Let’s learn how to restrict Microsoft Edge Personal Accounts Sync using Intune. In the Microsoft Edge browser, you can determine which accounts can be used as Microsoft Edge primary accounts during the Sync.
By signing in with a work or school account, your settings will sync your settings and browsing data across devices. Restricting Microsoft edge personal accounts sync allows you to have a great experience with secure browsing when signed in with an organizational account.
Once you’ve signed in to your account in Microsoft Edge, you can sync your browser data across all your devices that are signed in with the same account.
Sync makes the web a more personal, seamless experience across all devices—the less time you have to spend managing your experience, the more time you’ll have to get things done.
You can perform the basic Microsoft Edge security policy troubleshooting from the MEM admin center portal. One example is given below How To Start Troubleshooting Intune Issues from the server-side.
The next level of troubleshooting is with MDM Diagnostics Tool to collect the log and information from the client-side.
- Block Microsoft Edge Extensions using Intune
- Enable Microsoft Edge Sleeping Tabs using Intune
- Configure Edge Chromium Favorites Using Intune | Endpoint Manager
Restrict Microsoft Edge Personal Accounts Sync Using Intune
Let’s follow the below steps to Restrict Microsoft Edge Personal Accounts Sync using Intune –
- Sign in to the https://endpoint.microsoft.com/
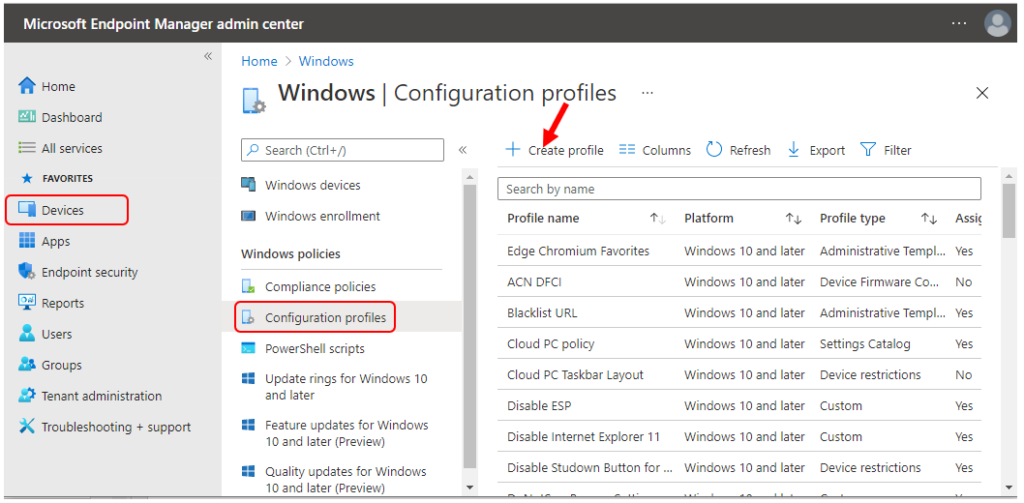
- To create a new Configuration profile, Select Devices > Windows > Configuration profiles > Create profile
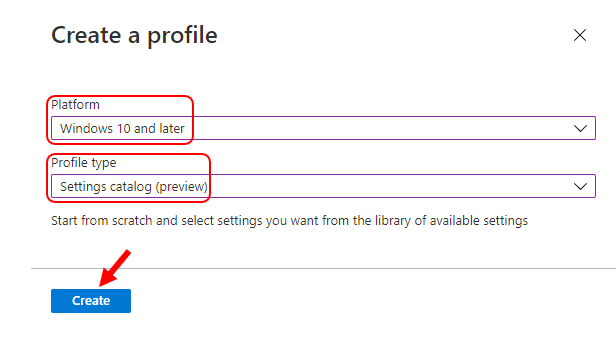
In Create a profile, Select Platform, Windows 10, and later and Profile, Select Profile Type as Settings catalog. Click on Create button.
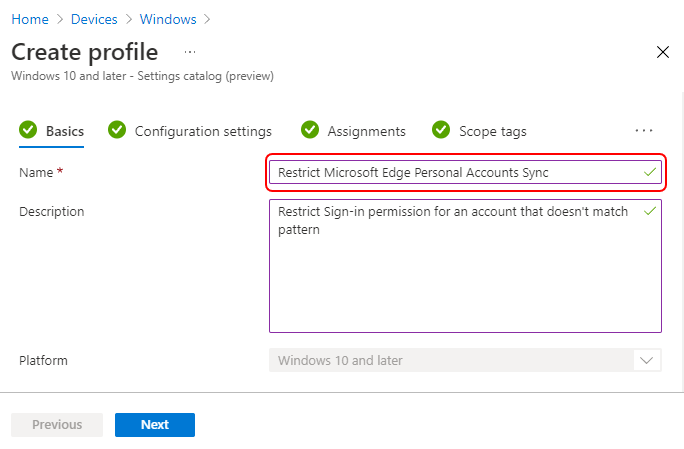
On the Basics tab, enter a descriptive name, such as Restrict Microsoft Edge Personal Accounts Sync. Optionally, enter a Description for the policy, then select Next.
