This guide helps you to use Intune security baselines to configure Windows devices from Intune MEM Portal. Intune makes it easy to deploy Windows security baselines to help you secure and protect your users and devices.
Security baselines are groups of pre-configured Windows settings that help you apply and enforce granular security settings recommended by the relevant security teams. You can also customize each baseline you deploy to implement only the required settings and values.
You deploy security baselines to groups of users or devices in Intune, and the settings apply to devices that run Windows 10/11. Security baselines can help you to have a secure end-to-end workflow when working with Microsoft 365.
Microsoft Endpoint Manager updates the versions of built-in Security Baselines depending on the changing needs of a typical organization. Each setting in a baseline has a default configuration for that baseline version.
If you’re new to Intune and not sure where to start, Intune Admin Portal is one of the first things you have to learn, and predefined security baselines give you an advantage. You can quickly create and deploy a secure profile, knowing that you’re helping protect your organization’s resources and data.
- Deploy Windows 365 Security Baseline Policies to Cloud PCs
- How To Start Troubleshooting Intune Issues | Fix Intune Issues With Easy Steps MEM
- Intune Security Baseline Microsoft Defender Policy Troubleshooting Tips For Cloud PCs
Intune Security Baselines Policies for Windows 10 or Windows 11
To manage baselines in Intune, your account must have the Policy and Profile Manager built-in role. Let’s see how to create security baseline policies for Windows 10 or 11.
- Sign in to Microsoft Endpoint Manager Admin Center https://endpoint.microsoft.com
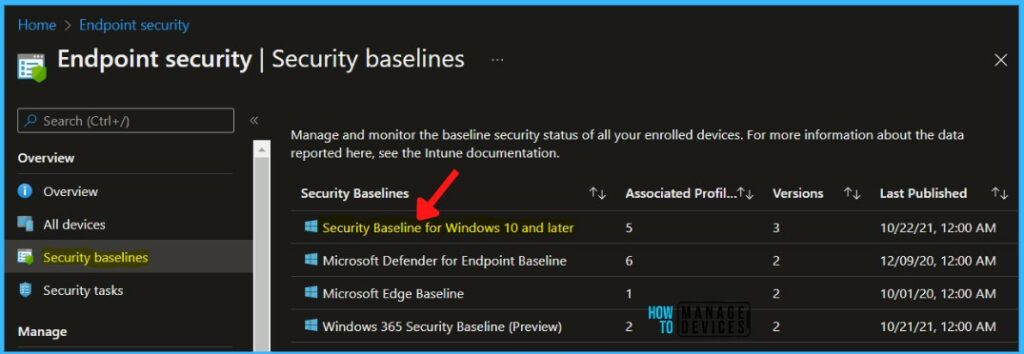
- Navigate to the Endpoint Security node. Click on the Security Baselines node.

Here You can see several other baseline policies in this node, Select the Security Baseline for Windows 10 and later set.
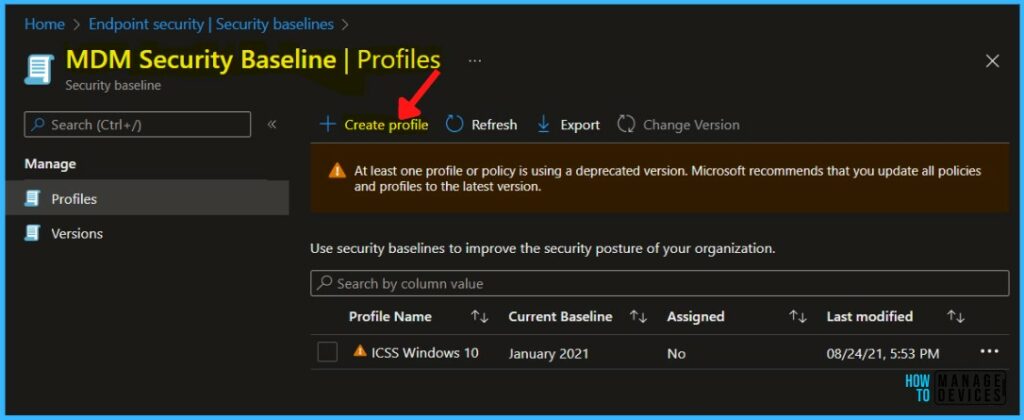
You can now click on + Create Profile to create a Security Baseline for Windows 10 or 11. You can also check the versions of the baseline available. The Supported baseline is November 2021.
