In this post, We will go through the topic of direct enrollment for macOS devices using Intune, reviewing briefly each step need to perform for the enrollment profile push. Also, as you know, we have covered the macOS BYOD enrollment method.
Our last blog post discussed managing macOS Login Background App using Intune. As we have observed in the last post, what is login and background item, and how to configure a policy with the help of Intune for macOS?
Also, as we discussed in our previous posts, the latest Microsoft Intune release 2211 supports 6 platforms such as Windows, iPadOS/iOS, macOS, Android, ChromeOS, and Linux OS. Let’s review each enrollment step available by Microsoft to set up macOS enrollment for company-owned and BYOD (Bring Your Own Devices).
As both company-owned (Corporate) and BYOD (Personal) setup devices can be managed in MDM (mobile device management) Microsoft Intune. However, a few prerequisites need to be met before the setup of the device enrollment process, as discussed below.
Enable Enrollment in Microsoft Intune
To enroll the MacBook enrollment to Intune, we should first complete the below steps :
| No. of Steps | Enable enrollment in Intune | Description |
|---|---|---|
| 1 | Verify that devices are eligible for Apple device enrollment | Eligible for macOS v10.9 or later |
| 2 | Configure domains | Make sure to have the organization domain configured/exists |
| 3 | Set the MDM Authority | Choose the MDM authority, e.g. Intune standalone, Co-management(JAMF+Intune). |
| 4 | Get an Apple MDM push certificate | Download and configure the trust relationship certificate from the Apple Push Certificates Portal. |
| 5 | Assign user licenses to the Microsoft 365 admin center | Make sure to have the required licenses to use Intune |
| 6 | Create groups | Create security and M365 groups to manage license and access |
| 7 | Configure the Company Portal app | Configure the company portal app as per the organisation standards |
Types of Enrollment Methods
After we enable enrollment in Intune, let’s discuss the types of enrollment methods
- Company-Owned (Corporate)
- User-Owned (BYOD)
Company Owned macOS Device Enrollment
As discussed in the enrollment methods, In Intune, Company owned macOS enrollment methods are further divided into 3 sub-categories :
- Apple Automated Device Enrollment – In this method, we can automate the enrollment experience of company purchased macOS devices through Apple Business Manager or Apple School Manager.
- Device enrollment manager (DEM) – In this method, particularly for large-scale deployments, IT Admins with device enrollment manager permissions can enroll up to 1,000 devices with single Azure AD account.
- Direct enrollment (discussed below in the blog)
Direct Enrollment
This method is only used for Company-Owned or corporate devices, It doesn’t need the device to be wiped out, however, it needs the user’s intervention while enrolling the device. This method only applies settings on the OS platform set by IT Admins as per company restrictions, policy settings, and standards in the Microsoft Endpoint manager Admin Center.
Prerequisites for Direct Enrollment
To enroll your macOS device, you will need to meet the following prerequisites:
- IT Admin/User needs to enroll the macOS device physically
- Set MDM authority
On Microsoft Intune release 1911 service release or later, MDM authority is by-default set to Intune.
- Apple MDM push certificate
- IT Admin/User must have Administrative privileges on the mac
Create an Apple Configurator Profile for Devices
As said earlier, this enrollment profile only applies the macOS settings during enrollment. To create the enrollment profile, let’s follow the process with Apple Configurator.
In the Microsoft Endpoint Manager admin center, choose Devices > Enroll devices.
