Let’s try to check how to troubleshoot Microsoft Edge security policy deployment issues with Intune. In the previous blog post, I have already shared the options to deploy Windows 365 Security Baseline Policies to Cloud PCs. Microsoft Edge security policies are also included in the Cloud PC security baseline.
You can perform the basic Microsoft Edge security policy troubleshooting from the MEM admin center portal. One example is given below How To Start Troubleshooting Intune Issues from the server-side. The next level of troubleshooting is with MDM Diagnostics Tool to collect the log and information from the client-side.
You can start client-side troubleshooting from the Work or School account connection available in the settings app. This helps to confirm whether the security policy is received by Windows 10 and Windows 11 PCs. You can go through the list of policies applied from the connection-> Info option.
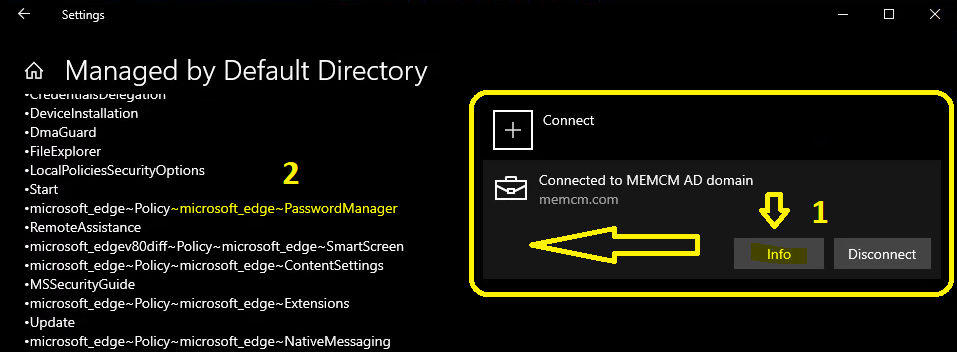
Microsoft Edge Password Manager Policy using Intune
I have deployed the Microsoft Edge password manager policy using Intune security baseline for Cloud PCs. This policy disables the password save and sync option from Microsoft Edge. Now, quickly check these security policy settings from different places.
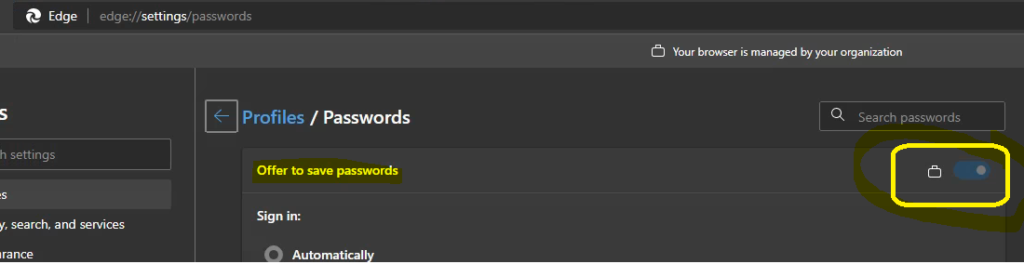
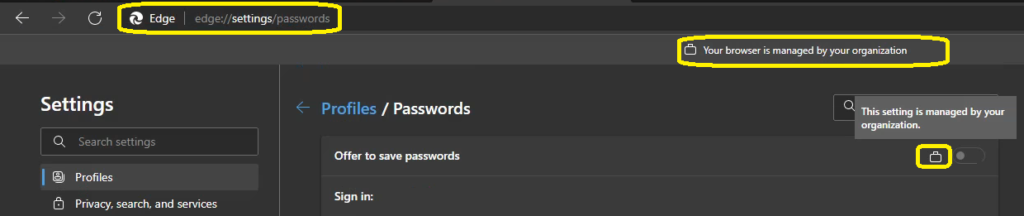
First, you can check the policy from the Edge browser itself by going to three dots and the Settings tab. Otherwise, you can use the following URL to open the Settings -> Password security policies for the browser. You can also notice the message “Your browser is managed by your organization.” Also, the Offer to Save password setting is managed by your organization. This confirms the policy deployed using Intune security policies.
