Let’s try to configure Cloud PC RDP properties using Intune settings catalog. You can already apply the RDP setting properties with group policies, but I don’t want to use group policies with Windows 365 Cloud PCs.
Let’s read through to know more about the conflict policy story as part of this deployment! I used the settings catalog profiles in Intune to test the RDP property policy deployment scenario.
One of my Device management community friends, Bruce, shared great news today that he tested disabling the clipboard redirection, which worked fine for him. I thought of trying the same in my lab environment.
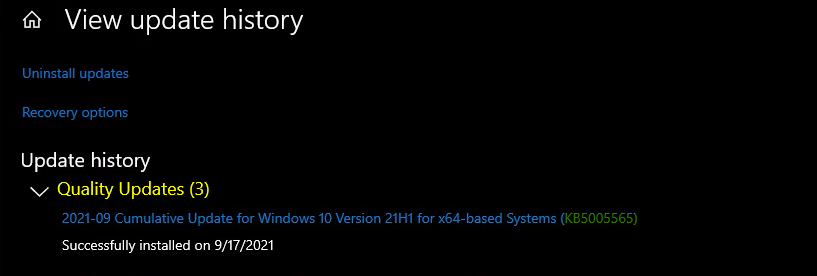
Recently Microsoft updated the settings catalog policies and the latest cumulative update for Windows 10 (SEP LCU). So, the KB5005565 update is the prerequisite to deploying the clipboard redirection policy to Cloud PCs.
NOTE! – The default gallery image available for Cloud PC is not updated with this KB. So you might need to update it via Software update or monthly patching policy (WUfB) created in Intune.
Create RDP Settings Policy using Intune
Let’s see how to create RDP settings policies for Cloud PC using Intune. The Intune settings catalog profile lists all the settings you can configure and all in one place using Windows CSP.
This feature simplifies how you create a policy and how you see all the available settings. You will have to log in to the MEM Admin center portal to create the policies with appropriate access.
- Login to Endpoint Manager Intune portal https://endpoint.microsoft.com/#home
- Navigate to Devices -> Windows -> Configuration profiles.
- Click on +Create Profile.
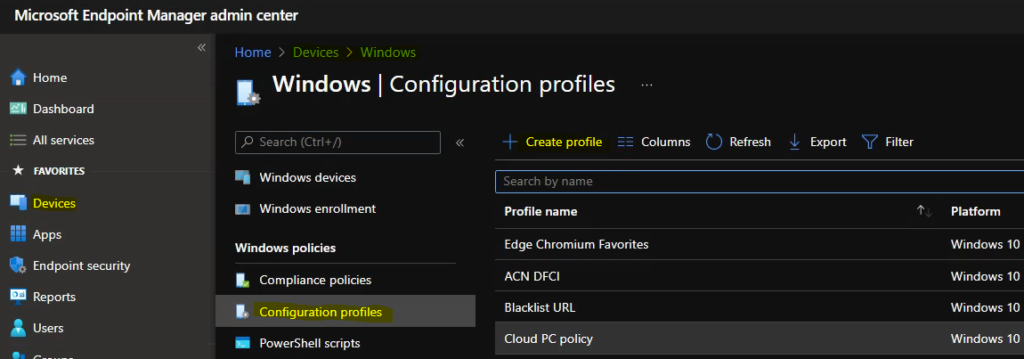
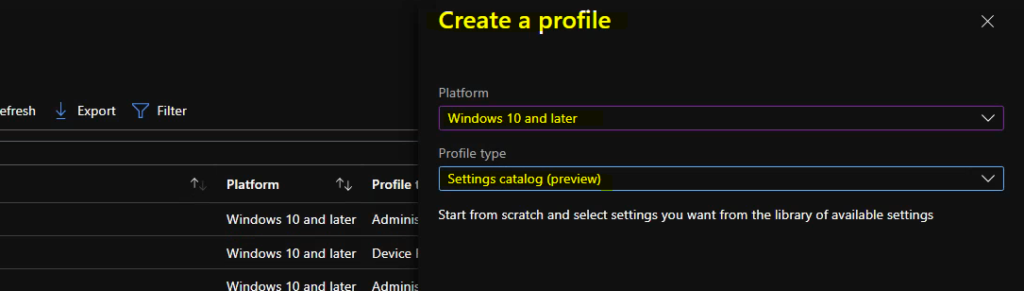
In Create Profile blade, You can select Platform: Select Windows 10 and later and Profile: Select Settings catalog (preview). Click on Create button.