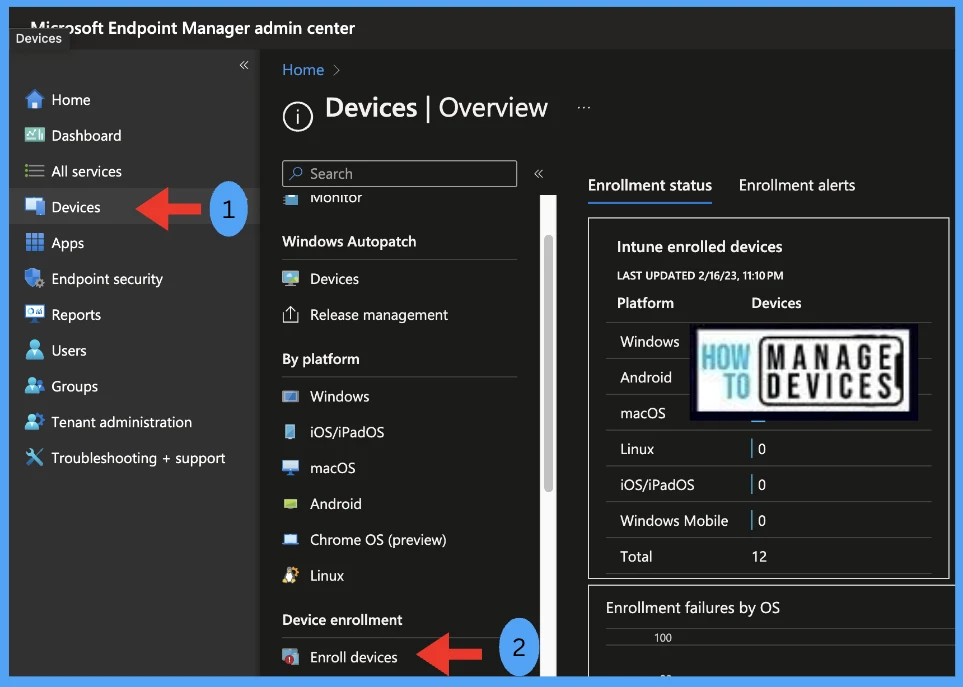
A device enrollment profile defines the settings applied during enrollment. These settings are applied only once. Select Apple enrollment > Apple Configurator.
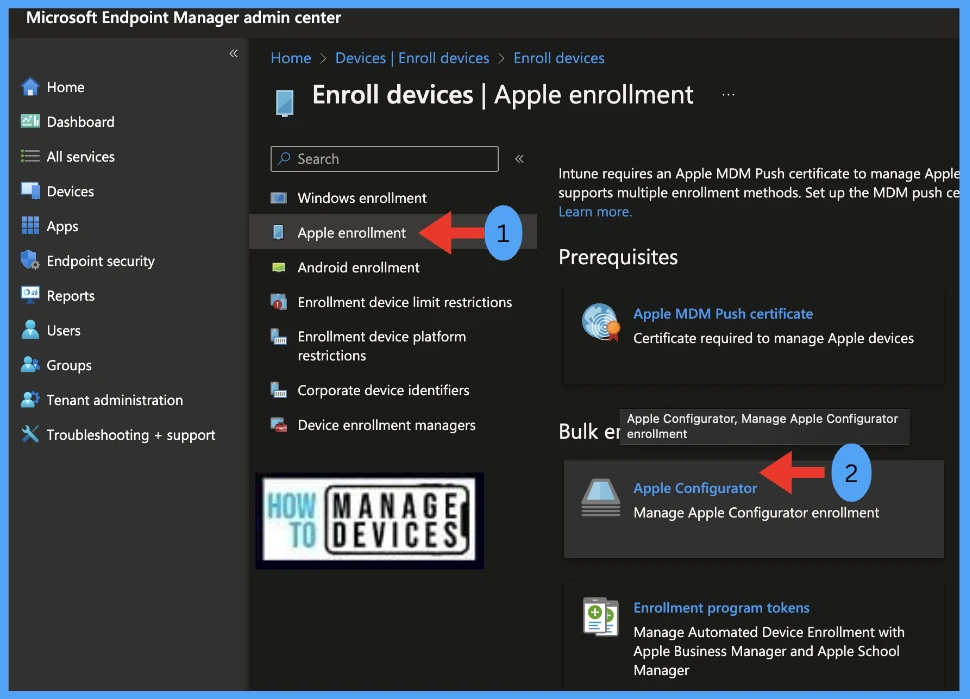
To enroll iOS devices through Apple Configurator, create an enrollment profile by choosing Profiles > Create.

