Let’s find out the method to disable PST Access to Outlook Profile using Intune MEM. Well, I don’t think this is not a big issue for an Intune admin to disable the access to PST from the Outlook application. If you are using the PWA version of OWA, there is no option to add a PST file.
You can prevent users from adding PSTs to Outlook profiles using Intune policies explained in this post. The best method is to define a policy using Intune Settings Catalog profiles. By default, users can add PSTs to their Outlook profiles. But some of the security teams are very particular about these PST configurations and policies.
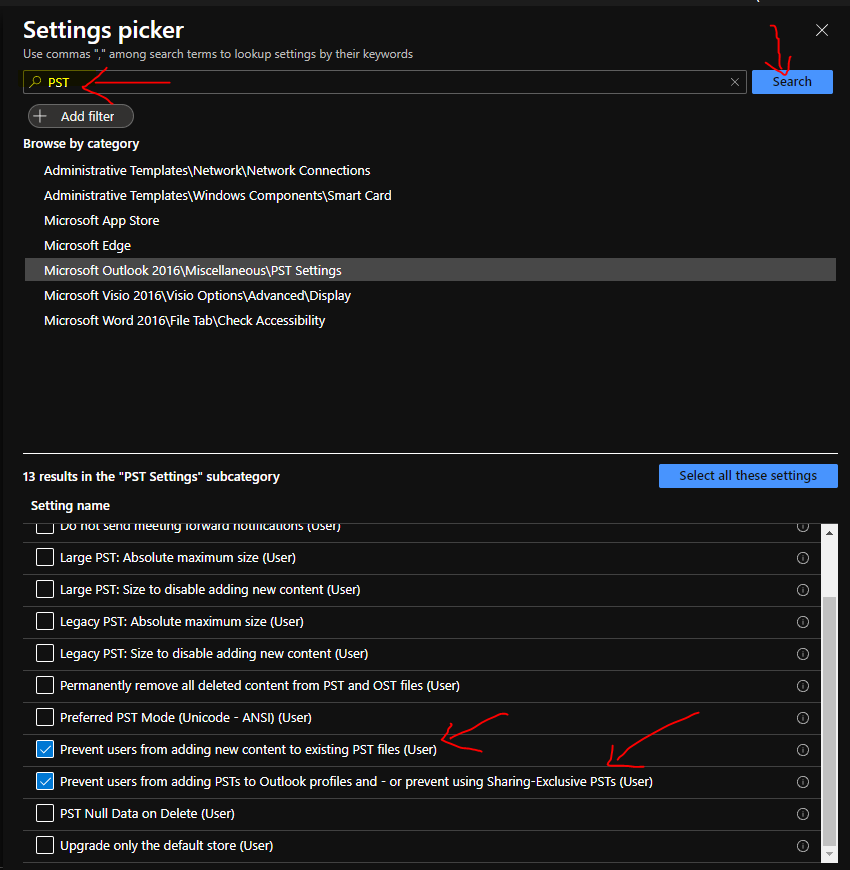
Intune can help security teams to set up these kinds of policies in the modern management world rather than using ADMX based group policies. There are many other PST/OST related policies available, as mentioned below.
Default location for OST files (User)
Default location for PST files (User)
Do not send meeting forward notifications (User)
Large PST: Absolute maximum size (User)
Large PST: Size to disable adding new content (User)
Legacy PST: Absolute maximum size (User)
Legacy PST: Size to disable adding new content (User)
Permanently remove all deleted content from PST and OST files (User)
Preferred PST Mode (Unicode – ANSI) (User)
Prevent users from adding new content to existing PST files (User)
Prevent users from adding PSTs to Outlook profiles and – or prevent using Sharing-Exclusive PSTs (User)
PST Null Data on Delete (User)
Upgrade only the default store (User)
Intune server-side details are available through various reporting nodes in Intune portal. You can perform the basic Intune user policy deployment troubleshooting from the MEM admin center portal. More details of Intune Logs Event IDs IME Logs are available in the HTMD blog post.