For Example – You have to select the platform Windows 10 and later. You can enter the details of the policy and settings in the next screens.
Once you click on Create button from the above page, you will need to enter the Name and Description of the setting catalog policy. Cloud PC RDP Settings Policy is the name that I provided for this settings catalog policy for clipboard and drive redirection settings.
You will need to click on the +Add Settings hyperlink from the next page of the policy configuration wizard. This opens up the search box and a lot of settings catalog policy categories. You can use the search box to find the relevant policies for Cloud PC RDP settings.
- Search with the keyword -> Device and Resource Redirection
- The following are the policies/settings available while writing this post:
- Allow audio and video playback redirection
- Allow audio recording redirection
- Allow time zone redirection
- Do not allow Clipboard redirection
- Do not allow COM port redirection
- Do not allow drive redirection
- Do not allow LPT port redirection
- Do not allow smart card device redirection
- Do not allow supported Plug and Play device redirection
- Do not allow video capture redirection
- Limit audio playback quality
I have selected the two policies highlighted in bold from the above list. The first one is to disable Clipboard redirection between base PC and Cloud PC. The second setting is for disabling drive redirection for Cloud PC. Click on the Select button to continue to the next page.
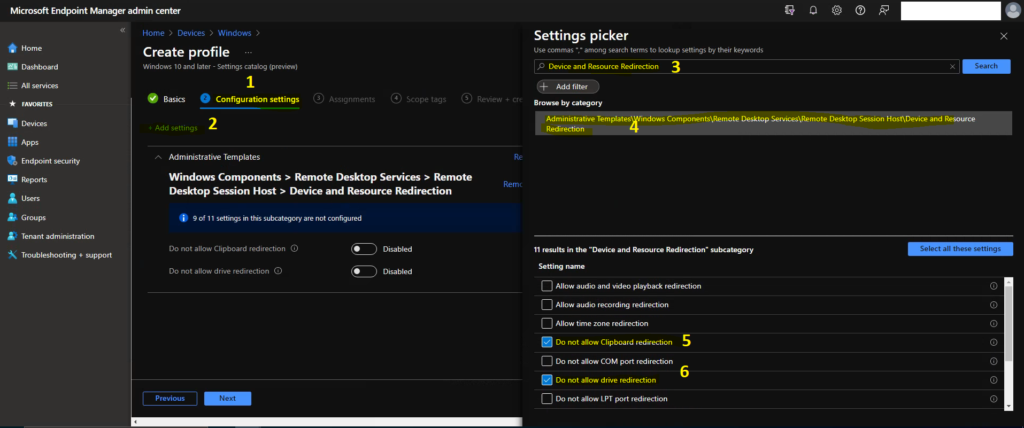
Do not allow Clipboard redirection – This policy setting specifies whether to prevent the sharing of Clipboard contents (Clipboard redirection) between a remote computer and a client computer during a Remote Desktop Services session.
Do not allow drive redirection – This policy setting specifies whether to prevent the mapping of client drives in a Remote Desktop Services session (drive redirection). By default, an RD Session Host server maps client drives automatically upon connection.
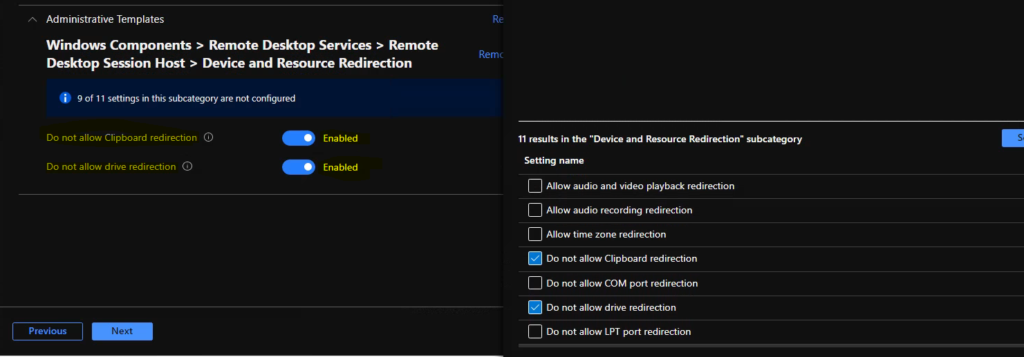
Now it’s time to enable these two settings to disable the clipboard and drive redirection. Click on the Next button to Continue. You can select all the other available policy settings if you require to disable or enable other RDP settings.
