Hey guys, welcome to the HTMD Community. In today’s article, let’s see how to Enforce Users to Enroll Devices with Intune Conditional Access Policies. In one of our posts, we discussed enforcing Multifactor Authentication to protect data. Similarly, forcing users to enroll their devices to Intune to access Corporate Data is very important.
Conditional access policies are part of Microsoft Entra. These policies can be used in conjunction with Intunen to safeguard your data. Conditional Access policies allow users to access corporate on any device if the user or device satisfies the Conditions configured.
In simple words, Conditional Access policies are If-then rules configured to allow access to corporate data or block access to corporate data. These policies can be used to apply the right access controls when needed to keep your organization secure.
Conditional Access policies can be configured based on the state of Devices, Users, Applications, IP location and Real-time and calculated risk detection. We can Block access if the condition is satisfied or Grant access to data per your organization’s requirements.
- Easiest Method to Enable MFA for Admins using Azure AD Conditional Access
- Enrolment Guide for Enrolling Android Devices to Corporate Owned Business Only in Intune
Create Conditional Access Policy
In the conditional access policy, we have the option to allow users to access data only if the device is Compliant. We will be using this condition to Grant access to corporate. This policy will be applied to Entra Enterprise apps. For our discussion, we will be using Office 365 apps. Let’s begin creating a Conditional access policy.
- Login to Microsoft Entra Admin Center with an admin account that has required permissions.
- Click on Protection on the right side menu, Click on Conditional Access.
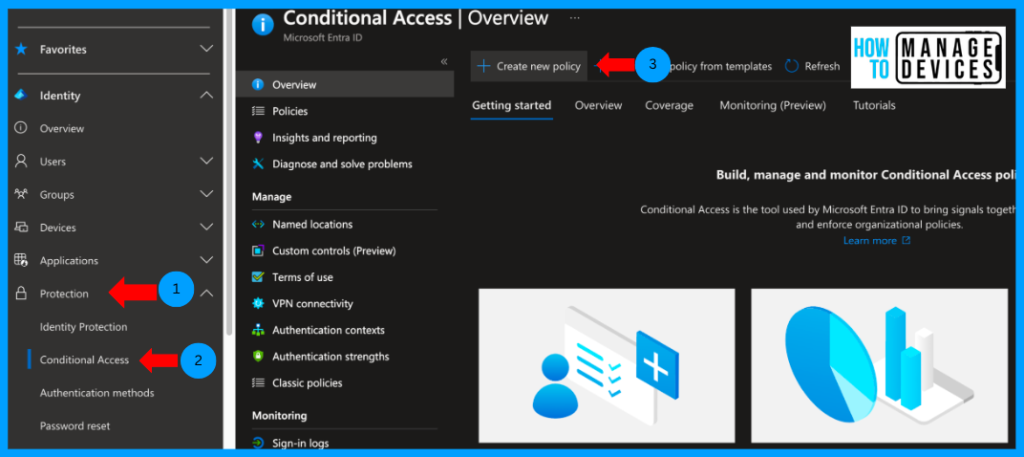
Now click on Create New Policy on the Overview page. Now provide a name to the Conditional access policy and click on the Users and groups to which the policy should be assigned. Here, we can assign the policy to all users or certain users and groups.