- Configure RDP Properties Using Intune Settings Catalog
- Intune User Policy Troubleshooting Tips For Prevent Changing Theme
- Intune Win32 App Deployment Troubleshooting Help Guide
- Intune Security Baseline Microsoft Defender Policy Troubleshooting Tips
- Troubleshoot Microsoft Edge Security Policy Deployment Issues
How to Disable PST Access to Outlook Profile
Let’s disable PST access to the outlook profile using Intune setting catalog policies. In this scenario, I’m going to cover only two policies related to Outlook and PST. For many organizations, this PST export and import is one of the main security threats.
I have not seen PST-related restrictions for many organizations after moving to Office 365. I have received one question in the HTMD forum that some organizations still wanted to disable this feature to make managed devices fully secure.
- Prevent users from adding new content to existing PST files (User)
- EnabledPrevent users from adding PSTs to Outlook profiles and – or prevent using Sharing-Exclusive PSTs (User)
The following are the two PST policies, and both are user-based policies. Let’s get started!
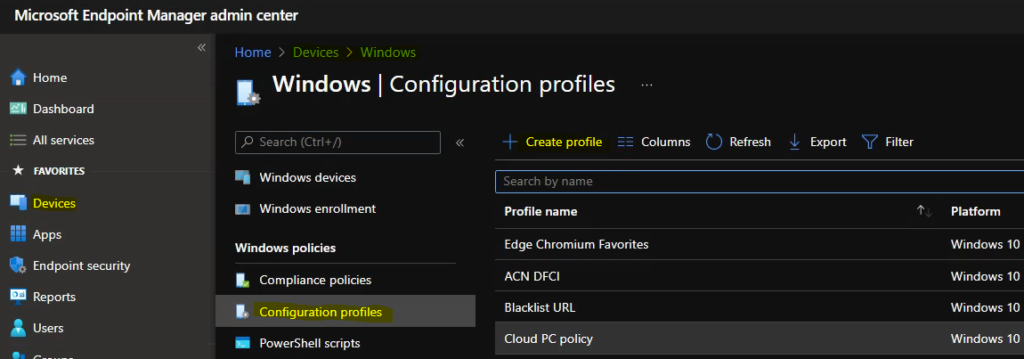
- Login to Endpoint Manager Intune portal https://endpoint.microsoft.com/#home
- Navigate to Devices -> Windows -> Configuration profiles.
- Click on +Create Profile.
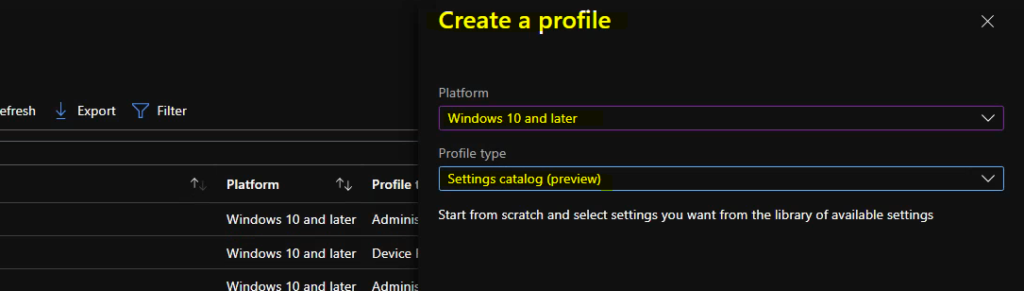
In Create Profile blade, You can select Platform: Select Windows 10 and later and Profile: Select Settings catalog (preview). Click on Create button.
For Example – You have to select the platform Windows 10 and later. You can enter the details of the policy and settings in the next screens.
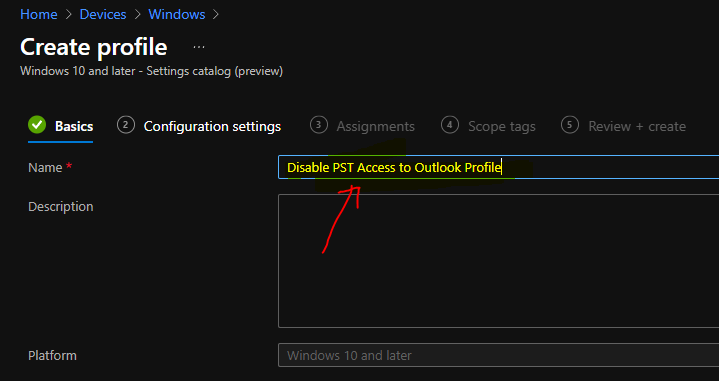
Once you click on Create button from the above page, you will need to enter the Name and Description of the setting catalog policy.
