Let’s check the Intune Audit Logs Track Who Restarted Device from MEM Portal. You can remotely initiate to restart the device from the Intune.
Intune Audit Logs are constructive to track who did what in your MEM environment. Audit logs include a record of activities that generate a change and show details on each event or task performed in the environment.
The Restart device remote action causes the device you choose to be restarted (within 5 minutes). You can check the status of the performed action by navigating to the device’s node and selecting the device in MEM Portal. However, It’s difficult to identify who has triggered the action until you have not done.
Once any of the actions are performed by users, you can directly visit audit logs to see recent actions. I have noticed that Audit logs in the MEM portal are very short-lived or removed immediately from the dashboard.
Create, update (edit), delete, assign, and remote actions to create audit events that administrators can review for most Intune workloads. By default, auditing is enabled for all customers. It can’t be disabled.
Who can access the data from Intune Audit Logs? Users with the following permissions can review audit logs –
- Global Administrator
- Intune Service Administrator
- Administrators assigned to an Intune role with Audit data – Read permissions
Recommended Posts –
- Windows 365 Cloud PC Audit Logs
- Migrate Group Policies GPOs to Intune Settings Catalog policy
- Intune Logs Event IDs IME Logs Details for Windows Client Side Troubleshooting
Intune Audit Logs Track Who Restarted Device from MEM Portal
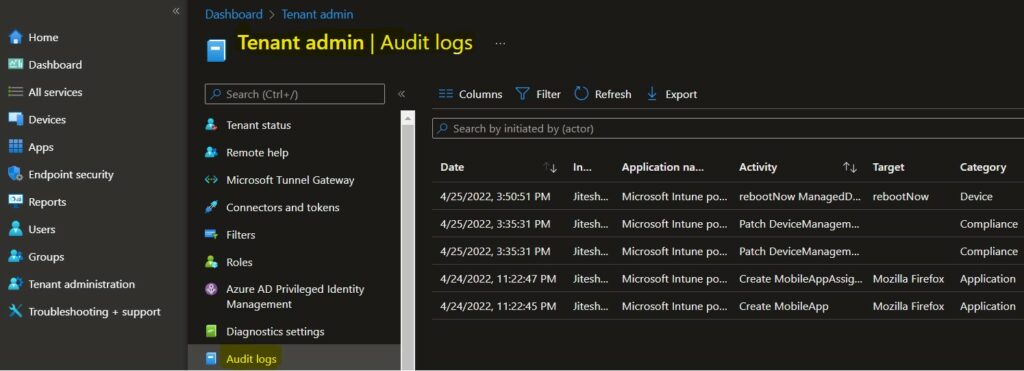
Let’s check who has restarted the device. You can find details from the audit logs in the MEM Admin center portal –
- Sign in to Microsoft Endpoint Manager Admin Center https://endpoint.microsoft.com/
- Select Tenant administration > Audit logs.
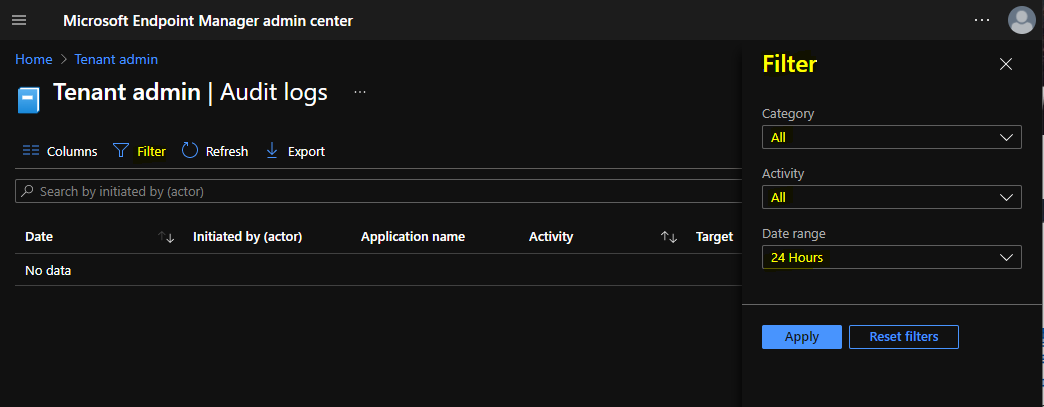
Select Filter and refine the results using the following options and select Apply to filter the results.
- Category: such as Compliance, Device, and Role.
- Activity: the options listed here are restricted by the option chosen under Category.
- Date range: you can choose logs for the previous month, week, or day.
