This post will take you through the Intune Audit IPsec Driver Policy deployment. We’ll make use of Intune’s Settings Catalog to enforce this policy. Configuration Profiles of Intune will be used to accomplish this task.
Audit IPsec, Driver Policy configuration, enables the auditing of events produced by the IPsec filter driver, encompassing the following scenarios: initiation and termination of IPsec services, rejection of network packets due to integrity check failure, rejection of network packets due to replay check failure, rejection of network packets for being in plaintext, and reception of network packets with an incorrect Security Parameter Index (SPI).
This might signal issues with the network card or the need for driver updates. Additionally, the policy covers the inability to process IPsec filters. An audit event is triggered for each IPsec filter driver operation when this policy setting is applied.
Successful attempts are documented as Success audits, while unsuccessful attempts are logged as Failure audits. Failure to configure this policy setting results in the absence of audit events for IPsec filter driver operations.

Deploy Intune Audit IPsec Driver Policy
To Deploy Intune Audit IPsec Driver Policy, follow the steps stated below:
- Sign in to the Intune Admin Center portal https://intune.microsoft.com/.
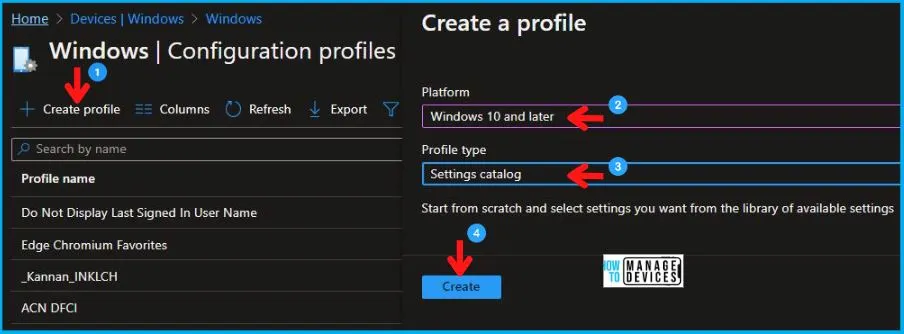
- Select Devices > Windows > Configuration profiles > Create a profile.
In Create Profile, I select Windows 10 and later in Platform and select Profile Type as Settings catalog. Click on the Create button.
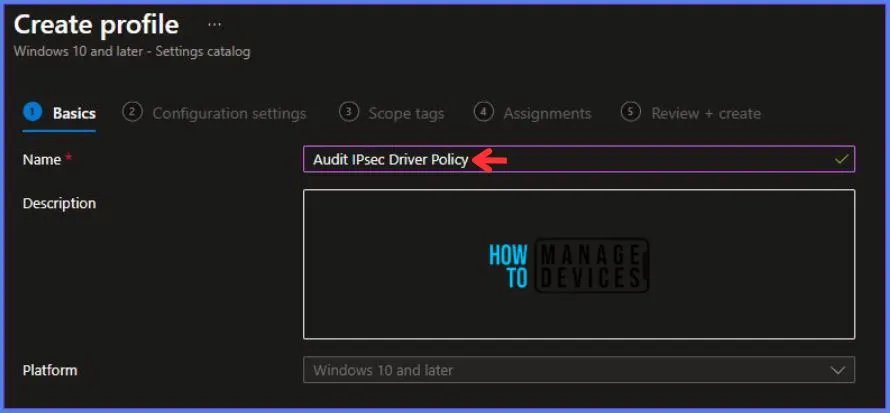
On the Basics tab pane, I provide a name for the policy as “Audit IPsec Driver Policy.”
- Optionally, if you want, you can enter a policy description and proceed by selecting “Next“.