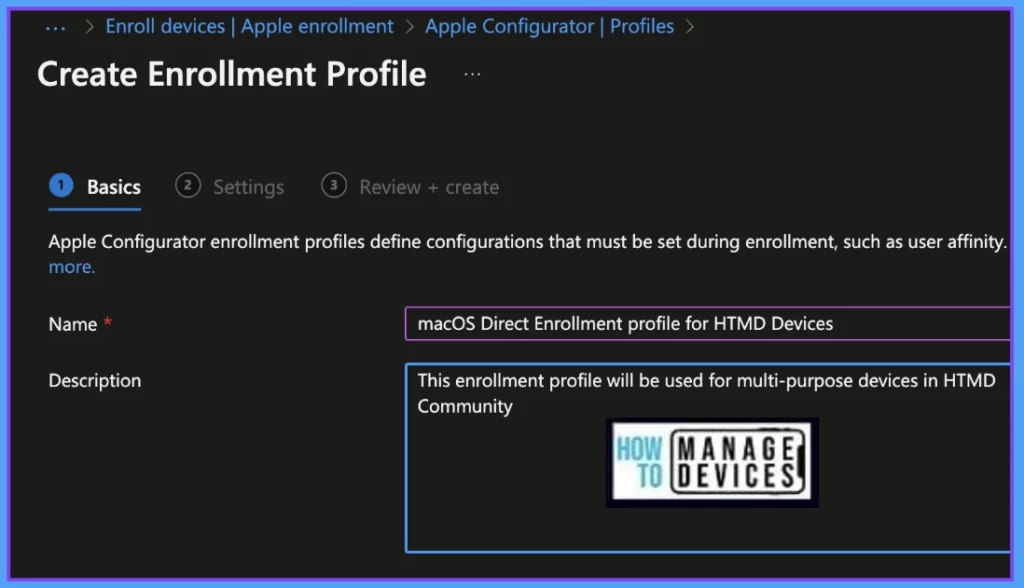
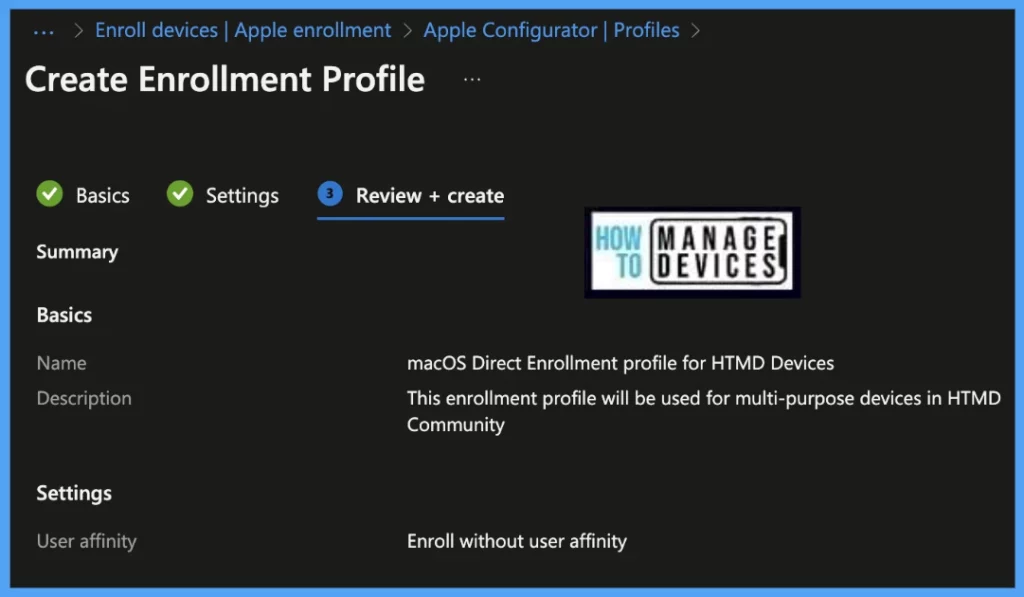
Under Create Enrollment Profile, in the Basics tab, type a Name and Description for the profile for administrative purposes.
