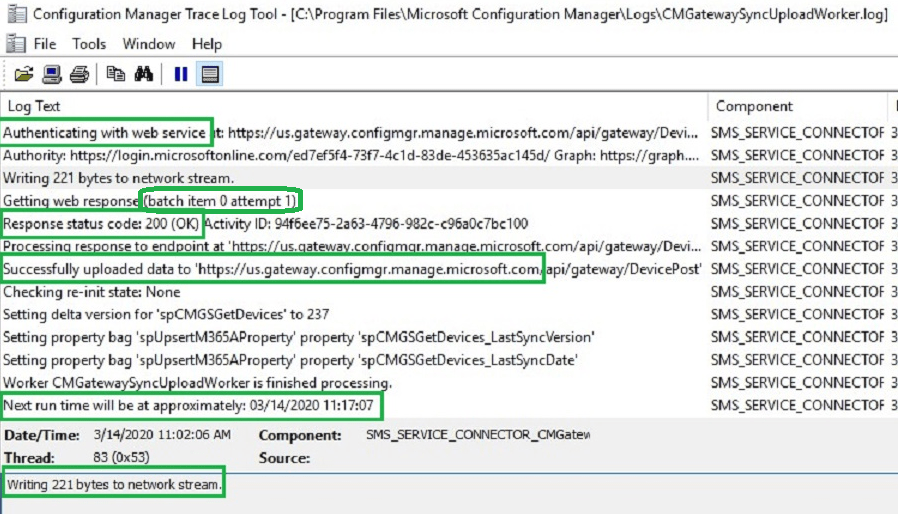
After successfully upload, You can see your ConfigMgr client in the Microsoft endpoint manager admin center console.
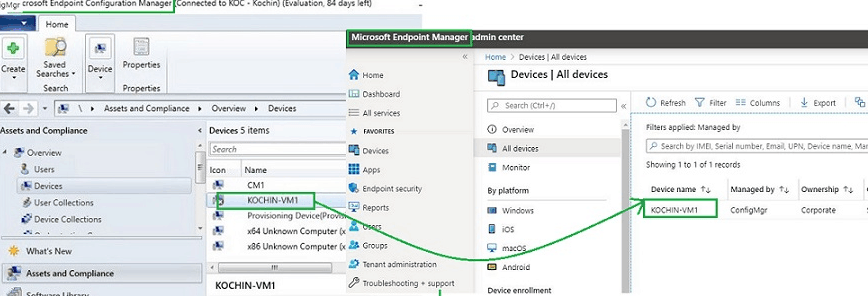
Until now, we discussed the device upload events from ConfigMgr to Intune. Next, let us discuss the workflow from the MEM admin console to ConfigMgr.
Intune to SCCM event workflow
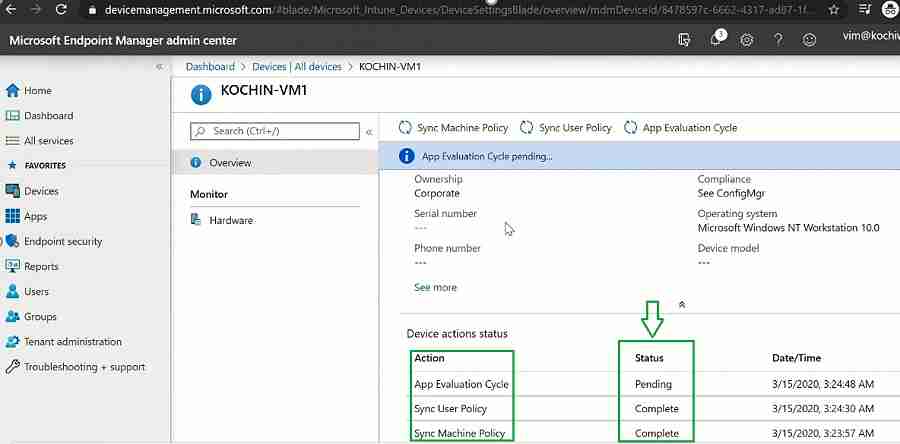
At the time of writing this post, only limited features are available in the MEM admin console for ConfigMgr clients, as listed below
- Machine policy synch
- User policy synch
- Application evaluation
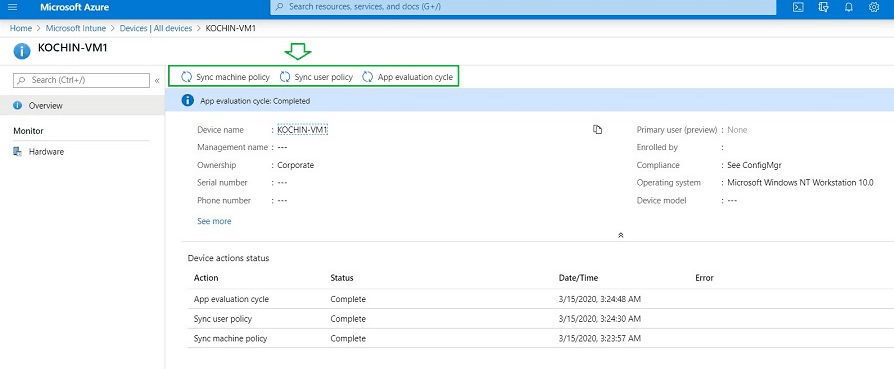
Let us see what happens when I trigger a machine policy from the MEM admin console. Below are the high-level activities
- MEM admin console sent instructions for triggering machine policy to the ConfigMgr server
- ConfigMgr server receives notification from MEM gateway and authenticates
- Forwards as BGB instruction and process
- ConfigMgr server sent the notification to the ConfigMgr client
- The ConfigMgr client receives the instruction from the ConfigMgr server and process
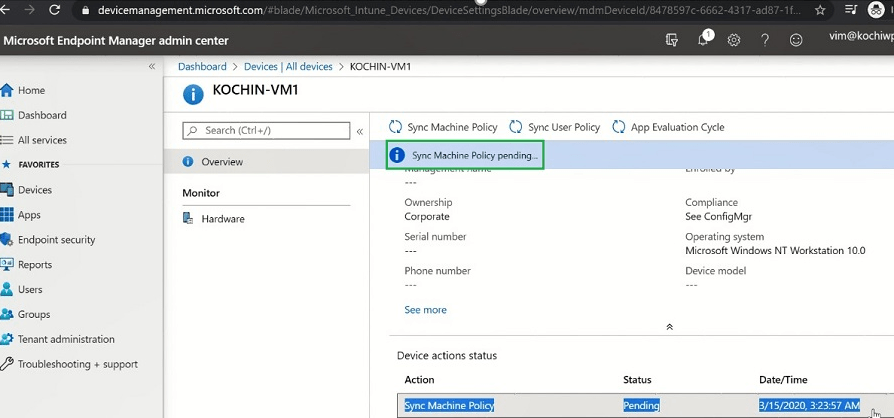
MEM admin console sent the machine policy instruction to the ConfigMgr server. Initially, you can see the status will show pending.
