Let’s check how to Migrate Group Policies GPOs to Intune using Settings Catalog policy and Group Policy Analytics. Microsoft added a migration option to the Group Policy Analytics workflow.
The system admins can quickly import, asses, and migrate GPOs to Intune using Intune Group Policy Analytics workflow. This is the easiest method to migrate on-prem to Cloud GPOs.
Intune Group Policy analytics is a tool that shows which settings are supported in cloud-based MDM providers. This tool helps identify the deprecated GPO settings or GPO settings that are not available. This tool also provides options to migrate GPOs to Intune Settings Catalog policy.
I don’t recommend importing all the Group Policies from on-prem Active Directory to Intune; rather, the better approach is to assess each GPO’s requirement and then migrate to Intune if it’s still required and supported by MDM CSP.
You can now create a Settings Catalog policy using your imported GPOs with the Group Policy analytics tool. After assessing GPO settings, there will be a Migrate option that creates a Settings Catalog profile.
Why Migrate to Cloud GPO?
On-prem GPOs are managed by Active Directory domains and the central GPO management is available for Domain Joined Windows 11 or Windows 10 PCs.
The modern management strategy is to join the Windows 11 devices to Azure AD join. You can’t manage Azure AD joined devices with AD group policies. So to manage to deploy and manage group policies for Azure AD joined Windows 11 devices, you need to use Cloud GPO using Intune or another MDM CSP solution.
Video Tutorial How to Migrate to Cloud GPO
Let’s check out the Video Tutorial on How to Migrate to Cloud GPO.
Export GPOs to XML using GPMC.msc
You need to find out the Group Policy settings from the On-prem Active Directory environment. The next step is to export a Group Policy Objects (GPOs) as an XML file.
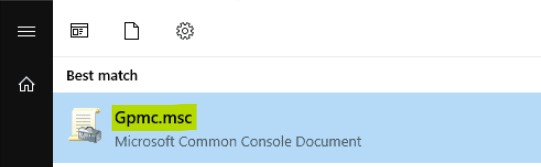
- Login to the Server or Workstation where you have access to Group Policy Management App (GPMC.msc) to export GPOs to XML.
- Launch Group Policy Management App (GPMC.msc) application.
Navigate to the Group Policy setting that you want to export. Select and right-click on the settings, then select the Save Report option.
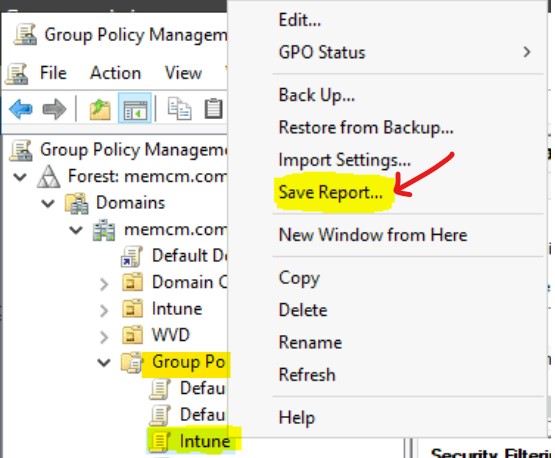
Let’s save the GPO settings to the folder from where you can import the XML file to Intune portal.
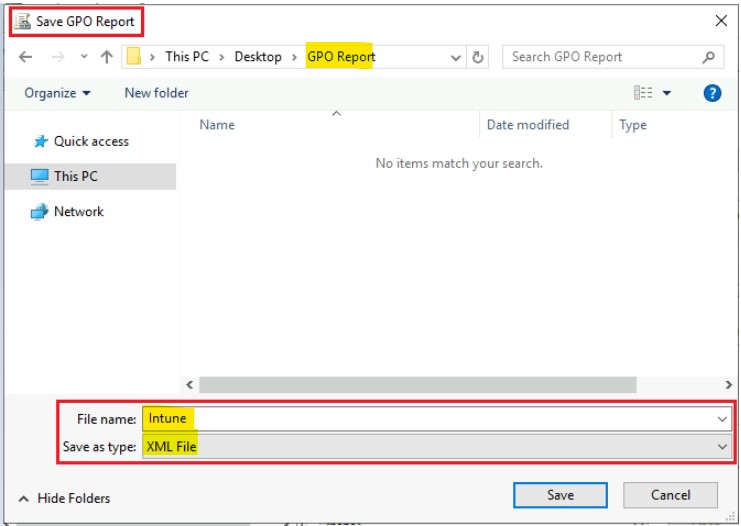
- From Save File prompt window, select Save As option.
- Click on the Browse button to select the appropriate folder path to save the XML file.
- In the Save as prompt:
- You have to enter the appropriate File Name for the XML file.
- You can save it as type “XML File.”
- Click on the Save Button.
