Fix Kerberos error 0x80090342 SCCM Endpoint Protection Policy Deployment Issues. Let’s find out how to fix the Antimalware Exception Folder Exclusion policy issue Kerberos error 0x80090342 with the SCCM Endpoint Protection rule.
I was working on a request to exclude a few folders from SCEP (System Center Endpoint Protection) Anti Virus scanning. We already had a default policy for all servers, but since this was a custom exclusion from scanning in antimalware policies, I had to create a new policy to achieve this task.
Let’s see what is the exact issue here and fix the issue. I created a new policy to exclude those folders in D drive and deployed it using SCCM. The SCEP and SCCM agents in the server were healthy, but the policy deployed was not reaching the client for some reason.
This post will see how to fix the Antimalware Exception Folder Exclusion Issue Kerberos error 0x80090342. When it comes to SCEP, then there are very few resources available. I have listed down some of the articles for your reference.
There is not much information on google, too, apart from the generic MS article https://docs.microsoft.com/en-us/mem/configmgr/protect/deploy-use/troubleshoot-endpoint-client and the one from Henrik Hoe https://blog.ctglobalservices.com/configuration-manager-sccm/heh/configuration-items-and-baselines-example-scep-client-compliance/.
The third one was written by me and published by Anoop somewhere in May 2021. But that is also covering only client-side troubleshooting. https://www.anoopcnair.com/fix-sccm-scep-related-issues-client-side-configmgr-defender/
So I thought of taking this issue as an example and trying to put as much as possible, which will be helpful from a server-end troubleshooting perspective. We need to Fix Kerberos error 0x80090342 SCCM Endpoint Protection Policy Deployment Issues.
Since we are talking about server-end tools and policy-related stuff, the first one I picked was CLIENTSPY.exe. I didn’t have to put much effort because Anoop briefly explains it in this post – https://www.anoopcnair.com/how-to-use-sccm-configmgr-tool-policy-spy-exe/.
Now what? The key troubleshooter mantra for SCCM. The LOGS are important, and one must read them to figure out what’s happening.
That’s where our experts come into the picture. Anoop Nair has described everything we need to know about logs, and if you notice, the blog is getting updated very frequently (If any addition in the logging mechanism of SCCM) https://www.anoopcnair.com/sccm-logs-files-list-of-configmgr-log-files/.
Collect SCEP support logs:
Let’s check how to collect support logs from Endpoint Protection. You can use the MpCmdRun command to gather all support logs at one location.
- Go to “C:\Program Files\Microsoft Security Client\Antimalware” or “C:\Program Files\Windows Defender” depending on Operating System.
- Run the following command
MpCmdRun.exe -getfiles
You can find all logs files in “C:\ProgramData\Microsoft\Antimalware\Support” or “C:\ProgramData\Windows Defender\Support” folder.
NOTE! – We didn’t find any error at the client end logs, and the policy was updated successfully, so we moved to check the issue from a core OS perspective. Even we didn’t find the issue was because of Kerberos error 0x80090342.
Core OS Related Checks
Let’s perform more troubleshooting to fix the Antimalware Exception Folder Exclusion Issue with SCCM Endpoint Protection. Once it comes to OS, we check the group policy application successfully. The second is WUA (Windows Update Agent).
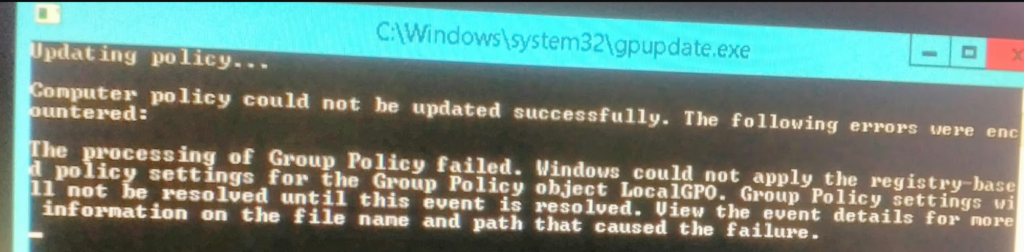
So gpupdate/force command errored out with the below message:
Computer policy could not be updated successfully. The following errors were encountered. The processing of Group Policy failed. Windows could not apply the registry-based policy settings for the Group Policy object LocalGPO.
Group Policy Settings will not be resolved until this event is resolved. View the event details for more information on the file name and path that caused the failure.
Fix Software Update issue by Renaming REGPOL
I have seen this before, and I know that renaming REGPOL will fix the issue. However, this issue was slightly different, so we might need to dig deeper.
Something similar to the SCAN Issue I covered in my earlier blog https://www.anoopcnair.com/fix-sccm-scan-failed-to-add-update-source-for-wuagent-configmgr/
Troubleshooting Method – Enable GPSvcDebugLevel to debug mode
But it didn’t fix the issue, so we started to look further. As I was expecting, there was no issue from the SCCM end. Computer policy fails to apply from the core policy handle method on the server.
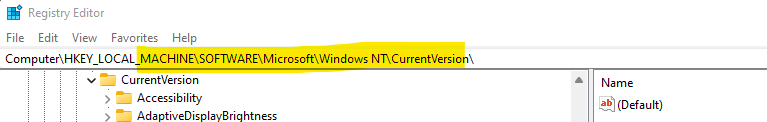
The next step in the troubleshooting to fix the exclusion issue with Endpoint Protection (Kerberos error 0x80090342) is to enable GPSvcDebugLevel to debug login using the registry key as explained below.
We also enabled gpsvc to debug logging by setting this registry key.