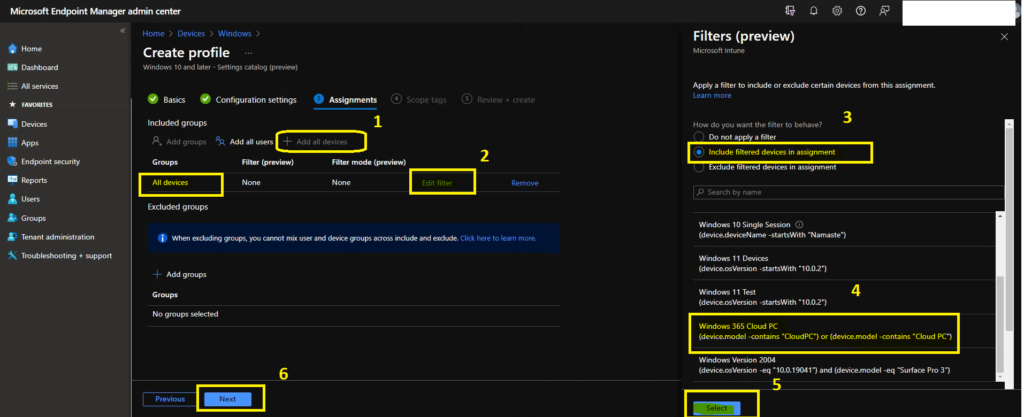
It’s time to assign the settings catalog policy for Cloud PC RDP settings to Cloud PC devices. I have not tried deploying this to Azure AD user groups. I used Intune filters for Cloud PC to cover this policy deployment. I have assigned the settings to all devices but included a filter for cloud pc so that this will get only be deployed to Cloud PCs.
- Click on All Devices.
- Click on Filter to add Windows 365 Cloud PC filter and you need to include only Cloud PC devices.
- Click on Review + Save to complete Intune monthly policy creattion process.
NOTE! – You will need to be careful about the deployment using Intune filter rules in production. I recommend testing all the Intune filter rules and this type of deployment in staging or pre-production environments before going to production.
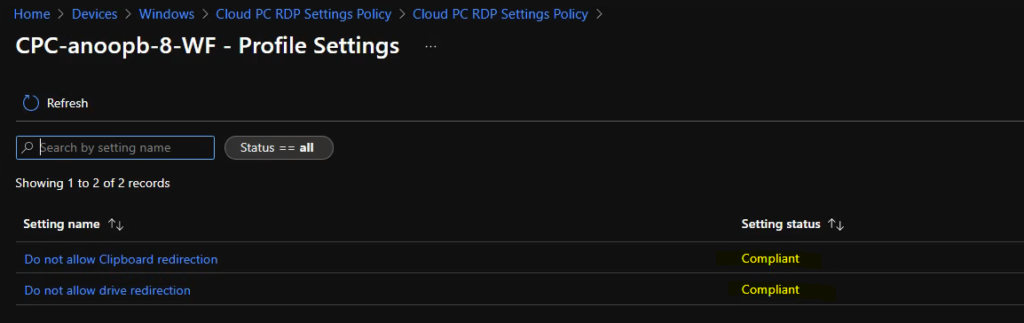
Summary of Cloud PC RDP Settings Policy
You can complete the policy creation process as explained above. As part of the review process in the RDP settings policy creation process for Cloud PC, you can review the settings that you have selected.
The settings catalog policy in Intune uses nothing but Administrative Templates similar to group policies and deploying this policy using the MDM channel. Path-> Windows Components > Remote Desktop Services > Remote Desktop Session Host > Device and Resource Redirection.
- Do not allow Clipboard redirection -> Enabled
- Do not allow drive redirection -> Enabled
Troubleshooting – Cloud PC RDP Settings Policy
I have manually initiated the Intune policy from the Company Portal application as explained in the previous Intune policy troubleshooting posts. You will have to go through the event logs to understand whether the policies are getting delivered to Cloud PC or not.
I have navigated to the following event log location and found the following event logs indicating that the Clipboard policy has arrived on the client’s PC. Now, you will need to understand why the Drive redirection policy has not arrived yet?