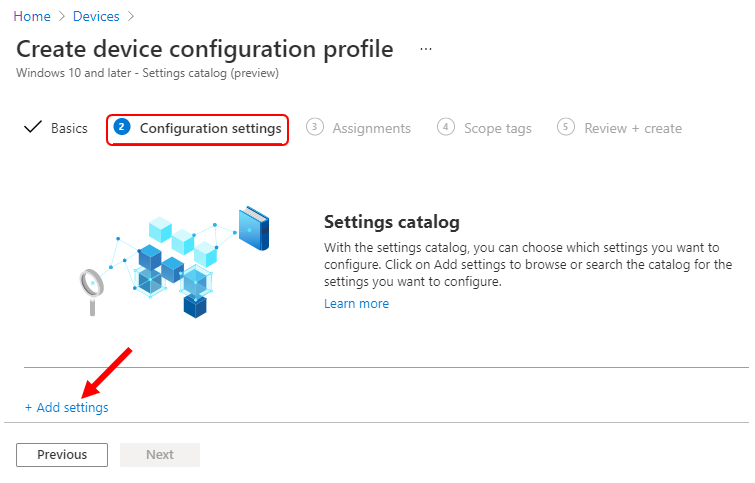
In Configuration settings, under Settings catalog, click Add settings.
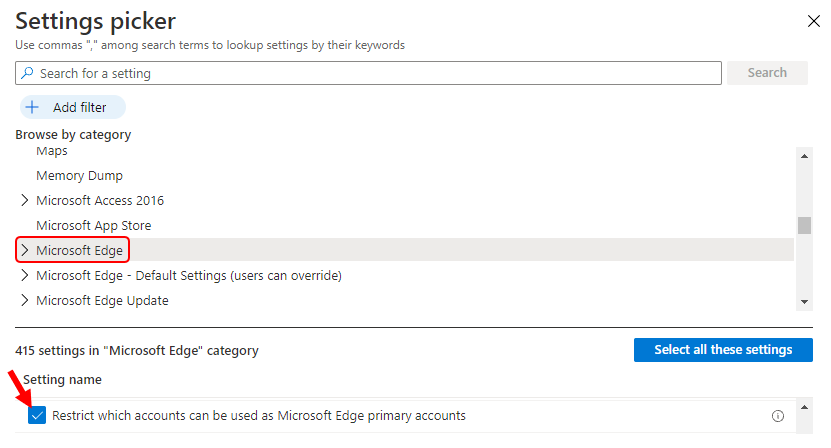
On the Settings Picker windows, Select Microsoft Edge to see all the settings in this category. Select Restrict which accounts can be used as Microsoft Edge primary accounts below.
After adding your settings, click the cross mark at the right-hand corner to close the settings picker.
Note – In policy, use the search box to find specific settings. You can search by category or a keyword, such as Edge Primary Accounts. It will display the related settings available.
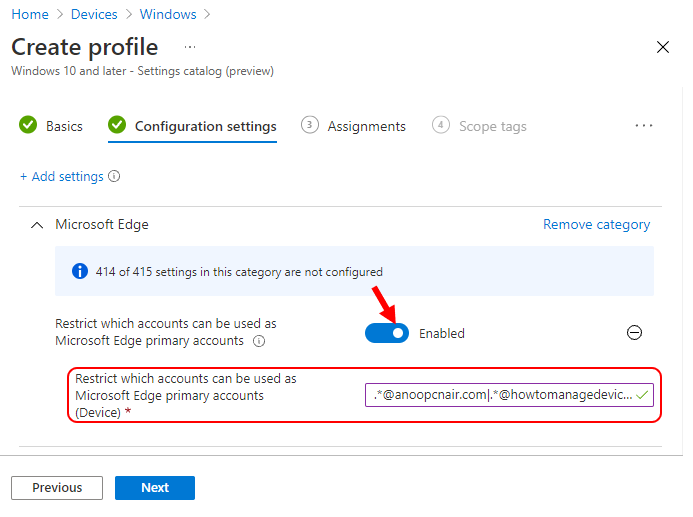
The setting is shown and configured with a default value Disabled. Set Restrict which accounts can be used as Microsoft Edge primary accounts to Enabled. Add the domain to allow sign-in to the browser, in format starts with .*@YourDomain.com if you want to add multiple domains separated by | and click Next.
Restrict which accounts can be used as Microsoft Edge primary accounts – Determines which accounts can be set as primary browser accounts in Microsoft Edge (the account chosen during the Sync opt-in flow).