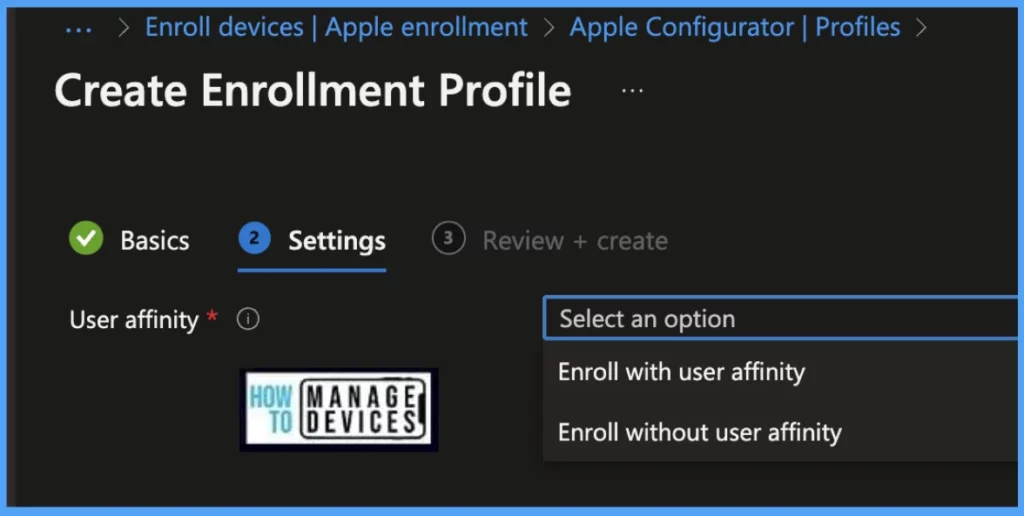
For User Affinity, choose Enroll without User Affinity
Select Enroll with User Affinity for devices that perform tasks without accessing local user data ( used for particular Users) (E.g. 1 user – 1 device).
Select Enroll without User Affinity for devices that don’t need company portal or will be used by multiple users in the organization. (E.g., kiosk, POS devices, or shared utilities)
Here you can review the added details for the enrollment profile and Select Create to save the profile.
As Direct Enrollment only supports enrollment without user affinity, the company portal cannot be used for application installation on the device.
Export the Profile and Install on macOS Devices
To export the profile and install it on macOS devices, follow these steps:
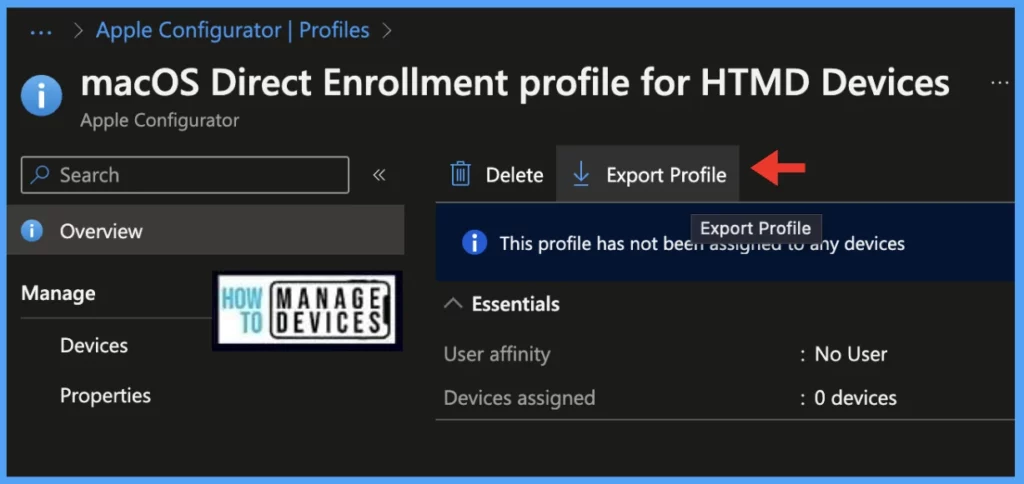
- In the Microsoft Endpoint Manager admin center, go to Devices > Enroll devices.
- Select Apple enrollment > Apple Configurator > Profiles.
- Select the profile you want to export, and then select Export Profile.
