Let’s quickly check whether Intune policy is Tattooed or Not Tattooed. I saw this behaviour during one of the demos in the recent Namaste Techies episode. The group policy tattooing is always a headache for ConfigMgr Client Installations using the AD group policy. Don’t forget to check Jason Sandys’s comments at the bottom of this post on the latest behaviours of Intune Tattooing!
I don’t blame Intune for tattooing policies into your Windows 11 or Windows 10 devices. The tattooing of settings is an issue or limitation of Windows CSP (Configuration Service Provider). Microsoft has already confirmed that many Windows CSPs are having this issue.
I don’t know whether we still have the Intune policy tattoo problem. I will let you see the conclusion with a small number of policy tests that I have done. Yes, it’s still a problem for some of the CSPs. Check out the conclusion section of this post to get more details.
The good news is that the new Windows CSP policies are expected to come with better management options. Ideally, they should not have an Intune policy tattooing effect. Let’s explore this further with some examples in this blog post.
- Intune User Policy Troubleshooting Tips For Prevent Changing Theme
- Intune Logs Event IDs IME Logs Details For Windows Client Side Troubleshooting
What is Intune Policy Tattooing?
Intune is a server-side system that helps IT admins create and deliver the configuration settings to the client. This is the easiest way to understand the Intune side of things. The Intune settings are based on the Windows configuration service provider (CSPs). The behavior of Windows CSP is something that can’t be controlled from the Intune side directly.
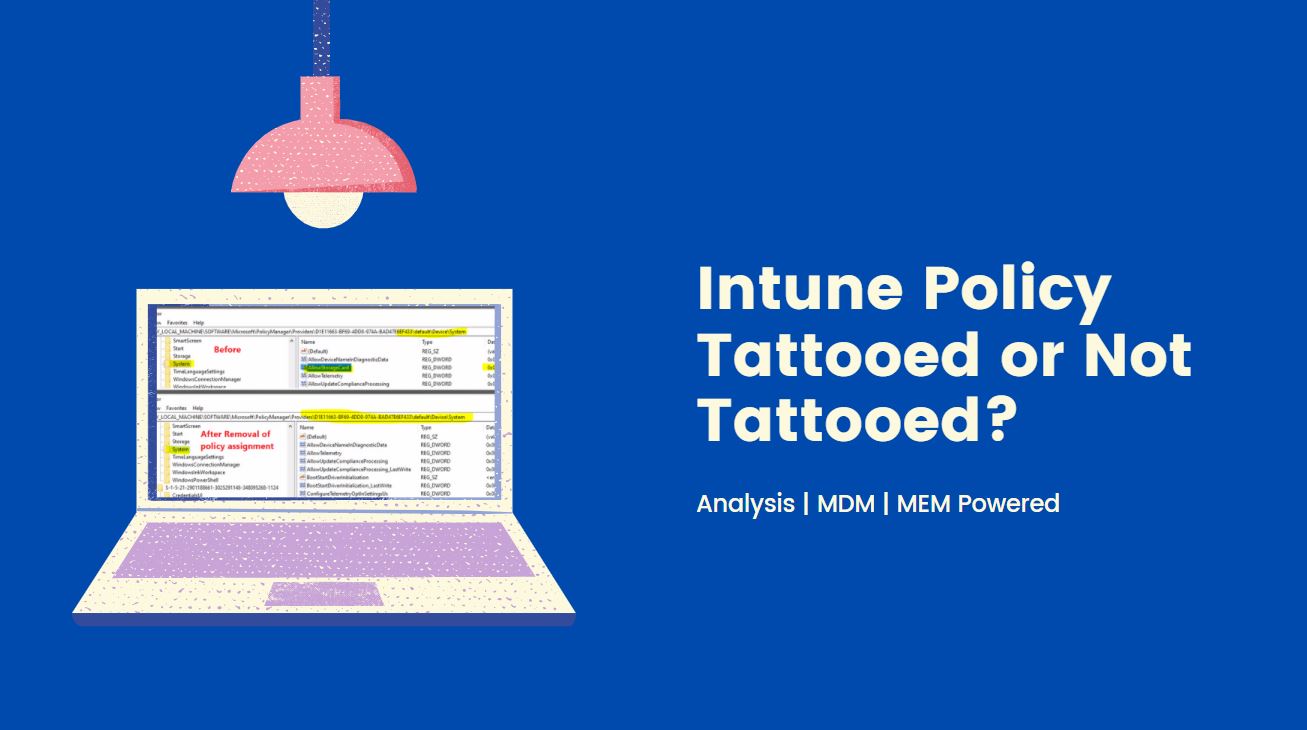
The policy tattooing behaviour depends on each Windows CSP. Some good and modern Windows CSPs remove the settings from your device after removing the policy assignment from Intune (as shown in the above screen capture). However, there are some “bad” Windows CSPs, and the related settings of those CSPs won’t get removed even after the removal of the policies.
