Let’s learn How to Secure Windows 10 Devices in a Modern Sophisticated Way Device Management SCCM. A few years ago, a Windows machine was protected only by antivirus software with malware/spyware protection. This world is changing now, and cyber attacks are getting more sophisticated.
I don’t believe that only antivirus and malware/spyware solutions can help us protect corporate devices. As you know, Windows 10 is redefining how we think about security. With TPM and UEFI, hardware can plug some of the holes attackers use to compromise systems.
Secure Windows 10 Devices – Of course, these capabilities are just part of a sophisticated solution that involves countless security enhancements to Windows 10 itself, such as improved identity and access control, cloud security integration, and containerization. Windows 10 delivers an unprecedented suite of capabilities to the enterprise.
Now, it’s up to you as IT systems administrators to use these new features correctly and help keep your company safe. To that end, Microsoft TechNet has an excellent overview here. Adaptiva has provided some background and how-to information in their recent Top 5 Security Best Practices for Windows 10 in the Enterprise report.
Table of Contents
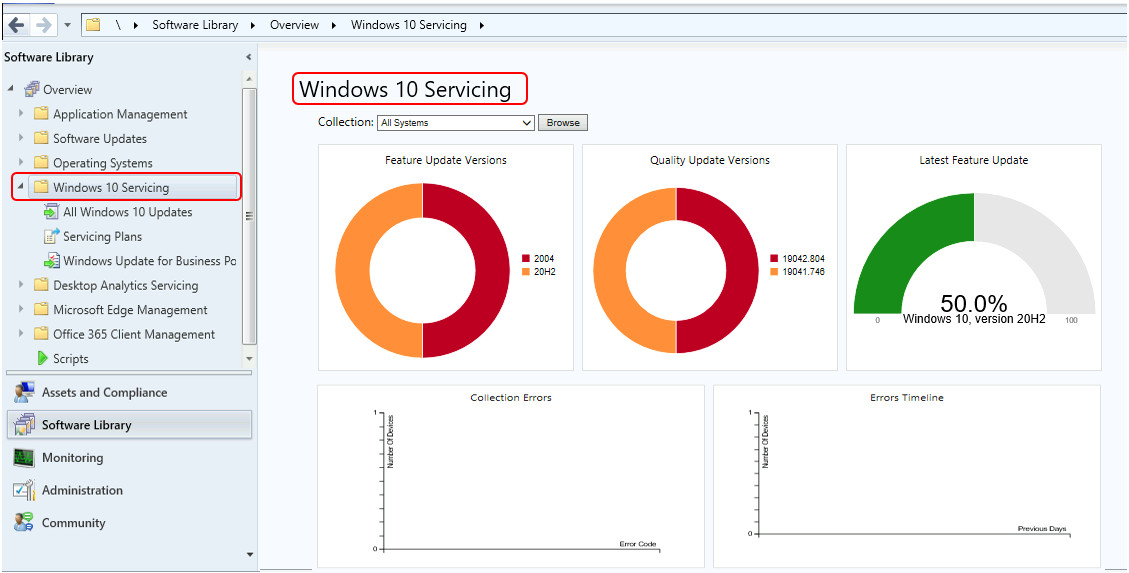
- What’s New In SCCM Windows 10 Servicing Dashboard | ConfigMgr
- SCCM Windows 10 OSD Best Practices with ConfigMgr
- How to Create SCCM Windows 10 Upgrade Task Sequence Configuration Manager ConfigMgr
- Upgrade Windows 10 21H2 using SCCM Task Sequence | Best Guide
- Deploy Windows 10 Feature Update Using SCCM Task Sequence | ConfigMgr
- Windows 10 21H1 Upgrade Using SCCM Task Sequence | ConfigMgr | Best Guide
- Windows Upgrade Troubleshooting Logs
- Windows 10 Upgrade Using SCCM Task Sequence
Learn How to Secure Windows 10 Devices in a Modern Sophisticated Way Device Management SCCM
Most of the topics covered below can be easily implemented using modern management methods, such as OMA-URI via Intune/SCCM. The report covers some of these topics.
Windows Information Protection
Want to keep your company’s confidential product roadmap from being sent from an employee’s private email or placed in their personal Dropbox account? Microsoft is solving that challenge through containerization with WIP. One of my blog posts explains how to create WIP/EDP policies via Intune and SCCM.
BitLocker
Imagine a future where part of your encryption key is stored in a system’s hardware and another in the software. If you run a TPM chip with BitLocker, that future is a reality today.
It makes life easier for users because they get this extra level of security while only entering their Windows login, not a separate encryption key. But it makes life hard for attackers, who would need both the hardware and software keys (or an extremely long recovery key) to break in.
UEFI with Secure Boot
UEFI changes everything because it enables secure boot. When your OS loads, it has to be trusted by the PC manufacturer, or it won’t run. The same goes for drivers and more—if they are not trusted, they don’t run. This makes life a lot harder for people looking to compromise your OS.
Credential Guard
We’ve all heard of “pass the hash” attacks, where security credentials are snagged and used for unfriendly purposes. Credential Guard helps prevent these and some other attacks.
Of course, securing the boot process, credentials, and hard disk is not enough. If one application is replaced with an imposter or contains malware or IS malware, a hacker has the keys to your enterprise’s front door. Device Guard prevents unauthorized applications from running.
| Vulnerability is not An Option |
|---|
| Suppose you are up to speed on and implementing all these technologies correctly; great! If not, you should invest some time to download the guides and reports out there and get up to speed on your security options with Windows 10 today. |
We are on WhatsApp now. To get the latest step-by-step guides, news, and updates, Join our Channel. Click here. HTMD WhatsApp.
Author
Anoop C Nair is Microsoft MVP! He is a Device Management Admin with more than 20 years of experience (calculation done in 2021) in IT. He is a Blogger, Speaker, and Local User Group HTMD Community leader. His main focus is on Device Management technologies like SCCM 2012, Current Branch, and Intune. He writes about ConfigMgr, Windows 11, Windows 10, Azure AD, Microsoft Intune, Windows 365, AVD, etc.