Import Group Policy XML to Intune
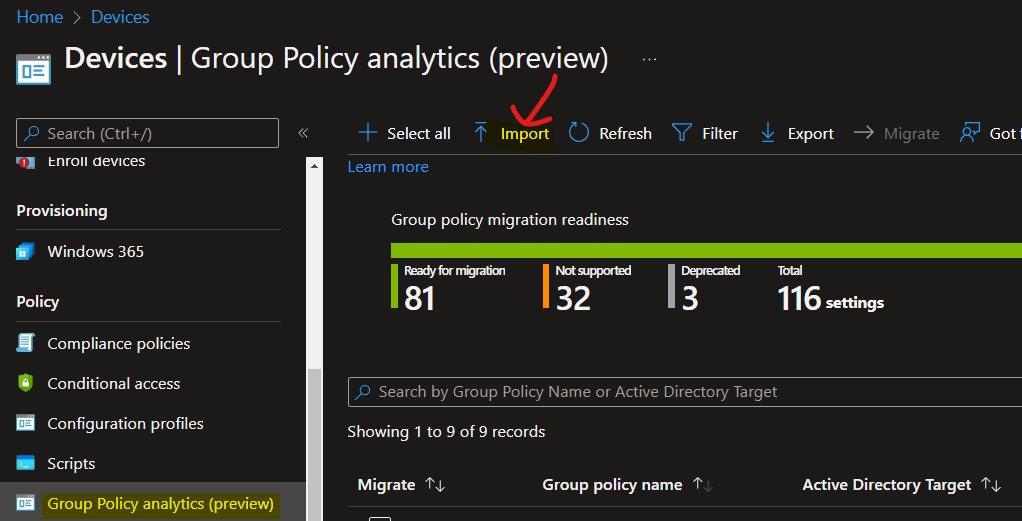
Let’s import the group policy XML files to Intune using the tool called Group Policy Analytics. The maximum size allowed for a single GPO XML file is 4 MB. If a single GPO is larger than 4 MB, the import will fail. Also, the GPO file must be Unicode-encoded.
Use Group Policy analytics to analyze your on-prem Group Policy Objects (GPO) and determine your level of modern management support. Click “Import” to begin the analysis and “Migrate” when you’re ready to move your settings to modern management.
You can follow the steps below to import the GPO XML to Intune.
- Login to the Endpoint.Microsoft.com portal.
- Navigate to Devices > Group Policy analytics (preview).
- Click on the Import button.
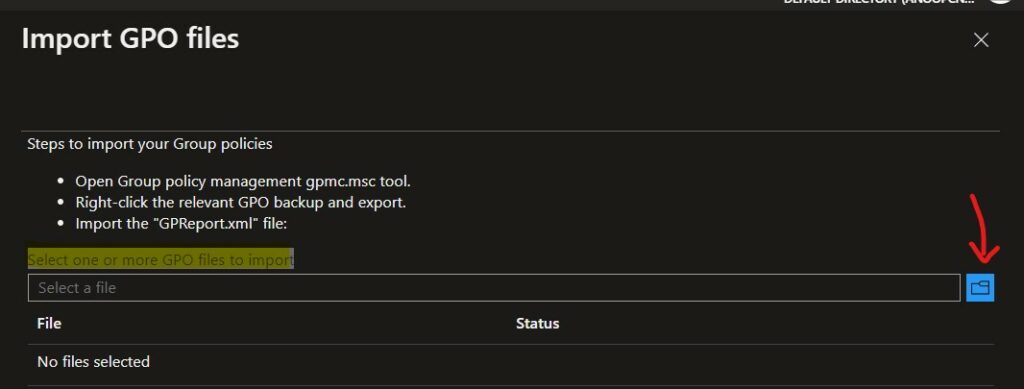
Let’s select the exported GPO file (XML) to Intune using the folder icon button as shown in the below screenshot. You can choose one or more GPO files to import.
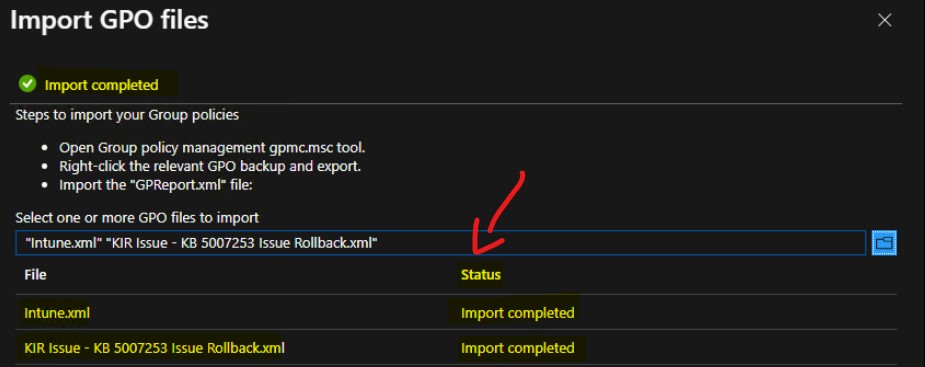
You will get a notification on the Import GPO files blade once the GRPO files are imported successfully. I have imported two GPO XML files, and I received the Import Completed message for both the XMLs.
