Hi All; let’s discuss about Modern Vs Legacy Azure Active Directory Authentication Methods. Microsoft has recently announced two significant enhancements to its authentication management processes that will provide users a more efficient experience when logging in to their accounts.
Alex Weinert shared the two key updates on May 09, 2023. With the ever-growing threat of cybersecurity breaches, it’s crucial to implement secure authentication protocols to safeguard sensitive data and prevent unauthorized access. However, the abundance of authentication methods available today can make it challenging to determine the most secure and effective.
These updates simplify the user authentication process and make it more user-friendly. This upgraded version of MFA is equipped with advanced features to detect and prevent fraud attempts during the authentication process. The General Availability of Converged Authentication Methods and Public Preview of a modernized multifactor authentication (MFA) Fraud Alert version.
The General Availability of Converged Authentication Methods allows users to use a more centralized and efficient authentication management system. This upgraded version of MFA has brought the configuration of fraud alert settings into the authentication methods policy, enabling administrators to manage and enforce security policies more efficiently.
- Easiest Method to Enable MFA for Admins using Azure AD Conditional Access
- How to Reset MFA Contact Details of Azure AD User
Modern Authentication Industry Standard
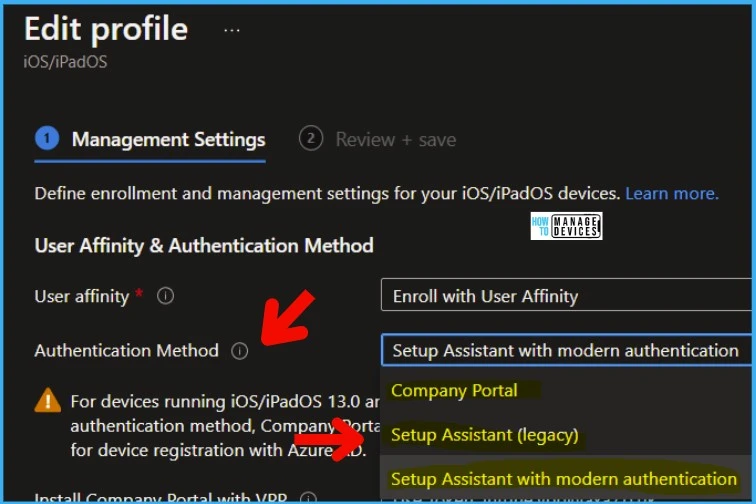
The new industry standard is modern authentication, which is not only for Microsoft. Apple is removing legacy authentication methods for its device enrollment scenarios. You need to change the authentication method to Setup Assistant for the existing ADE profiles with modern authentication.
Modern Vs Legacy Authentication Protocols
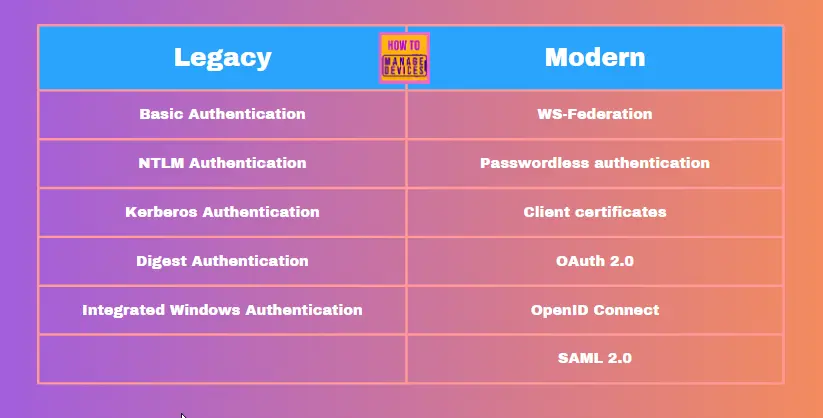
Let’s check out the different protocols between the legacy and modern authentication worlds. The following table will give you the details on different authentication protocols. Modern authentication protocols are aligned with Azure AD and other IDP providers such as Ping Identity.