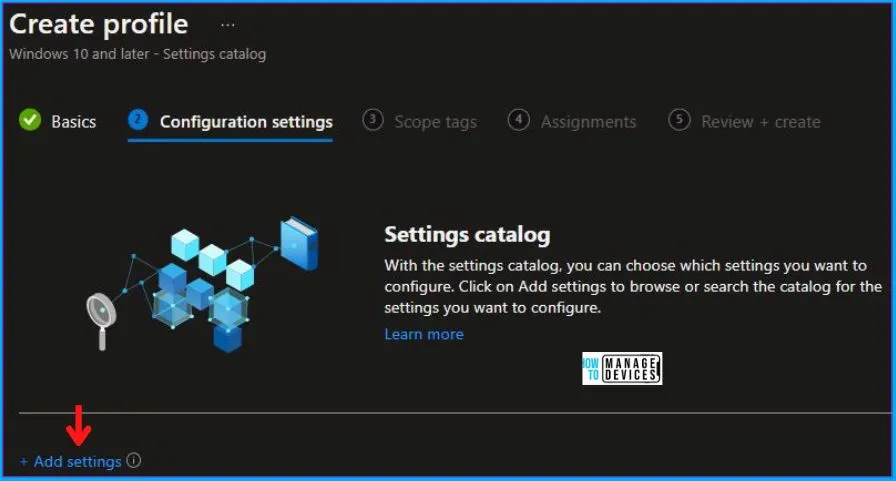
Now in Configuration Settings, Click Add Settings to browse or search the catalog for the settings I want to configure.
In the Settings Picker windows. I searched for the keyword Audit. I found the category Auditing and selected this.
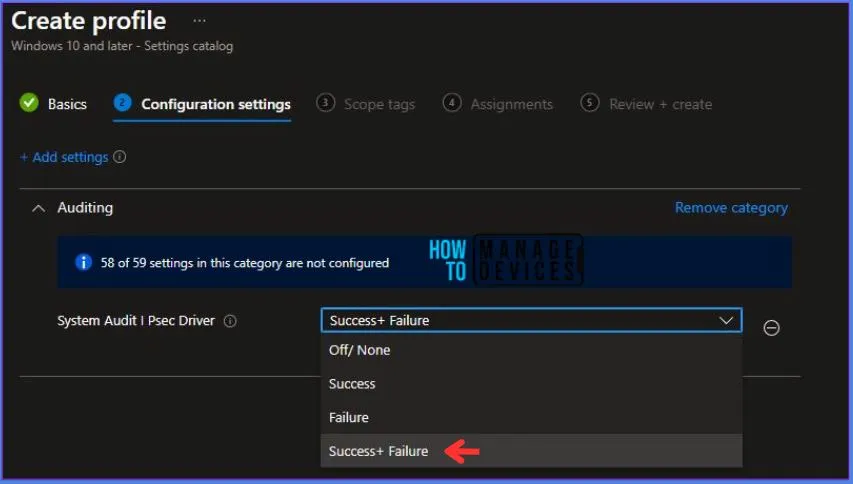
When I select that option as stated above, I see the sub-category System Audit I Psec Driver. After selecting that, click the cross mark at the right-hand corner, as shown below.
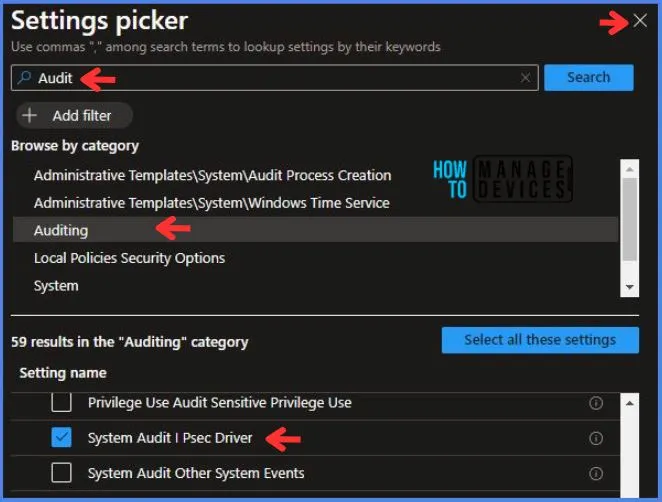
Here in System Audit I Psec Driver, there are multiple options to select, which are:
- Off/ None
- Success
- Failure
- Success + Failure
Here I choose Success + Failure for this policy.
Using Scope tags, you can assign a tag to filter the profile to specific IT groups. One can add scope tags (if required). More details on Intune Scope Tags Implementation Guide.
- Click Next to continue.