Value Path: HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Diagnostics
Value Name: GPSvcDebugLevel
Value Type: REG_DWORD
Value Data: 30002 (hex)
Kerberos Error 0x80090342 with SCCM Endpoint Manager
Now, let’s find out the details of Kerberos error 0x80090342 for exclusion policy with SCCM Endpoint Manager.
You can check the log file after enabling the debug mode from the following location: %windir%\debug\usermode\gpsvc.log
The debug log shows a Kerberos error 0x80090342. Now, we will need to fix the Kerberos error 0x80090342 directly. How to fix Kerberos error 0x80090342 with SCCM Endpoint Manager?
Kerberos error 0x80090342 translates to unknown EType
The machine in question has only Kerberos AES128 and AES256 enabled. The RC4 is disabled for Kerberos.
Fix Kerberos error 0x80090342 with msDS-supportedencryptiontypes Attribute
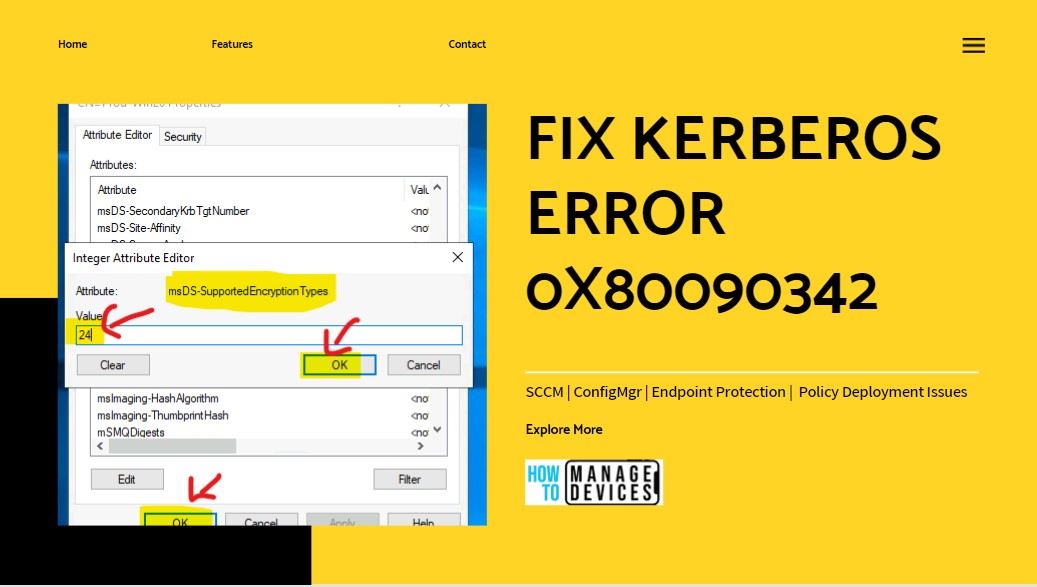
Now, let’s find out the fix for this Kerberos error 0x80090342 with msDS-supportedencryptiontypes Attribute. The computer account in the account directory should have a corresponding attribute named MSDS-supportedencryptiontypes set to decimal 24.
However, the MSDS-supportedencryptiontypes attribute was blank. When it is empty, the DC assumes the machine supports only RC4. Hence it generates a mismatch error and spits out 0x80090342.
We will need to set the MSDS-supportedencryptiontypes attribute value in AD to 24. You can follow the steps explained below to fix the issue. Also, use PowerShell Script to fix the attribute value for many devices.
- Launch ADSIEdit from the RUN many by typing ADSIEdit.MSC.
- Navigate to the OU where the problematic computer account is located.
- Right click and go to properties of the computer account to open the properties.
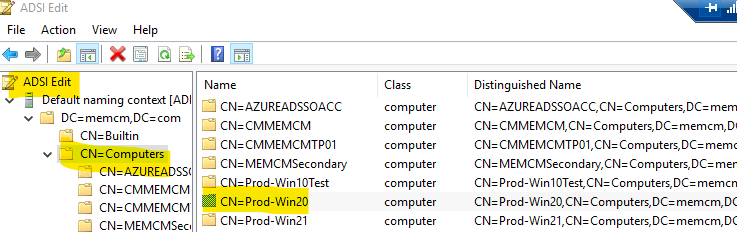
Now, you can scroll down until you reach the msDS-supportedencryptiontypes attribute. You can change the encryption attribute to 24 directly to fix the issue with that computer.
Double click on the attribute you want to change and enter the value as explained above to 24. Click on OK and OK t save the value.
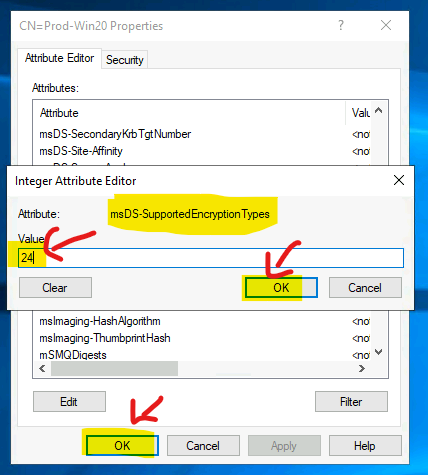
After changing the Encryption Types in the Active Directory (ADSI Edit) for the computer account, the Endpoint Protection policy worked as expected. Post that initiated SCCM Policy, we could see folders were excluded.
NOTE! – More details about encryption values Decrypting the Selection of Supported Kerberos Encryption Types – Microsoft Tech Community.
Disclaimer – The information provided on the site is for general informational purposes only. All information on the site is provided in good faith. However, we make no representation or warranty of any kind, express or implied, regarding the accuracy, adequacy, validity, reliability, availability, or completeness of any information on the website.