cmgatewaynotificationworker.log :
This log tracks the events from Intune to ConfigMgr. You can refer to this log while troubleshooting communication between Intune and ConfigMgr.
ConfigMgr server receives the notification and authenticates the user who initiated the policy from the MEM console.
The ConfigMgr BGB remote task will be processed further if user authentication is successful.
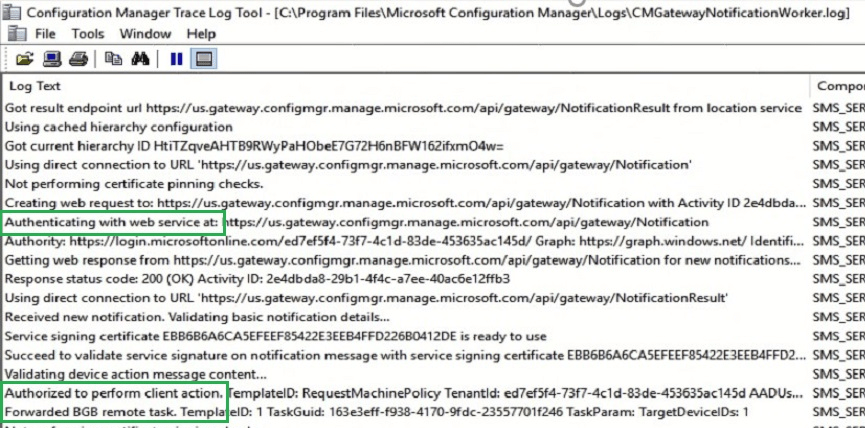
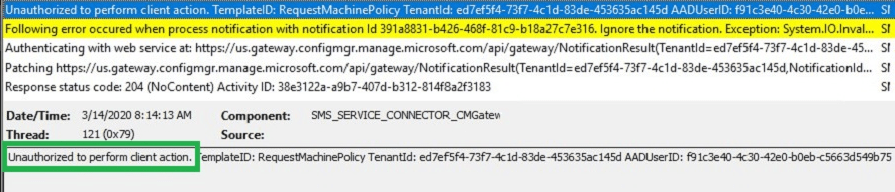
You may get the error below if the user does not have the necessary ConfigMgr permission, as mentioned in the pre-req. Also, we see the error below if the user is not an on-prem user ID and is not synchronized to Azure.
Unauthorized to perform client action. TemplateID: RequestMachinePolicy TenantId: ed7ef5f4-73f7-4c1d-83de-453635ac145d AADUserID: f91c3e40-4c30-42e0-b0eb-c5663d549b75.
ConfigMgr processes the BGB notification service. Then, send the notification to the ConfigMgr client.
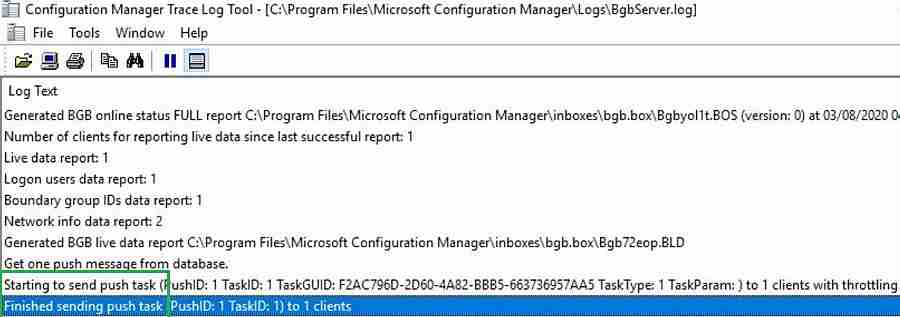
You can also track the ConfigMgr client Machine policy status, which you initiated from the MEM console. The different statuses are Completely pending or failed, as shown below.
For this post, I used the MEM admin portal on my mobile phone to manage the SCCM agent. However, we could also manage my SCCM agent from a mobile web browser, which is a great step.
Resources
We are on WhatsApp. To get the latest step-by-step guides and news updates, Join our Channel. Click here –HTMD WhatsApp.
Author
Vimal Das has over 10 years of experience in SCCM device management solutions. His main focus is on Device Management technologies like Microsoft Intune, ConfigMgr (SCCM), OS Deployment, and Patch Management. He writes about SCCM, Windows 10, Microsoft Intune, and MDT.