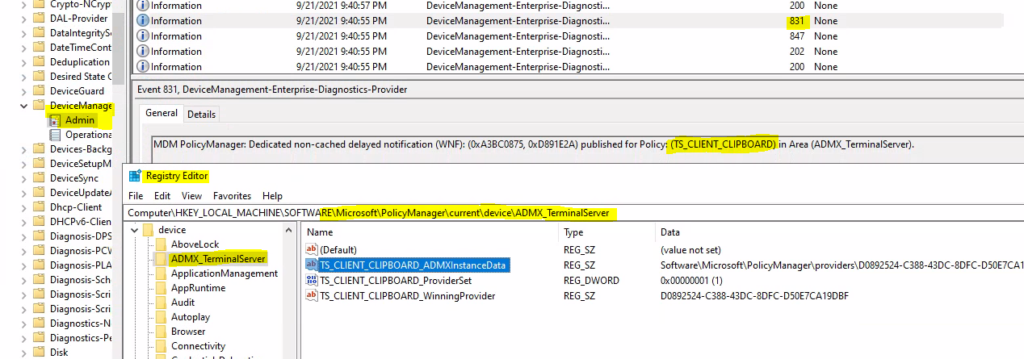
Event ID – 208 -> MDM Session: OMA-DM session started for EnrollmentID (D0892524-C388-43DC-8DFC-D50E7CA19DBF) with server: (MS DM Server), Server version: (4.0), Client Version: (1.2), PushRouterOrigin: (0xB), UserAgentOrigin: (0x8), Initiator: (0x0), Mode: (0x2), SessionID: (0x69), Authentication Type: (0x1).
Event ID – 814 -> MDM PolicyManager: Set policy string, Policy: (TS_CLIENT_CLIPBOARD), Area: (ADMX_TerminalServer), EnrollmentID requesting merge: (D0892524-C388-43DC-8DFC-D50E7CA19DBF), Current User: (Device), String: (), Enrollment Type: (0x6), Scope: (0x0).
Event ID – 831 -> MDM PolicyManager: Dedicated non-cached delayed notification (WNF): (0xA3BC0875, 0xD891E2A) published for Policy: (TS_CLIENT_CLIPBOARD) in Area (ADMX_TerminalServer).
Registry Entry that you can look into confirming whether the policy is enabled or not -Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PolicyManager\current\device\ADMX_TerminalServer
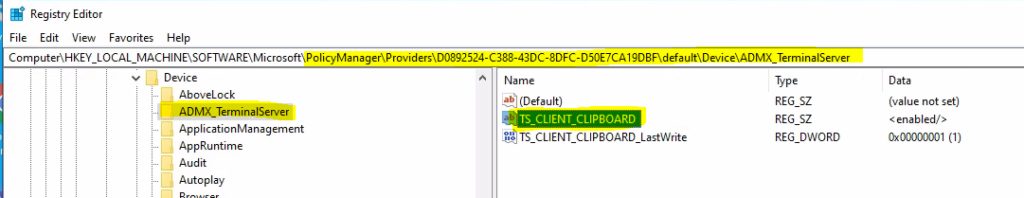
Also checked and confirmed the registry entries from the following path. It looks ok to me from the Clipboard redirection perspective. However, I didn’t find any clue about the Drive letter policy in this registry path related to ADMX Terminal Server.
- Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PolicyManager\Providers\D1E11663-BF69-4DD8-974A-BAD47E6EF433\default\Device\ADMX_TerminalServer
- TS_CLIENT_CLIPBOARD
You can also see the registry entries related to the ADMX Terminal server TS_Client Clipboard in the following registry path. However, there is no information about the Drive redirection policy setting!
Fix Intune Policy Conflict in Intune
You can perform the basic Intune policy conflict troubleshooting from the MEM admin center portal. One example is given below How To Start Troubleshooting Intune Issues from the server-side.
I have gone back to Intune portal and opened the settings catalog policy that I have created above to check the status of the policy deployment it shows there in the console.
Well, it shows Intune policy conflict issue now! What is this Intune policy conflict issue? Conflicts happen when two profile settings are the same. Let’s learn more about Intune policy conflict and resolution of policy conflicts from the RDP settings example itself.
For example – I tried to deploy and configure the same policy (Drive redirection), from different places, with different values, which creates a conflict between those two or more policy settings.
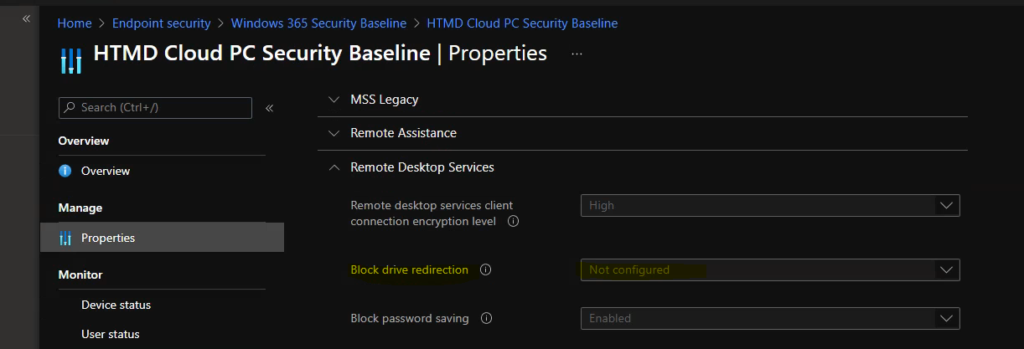
I made a Drive redirection policy from the settings catalog as explained above. I deployed the drive redirection policy already using Intune Windows 365 security baseline policy.
