In this post, let’s see how to configure FileVault Encryption Settings for macOS Devices using Intune. We will give a quick overview of how and why it is important to create FileVault encryption settings for macOS devices. Also, we will discuss the different settings that can be configured while creating a custom profile.
Our last blog post discussed creating a Device restriction profile in Intune. compliance policies, configuration profiles, and Conditional Access policies are the mandatory steps for any organization to protect their resources before providing access to employees for corporate applications usage on Intune.
Microsoft Intune includes many built-in settings to control different features on devices. We will create a custom FileVault encryption profile. These profiles include FileVault settings for organizations to control on company-enrolled macOS devices.
The FileVault Encryption Setting can be created in two ways, You can either navigate to the Configuration profiles or Endpoint security inside Intune Admin portal.
- Endpoint security policy for macOS FileVault. The FileVault profile in Endpoint security is a focused group of settings that is dedicated to configuring FileVault.
- Device configuration profile for endpoint protection for macOS FileVault. FileVault settings are one of the available settings categories for macOS endpoint protection.
Why Should We Create a Disk Encryption Settings Profile
Let’s understand what a disk encryption setting means exactly and how exactly Filevault works on a Mac.
Simply, Disk encryption is a technology that protects information by encoding it into unreadable data that cannot be understood easily by users. This method encrypts every bit of data stored on a disk to prevent unauthorized access to data storage.
If we store any sensitive files and information in a MacBook, it uses the FileVault encryption feature to protect the data stored on the disk. Also, FileVault encodes data on the disk startup, so unauthorized users can’t access organization data. To ensure security, other security features are also turned on when we turn on FileVault on a Mac.
The recovery key is an alphanumeric code created and saved for use in case we forget the company-owned device’s login password, which helps decrypt data saved on the disk. It can be accessed from Intune portal once the macOS device is enrolled in Intune.
- Should you upgrade to Mac OS Ventura v13 managed using Intune
- New System Settings in macOS Ventura v13 and Intune Software Update Configs
How to Configure FileVault Disk Encryption Settings for Intune-enrolled macOS Devices
To create a disk encryption profile, we must ensure to have the required access to the Microsoft Intune Portal. Follow the steps mentioned below to create a profile in Intune portal for macOS devices.
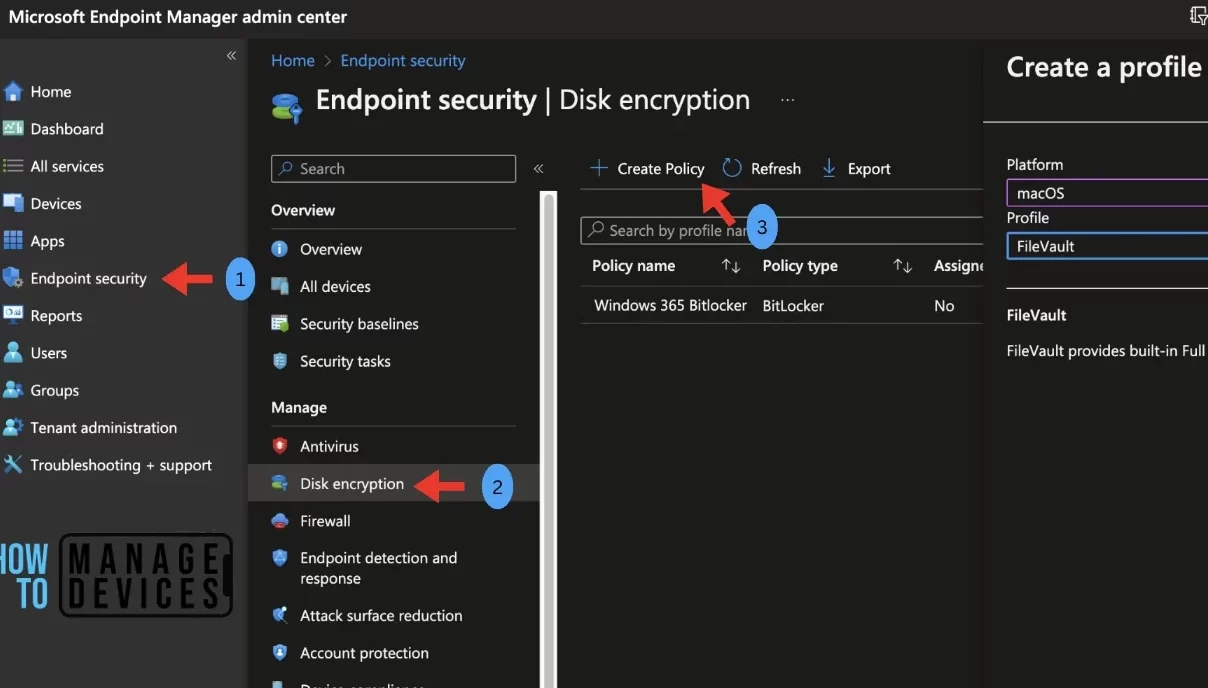
- Sign in to the Microsoft Intune admin center https://endpoint.microsoft.com/.