- Name – Disable PST Access to Outlook Profile
You will need to click on the Next button to continue and select disable PST policy settings from that Settings catalog configuration page.
You will need to click on the +Add Settings hyperlink from the next page of the policy configuration wizard. This hyperlink will help with a new blade called the Settings Picker with a search box.
Settings catalog – With the settings catalog, you can choose which settings you want to configure. Click on Add settings to browse or search the catalog for the settings you want to configure.
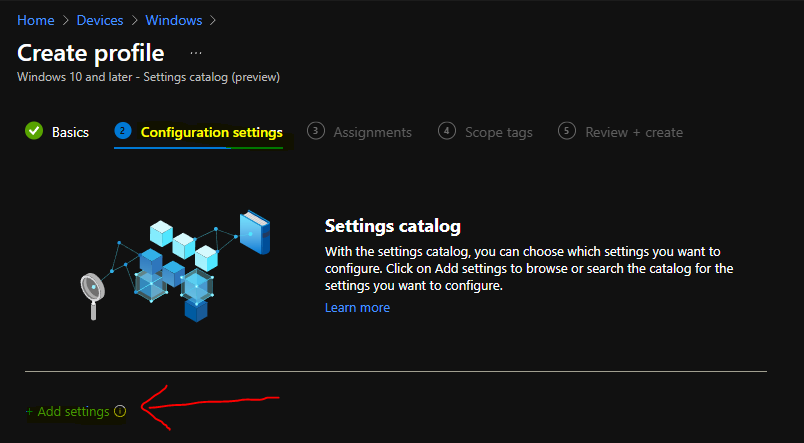
You also have many other options like filtering the policies based on OS edition etc. A lot of settings catalog policy categories. You can use the search box to find the relevant policies to Disable PST Access to Outlook Profile.
I have clicked on Microsoft Outlook 2016\Miscellaneous\PST Settings category and selected the following two policies as per my requirement here.
- Prevent users from adding new content to existing PST files (User)
- Prevent users from adding PSTs to Outlook profiles and – or prevent using Sharing-Exclusive PSTs (User)
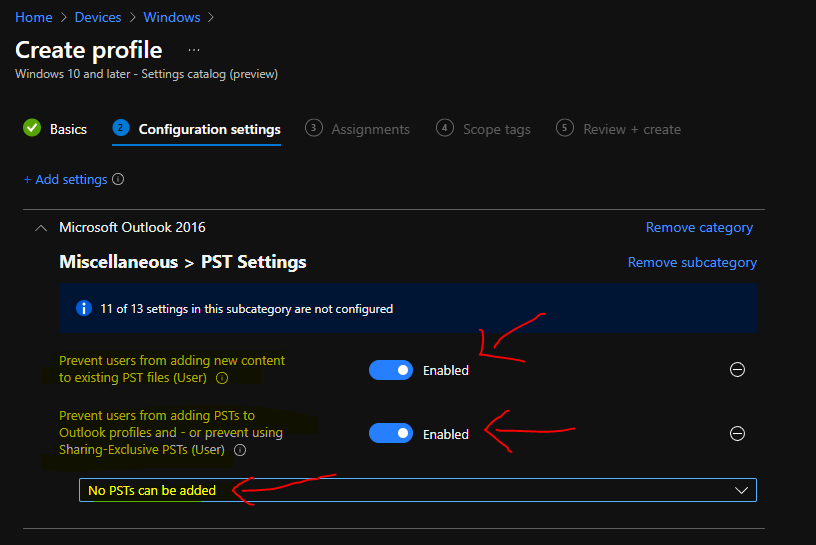
After selecting those two policies from Settings Catalog, you can close the Settings Picker Blade. You can now continue with those two PST policy configurations. Both of the below policies are user-based policies, and they will get deployed only after the user’s login.
Enable the first policy Prevent users from adding new content to existing PST files (User) –
This setting prevents users from adding any new content to PST files linked to their profiles.
