Let’s learn how to configure Intune RBAC for Windows drivers policy creation, and deployment management. By creating RBAC Role for Windows Drivers using the step-by-step process, you can assign roles with appropriate permissions, restricting access to sensitive settings and actions.
Configuring Intune Role-Based Access Control (RBAC) for Windows driver management is essential for effective and secure device management in modern organizations. RBAC allows administrators to grant specific permissions to individuals or groups, ensuring that only authorized personnel can create and manage policies for Windows driver updates.
Windows driver and firmware update management policies and reports in Intune allow you to efficiently keep your Windows drivers up to date without needing manual or scripted tasks. This robust RBAC setup ensures smoother operations, reduces the risk of unauthorized changes, and enhances overall security.
You can take a look to examine New Driver & Firmware Servicing Architecture for a better understanding of the flow involved in the updated driver and firmware management process.
Intune provides integrated reports that allow you to view comprehensive status information for Windows driver updates on devices assigned to Windows Driver update policies, By reviewing this detailed report, you can gain insights into the driver update status, Detailed Review Windows Driver Update Report From Intune
- 300 Windows 11 Performance Improvements – Benchmark Report From Microsoft
- Intune Architecture And Sample Architecture Diagram Explained
Intune RBAC Role for Windows Drivers Update Management
To use Windows Driver Update management, you must have privileges for setup policy and configurations for driver update. The following steps will help you to configure RBAC for Intune Driver Management.
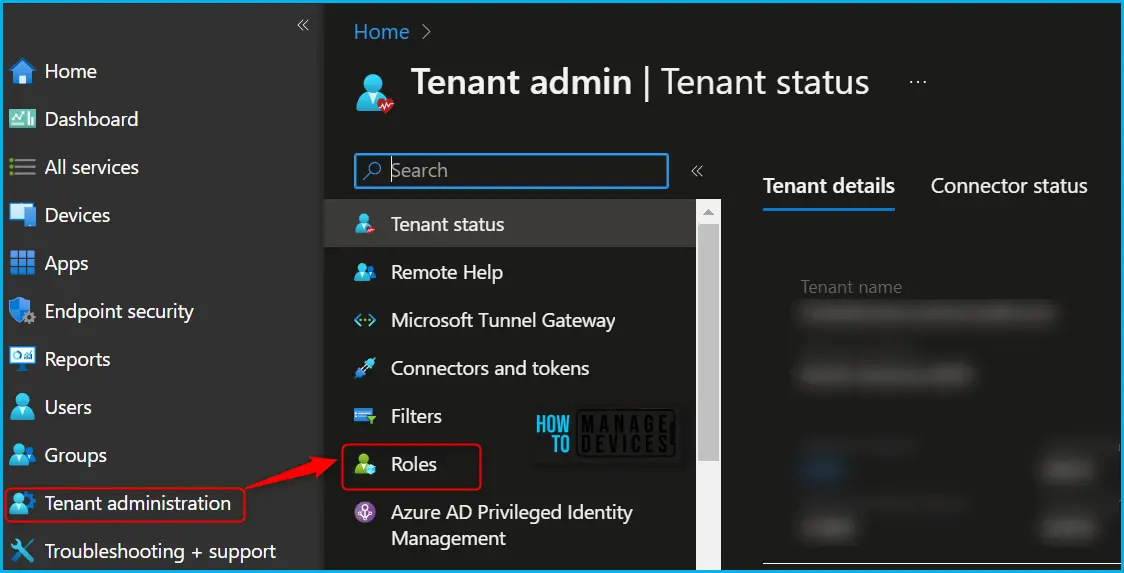
- Sign in to the Microsoft Intune admin center https://intune.microsoft.com/.
- Navigate to Tenant administration > Roles.
In the All roles, you will find all the built-in roles and created custom roles available in the tenant. There is a set of twelve (12) predefined Intune roles available. The Policy and Profile manager built-in role has permission to create or assign device configuration profiles.