- On the left sidebar, select Endpoint security > under Manage, select Disk encryption.
- The list of existing profiles will reflect on the right side. To create a new policy, click on Create Policy.
- Select the categories,
- Platform – macOS
- Profile – Filevault
- Click on Create.
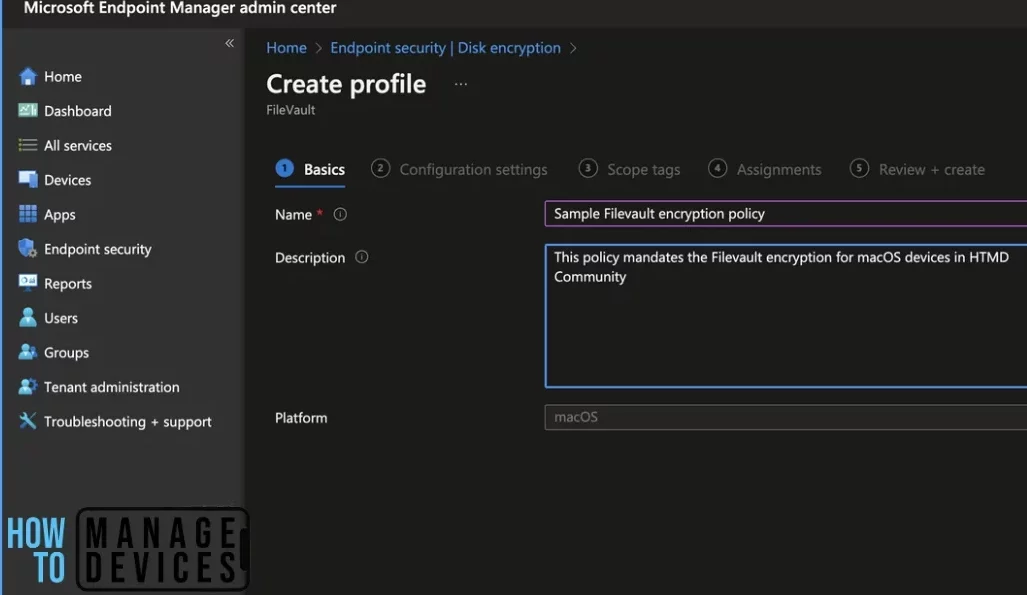
Once you click on Create button from the above page, Provide the Name and Description and click on Next.