Monitor Imported GPOs using Intune Group Policy Analytics
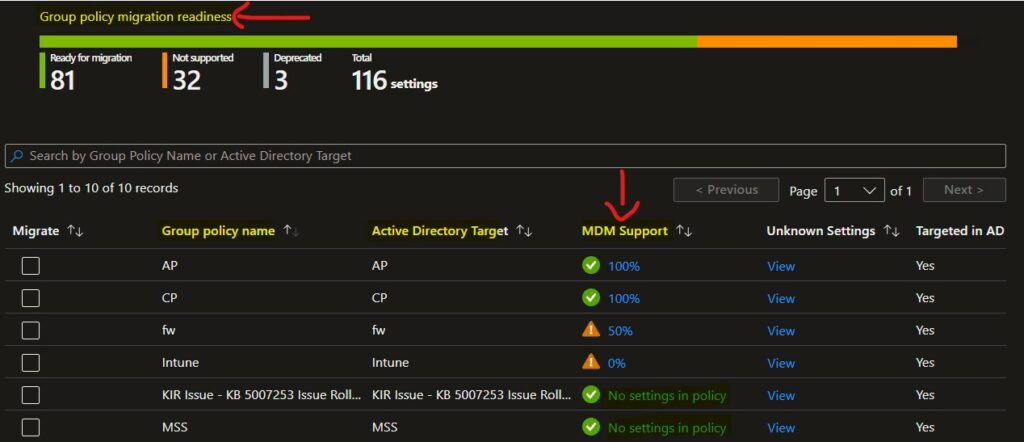
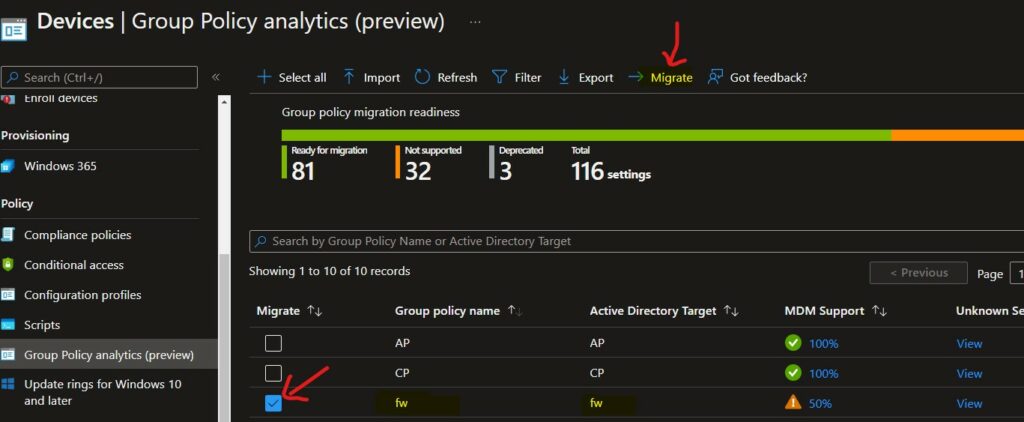
Let’s check the imported GPOs using Intune Group Policy Analytics tool. Different options are available on the home page (Group policy migration readiness) for the Group Policy Analytics tool. These columns and sample values are shared in the following table and screenshot.
The following list from Group policy migration readiness provides the details of each column that contains the results of Group Policy Analytics from Intune.
- Group Policy name: The name is automatically generated using the information in the GPO.
- Active Directory Target: The target is automatically generated using the organizational unit (OU) target information in the GPO.
- MDM Support: This shows the percentage of group policy settings in the GPO with the same Intune setting.
- Targeted in AD: Yes, the GPO is linked to an OU in on-premises group policy. No means the GPO isn’t linked to an on-premises OU.
- Last imported: This shows the date of the last imported.
| Migrate | Group policy name | Active Directory Target | MDM Support | Unknown Settings | Targeted in AD | Last Imported |
| AP | AP | 100% | View | YES | ||
| FW | FW | 50% | View | YES | ||
| Intune | Intune | 0% | View | YES | ||
| MSS | MSS | No settings in the policy | View | YES |
NOTE! – The percentage under the MDM Support column will get automatically updated to reflect the changes. This happens whenever the Microsoft Intune product team changes the mapping between GPO settings and MDM Policies in Intune.