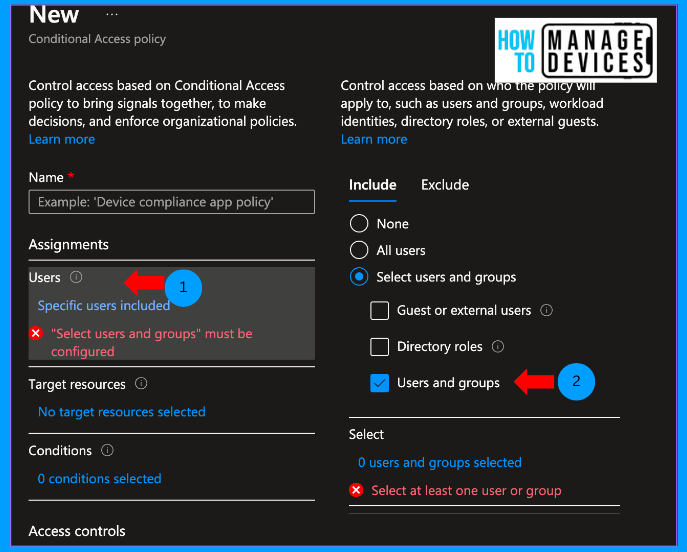
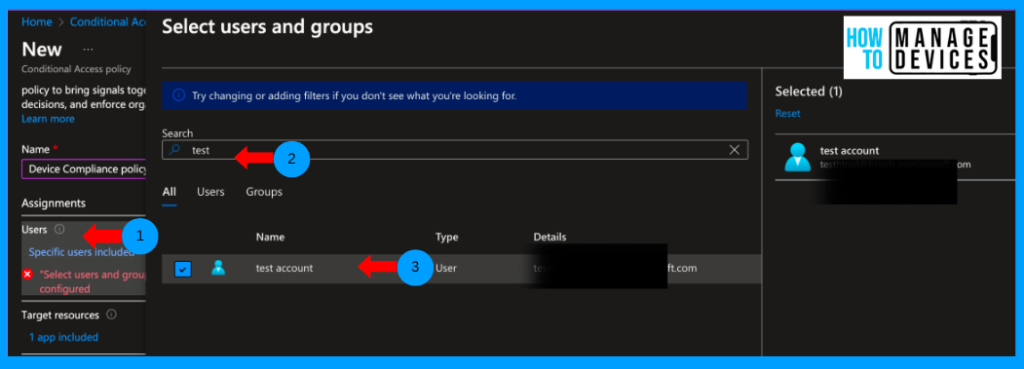
I have chosen Users and Groups. Now search for the user or group, select the group and click on Select. Now, we must select the application to which the Conditional Access policy should be assigned.
Click on Target resources. Here, we have the option to select Cloud appsCloud apps are apps that are registered in Entra under Enterprise apps), User access, Global Secure Access or Authentication Access. I have chosen Cloud apps for our discussion.
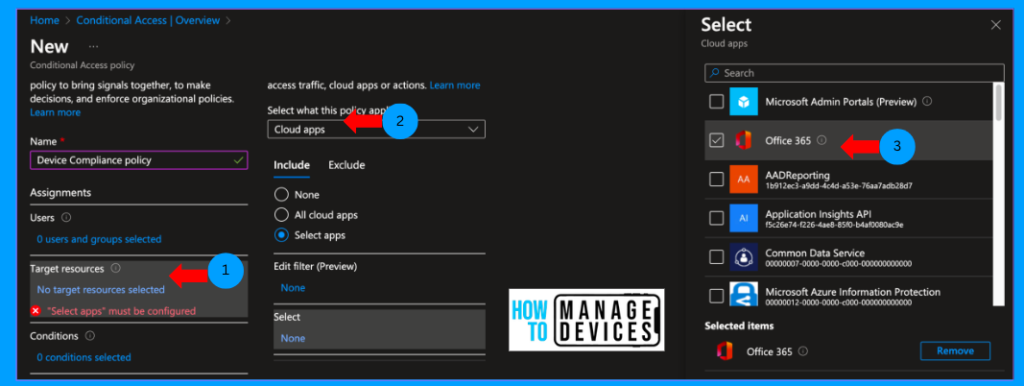
After selecting the Cloud apps, we need to decide whether to apply this Conditional Access Policy to all CLoud apps or a few, as I want to restrict access to only. O365 apps: I have selected “Select apps” and selected the O365 apps.
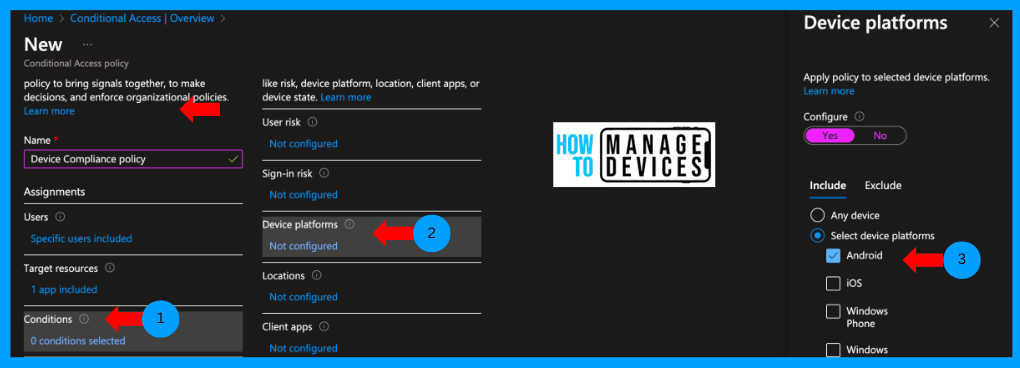
Now click on Conditions. This is the place where you will decide the conditions, and the condition includes Device Platform, Signin risks, User risk, Location etc., etc. I want to restrict access only to Android and iOS, so select Device Platform and choose Android and iOS.