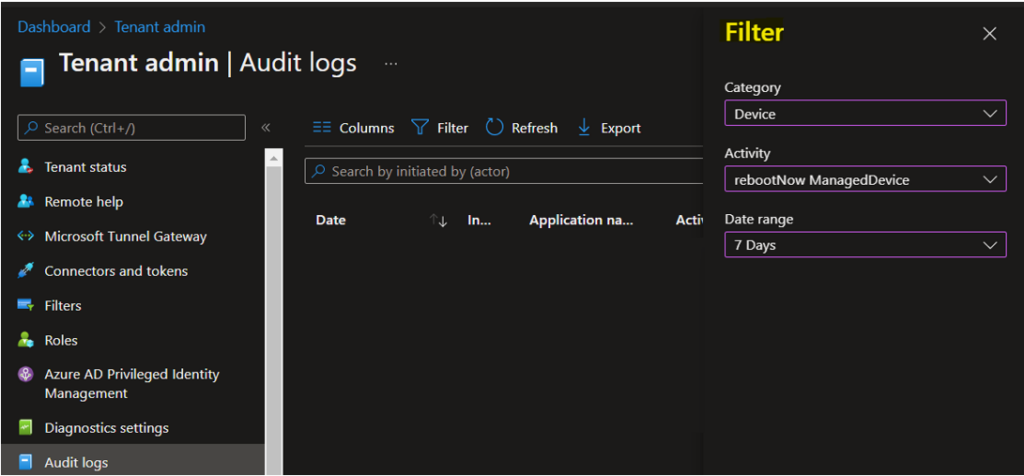
Let’s check who has rebooted the device. You need to click on Filter and select the following options to get the details for created device configuration policy and click Apply –
- Catagory – Device
- Activity – rebootNow ManagedDevice
- Date range -> 7 Days
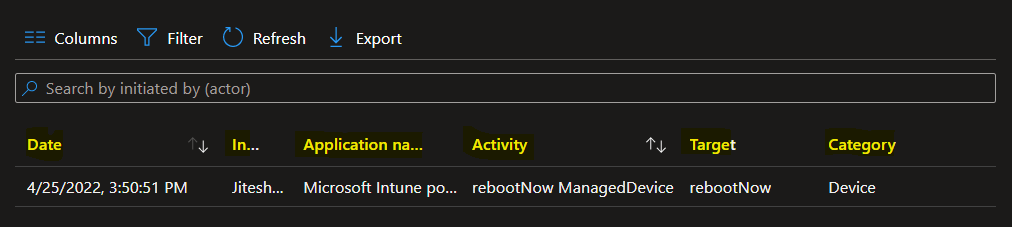
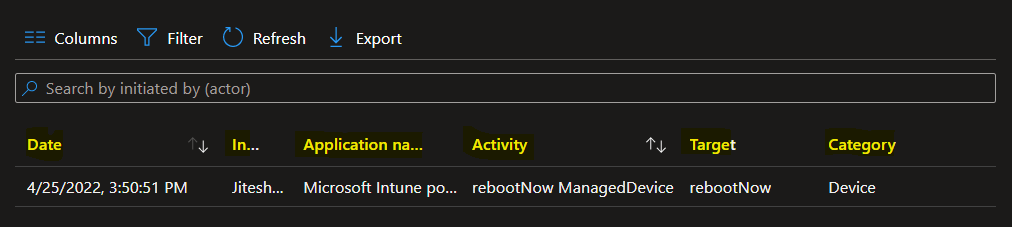
The following are some of the categories available for MEM portal audit logs. You can select an item in the list to see the activity details.
- Date – Date of the activities.
- Initiated by (actor) – Who Initiated the Action?
- Application name – The API name of the application.
- Activity – rebootNow ManagedDevice
- Target – Profile Name
- Category – Device
Here you can see the activity details for the activity rebootNow ManagedDevice.