When a new baseline version becomes available, it replaces the previous version. Profiles instances that you’ve created prior to the availability of a new version.
You may notice the banner showing the message that At least one profile or policy is using a deprecated version. Microsoft recommends that you update all policies and profiles to the latest version.
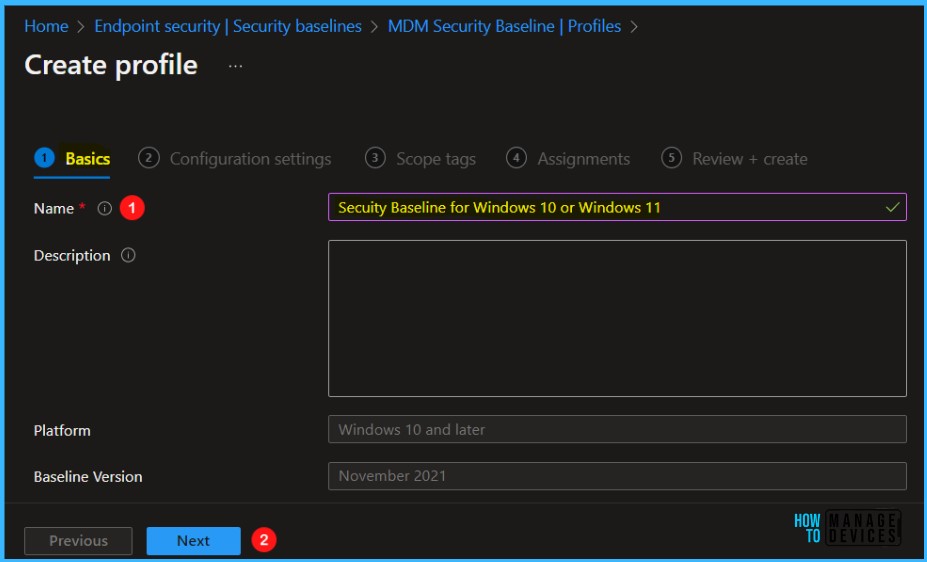
You will have to enter the name and description of the Security Baseline for Windows 10 or 11. The platform and Baseline version are automatically selected. You can click on the Next button to continue.
- Name -> Security Baseline for Windows 10 or Windows 11
- Platform -> Windows 10 and Later
- Baseline Version -> November 2021
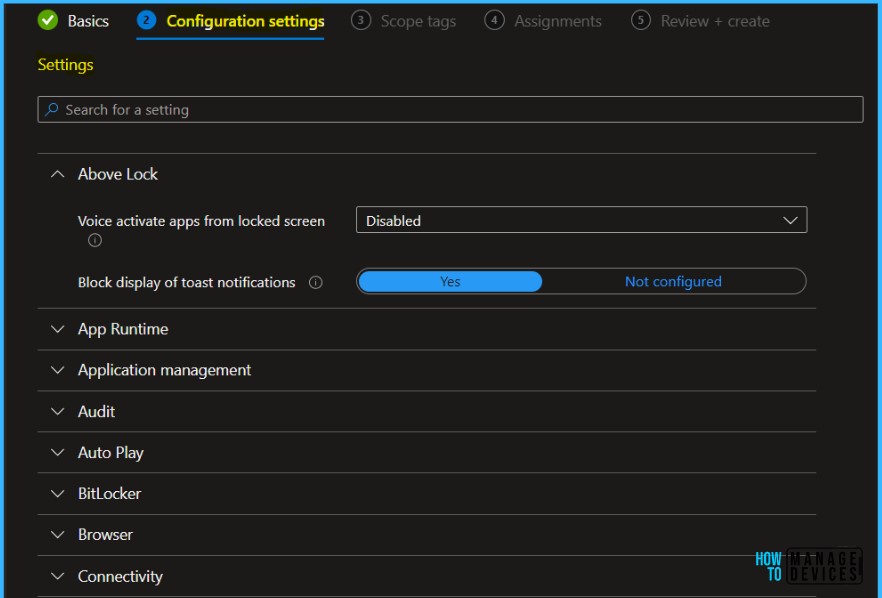
You can get a quick overview of the Windows 10 or Windows 11 security baseline categories with the default values of these tables.