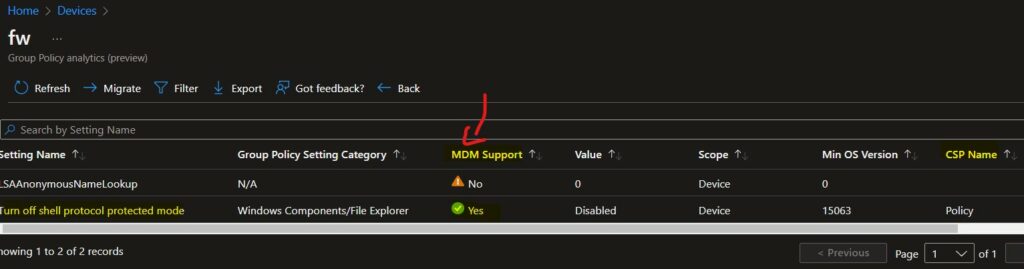
You can click on the View link to analyze which GPO settings are compatible with MDM CSP settings and which are not. The details of Group Policy Analytics provide CSP mapping for each GPO setting if there a supported MDM CSP settings.
- Setting Name – Provides the GPO Setting Name.
- Group Policy Setting Category – Provide the CSP or Group Policy settings category path.
- MDM Support – YES means the MDM CSP supports the GPO setting. NO means this Group Policy setting is not supported by the MDM CSP.
- Value – Provides the value set in the group policy configuration.
- CSP Mapping – This column provides the corresponding CSP mapping for each GPO setting.
| Setting Name | Group Policy Setting Category | MDM Support | Value | Scope | Minimum OS Version | CSP Name | CSP Mapping |
| LSAAnonymousNameLookup | No | 0 | 1 | 0 | null | null | |
| Turn off shell protocol protected mode | Windows Components/File Explorer | Yes | Disabled | 1 | 15063 | Policy | ./Device/Vendor/MSFT/Policy/Config/ADMX_WindowsExplorer/ShellProtocolProtectedModeTitle_2 |
The analytics include the minimum supported version of OS required for MDM CSP settings. This information and CSP mapping information are useful to assess the group policy migration process.
Migrate Group Policies to the Cloud Intune
Let’s check how to migrate the supported Group Policies to the Cloud Intune. The settings are ready for migration or have technology available in cloud-based Device Configuration (MDM).
When you migrate or move to cloud-based (MDM CSP) policy management, you need to evaluate each setting for applicability to your organization.
As part of the Migration workflow, Microsoft will present some groups of settings supported in MDM, and you can confirm if you want to configure them in MDM policy.
There are two options to migrate Group Policies to Intune while writing this post during the preview release. To start the Migration workflow, you can select one particular Group Policy Settings from the Group policy migration readiness home page, as shown below.
- From the Devices -> Group Policy Analytics page, select one of the GPO settings that you want to migrate.
- Click on Migrate button to start the Group Policy to Intune Cloud policy migration workflow.
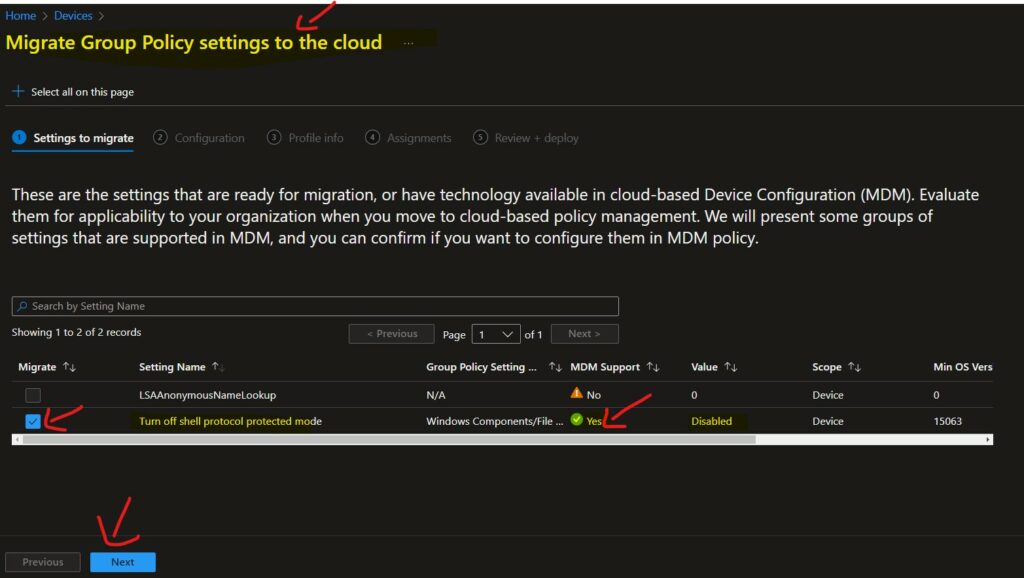
From the Migrate Group Policy settings to the cloud page, you get an option to select only the supported GPO Settings. If one GPO setting is not supported for MDM CSP migration, you can’t select that particular GPO setting, as you see in the below screenshot.