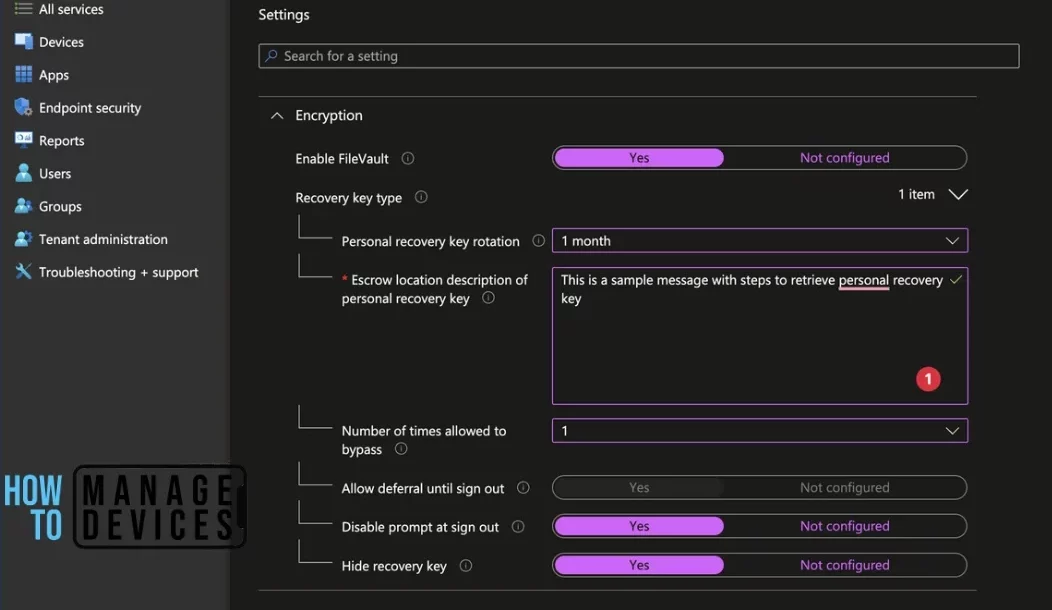
Under the Configuration settings tab, Turn on the setting by selecting Enable Filevault: Yes ( this setting will enable the FileVault on the Mac once the policy is deployed on the next user login). Under the recovery key type, select settings to determine which type of key should be enabled for the organization
- Personal recovery key rotation: (how frequently you want the key to be auto-generated on the device)
- Escrow location description of personal recovery key : (here, we can add a message to help users with steps to retrieve the recovery key for their device)
- Number of times allowed to bypass : (We can set the number of times a user can bypass the prompt to encrypt their device using Filevault)
- Allow deferral until sign out : (Allows users to defer or skip the prompt until sign out)
- Disable prompt at sign out : (Set to disable in case the prompt appears for FileVault encryption)
- Hide recovery key : (Intune Administrators are allowed to view personal recovery keys for encrypted company-owned macOS devices enrolled in Intune)
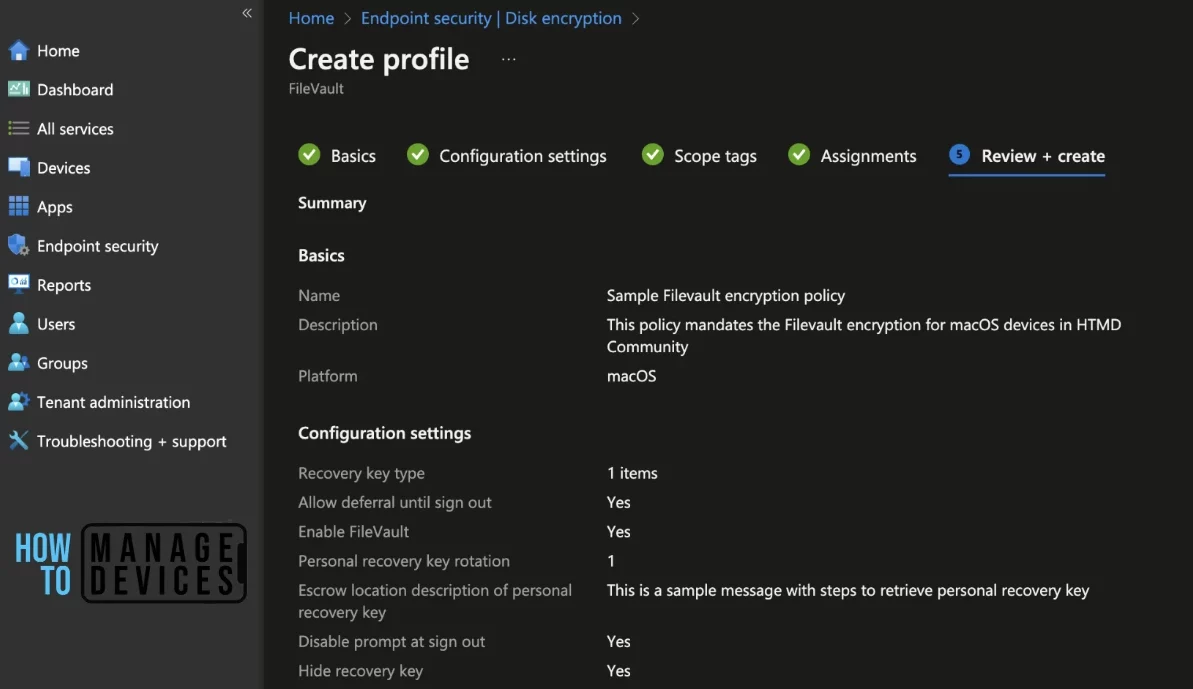
Here we have selected the below encryption settings;
Personal recovery key rotation: 1 month
Escrow location description of personal recovery key: This is a sample message with steps to retrieve Personal recovery key
Number of times allowed to bypass: 1
Allow deferral until sign-out: Yes
Disable prompt at sign out: Yes
Hide recovery key: Yes
On the next page, Scope tags are filtering options provided in Intune to ease the admin jobs. In the scope tag section, you will get an option to configure scope tags for the policy. Click on Next.