- Select a group to expand and review the available settings.
- Use the search bar and specify keywords that filter the view to display only those groups that contain your search criteria.
Each setting in a baseline has a default configuration for that baseline version. This will help you understand the configurations quickly and adjust them as per your requirements. However, We would recommend using the default security baseline.
| Setting Name | Baseline Default |
| RPC unauthenticated client options | Authenticated |
| Account Logon Audit Credential Validation (Device) | Success and Failure |
| Block user control over installations | Yes |
| Scan incoming email messages | Yes |
| Apply UAC restrictions to local accounts on network logon | Enabled |
| Auto play default auto run behavior | Do not execute |
In Scope tags, you can assign a tag to filter the profile to specific IT groups. Add scope tags (if required) and click Next.
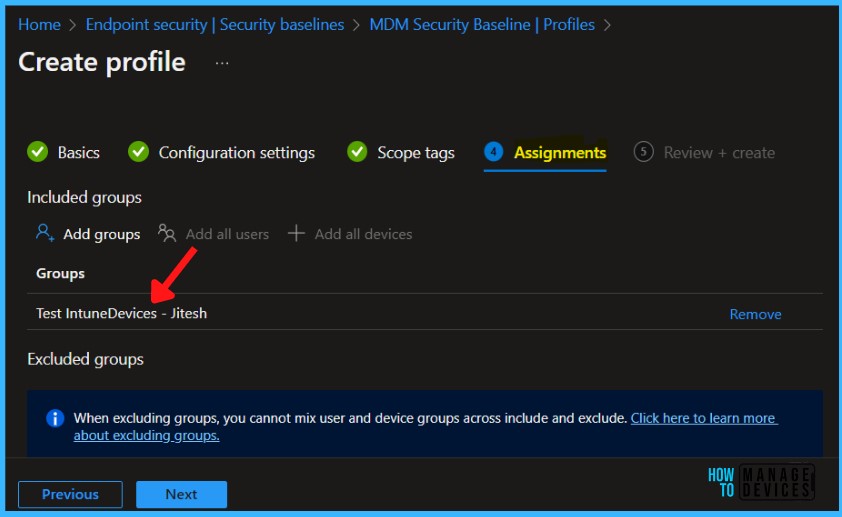
On the Assignments tab, select groups to include and assign the baseline to one or more groups. Use Select groups to exclude to fine-tune the assignment. Select Next to continue.
When you’re ready to deploy the baseline, advance to the Review + create tab and review the details for the baseline. Select Create to save and deploy the profile.

A notification will appear automatically in the top right-hand corner with a message. You can see the message “Profile created successfully”. Once you create the profile, it’s pushed to the assigned group and might apply immediately.

Monitor Intune Security Baselines and Profiles
Intune provides several options to monitor security baselines. You can:
- Monitor a security baseline, and any devices that match (or don’t match) the recommended values.
- Monitor the security baseline profile that applies to your users and devices.
- View how the settings from a selected profile are set on a selected device.