If a user tries to set a primary browser account with a username that doesn’t match this pattern, they are blocked and see an appropriate error message. For Example, *@anoopcnair.com|.*@howtomanagedevices.com
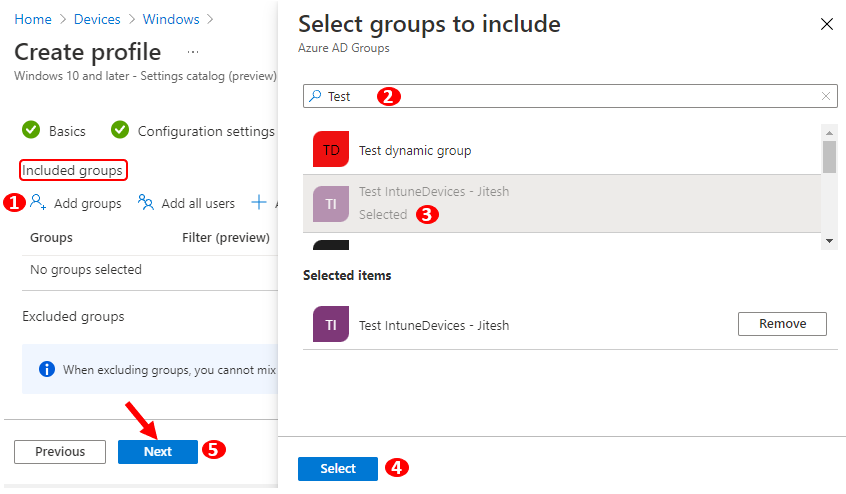
Under Assignments, In Included groups, click Add groups and then choose Select groups to include one or more groups. Click Next to continue.
You can assign a tag to filter the profile to specific IT groups in-Scope tags. Add scope tags (if required) and click Next.
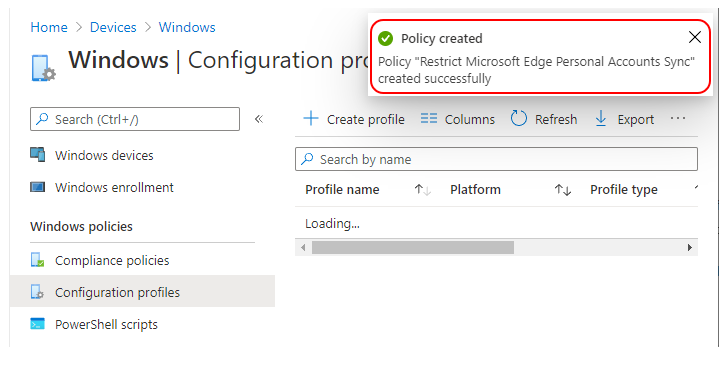
In Review + create, review your settings. When you select Create, your changes are saved, and the profile is assigned.
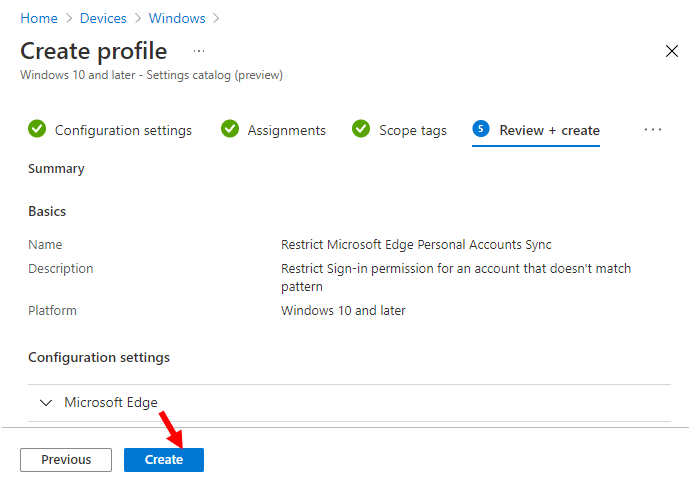
A notification will appear automatically in the top right-hand corner with a message. Here, Policy “Restrict Microsoft Edge Personal Accounts Sync” was created successfully. The policy is also shown in the Configuration profiles list.
Your groups will receive your profile settings when the devices check-in with the Intune service. Once the policy applies to the devices, If a user tries to set a primary browser account with a username that doesn’t match this pattern, they are blocked and see an appropriate error message.
To check if the policy is applied, Open Microsoft Edge. Enter edge://policy in the address bar, and you will see the policy is applied with added domains.
Author
About Author -> Jitesh has over 5 years of working experience in the IT Industry. He writes and shares his experiences related to Microsoft device management technologies and IT Infrastructure management. His primary focus area is Windows 10 Deployment solution with Configuration Manager, Microsoft Deployment Toolkit (MDT), and Microsoft Intune.



I enabled this policy on my tenant and it promptly broke my Automatic Sign-in and Sync configuration. Have you experienced the same thing? If go back and disable this policy, then Edge will automatically sign-in and sync again.
Andrew, have you found a solution to this problem? I’m attempting to auto sign in AND force sync.
Try to enable the below policy
https://learn.microsoft.com/en-us/deployedge/microsoft-edge-policies#aadwebsitessousingthisprofileenabled