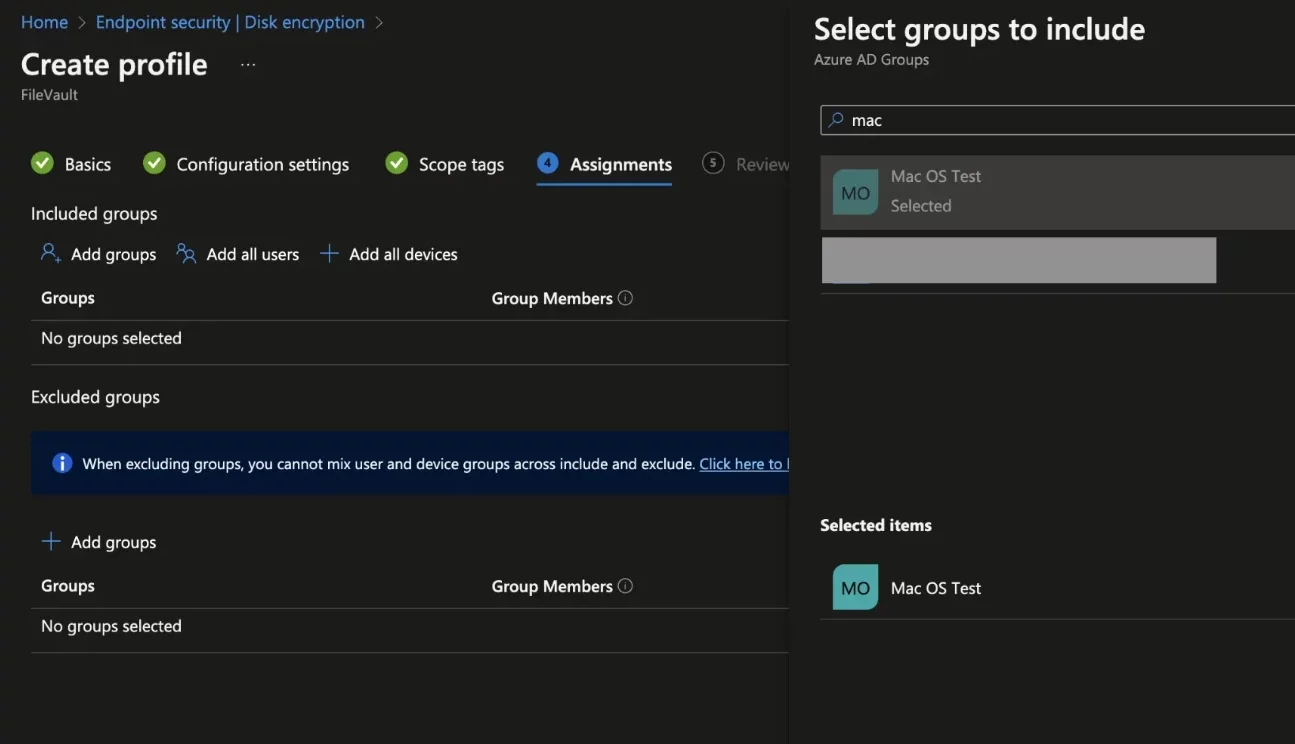
On the next page, select Assignments group (Included groups and Excluded groups) and click Next.
Assignment Group: It determines who has access to any app, policy, or configuration profile by assigning groups of users to include and exclude.
On the Review+create page, please review if any settings need to be changed, or else go ahead and create the policy.
Once the FileVault encryption policy is created, it will take a few minutes to get pushed to the mentioned devices in the selected group; also, to view the deployment status on the list of targeted devices, we can check as per the below steps.
- To see all the device statuses, Navigate to Endpoint Security> under Manage, and select Disk encryption. Click on the FileVault encryption policy, and on the Overview page, you may see the Profile deployment status.