Turn off shell protocol protected mode is the only supported Group Policy setting in the MDM CSP migration scenario. The LSAAnonymousNameLookup setting is not supported with the MDM CSP setting.
- I have selected Turn off shell protocol protected mode GPO settings to migrate.
- Click on the Next button to continue.
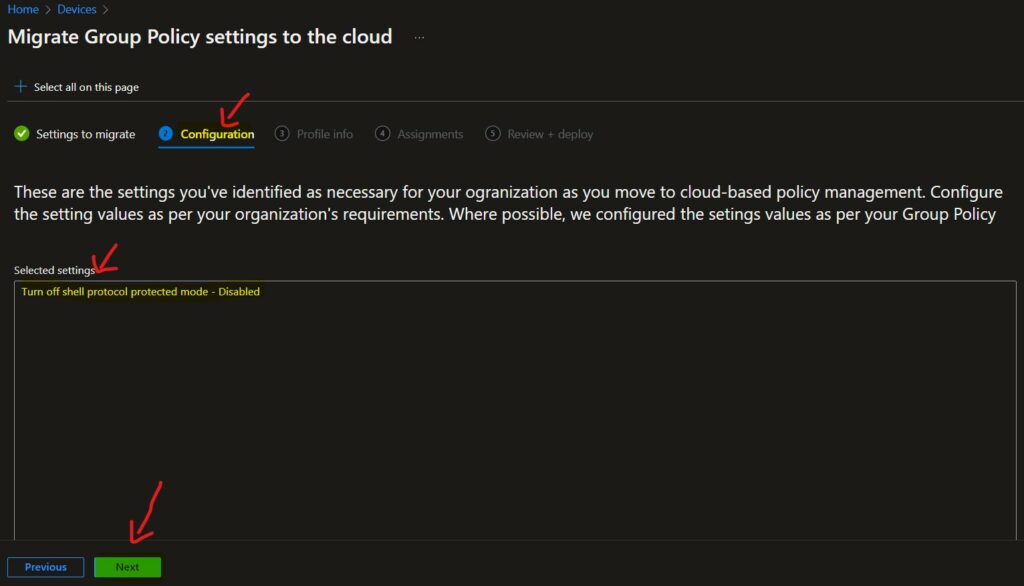
The next screen (Configuration page) provides the following description and lists all the selected GPO policies from the previous page with the settings of individual policies.
Ensure that these are the settings you’ve identified as necessary for your organization as you move to cloud-based policy management. Configure the setting values as per your organization’s requirements. Where possible, Microsoft configured the settings values as per your Group Policy.
- Selected Settings – Turn off shell protocol protected mode – Disabled
- Click on the Next button to continue.
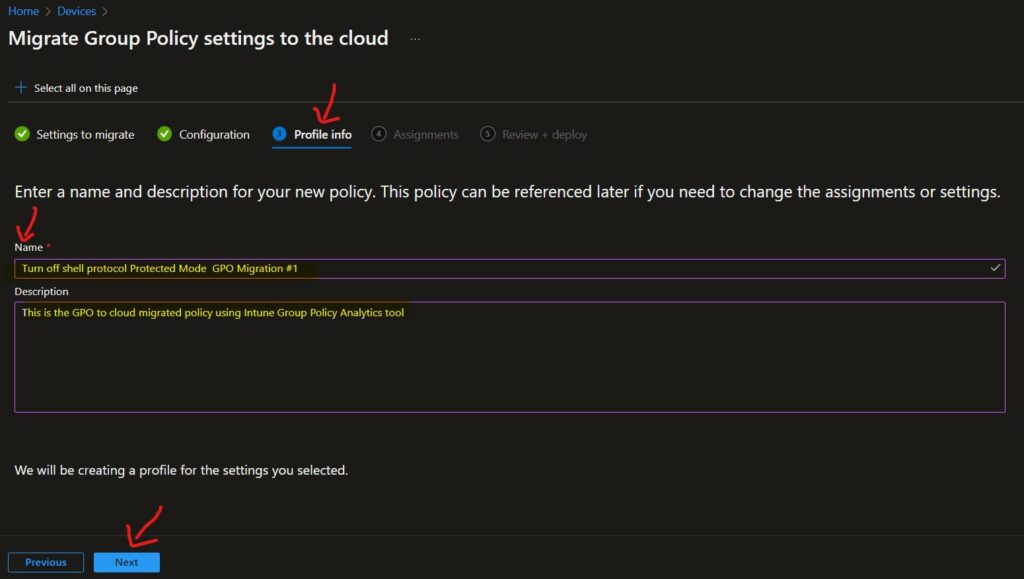
You need to Enter a name and description for your new MDM policy. This policy can be referenced later if you need to change the assignments or settings.
- Enter the Name of the policy – Turn off shell protocol Protected Mode GPO Migration #1
- Enter the Policy Description – This is the GPO to cloud migrated policy using Intune Group Policy Analytics tool.