This type of permanent policy setting behaviour is called tattooing (for example, “bad” CSPs from the above paragram). You don’t have an out-of-the-box easy way to remove these settings (tattooed ones) from Windows 11 or Windows 10 devices. Instead, you might need to configure the policy with a new preferred value to have the desired output.
Disable Control Panel Settings App Access Intune Policy Tattooed?
As mentioned above, there are some good and modern Windows CSPs that do have tattooing issues. So these policies are easy to manage, and these settings will get removed from the client device whenever you remove the policy assignment from that device using Intune.
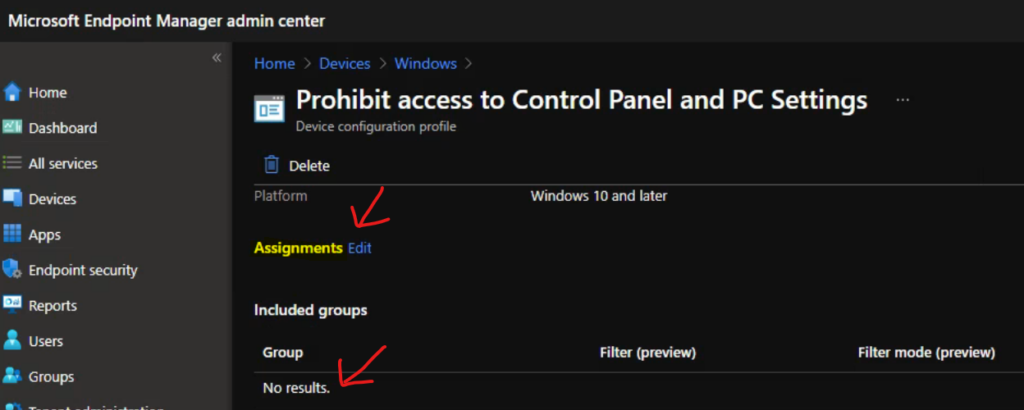
One of the example policies is “Prohibit access to Control Panel and PC settings (User),” which helps admins disable access to Control Panel and Settings apps from Windows devices. I have a post that explains how to implement this policy (Disable Control Panel PC Settings Using Intune Prohibit access).
The Intune policy setting was applied on the device, as you can see in the above screenshot. However, the settings also got removed when I removed the policy from the Azure AD user group (because this is a user-based policy). Let’s see more details below.
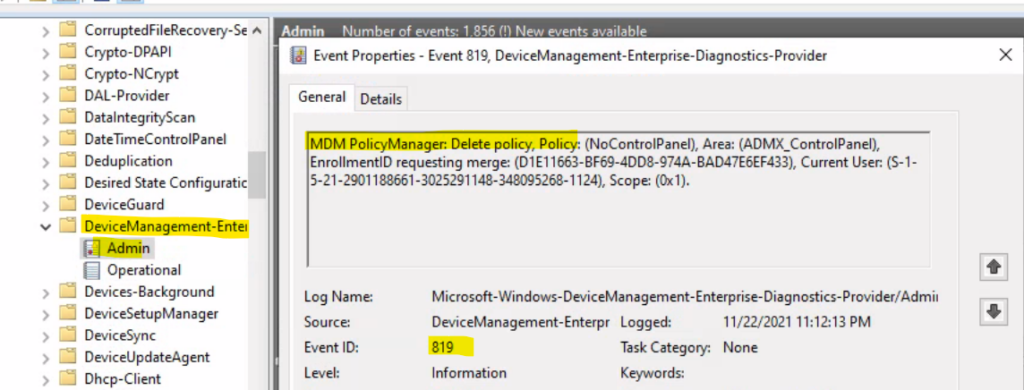
Intune Event Log ID 819 Not Tattooed Policy Removal Event
Let’s see what Event Log ID 819 means for Windows MDM and Intune Intune management. The Event log ID 819 means the MDM policy manager deleted the policy on the Windows 10 or Windows 11 client device. So, this deletion action will happen for Intune policies or Windows CSP policies that don’t have tattooing issues.
