Hello Techies, Hope you are doing perfectly fine!!! Today, I wanted to discuss the New macOS Antivirus Policies using Intune service release 2308 or later for macOS devices. In case you missed our post covering how to configure Antivirus policy from scratch, check it here: How to Configure macOS Antivirus Policy Using Intune.
As mentioned above, in this post, we will only discuss the 9 additional settings added to the existing policies, which will only be applicable on Intune release version 2308 or later. If you are unsure about how to check the service release status on the Intune portal, check out Section How to Check Microsoft Intune Version in the post: Intune August Update 2308 New Features Improvements
In case you missed reading our last post, we’ve plugged it in here. The article Upgrade to macOS Sonoma and Intune Management covers everything you need to know about upgrading to macOS Sonoma and Intune Management.
We talk about which devices are eligible to get an upgrade to macOS Sonoma, how to install the public beta of macOS Sonoma, and all the cool features that make it more productive for techies like us. Plus, we’ve included details on the configuration profile settings that are only available for macOS Sonoma devices managed through Intune.
If you’re curious about managing macOS devices using the Intune MDM Platform, check out my posts here, which you might find helpful. We also had a video talk on how to restrict corporate macOS devices using Intune, and we discussed all the restriction settings and their usage. For example, you can disable AirDrop or iCloud to keep your data safe.
Before we get into the nitty-gritty of configuring antivirus settings, let’s take a moment to understand what antivirus policies are and how they can help IT Admins secure their devices. Essentially, Antivirus policies are a pack of different profiles from endpoint protection or device restriction categories, however, they consist only of antivirus-related settings.
In our case, we are considering the Microsoft Defender as the antivirus protection. Antivirus policies can prevent cyberattacks on devices and secure organizational data. The Antivirus policy replaces the traditional method of configuring settings in .plist files.
Note! Plist files allow saving macOS app preferences. Occasionally they may need to be deleted to restore proper functionality to an app experiencing conflicts.
Antivirus policies are the backbone of device security, safeguarding against malicious software and other threats. To ensure the organisation-procured corporate devices are optimally protected, it’s critical to configure these policies correctly and avoid unwanted consequences.
Before deploying any antivirus policy in Intune, we must first check for the necessary prerequisites. Let’s delve deeper into the purpose and importance of antivirus policies and understand why precise configuration is essential in keeping our devices safe and secure.
Why is It Important to Configure macOS Antivirus Policy Settings?
In today’s world, Cyber attackers are always on the lookout for vulnerable devices that can get easily infected with malware, allowing them to steal users’ data and compromise data privacy. So to prevent the devices affected from attackers and keep the device secure, Admins need to install a reliable security program that should protect the device, irrespective of OS, from malicious software, including viruses, worms, Trojans, and spyware.
For organisations with organisation-procured macOS devices, anti-virus protection is an essential initial step that should be taken alongside other configurations like Firewall and Disk encryption to ensure the safety and security of your sensitive data.
Thankfully, Apple has designed its hardware and software with advanced technologies that work together to keep your device running smoothly and securely. Update your macOS to the latest version for the best protection against cyber threats and malware.
Pre-Requisites to deploy macOS Antivirus policy
Before proceeding, please ensure that you have completed the pre-requisite check. To do this, check the Intune service release version in the portal and verify that all antivirus policies are available. Additionally, please ensure the steps mentioned below:
- All macOS versions are supported.
- Microsoft Defender must be installed on the device.
How to Configure macOS Antivirus Policy using Intune
Now that we understand the importance of configuring the antivirus policies and their pre-requisites, the next step is to create and deploy an antivirus policy, also before creating a policy, we must ensure to have the required access to the Intune Portal and then Follow the below-mentioned steps:
- Sign in to the Microsoft Intune Admin Center https://endpoint.microsoft.com/.
- Select Endpoint Security > under Manage, and select Antivirus. Click on Create Policy.
- Select Platform – macOS, Profile – macOS Defender Antivirus(Preview), and Click on Create.

After clicking on Create, Provide the Name of the Profile or Antivirus policy along with a detailed description and click Next to move further.