- Click on the Next button to go to the assignment page.
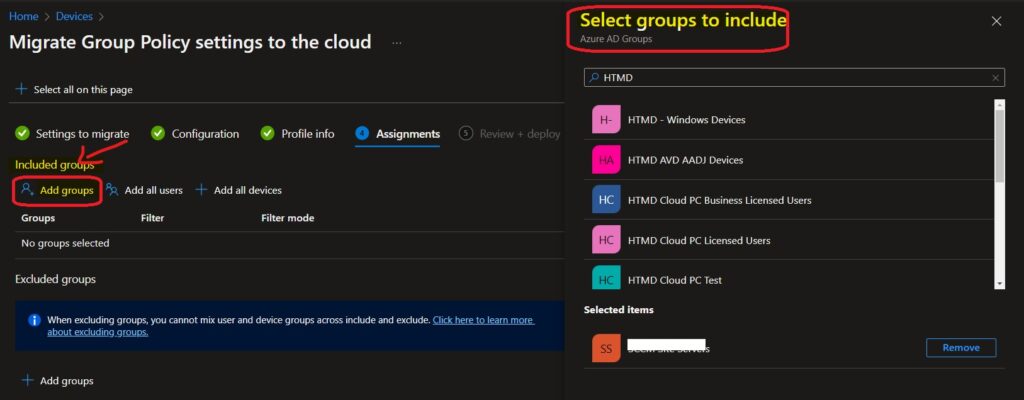
You can assign this cloud policy to Azure AD groups on the assignment page. You can search for the user or device Azure groups and assign the policy to that AAD group.
If you are looking for more details like How to Use Filters for Intune policy deployments, go through Use Filters For Assigning Apps Policies And Profiles In Intune Portal | Endpoint Manager.
- Under Assignments, Select Included groups and then choose Select groups to include one or more groups.
- Click on the Select and Next buttons to continue.
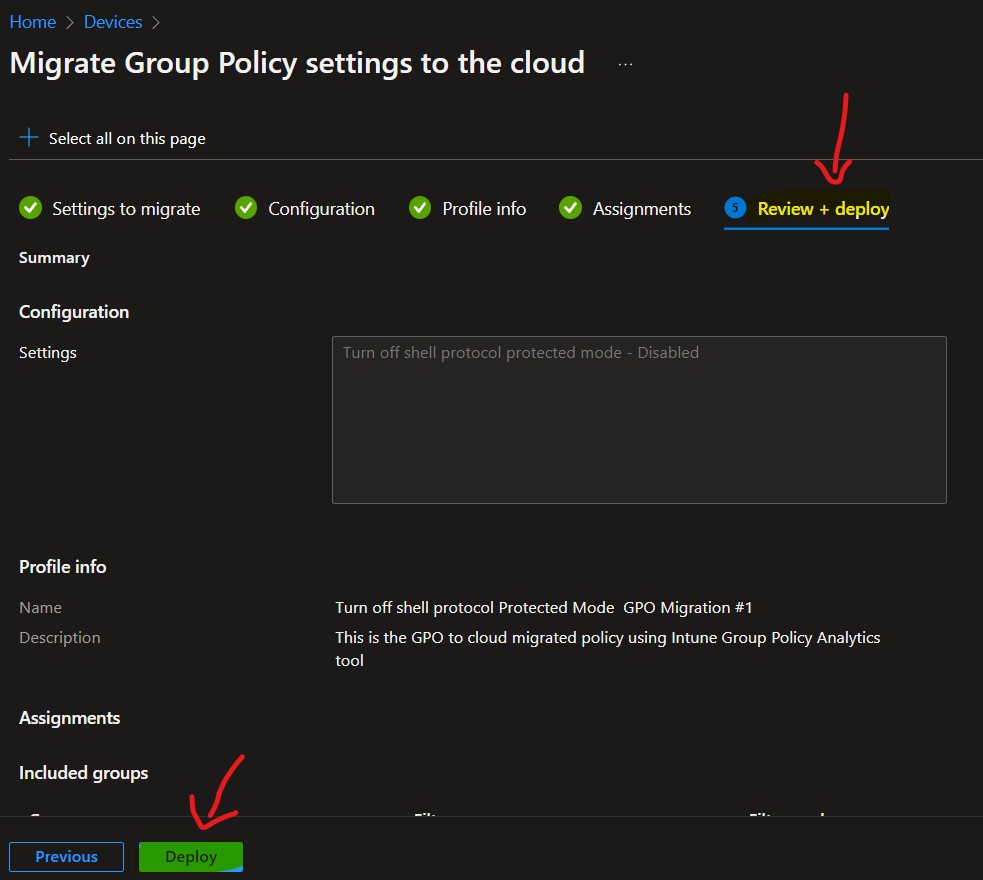
On the Review + Deploy page, you will get an option to verify and confirm all the configurations you did for this Group policy migration to Cloud (Intune).