Enable the second policy Prevent users from adding PSTs to Outlook profiles and – or prevent using Sharing-Exclusive PSTs (User) – By default, users can add PSTs to their Outlook profiles and use Sharing-Exclusive PSTs for storing SharePoint Lists and Internet Calendars.
You will also need to select the behavior of the second PST policy from the drop-down option. I have gone with a very strict option called – No PSTs can be added. You will need to click on the NEXT button to continue.
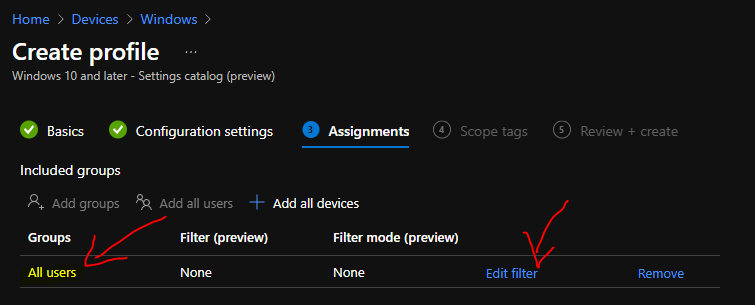
Assign Disable PST Access to Outlook Profile Policy to AAD User Group
This section will help you assign Disable PST Access to Outlook Profile Policy to the AAD User Group. You can refer to the following guide to Create Intune Settings Catalog Policy and deploy it only to a set of Intune Managed Windows 11 or Windows 10 devices using Intune Filters.
I used all users‘ deployment as an example for this particular policy deployment. I want to disable PST access to Outlook profile for all the users. You can click on the Next button and add the Scope Tags on the next page.
You will need to click on the next and create buttons to complete the policy creation process.
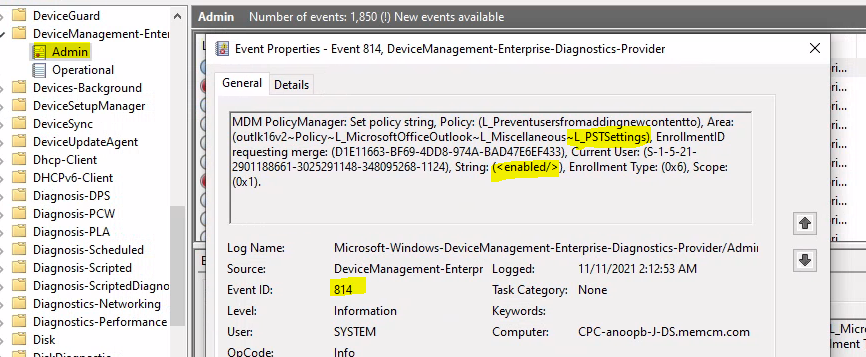
Intune MDM Event Log 814
The Intune event ID 814 indicates a string policy is applied on the Windows 11 or Windows 10 devices. You can also see the exact value of the policy being applied on those devices.
You can check the Event log path to confirm this – Applications and Services Logs – Microsoft – Windows – Devicemanagement-Enterprise-Diagnostics-Provider – Admin.
The policy setting that got applied and this policy is applied for the current user. The settings value is given below – outlk16v2~Policy~L_MicrosoftOfficeOutlook~L_Miscellaneous~L_PSTSettings.
MDM PolicyManager: Set policy string, Policy: (L_Preventusersfromaddingnewcontentto), Area: (outlk16v2~Policy~L_MicrosoftOfficeOutlook~L_Miscellaneous~L_PSTSettings), EnrollmentID requesting merge: (D1E11663-BF69-4DD8-974A-BAD47E6EF433), Current User: (S-1-5-21-2901188661-3025291148-348095268-1124), String: (), Enrollment Type: (0x6), Scope: (0x1).
MDM PolicyManager: Set policy string, Policy: (L_Preventusersfromaddingpsts), Area: (outlk16v2~Policy~L_MicrosoftOfficeOutlook~L_Miscellaneous~L_PSTSettings), EnrollmentID requesting merge: (D1E11663-BF69-4DD8-974A-BAD47E6EF433), Current User: (S-1-5-21-2901188661-3025291148-348095268-1124), String: (), Enrollment Type: (0x6), Scope: (0x1).