| Protocol Name | Description | Legacy or Modern |
|---|---|---|
| Basic Authentication | Sends the user’s username and password in cleartext over the network. | Legacy |
| Digest Authentication | Sends the user’s username, password, and a hashed version of the password over the network. | Legacy |
| Integrated Windows Authentication | Uses the user’s Windows credentials to authenticate them to a web server. | Legacy |
| Kerberos Authentication | Uses a trusted third party to authenticate users to a web server. | Legacy |
| NTLM Authentication | Uses a challenge-response mechanism to authenticate users to a web server. | Legacy |
| OAuth 2.0 | A protocol for authorizing users to access third-party resources without sharing their passwords. | Modern |
| OpenID Connect | A protocol for authenticating users to third-party applications. | Modern |
| SAML 2.0 | A protocol for exchanging security assertions between identity providers and service providers. | Modern |
| WS-Federation | A protocol for exchanging security assertions between identity providers and web services. | Modern |
| Client certificates | A way to authenticate users by using a digital certificate. | Modern |
| Passwordless authentication | A way to authenticate users without using a password. | Modern |
Modern Authentication
In the past, authentication methods for Multifactor Authentication (MFA) and self-service password reset had to be managed separately, leading to potential inefficiencies and security gaps. However, recent advancements have enabled the management of MFA and self-service password reset methods in a single policy, along with passwordless methods like FIDO2 security keys and certificate-based authentication.
Additionally, user-reported suspicious MFA prompts are now integrated with Identity protection, enabling better fraud detection and mitigation. With these enhancements, Microsoft is taking a significant step forward in improving the security of its authentication management system.
- This integration gives users a more cohesive authentication experience and greater control for administrators.
- Additionally, the latest update includes newly added methods such as SMS, Voice Calls, Third-party Software OATH, and Email OTP, further enhancing the flexibility and security of the authentication management system.
- These developments represent a significant step in improving authentication management processes and strengthening cybersecurity measures.
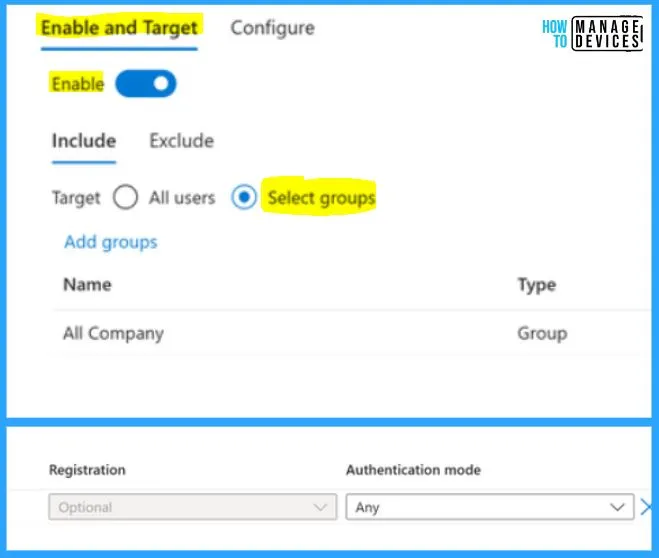
Microsoft’s latest update to its authentication management system offers greater granularity in managing authentication methods. With this new update, administrators can enable authentication methods for specific groups of users rather than applying them to all users.
- This allows for targeted testing of methods with pilot groups and limiting lower security methods like SMS and Voice to smaller groups of users.
- Moreover, administrators can exclude certain user groups from being targeted, further improving the customization and control over authentication policies.
- These granular management capabilities represent a significant advancement in authentication management, enabling organizations to tailor their authentication protocols to specific security requirements.
Under Enable and Target, you should toggle the pane to the right side; the included section shows the options such as Target, All users, and Select groups. From these included groups, choose the Select Groups option. Choose the Name, Type, Registration, and Authentication mode from the below window.