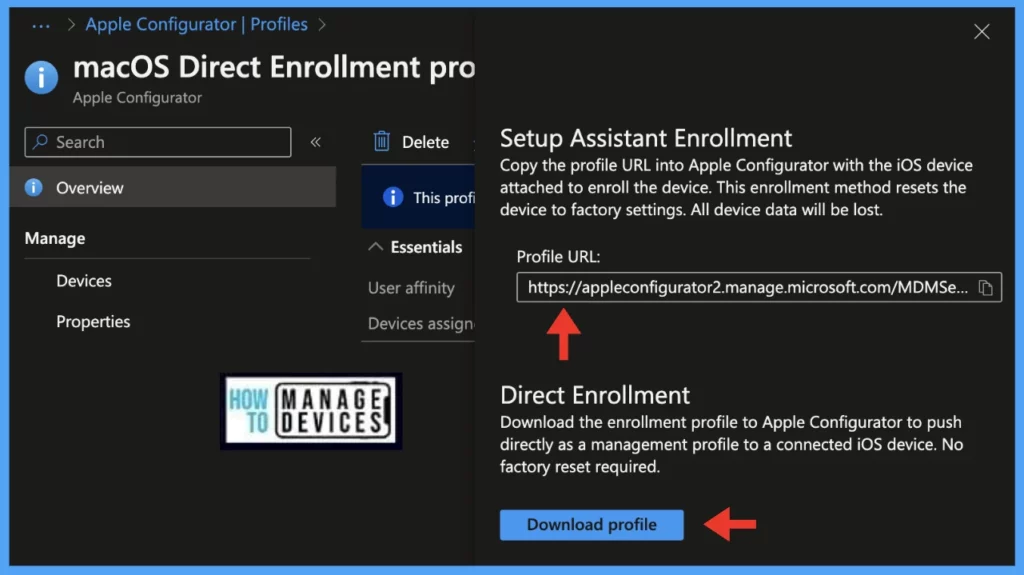
Under Direct enrollment, choose Download profile, and then save the file on the macOS device.
On the mac, double-click on the downloaded .mobileconfig to execute. When prompted to install the management profile, select Install.
Confirm on the next prompt you want to install the management profile by selecting Install.
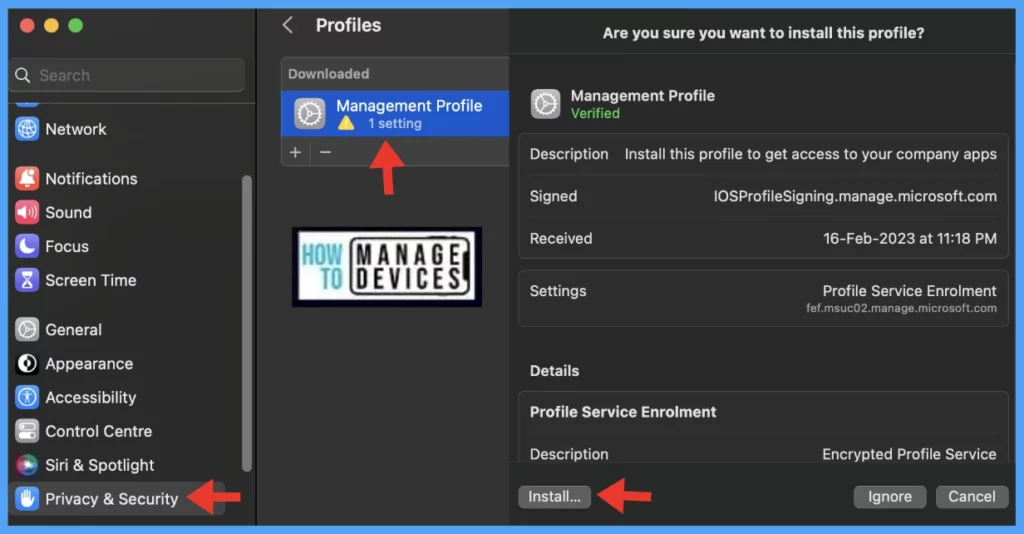
Sign in with an admin account on the macOS device, then select Enrol.