You can navigate to the following Event log path to confirm whether the policy tattooing behavior of the policy – Applications and Services Logs – Microsoft – Windows – Devicemanagement-Enterprise-Diagnostics-Provider – Admin.
MDM PolicyManager: Delete policy, Policy: (NoControlPanel), Area: (ADMX_ControlPanel), EnrollmentID requesting merge: (D1E11663-BF69-4DD8-974A-BAD47E6EF433), Current User: (S-1-5-21-2901188661-3025291148-348095268-1124), Scope: (0x1).
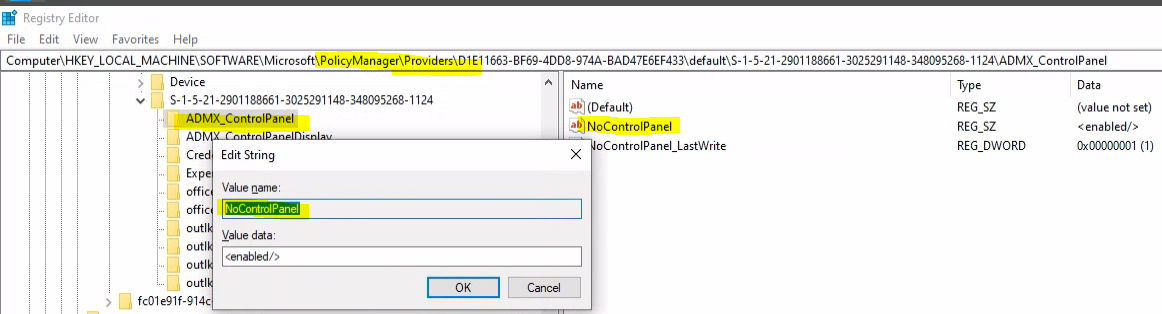
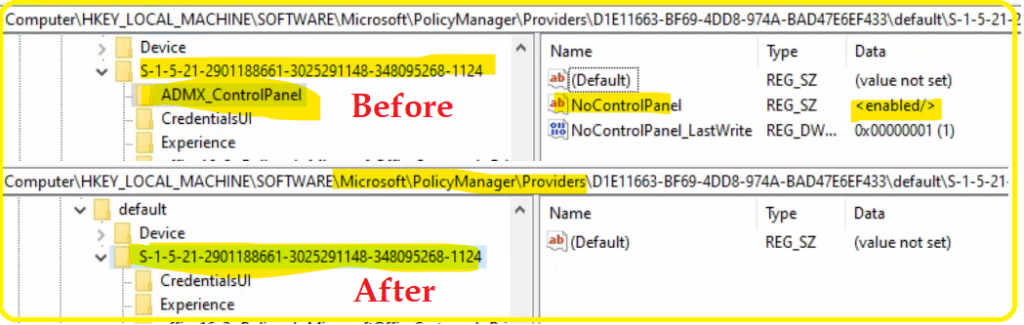
Delete policy Event Log – Registry Confirmation for Non Tattooed Policy
Now, you can head back to the registry and confirm whether the actual settings to disable the control panel or setting catalog are removed from the registry or not. If this setting is removed, that means this ControlPanel ADMX – NoControlPanel policy doesn’t have a tattooing issue.