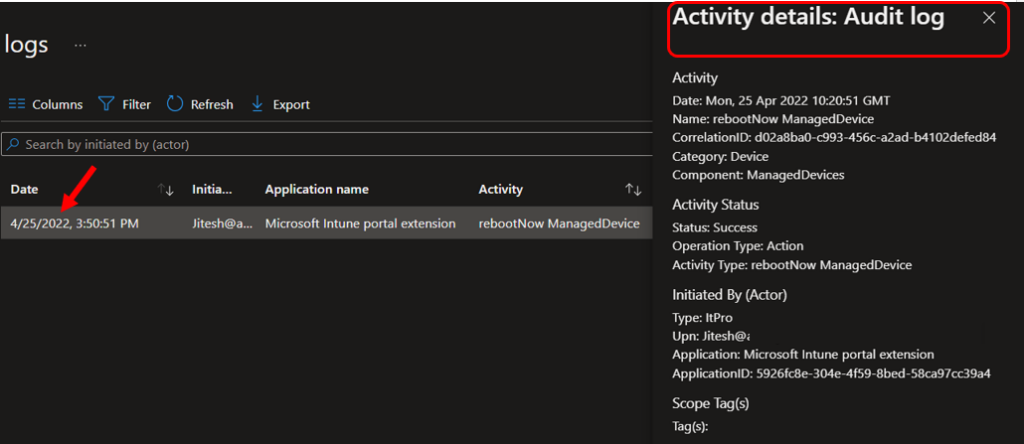
Activity details: Audit log
Activity
Date: Mon, 25 Apr 2022 10:20:51 GMT
Name: rebootNow ManagedDevice
CorrelationID: d02a8ba0-c993-456c-a2ad-b4102defed84
Category: Device
Component: ManagedDevices
Activity Status
Status: Success
Operation Type: Action
Activity Type: rebootNow ManagedDevice
Initiated By (Actor)
Type: ItPro
Upn: Jitesh@htmd.onmicrosoft.com
Application: Microsoft Intune portal extension
ApplicationID: 5926fc8e-304e-4f59-8bed-58ca97cc39a4
Scope Tag(s)
Tag(s):
Target(s)
Target
Type: Microsoft.Management.Services.Api.ManagedDevice
Name: rebootNow
ObjectID: 7f4fbc73-6a36-477c-b32a-f436f058bd6a
Modified Properties
Property: DeviceManagementAPIVersion
New Value: 5022-02-03
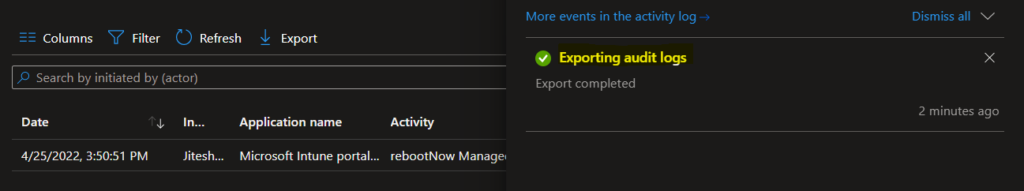
Old Value: Export Intune Audit Logs
Let’s follow the steps below to export the audit logs that would be helpful for reporting –
In the filtered Intune Audit logs, Select Export.
A prompt will appear clicking on Download will export all data.
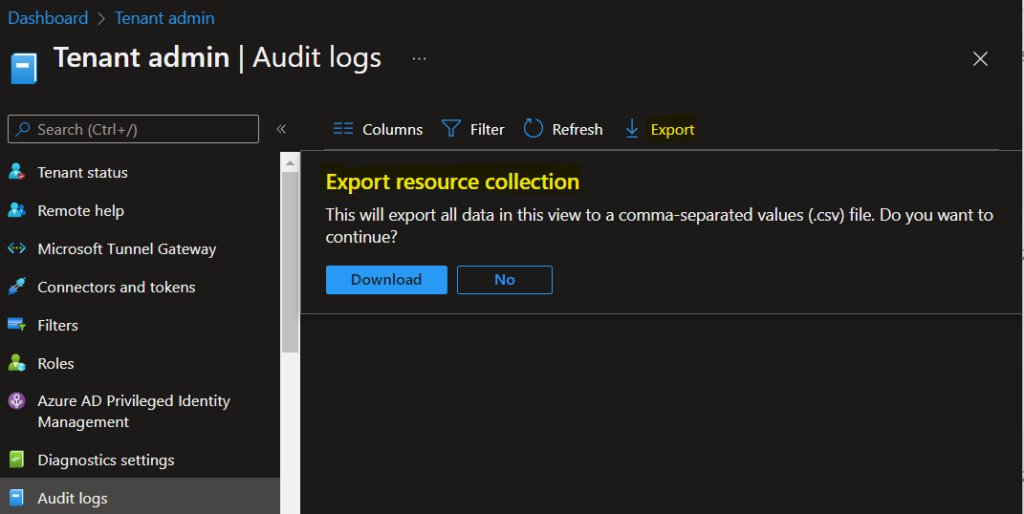
A notification will appear automatically in the top right-hand corner with the message Export is in progress. You can also see the status by selecting the notification icon.
The exported audit logs will be automatically downloaded in a .csv file to your browsers, and a notification message will appear Export completed.