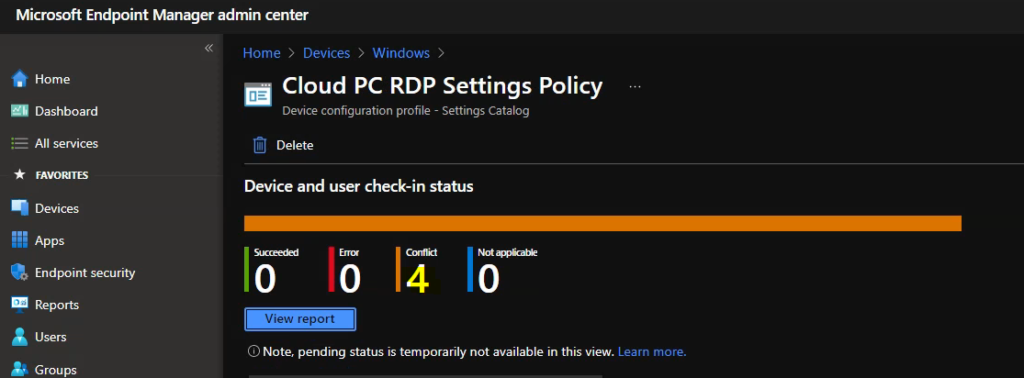
So, as I mentioned above, you can see the conflicting policies in two places. One in settings catalog and other policy in Endpoint security -> Windows 365 security baseline. I will need to manually fix this policy conflict issue from the MEM admin center portal.
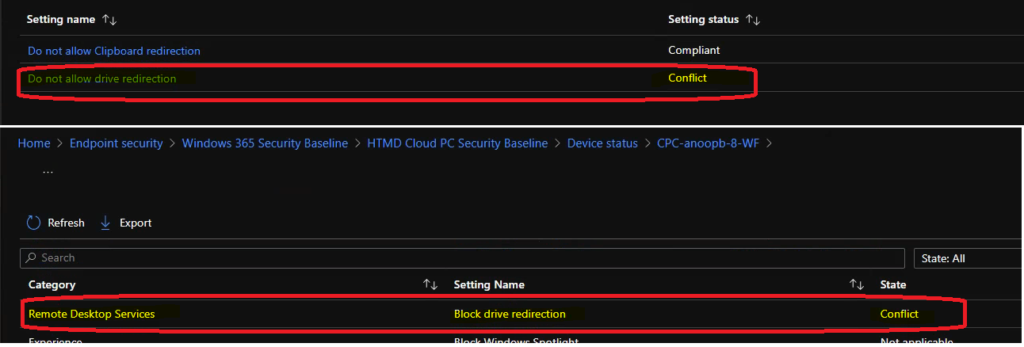
I have changed the Windows 365 security baseline policy configuration related to Remote Desktop Service -> Block Drive Redirection to NOT Configured, initiated the Intune policy sync from the company portal again and the changes delivered to the Cloud PC.
Event Log -> MDM PolicyManager: Set policy string, Policy: (DoNotAllowDriveRedirection), Area: (RemoteDesktopServices), EnrollmentID requesting merge: (D0892524-C388-43DC-8DFC-D50E7CA19DBF), Current User: (Device), String: (), Enrollment Type: (0x6), Scope: (0x0).
The registry details of the new Drive redirection configurations are available in a different place. It’s not the same registry path where the terminal server ADMX values are stored. It’s a bit confusing for me, and I don’t know the reason for the same.
- Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\PolicyManager\Providers\D1E11663-BF69-4DD8-974A-BAD47E6EF433\default\Device\RemoteDesktopServices
- DoNotAllowDriveRedirection
- DoNotAllowPasswordSaving
- PromptForPasswordUponConnection
After those changes explained above, you can see the policy reports show that the conflict is removed and both the RDP settings policy for Cloud PC applied successfully.
NOTE! – I have to log off and login back in to get the clipboard redirection policy working.