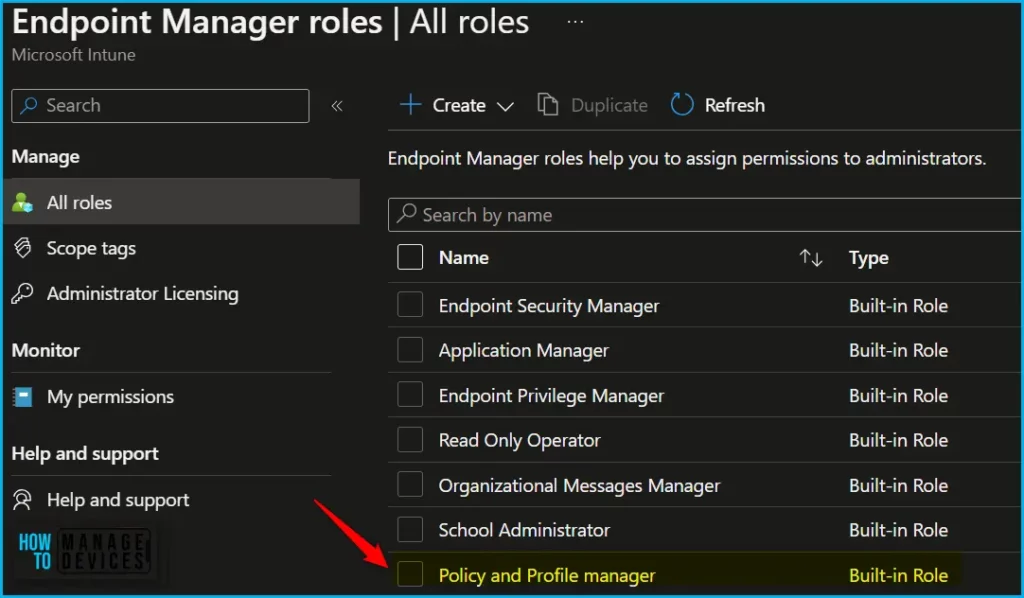
By default, the built-in Policy and Profile manager role sets all of these permissions to Yes. You can use the built-in role or create custom roles to grant permissions only for managing driver updates that you want different groups of users to have.
In Endpoint Manager All roles, Click on Create and select Intune role from the appeared options.
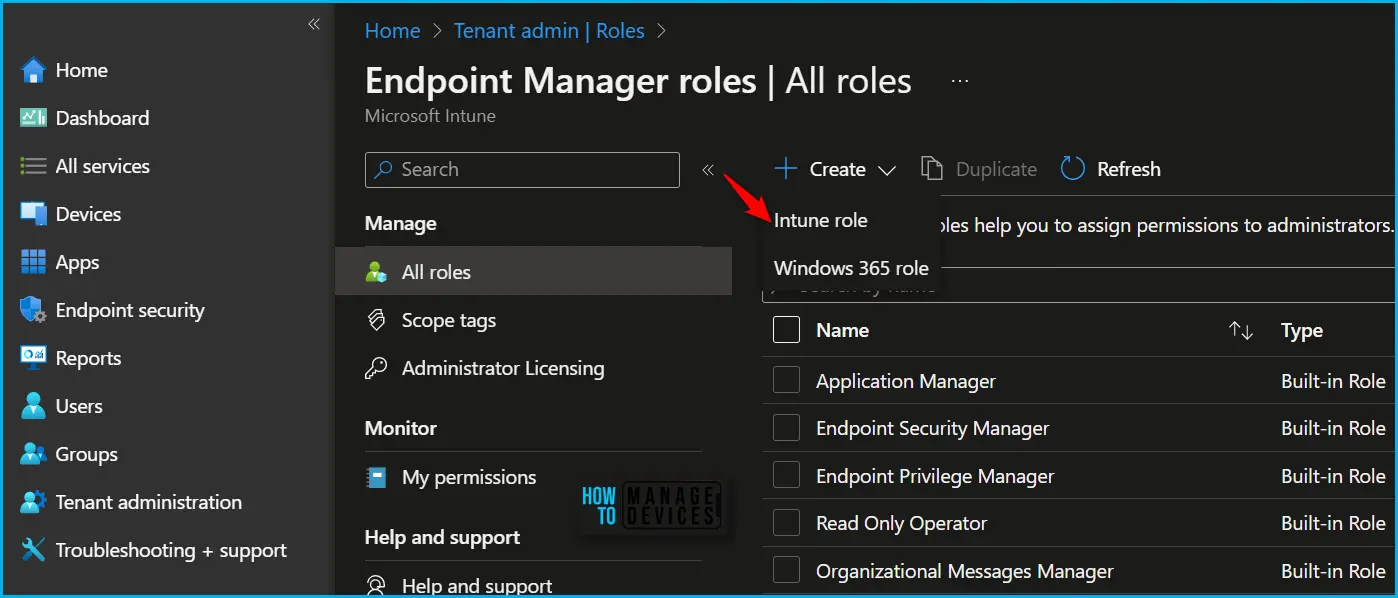
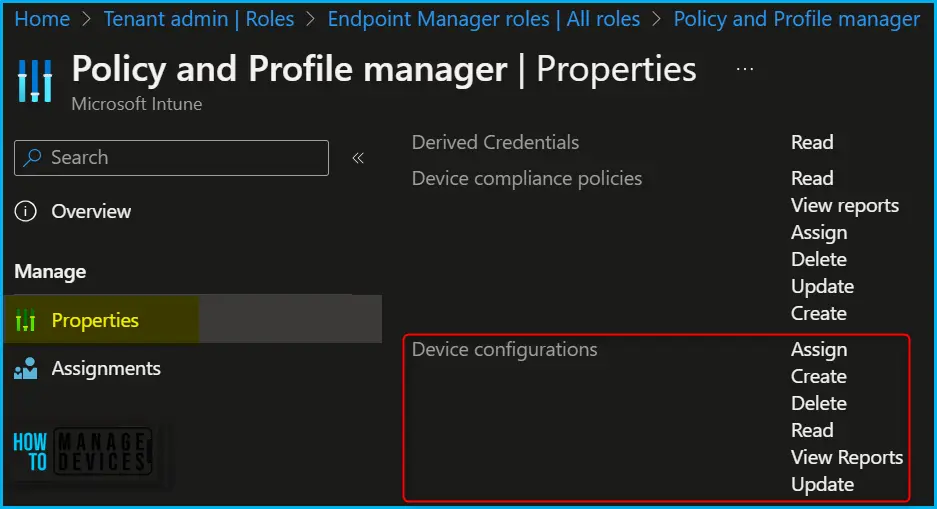
On the Basics page, enter a name and description for the custom role, then choose Next. To modify the roles associated with a particular category, navigate to the “Permissions” page. When creating custom roles, you can enable the relevant permissions by selecting appropriate roles.

To manage Windows Driver updates, your account must be assigned an Intune role-based access control (RBAC) role that includes the following permissions:
| Permission | Configure | Descriptions |
| Assign | Yes | Assign device configuration profiles or assign device enrollment restrictions to Azure AD security groups. |
| Create | Yes | Create new device configuration profiles, or create new device enrollment restrictions. |
| Delete | Yes | Delete device configuration profiles, or delete device enrollment restrictions. |
| Read | Yes | View device configuration profiles, or view device enrollment restrictions. |
| View Reports | Yes | View, generate, and export device configuration reports. |
| Update | Yes | Change device configuration profiles, or change device enrollment restrictions. |
You can duplicate built-in roles to create, edit, or assign Intune roles, and assign a built-in or custom role to an Intune user, choose the created role you want to assign > Assignments > + Assign.
Author
About Author – Jitesh, Microsoft MVP, has over six years of working experience in the IT Industry. He writes and shares his experiences related to Microsoft device management technologies and IT Infrastructure management. His primary focus is Windows 10/11 Deployment solution with Configuration Manager, Microsoft Deployment Toolkit (MDT), and Microsoft Intune.