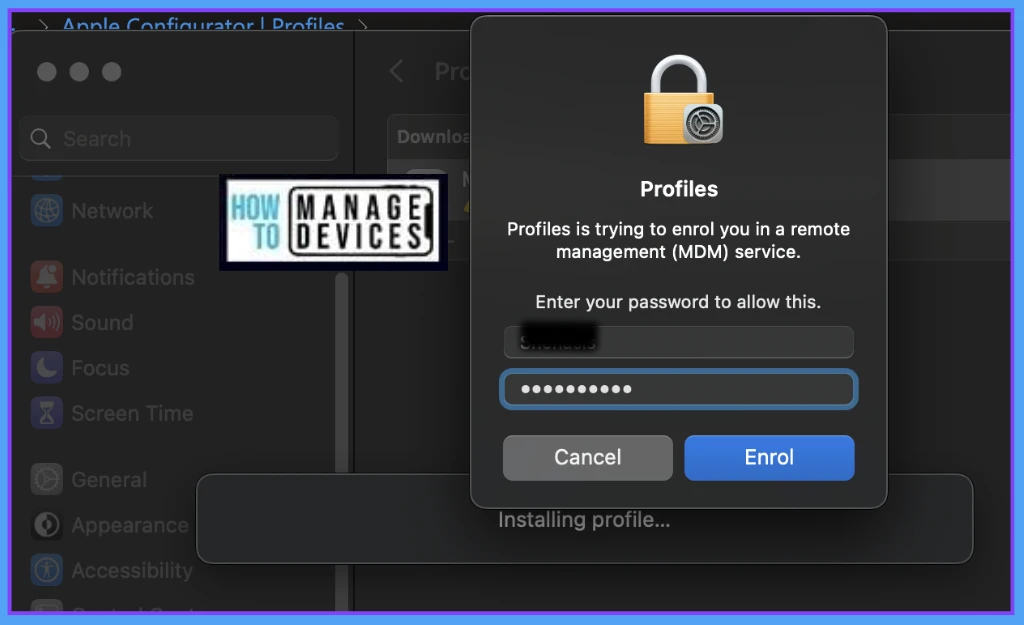
The macOS device is now enrolled in Intune and ready to manage. To verify the device is enrolled, we can check by the below steps.
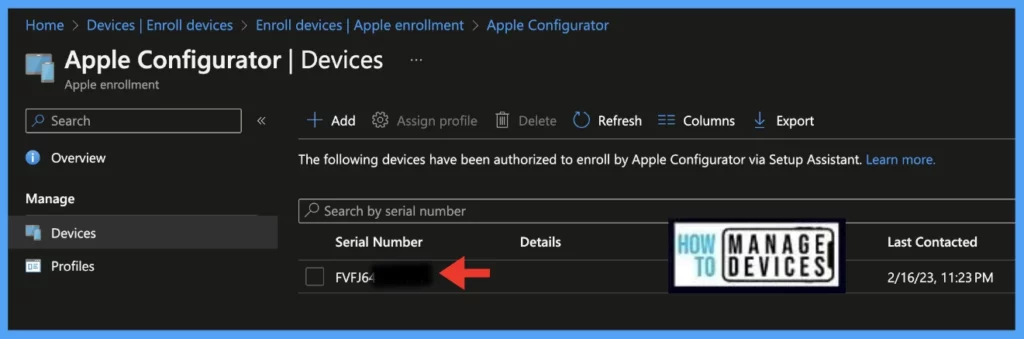
- In the Microsoft Endpoint Manager admin center, go to Devices > Enroll devices.
- Select Apple enrollment > Apple Configurator > Profiles.
- Select the profile > Click on Devices.
Conclusion
As we know, organizations use kiosk devices, or multi user devices which can use Direct enrollment method to get managed by Intune MDM Platform. Once the device is enrolled, through intune compliance policies and configuration profiles can be pushed by IT Admins to secure and protect the device inside organisation.
Author
Snehasis Pani is currently working as a JAMF Admin. He loves to help the community by sharing his knowledge on Apple Mac Devices Support. He is an M.Tech graduate in System Engineering.