- Click on the Deploy button to complete the Group Policy to Cloud Policy migration process.
Cloud GPO Policy Settings Reports | Event Logs | Troubleshooting
Let’s check the event logs to understand whether the Cloud policy is deployed to Windows 11 devices or not. There are different ways to pull reports (MDMDiagHTMLReport.html – MDM Diagnostic Information) for Cloud Policies, similar to RSOP in Group Policy reports.
Read More: Intune Policy Reports, Logs, Event IDs, and IME Logs Details For Windows Client Side Troubleshooting
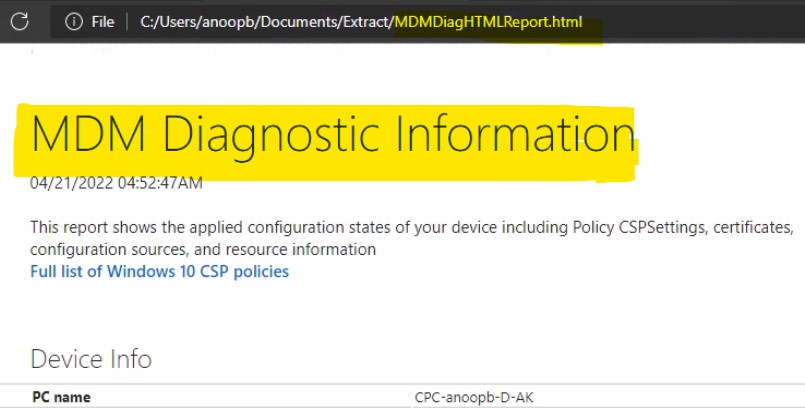
You can manually initiate the Intune (Cloud) policy Sync similar to Group Policy force update (gpupdate /force) using the following method Initiate a Manual Intune Policy Sync from Windows 10 or Windows 11 PCs.
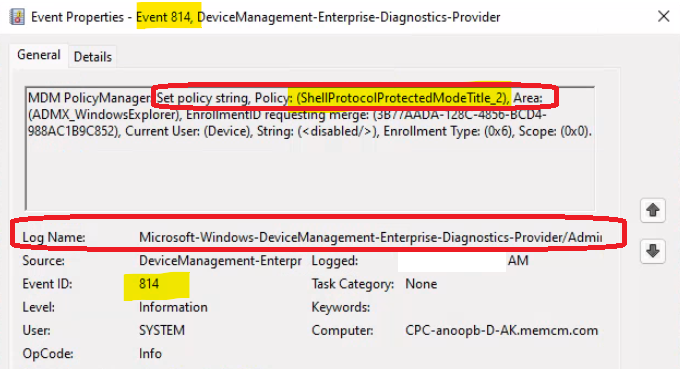
Intune log (event) path is the Applications and Services Logs – Microsoft – Windows – Devicemanagement-Enterprise-Diagnostics-Provider – Admin.
The event ID 814 signifies the type of Intune policy received as well. This event ID indicates that the policy received is STRING. As you know, there are different types of policy types in Windows CSP. The string is one of those policies.
MDM PolicyManager: Set policy string, Policy: (ShellProtocolProtectedModeTitle_2), Area: (ADMX_WindowsExplorer), EnrollmentID requesting merge: (3B77AADA-128C-4856-BCD4-988AC1B9C852), Current User: (Device), String: (), Enrollment Type: (0x6), Scope: (0x0).
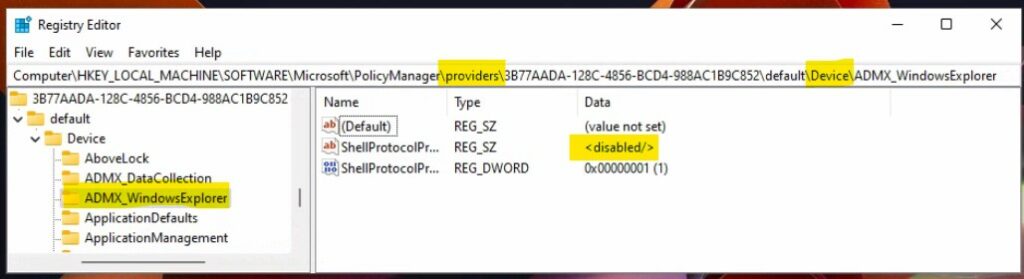
Cloud GPO Registry Settings | Intune Policy
Like Group Policy, Cloud policies or Intune policies can also be tracked through registry keys. There would be different registry paths for user policies and device policies. The following is the registry path and settings for the Turn off shell protocol protected mode policy.