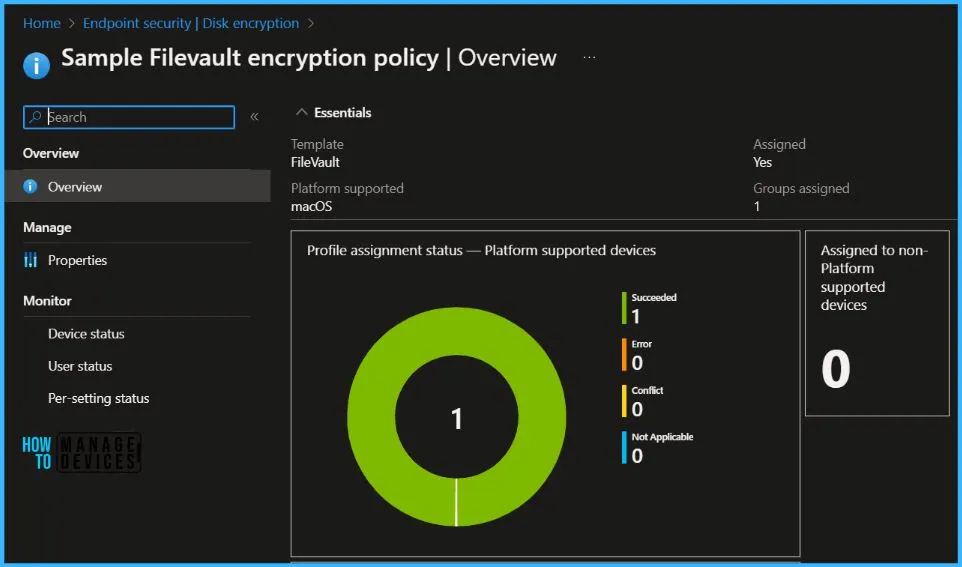
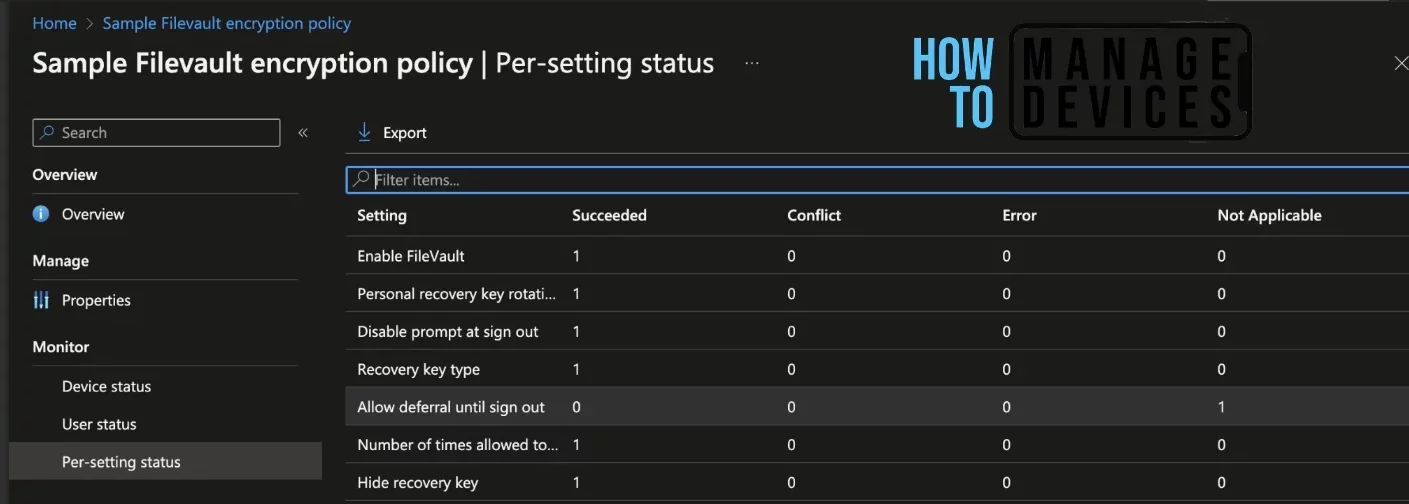
Also, we can view the per user, per device, and per setting status under every FileVault encryption policy.