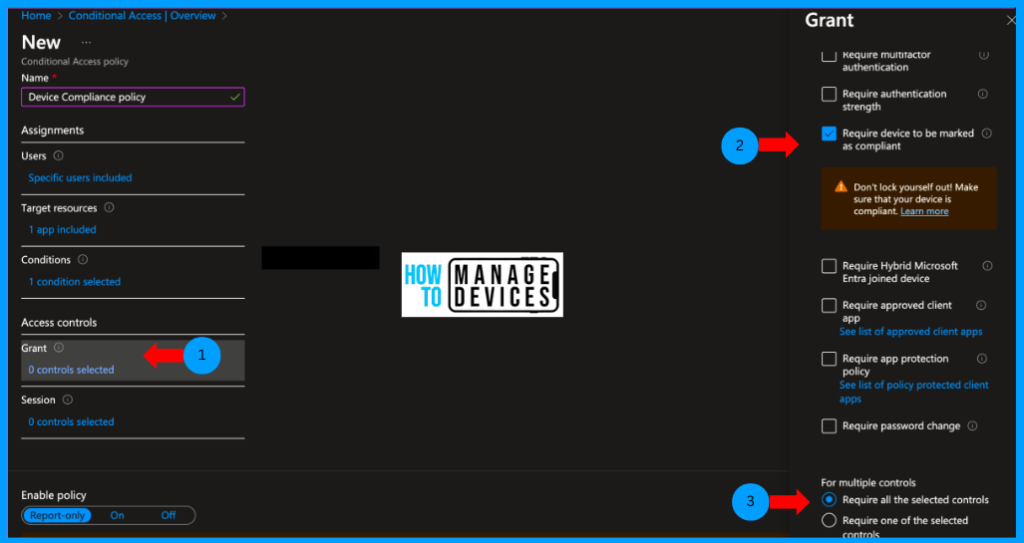
We have configured the conditions, applications and users, and now we need to provide a Grant Control to the apps, i.e., we need to decide whether we need to grant or block the access of the conditions satisfied. Click on Grant, select Grant Access and choose “Require device to be marked as compliant“, as we want to allow access to only Compliant devices.
The device’s compliance can be evaluated only if the device is enrolled on Intune. So, when we assign this policy to users, they will get a message to enrol the device to access the O365 apps. This way, we will force users to enrol the device into Intune.
If you have multiple Grant controls configured, under For multiple controls, select Require all the selected controls to satisfy all the controls configured. Else, select Require one of the selected controls. This will allow or block access even if one of the controls configured satisfies. Now click on click on Select.
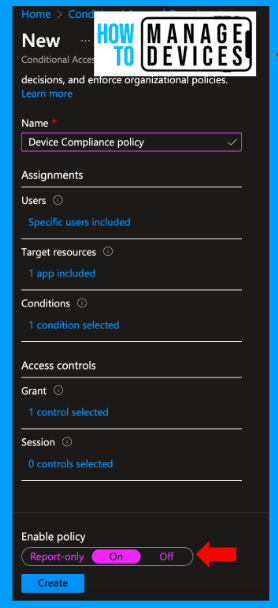
By default, the policy will be read-only. Change that to ON under Enable policy. This will create and apply the Conditional access policy to the targeted users and application. Let’s discuss the User experience.