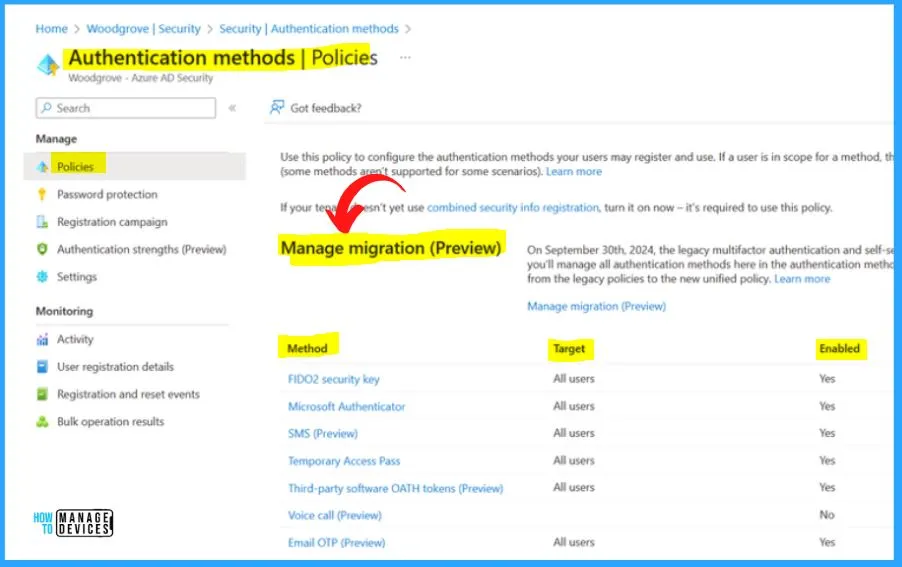
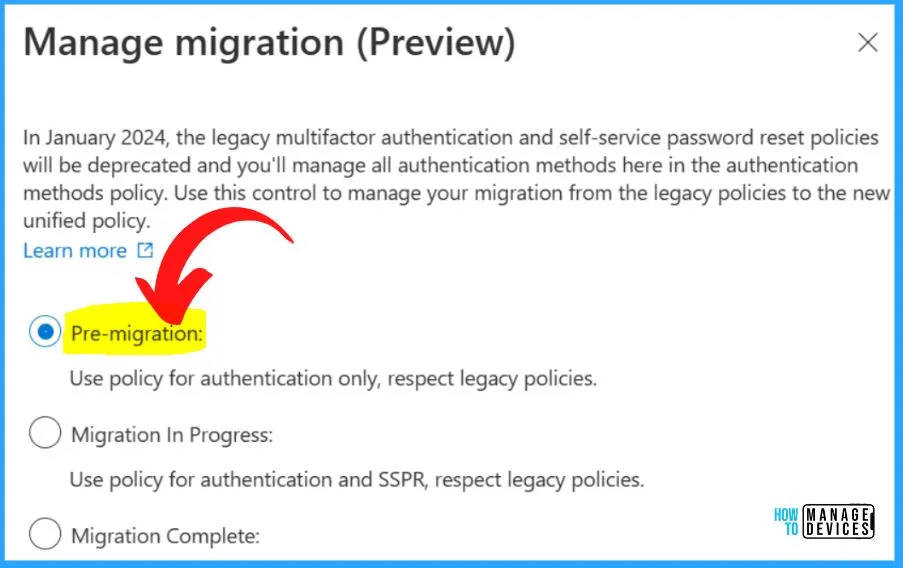
Microsoft has introduced a new migration control feature that simplifies the migration of authentication methods from legacy Multifactor Authentication (MFA) and self-service password reset policies to the updated authentication methods policy.
- This feature helps users ensure that all authentication methods are securely and accurately transferred without compromising the system’s integrity.