Registry Path Example 1 – Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PolicyManager\current\S-1-5-21-2901188661-3025291148-348095268-1124\ADMX_ControlPanel
Registry Path Example 2- Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PolicyManager\Providers\
Registry Path Example 3- Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PolicyManager\Providers\D1E11663-BF69-4DD8-974A-BAD47E6EF433\default\Device
Registry Path Example 4 Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PolicyManager\Providers\D1E11663-BF69-4DD8-974A-BAD47E6EF433\default\S-1-5-21-2901188661-3025291148-348095268-1124
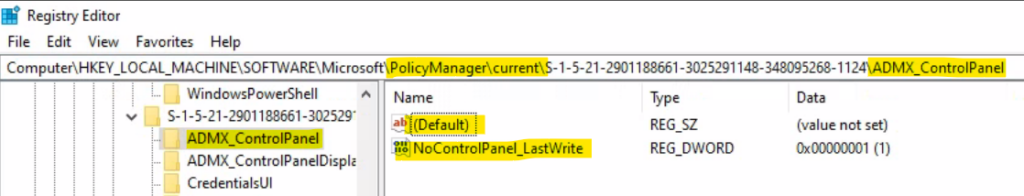
The NoControlPanel registry entry was removed after I removed the policy deployment or assignment from the Microsoft Intune policy (settings catalog). This confirms that there is no tattooing issue for this particular Windows CSP policy.
Example Registry Value 2 – Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PolicyManager\Providers\D1E11663-BF69-4DD8-974A-BAD47E6EF433\default\S-1-5-21-2901188661-3025291148-348095268-1124\ADMX_ControlPanel
Let’s check the before and after effects of this policy not being tattooed in Intune. This is a really good sign!
NOTE! – I tested this with Windows 10 21H1 build 19043.1348.
Prevent changing theme (User) – Intune Policy Tattooed or Not Tattooed?
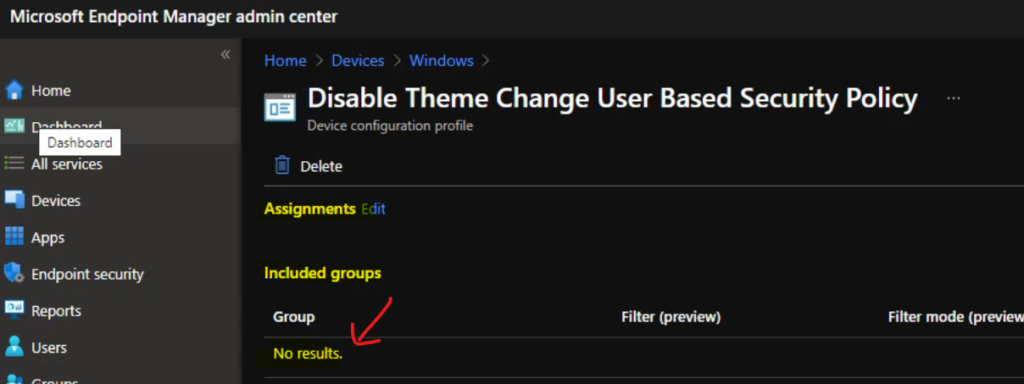
Let’s now check the policy called Prevent changing theme (User) for the tattooing effect. Another user-based approach is to disable the theme change using the Intune setting catalog. The policy is disabled from Intune and deployed to the Azure user group. The following is one of the registry keys; it shows the value as disabled.
Registry path – Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PolicyManager\Providers\D1E11663-BF69-4DD8-974A-BAD47E6EF433\default\S-1-5-21-2901188661-3025291148-348095268-1124\ADMX_ControlPanelDisplay
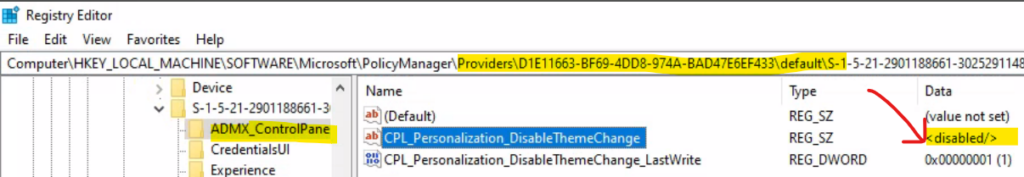
Let’s remove the Azure AD user group from the disable the theme change Intune settings catalog policy. If the Windows CSP supports removing the policy entry, this is a good policy and doesn’t have Intune policy tattooing issues.
Let’s check event log ID 819 for now and confirm whether an event has appeared on Windows 11 or Windows 10 devices. The registry values are not tattooed to the client’s devices as per the below event log.
MDM PolicyManager: Delete policy, Policy: (CPL_Personalization_DisableThemeChange), Area: (ADMX_ControlPanelDisplay), EnrollmentID requesting merge: (D1E11663-BF69-4DD8-974A-BAD47E6EF433), Current User: (S-1-5-21-2901188661-3025291148-348095268-1124), Scope: (0x1).