User Experience – Intune Conditional Access Policies
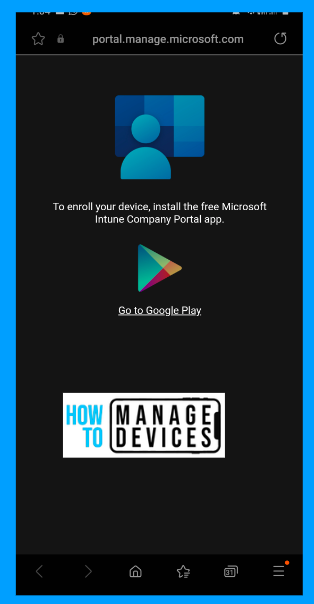
Let’s download any Office 365 apps like Outlook, Word or Excel from PlayStore to check how users are forced to enrol the device. I have downloaded the Outlook app from Playstore. Open the app and sign in with a user account. The user will be prompted with the below message.
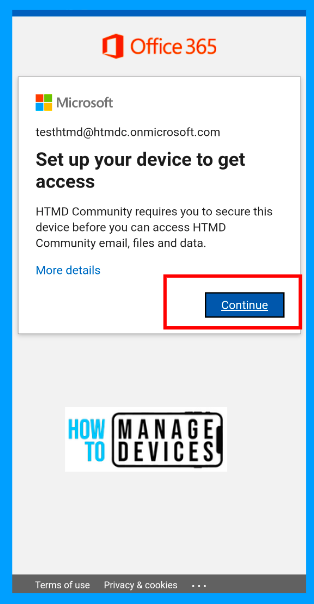
The users are prompted to “Set up your device to get access.” When they click on Continue, they will be redirected to Playstore to download the Company Portal app. Now, users can download the app, enrol the device and configure Outlook.
This is the best way to force users to enrol the devices. While planning the enforcement, as an admin, we should inform users well in advance and publish enrollment guides on enrolling the devices to Intune, so there won’t be much noise regarding the changes.
Monitor User sign-ins
As we have enforced Conditional access policies, sometimes users might be blocked from accessing corporate data. In that case, sign-in logs help us to check where and how users are getting blocked. To view the Sign-in logs, please follow the below steps.
- Login to Microsoft Entra Admin Center
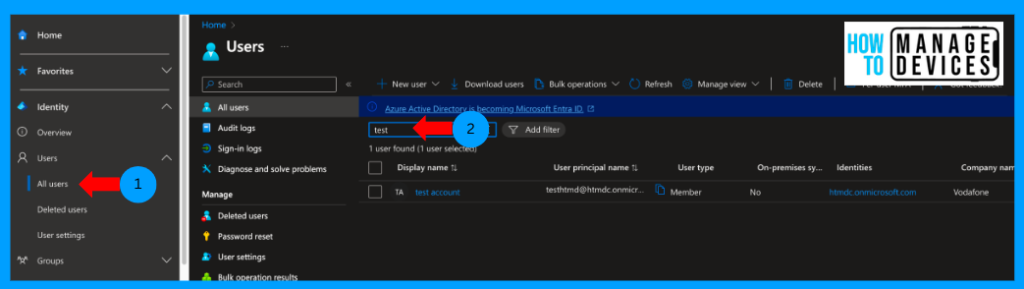
- Click on Users > All users.
- Search for the user, Click on user.
Now click on Sign-in logs. You can view all the sign-in logs for the last 24 hours. We can view for a maximum of 30 days logs. Click on any failure log to view the details.
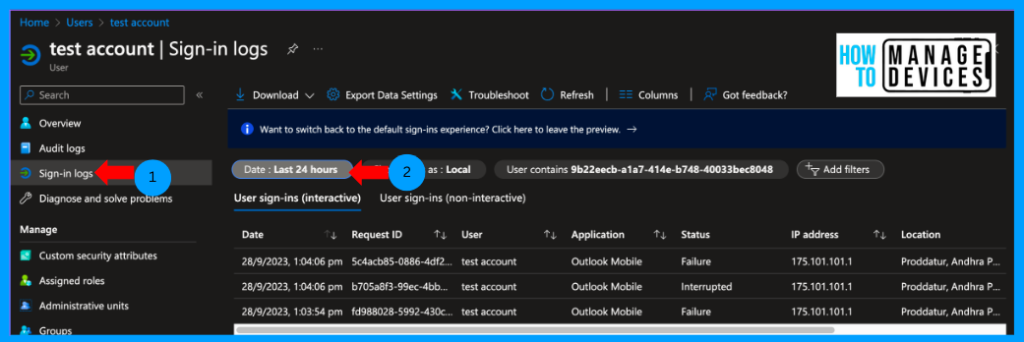
When you click on the log, we can view details of the log and click on Conditional access. This tab will provide details of various Conditional Access policies assigned to users and applied to them.