- With this new migration control, organizations can save time and effort while upgrading their authentication protocols, thus enhancing their overall security posture.
- This feature is another step towards making authentication management simpler and more efficient.
- Turn ON Pre-migration from the below Manage migration (preview) window
Note! – In January 2024, the legacy multifactor authentication and self-service password reset policies will be deprecated, and you will manage all authentication methods here in the authentication methods policy. Use this control to manage your migration from the legacy to the new unified policy.
MFA Fraud Alert Feature in Azure Active Directory
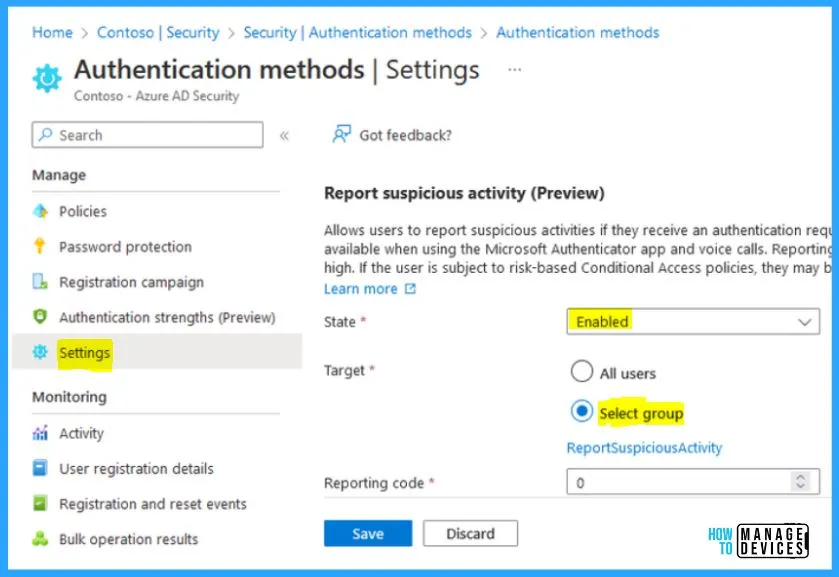
Azure Active Directory’s (Azure AD) MFA Fraud Alert feature has allowed users to report suspicious Multifactor Authentication (MFA) prompts received on the Microsoft Authenticator app or via phone. Managing this feature and its associated block list previously required Global Admin privileges, leading to potential inefficiencies and security risks.
- To address this, Microsoft has modernized the Fraud Alert feature by introducing the Report Suspicious Activity feature.
- This update has integrated the alert events with Identity Protection, allowing for more comprehensive and configurable action once a user reports a suspicious prompt.
- The new configuration has been moved to the authentication methods policy, allowing for a more centralized and streamlined approach to authentication management.
- By improving the Fraud Alert feature, Microsoft has strengthened its security measures and enhanced its authentication management capabilities.
Report Suspicious Activity (preview) allows users to report suspicious activities if they receive an uninitiated authentication request. This control is available when using the Microsoft Authenticator app and voice calls. Reporting suspicious activity will set the user’s risk too high. The user may be blocked if they are subject to risk-based conditional access policies.
- The State should be Enabled, and the Target should be Select Group.