The entire registry value and key/folder were removed from the system after removing the policy assignment. This activity proved that the registry values are not tattooed for the ADMX_ControlPanelDisplay policy.
NOTE! – ADMX_ControlPanelDisplay entry is not available in the registry now!
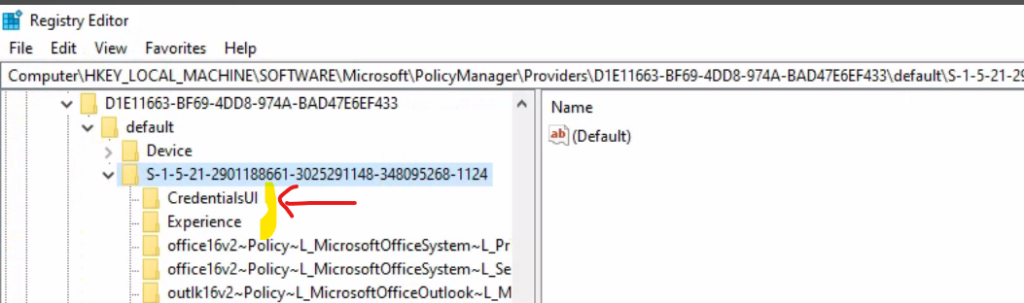
Redirection Settings Intune Policy Tattooed?
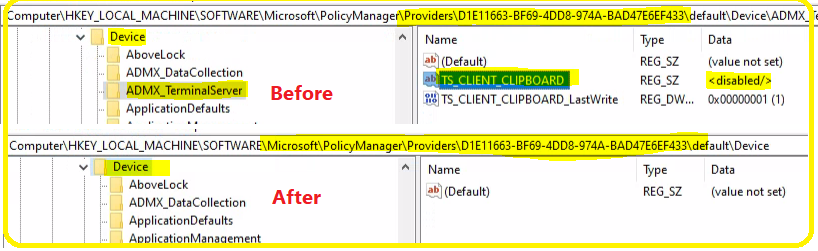
Let’s find out whether the Redirection Settings (device-based) Intune Policy is Tattooed. In the previous post, I explained the deployment of Cloud PC redirection policies. Now, let’s try to remove the assignment of that Intune settings catalog policy.
To quickly check whether the policy changes are reflected on Windows 10 or Windows 11, initiate the Intune policy sync (Initiate a Manual Intune Policy Sync) from the Company Portal app. As per the event log ID 819, two settings have been removed from the Windows device.
You can check the following event logs – Devicemanagement-Enterprise-Diagnostics-Provider – Admin.
MDM PolicyManager: Delete policy, Policy: (DoNotAllowDriveRedirection), Area: (RemoteDesktopServices), EnrollmentID requesting merge: (D1E11663-BF69-4DD8-974A-BAD47E6EF433), Current User: (Device), Scope: (0x1).
MDM PolicyManager: Delete policy, Policy: (TS_CLIENT_CLIPBOARD), Area: (ADMX_TerminalServer), EnrollmentID requesting merge: (D1E11663-BF69-4DD8-974A-BAD47E6EF433), Current User: (Device), Scope: (0x1).
The registry entry changes are shown in the screen capture below. The ADMX_TerminalServer (and RemoteDesktopServices) entries were removed, which means Redirection settings are not tattooed into the registry.
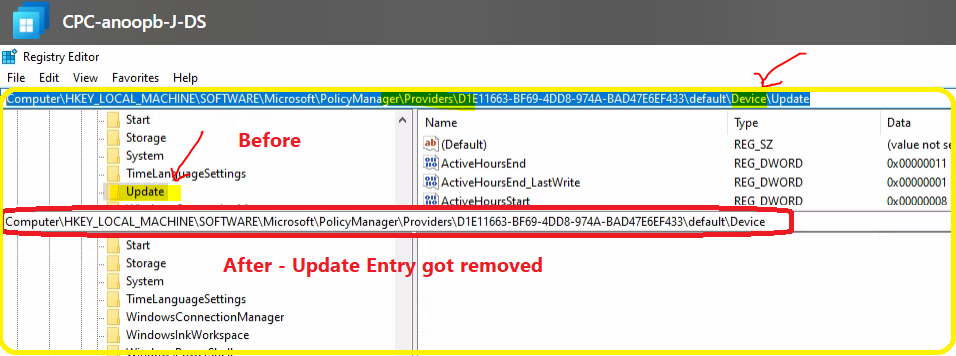
WUfB Policies Are Tattooed or Not Tattooed?