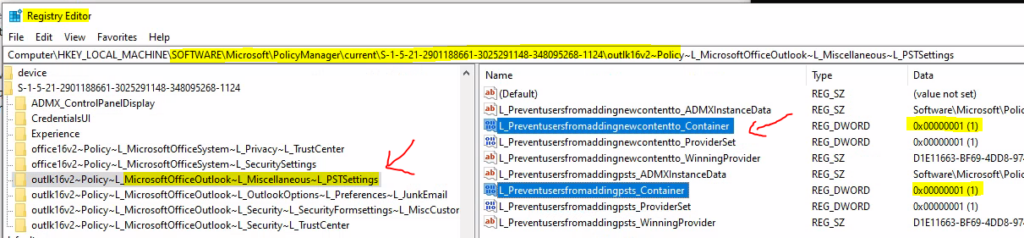
Registry Confirmation – Disable PST Access to Outlook Profile using Intune
You will need to check a different registry path to confirm whether user policies are deployed. So, the troubleshooting user policy deployment using Intune is a bit different than that of device-based.
The best option is to take the keyword from the event log and search the registry for that entry. In this example, outlk16v2~Policy~L_MicrosoftOfficeOutlook~L_Miscellaneous~L_PSTSettings.
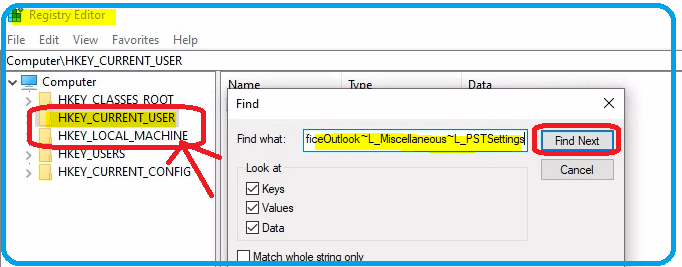
The keyword search helped find the correct registry path for policy to disable PST access to Outlook. The two registry values determine the access (?) to add PSTs to the Outlook app.
- L_Preventusersfromaddingpsts_Container = 1
- L_Preventusersfromaddingnewcontentto_Container = 1
The registry path – Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PolicyManager\current\S-1-5-21-2901188661-3025291148-348095268-1124\outlk16v2~Policy~L_MicrosoftOfficeOutlook~L_Miscellaneous~L_PSTSettings
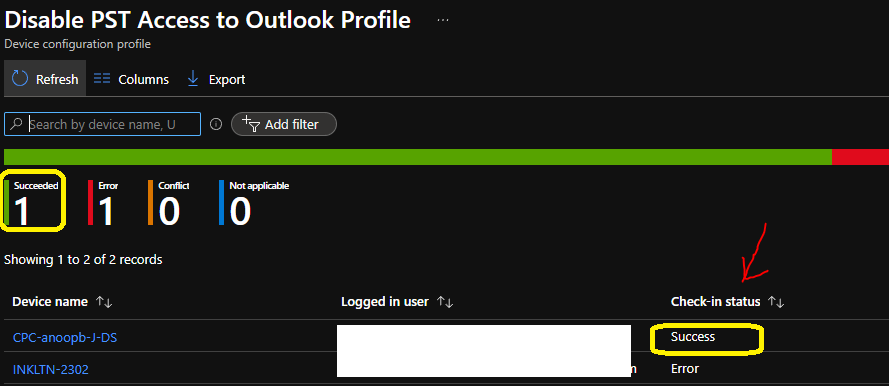
Results – Disable PST Access to Outlook Profile using Intune policy Deployment
You can check the Intune reports to confirm whether the client is sending the policy deployment status back to the server or service. The policy got successfully deployed on one of the devices and failed on one. We will more details on the failed device at some point of time in the future.
Author
Anoop is Microsoft MVP! He is a Solution Architect in enterprise client management with more than 20 years of experience (calculation done in 2021) in IT. He is Blogger, Speaker, and Local User Group HTMD Community leader. His main focus is on Device Management technologies like SCCM 2012, Current Branch, and Intune. He writes about ConfigMgr, Windows 11, Windows 10, Azure AD, Microsoft Intune, Windows 365, AVD, etc……………



Hi Anoop,
I have done all the settings and Intune report also confirms that policy is applied successfully. But still I am able to add the PST file in the outlook profile.
Please advise.