Under the Configuration settings tab, select settings as defined by the organization standards.
Here I have only configured the additional or new settings available after the Intune release 2308 or later.
| Configuration Setting | Description | Value |
|---|---|---|
| Degree of parallelism for on-demand scans | If enabled, this setting performs the degree of parallelism for on-demand scans, so need to provide the number for on-demand scans. | Toggle on/off Value (in numbers) |
| Enable file hash computation | This setting enables MS Defender to compute hashes for files it scans, which improves the accuracy of Custom Indicator matches, however may impact the device performance. | Enable / Disable |
| Run a scan after definitions are updated | This setting specifies whether to start scanning after new security intelligence updates are downloaded on the device, however increase in scans may impact device performance. | Enabled / Disabled |
| Scanning inside archive files | If set as true, MS Defender will unpack archives and even scan files inside them. if set as false, it will only scan archives and move further. | True / False |
| Enforcement level (under Network Protection) | If set to disable, it allows all-network related changes on the device, however, if set to audit, it allows and logs all the network related changes on the device. Once set to block, it blocks all the Networking change operations on the device. | block / audit/ disabled |
| Enforcement level (Under Tamper Protection) | If set to disable, it allows all app installation, however, if set to audit, it allows and logs all the app installation and file and folder access on the device. Once set to block, it blocks all the tampering operations on the device. | block / audit/ disabled |
| Control sign-in to consumer version | If enabled, it allows the end user to sign in consumer version of MS Defender | enabled / disabled |
| Show/hide status menu icon | This setting, if enabled, shows the MS Defender icon on the top right corner of the screen. | Disabled / enabled |
| User-initiated feedback | If enabled, users can submit feedback to Microsoft by going to Help > Send Feedback | enabled / disabled |
For the sample profile, I have selected values as mentioned below.
| Configuration Settings | Value |
|---|---|
| Degree of parallelism for on-demand scans | Configured, Value : 2 |
| Enable file hash computation | False |
| Run a scan after definitions are updated | Enabled |
| Scanning inside archive files | True |
| Enforcement level (under Network Protection) | audit |
| Enforcement level (Under Tamper Protection) | audit |
| Control sign-in to consumer version | enabled |
| Show/hide status menu icon | Disabled |
| User-initiated feedback | enabled |
Below are the configuration settings I have used. You can set the configurations according to your requirements.

On the next page, Scope tags are filtering options provided in Intune to ease the admin jobs. In the scope tag section, you will get an option to configure scope tags for the policy. Click on Next.

On the next page, select Assignments group (Included groups and Excluded groups) and click Next.
Assignment Group: It determines who has access to any app, policy, or configuration profile by assigning groups of users to include and exclude.

On the Review+create page, please review if any settings need to be changed, or else go ahead and create the policy.

As we discuss the additional Antivirus policy configuration, Administrators can follow the steps below to edit it in an existing Antivirus policy.
- Ensure the Intune Portal is running on Intune release 2308 or later
- Go to Endpoint Security > Antivirus
- Search for the existing policy, and click on the profile to edit.
- Click on properties > Configuration Settings > Edit
- Now you can configure the new settings and click on save.

Although the policy already exists on the end-user device, as we have made new modifications, it should be reflected upon the next sync on all the devices.
Policy Deployment– Monitoring on Intune Portal
Once the Antivirus policy is created, it will take a few minutes to get pushed to the targeted devices in the selected group; also, to view the push status on the list of targeted devices, we can check as per the below steps.
To see all the device statuses, Navigate to Endpoint Security> under Manage, and select Antivirus. Click on the deployed policy name, and on the Overview page, you can find the list of devices under categories such as below.
- Succeeded
- Error
- Conflict
- Not Applicable
- In Progress

Once you click on the view report button, you can see the list of devices along with their details Device Name, Logged-in User, Check-in Status and Last check-in time.

Also, we can view the two different types of reports, and you can quickly check the update as devices/users check-in status reports.
Device assignment status, This report will show the list of targeted devices under the configuration profile, including devices in pending policy assignment status.
Per settings status, This report will show the configuration status of each set for this policy across all devices and users.