Here is the Windows Update for Busines (WUfB) last policy that I’m going to check whether it’s tattooed or not. As per my testing, these policies are not tattooed because when I removed the assignment from the Azure AD group, all these policy settings from the registry also got deleted.
As you can see in the below screenshot, there are many event log IDs with 819. All these event logs confirm that the Windows Update for Business policies are getting deleted.
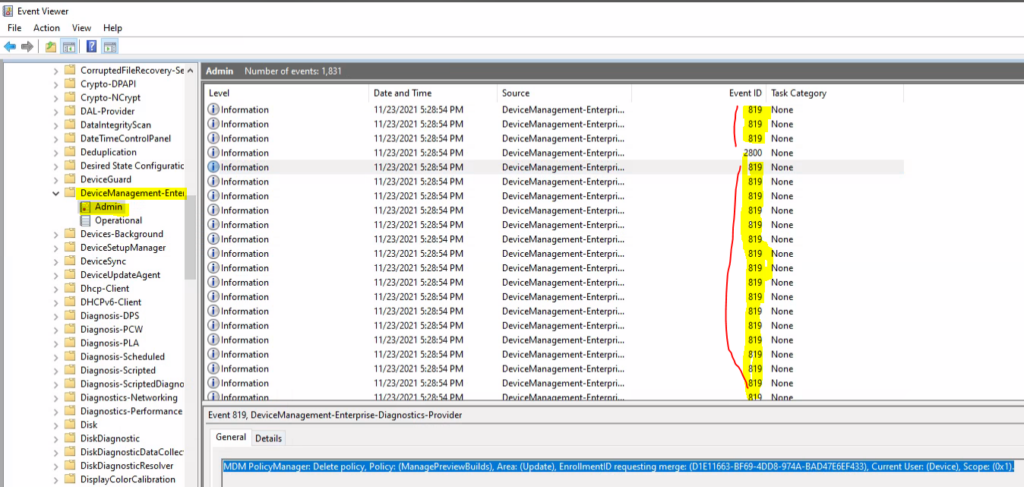
MDM PolicyManager: Delete policy, Policy: (ConfigureDeadlineNoAutoReboot), Area: (Update), EnrollmentID requesting merge: (D1E11663-BF69-4DD8-974A-BAD47E6EF433), Current User: (Device), Scope: (0x1).
MDM PolicyManager: Delete policy, Policy: (ConfigureDeadlineGracePeriod), Area: (Update), EnrollmentID requesting merge: (D1E11663-BF69-4DD8-974A-BAD47E6EF433), Current User: (Device), Scope: (0x1).
MDM PolicyManager: Delete policy, Policy: (ConfigureDeadlineForQualityUpdates), Area: (Update), EnrollmentID requesting merge: (D1E11663-BF69-4DD8-974A-BAD47E6EF433), Current User: (Device), Scope: (0x1).
MDM PolicyManager: Delete policy, Policy: (ConfigureDeadlineForFeatureUpdates), Area: (Update), EnrollmentID requesting merge: (D1E11663-BF69-4DD8-974A-BAD47E6EF433), Current User: (Device), Scope: (0x1).
MDM PolicyManager: Delete policy, Policy: (ConfigureDeadlineForFeatureUpdates), Area: (Update), EnrollmentID requesting merge: (D1E11663-BF69-4DD8-974A-BAD47E6EF433), Current User: (Device), Scope: (0x1).
The following screenshot gives you an idea of the before-and-after removal of Windows Update for Business policies deployed using Intune. The following registry path helps you understand whether the Update entry is there or not.