Registry Settings for Cloud Policy | Intune Policy – Device Based Policy – > Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PolicyManager\providers\3B77AADA-128C-4856-BCD4-988AC1B9C852\default\Device\ADMX_WindowsExplorer
- Value name – ShellProtocolProtectedModeTitle_2
- Value Data – Disabled
Cloud Policy Reports from MEM Admin Center Portal
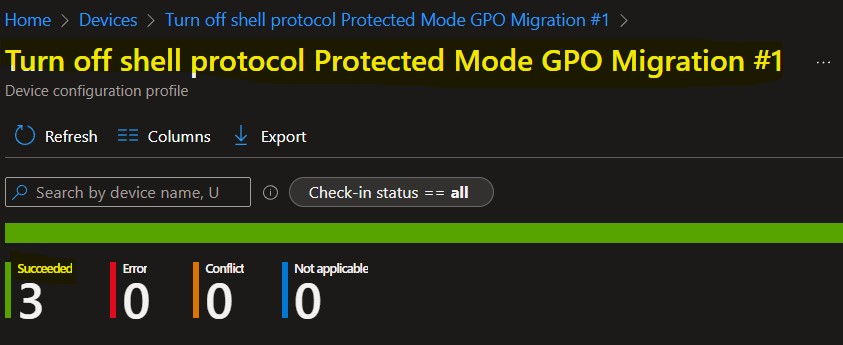
The Setting Catalog profile type is created as part of the Group Policy to Cloud policy migration process.
Read More – Intune Policy Per Setting Status Report
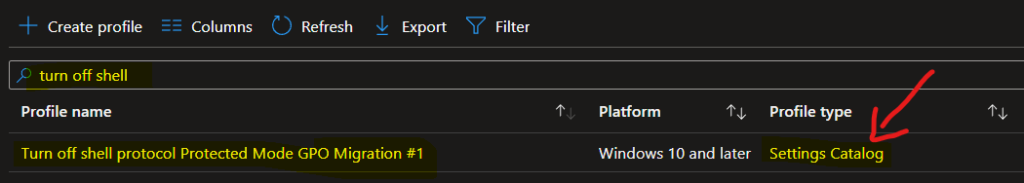
You can check the deployment reports from the server-side MEM admin center portal. You can also check the Cloud GPO Policy Settings deployment reports/status from Intune portal.
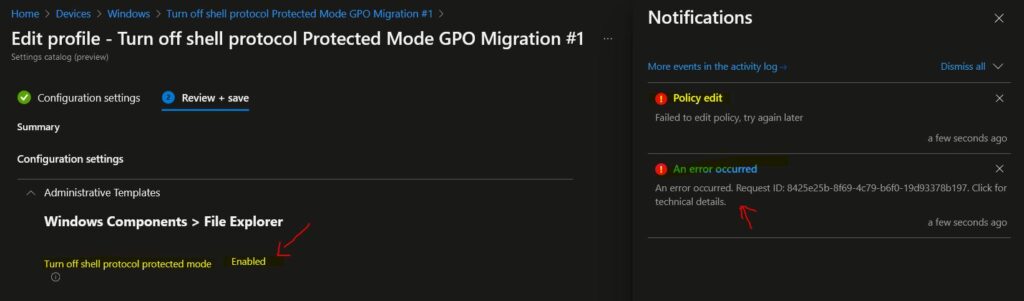
Known Issue with Altering Migrated Cloud GPOs
Update (16th June 2022) – I have performed a retest and the following know issue while editing the migrated Group Policy is FIXED! Thank you for the other hint MikeDano (Microsoft PM).
I have been asked to try altering the existing migrated policies with different configuration settings and tests by Murray Webber. I have done and to my surprise, the altering the settings of the migrated policy didn’t work.
When I clicked on the Save button it gave me the following error. So this is something you need to take care of. I hope Microsoft will fix the Known Issue with the Altering Migrated Cloud GPOs issue soon.
Policy editFailed to edit policy, try again later! An error occurred – Request ID: 8425e25b-8f69-4c79-b6f0-19d93378b197. Click for technical details.
I couldn’t find any technical details to further troubleshoot this issue in the link specified in the MEM Admin center portal.


Do you have any idea how to migrate Domain joined PCs to Intune? – Thank you!
For Hybrid Azure AD join devuces it’s easy …. but it’s not very easy to take decision based on one liner comment need to have strategic discussion. But technically it’s possible https://www.anoopcnair.com/windows-10-intune-enrollment-using-group-policy/
After importing the XML, I am getting many policies with MDM support- No. How to deploy such policies? Are any OMA URI options available? Or if we choose to deploy from AD GPO, how do we deploy for Intune managed devices.
Is there a way to export the .xml for each GPO without having to manually go to each one? (fancy powershell script)
Even i have settings in GP , After importing getting as “No Settings in policy”
We have around 60% of our gpo(1200) having item level targeting such as file match and other types of ILF , any suggestions on how to migrate those to Intune
PolicyPak has an application that can help bridge the gap between GPO and Intune. You will be able to deliver GP Preferences and continue to use ITL.