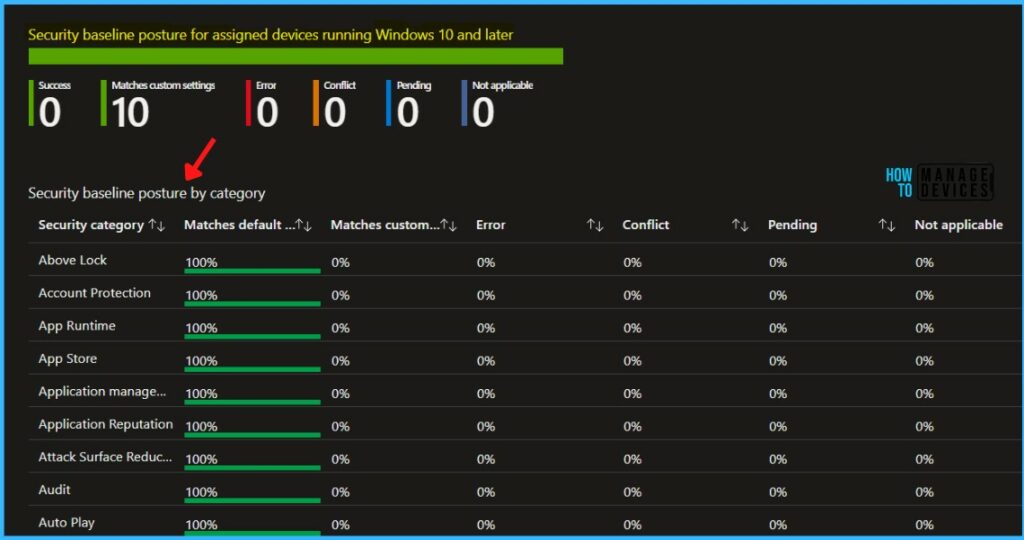
You can also view the Device configuration report to see which device configuration based policies apply to individual devices, which include security baselines.
Monitoring the profile gives insight into the deployment state of your devices, but not the security state based on the baseline recommendations.
- In Intune, select Endpoint security > Security baselines, and select a security baseline type like the MDM Security Baseline > MDM Security Baseline for Windows 10 and later for November 2021 > Properties.
- In the Properties of the baseline, expand Settings to drill in and view all the settings categories and individual settings in the baseline, including their configuration for this instance of the baseline.
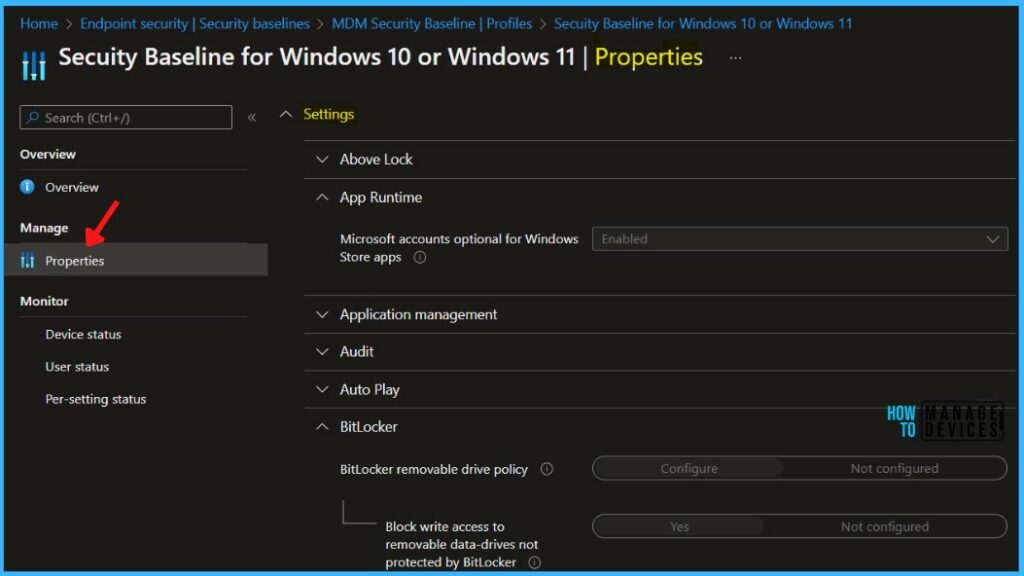