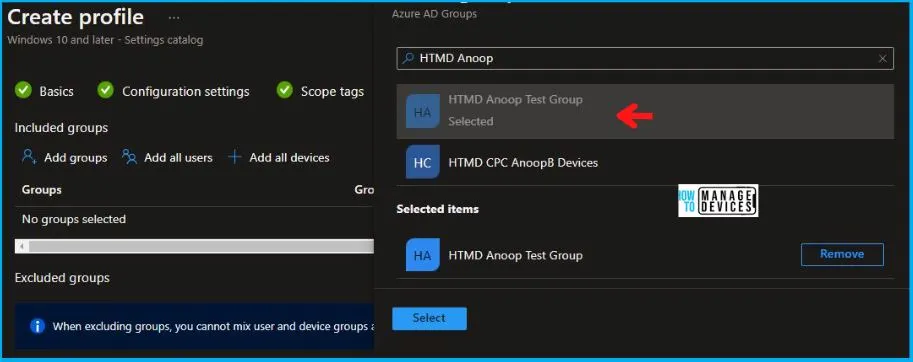
Now in Assignments, in Included Groups, you need to click on Add Groups and choose Select Groups to include one or more groups. Click Next to continue.
In the Review + Create tab, I review settings. After clicking on Create, changes are saved, and the profile is assigned.
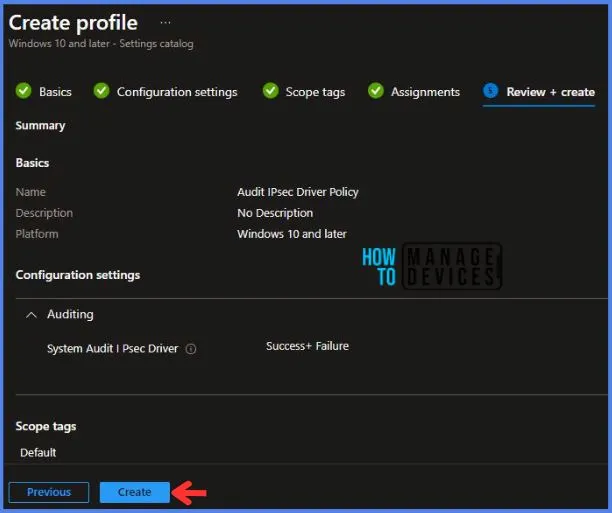
After successfully creating the “Audit IPsec Driver Policy,” a notification will appear in the top right-hand corner confirming the action. You can also verify the policy’s existence by navigating to the Configuration Profiles list, where it will be prominently displayed.
Your groups will receive your profile settings when the devices check in with the Intune service. The Policy applies to the device.
Intune Report for Audit IPsec Driver Policy
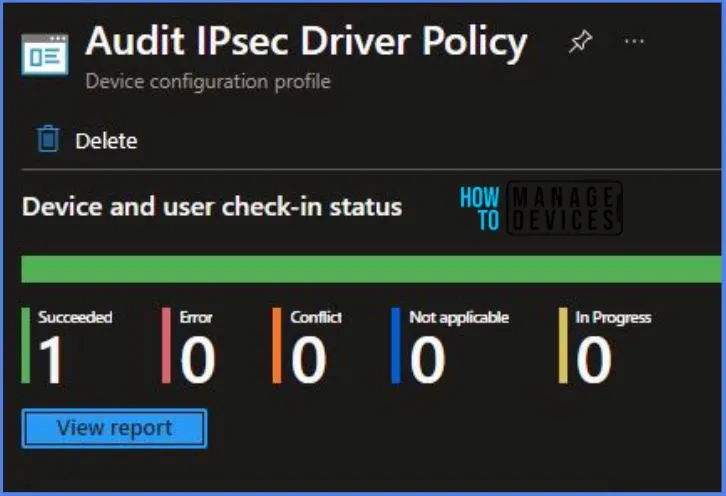
From the Intune Portal, you can view the Intune settings catalog profile report, which provides an overview of device configuration policies and deployment status.
To track the assignment of the policy, you need to select the relevant policy from the Configuration Profiles list. Then, you can review the device and user check-in status to determine whether the policy has been successfully applied.
- If you require more detailed information, you can click on “View Report” to access additional insights.
Intune MDM Event Log – Audit IPsec Driver Policy
To verify the successful implementation of String or integer policies for Audit IPsec Driver Policy on Windows 10 or 11 devices through Intune, you can leverage event IDs 813 and 814.
These event IDs provide valuable insights into the Audit IPsec Driver Policy‘s application status and the specific value assigned to the policy on those devices. In the case of this particular policy, the value is an Integer and is linked to the event ID 813.
By analyzing these event IDs, you can gain a clear understanding of the policy’s application status and the corresponding value associated with it on the devices in question.
To confirm this, you can check the Event log path – Applications and Services Logs – Microsoft – Windows – Devicemanagement-Enterprise-Diagnostics-Provider – Admin.
MDM PolicyManager: Set policy string, Policy: (