Example 1 – Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PolicyManager\Providers\D1E11663-BF69-4DD8-974A-BAD47E6EF433\default\Device
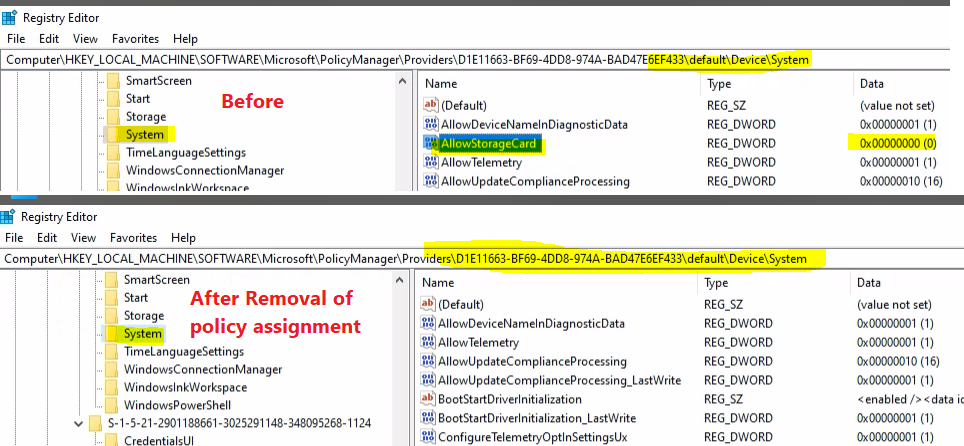
Disable Removable Storage Write Access Using Intune policy Tattooed?
Check whether the Disable Removable Storage Write Access Using Intune policy is Tattooed from event logs and registry entries.
MDM PolicyManager: Delete policy, Policy: (RemovableDiskDenyWriteAccess), Area: (Storage), EnrollmentID requesting merge: (D1E11663-BF69-4DD8-974A-BAD47E6EF433), Current User: (Device), Scope: (0x1).
MDM PolicyManager: Delete policy, Policy: (RemovableDiskDenyWriteAccess), Area: (Storage), EnrollmentID requesting merge: (D1E11663-BF69-4DD8-974A-BAD47E6EF433), Current User: (Device), Scope: (0x1).
Conclusion
I tested five (5) different Intune policies (Windows CSP policies), and I couldn’t find any of these policies tattooed into the Windows devices. So, it’s safe to assume that most of the Windows CSP or Intune policies are not tattooed as before.
Let me know if you see any policies being tattooed in Intune. This will make things difficult for admins. You will need to reconfigure the Intune policy to not configure or something else to fix this kind of tattooed entry in the registry.
NOTE! – In the worst-case scenario, you will need to deploy a PowerShell remediation script using Intune to remove these tattooed entries. I don’t recommend performing this method unless and until there is no other option.
Updated on 24th Nov – I learned from Kenneth van Surksum (my MVP colleague) that the tattooed settings can’t be confirmed from the removal of the registry entries in his experience. So as per him, some settings can still be tattooed even though the related entries are removed from the registry.
Updated on 3rd Dec – I learned from Jason Sandys (Microsoft Senior Program Manager, Former Microsoft MVP (12 years)) that the method of checking whether the CSP policy is tattooed or not using the registry is not valid. As per him, the best bet here is to use the WMI bridge to check actual settings to determine whether or not they are tattooed.
There should NOT be any Intune policy Tattooing behaviour for any of the policies in Windows. If you see this behaviour for any of the policies, you need to consider this a bug or raise a support ticket with Microsoft.
Author
Anoop is Microsoft MVP! He is a Solution Architect in enterprise client management with more than 20 years of experience (calculation done in 2021) in IT. He is Blogger, Speaker, and Local User Group HTMD Community leader. His main focus is on Device Management technologies like SCCM 2012, Current Branch, and Intune. He writes about ConfigMgr, Windows 11, Windows 10, Azure AD, Microsoft Intune, Windows 365, AVD, etc……………


Hi,
Thank you for this blog. Have you tested the ASR policies? I’ve have experienced that the ASR policies being tattooed even after I remove the devices from the assignment group.
I have not tested ASR but I have tested ESP policies and I think they also get tattooed.
Hi,
Here are things that I have faced :
1. Applied the block USB devices policy to All devices.
2. Added an exception to this policy for a device with a different Custom OMA-URI policy.
3. But it did not allow the USB on that device.
4. Though the registry key AllowStorageCard to 1.
Any suggestions to add this exception.
Regards,
Ashish Arya
We are experiencing tattooing when deploying a LAN profile that enforces 802.1x.