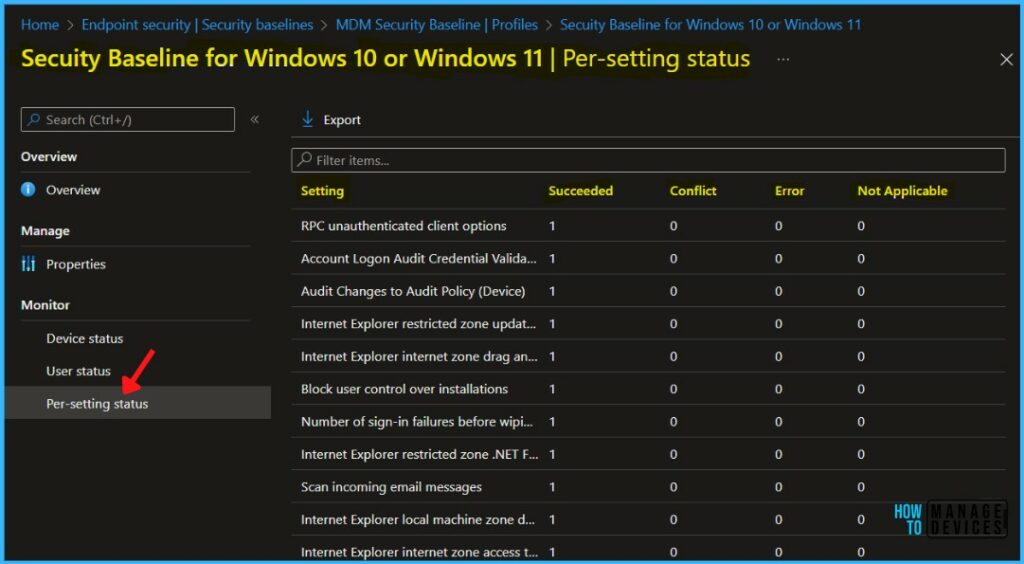
Use the options for Monitor to view the deployment status of the profile on individual devices, the status for each user, and the status of the settings from the instance of the baseline.
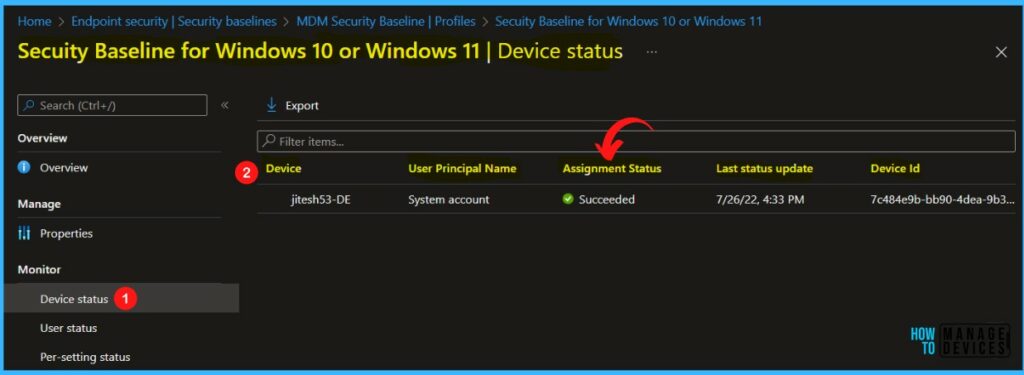
Click on the Per setting status policy report, and This report shows the security baseline status of each setting for the policy across all devices and users.
| Setting Name | Baseline Default |
| Block display of toast notifications | Yes |
| Turn on Windows SmartScreen | Yes |
| Block Automatically connecting to Wi-Fi hotspots | Yes |
| PowerShell script block logging | Enabled |
| Scan removable drives during a full scan | Yes |
| Block app installations with elevated privileges | Yes |