- edge://settings/passwords
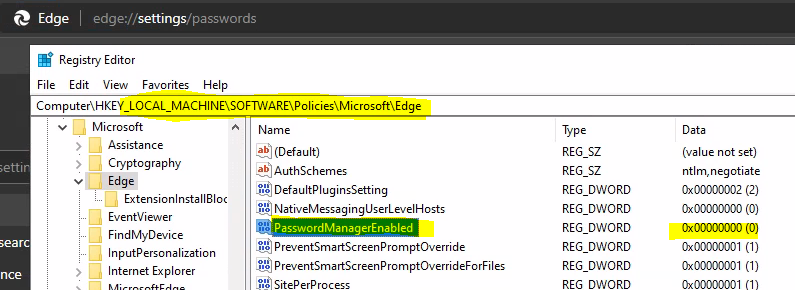
The next step is to go to the registry key for Microsoft Edge browser policy settings and confirm the Password Manager value to ensure this is disabled. Once that is done, you can go ahead and start the simulation exercise for Intune security policy troubleshooting for the Microsoft Edge browser.
- Registry Path for Microsoft Edge Security Policies -> Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Edge
- Regitry Entry and Value for the Key -> PasswordManagerEnabled = 0 (REG_DWORD)
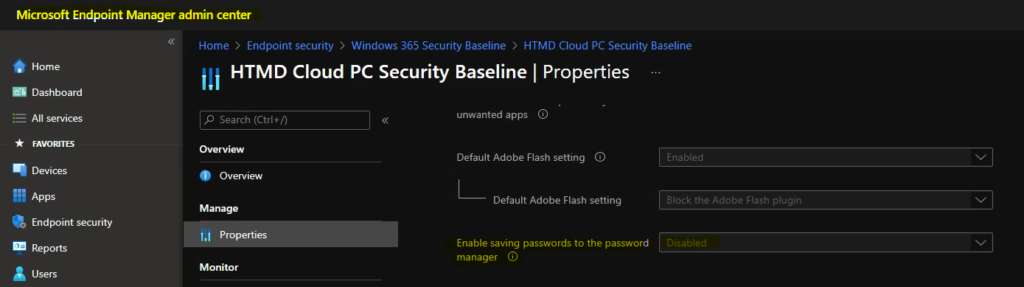
Now, it’s time to check the Intune security baseline policy to confirm the password manager policy. The enable saving passwords to the password manager is disabled by default.
- Enable saving passwords to the password manager -> Disabled
How to Troubleshoot Microsoft Edge Security Policy Deployment using Intune
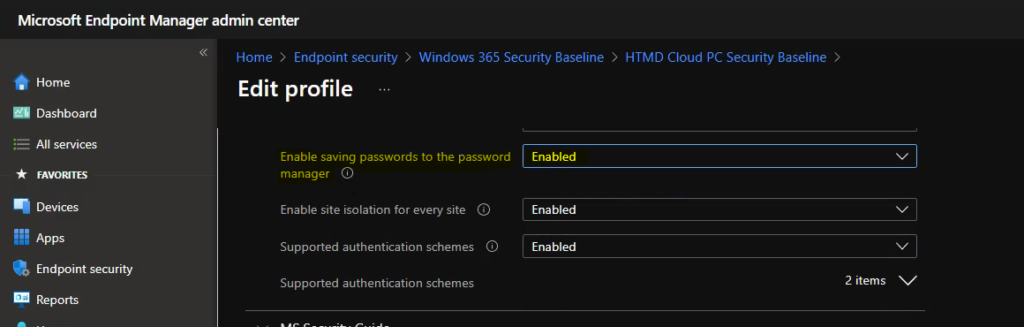
It’s time to change the value of saving passwords to the password manager policy to enable. This change will help us go through the troubleshooting process of Microsoft Edge Security Policy Deployment issues with Intune.
- Navigate to Endpoint Security -> Windows 365 Security Baseline -> HTMD Cloud PC Security Baseline.
- Edit the profile -> Microsoft Edge
- Enable saving passwords to the password manager -> Enabled.
- Click Save button to save the configuration changes.
How to Initiate Intune Policy Sync Immediately
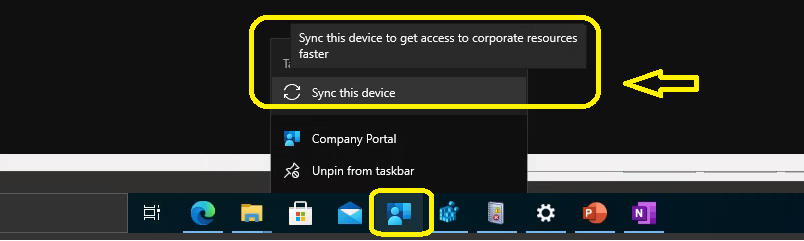
Let’s now verify the Microsoft Edge password manager setting from the Windows PC. The default policy sync period is 8 hours. I don’t think it’s worth waiting for 8 hours in the troubleshooting scenario. You can manually initiate a sync Intune policy sync from Company Portal or Info -> Managed by Default Directory – Areas Managed location mentioned above.