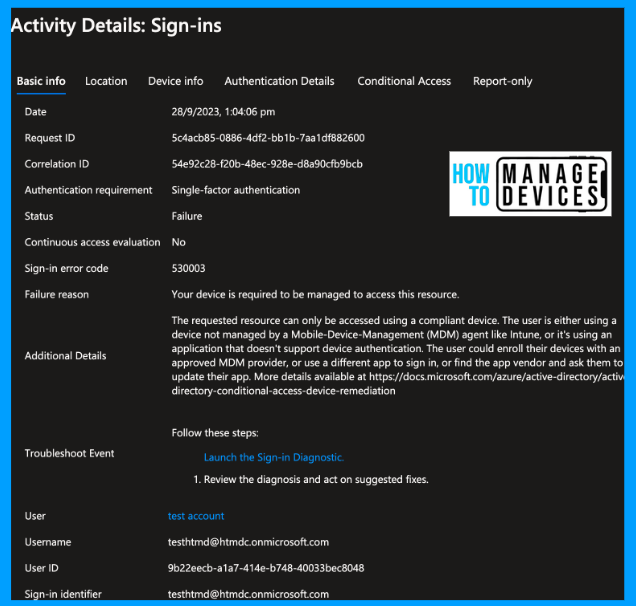
In our case, we can view the test account as blocked due to 2 Conditional access policies, and we can also view the Conditional Access policies.
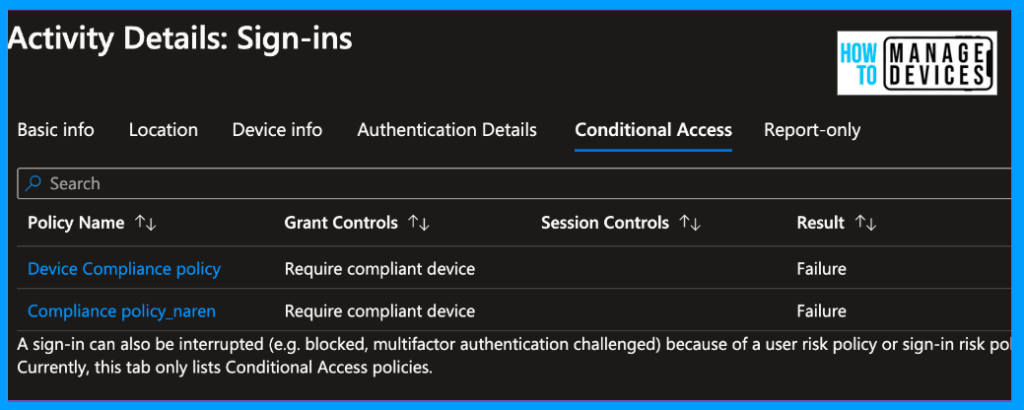
So, in this way, we can view and troubleshoot the user issue if they cannot access corporate data due to Conditional access policies. The policy we created blocks all the non-compliant devices, even if they are enrolled on Intune. Make sure you make the device to be compliant to access the data.
Conclusion
I hope you like the article. This article is helpful if you want to block access to non-compliant devices in Intune and force users to enrol the devices on Intune. We will discuss a new topic in a new post. Till then, have a great day.
Author
About Author – Narendra Kumar Malepati (Naren) has 11+ years of experience in IT, working on different MDM tools. Over the last seven years, Naren has been working on various features of Intune, including migration from different MDMs to Intune. Naren mainly focuses on Android, iOS, and MacOS.



Narendra I would like to inform you that your article is really very helpful for who is working in azure environment and planning for the same. Thanks for the intune article
Thanks a lot Brajesh, this kind of feedback motivates us to create more posts.
Great and simple article. Thank you Narendra
I found the answer I was looking for in your article. Really appreciate your work—keep posting!