Here’s how to export the Intune setting catalogue Profile report from the Intune portal. You have two options to navigate to the compliance policies node either you can navigate to the Devices node or Endpoint Security, Intune Settings Catalog Profile Report.
Conflicts while setting up Values
As IT administrators, we have the power to create multiple profiles with identical settings or values. However, this can lead to errors and conflicts, which can hinder the performance of end-user devices impacting end-user experience. To avoid such issues, it is crucial to ensure that the settings are varied, and not identical.
For instance, We already have a configuration profile for Tamper Protection with the enforcement level set to block, and again when we try to configure the antivirus policy with the enforcement level set to audit, it results in a conflict and given error. We simply removed the configuration in the antivirus setting to remove the error, which fixed the issue.
If you have not checked my post on what tamper protection is and how to enable it, check it here: Easy Method to Enable Tamper Protection for macOS using Intune

- Configure FileVault Encryption For MacOS Devices Using Intune
- Configure macOS Compliance Policy in Intune for Devices
Monitor Antivirus Policy on macOS
Once the Policy gets pushed to the list of macOS devices as part of the assignment group, it may take a few minutes to reflect on the end user’s device. Once the user successfully logs in to the device, we can follow the steps below to check the profile status.
- Click on the Apple icon at the top-left corner.
- Select System Settings from the list of options.
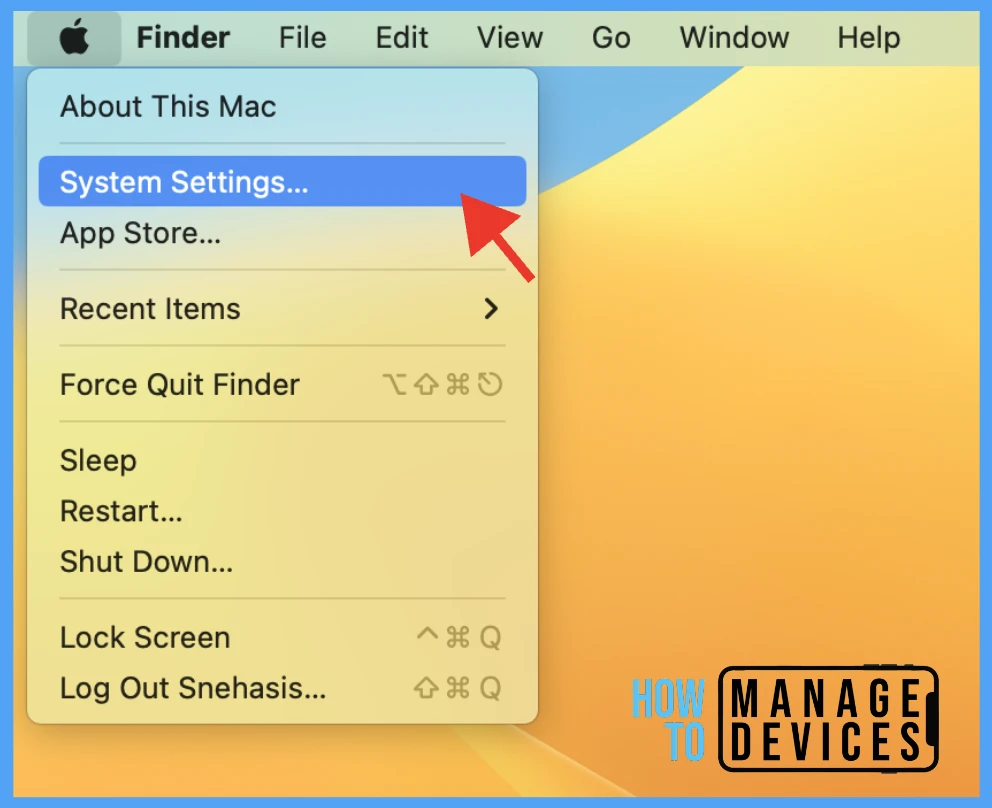
Go to Privacy & Security > Profiles > you can see profiles deployed related to the Antivirus setting on the Mac.

To view the settings in the profiles, double-click and open them to view the details. Here you can see the detailed status of the applied antivirus protection policy.

Conclusion
To ensure the protection of company resources, organizations must prioritize implementing Antivirus policies as a mandate for all organisation-procured devices, irrespective of OS platforms. These policy helps to secure network activity on the user’s device.
Author
Snehasis Pani is currently working as a JAMF Admin. He loves to help the community by sharing his knowledge on Apple Mac Devices Support. He is an M.Tech graduate in System Engineering.