Right-click on the company portal taskbar icon – Sync this device -> Sync this device to get access to corporate resources faster
Check Event Logs to Troubleshoot Microsoft Edge Security Policy Deployment Issue
Once the sync is initiated, you will need to check the Event logs to confirm the policy is reached on Windows 1o or 11 PC. You have many other Intune logs which can be used for Win32 application deployment, etc. But MDM related logs are stored in the event logs mentioned below. The Intune related event logs are available in the following path:
Event Log path for Intune logs –> Applications and Services -> Microsoft->Windows->DeviceManagement-Enterprise-Diagnostics-Provider->Admin
The event ID 208 means the Windows client is contacting Intune Service to check whether there is any new policy or not. The Event ID 814 means receiving a new Intune security policy from the server-side related to Microsoft Edge Password Manager settings.
Event ID 208 -> MDM Session: OMA-DM session started for EnrollmentID (D0892524-8DFC-D50A19DBF) with server: (MS DM Server), Server version: (4.0), Client Version: (1.2), PushRouterOrigin: (0xB), UserAgentOrigin: (0x8), Initiator: (0x0), Mode: (0x2), SessionID: (0x58), Authentication Type: (0x1).Event ID 814 - MDM PolicyManager: Set policy string, Policy: (PasswordManagerEnabled), Area: (microsoft_edge~Policy~microsoft_edge~PasswordManager), EnrollmentID requesting merge: (D0892524-8DFC-D50A19DBF), Current User: (Device), String: (<enabled/>), Enrollment Type: (0x6), Scope: (0x0).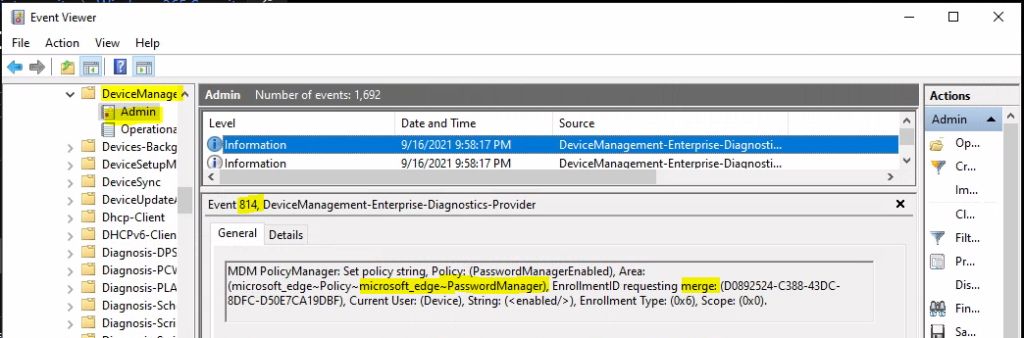
Registry Level Troubleshooting for Intune Security Policy Deployment
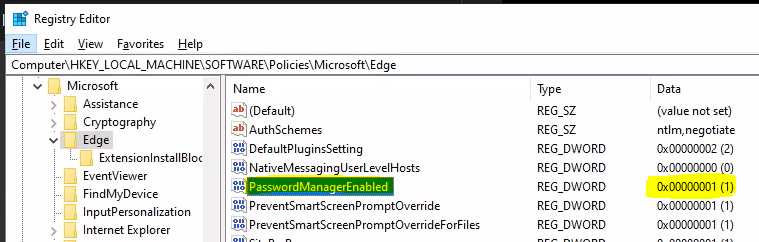
It’s time to check and confirm the registry entries related to the Microsoft Edge password manager. The Registry Level Troubleshooting for Intune Security Policy Deployment is explained in this section. You can launch Regedit.exe and navigate to the following path to confirm the registry entry changes.
- Try to refresh the registry value if you have already opened the registry.
- Navigate to Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Edge -> PasswordManagerEnabled -> 1 (REG_DWORD).
This means the Microsoft Edge Password Manager policy change is already applied to Windows PC. If it’s not changed, you need to confirm whether this is the correct registry entry for the policy settings.
MDM Registry Settings for Cloud Policy | Intune Policy – Device Based Policy – > Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PolicyManager\providers\3B77AADA-128C-4856-BCD4-988AC1B9C852\default\Device\
Results
As you can see in the below screenshot, the Offer to save passwords setting is ENABLED now. This means the Intune policy settings changes for the Microsoft Edge security policies worked perfectly fine.