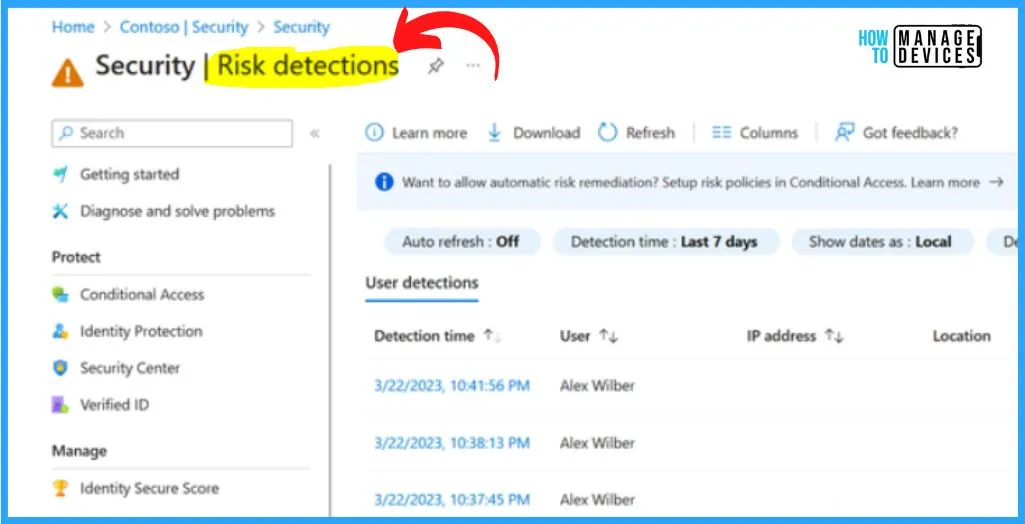
Risk Detections with Modern Authetication
When a user reports a suspicious Multifactor Authentication (MFA) phone app push notification or voice MFA prompt, their account will be flagged as having a high user risk. This security feature is automatically triggered once the Report Suspicious Activity feature is enabled, allowing for swift identification and action against potential fraudulent activities.
- With this update, Azure Active Directory (Azure AD) is better equipped to protect user accounts against unauthorized access and cyber threats, making it a more secure and reliable authentication management solution.
- By utilizing the risk-based policies available in Azure Active Directory (Azure AD), administrators can exercise greater control over the remediation process for users flagged with a high-risk status.
- These policies allow for more specific and tailored actions, such as requiring an immediate password change through a self-service password reset, mandating MFA for all authentications until the risk is resolved, or even blocking authentication entirely until the issue is addressed.
Modern Authentication VS Legacy Authentication
Modern authentication methods offer enhanced security and flexibility. Modern authentication is a set of advanced techniques and methods that utilize multifactor authentication (MFA) and other sophisticated security measures to protect against a range of cyber threats, such as phishing, man-in-the-middle attacks, and other malicious activities.
- Compared to traditional authentication methods, modern authentication offers a more comprehensive approach to security, providing a robust defense against the latest and most sophisticated cyber threats.
- Individuals and organizations can better safeguard their sensitive data with modern authentication methods.
Legacy Authentication is the traditional method to verify a user’s identity. These methods rely on single-factor authentication, such as a username and password. This method does not include additional security measures like multifactor authentication (MFA) or biometric authentication.
- Legacy authentication is less secure than modern authentication.
- Legacy authentication is easily compromised by cyberattacks like phishing, brute-force attacks, and credential stuffing.
- Attacks can be used to steal user credentials and gain unauthorized access to sensitive information.
| Modern Authentication | Legacy Authentication |
|---|---|
| An Additional layer of security through the use of advanced security mechanisms like MFA | Weak security and limited encryption |
| Greater flexibility allows users to securely access their digital assets from various devices, platforms, and applications. | Limited flexibility with poor support |
| User-friendly and provide a seamless user experience | Poor user experience |
| Modern Authentication is used in cloud-based environments, such as Software as a Service (SaaS) applications, web-based applications, and cloud storage services. | Used in older systems and applications and does not support modern authentication protocols |
| Protocols such as OAuth 2.0, FIDO (Fast Identity Online), OpenID Connect, Security Assertion Markup Language (SAML) | Protocols such as NT LAN Manager (NTLM), Kerberos, Basic Authentication, and Digest Authentication |
Reference Site – Modernizing Authentication Management – Microsoft Community Hub
Author
About Author – Vidya is a computer enthusiast. She is here to share quick tips and tricks with Windows 11 or Windows 10 users. She loves writing on Windows 11 and related technologies. She is also keen to find solutions and write about day-to-day tech problems.