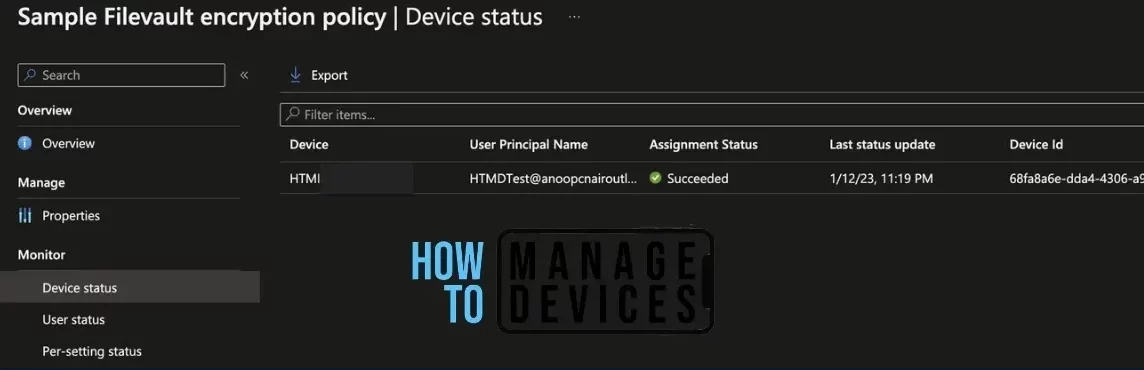
Device Status: On this page, we can see a list of devices that the FileVault encryption policy has been pushed and how many of them are shown as Succeeded, Conflict, Error, and Not-Applicable.
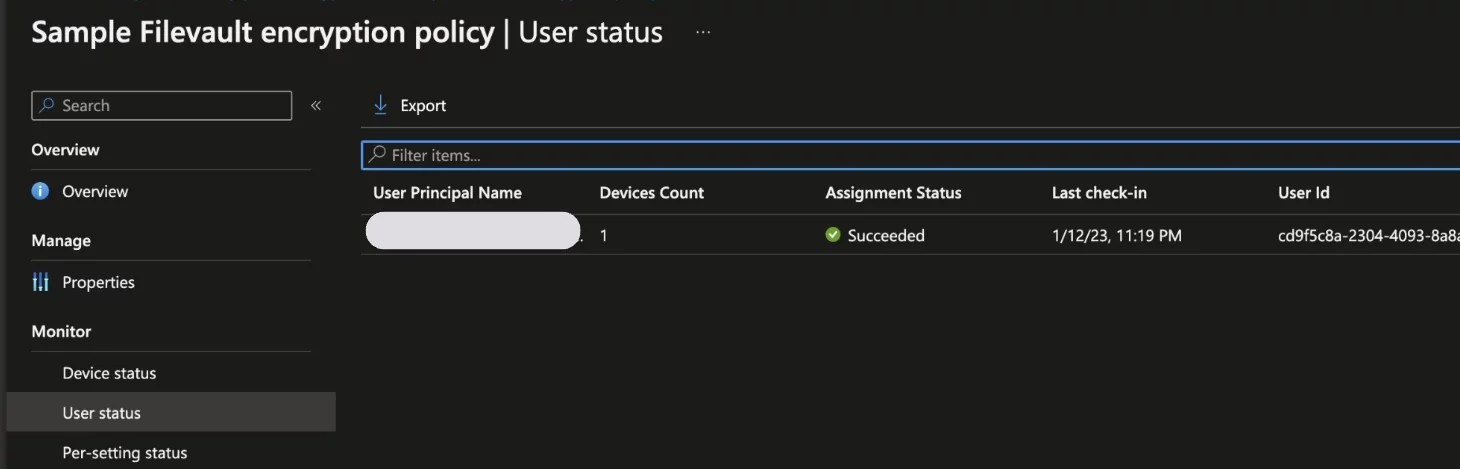
User Status: On this page, we can see a list of users associated under Intune and push with the encryption setting policy and how many of them are showing as Succeeded, Conflict, Error, and Not-Applicable.
Per Setting Status: On this page, we can see a list of encryption Settings pushed to a list of devices; we can view the status as Succeeded, Conflict, Error, and Not-Applicable for each of the settings.
If Encryption is not enabled on a device after deploying a policy, check the encryption report to see if the device meets the prerequisites.
Intune provides a built-in encryption report that presents details about the encryption status of devices, across all your managed devices. The encryption report shows common details across the supported devices you manage, Intune Device Encryption Status Report for deploying disk encryption using Intune.
- Enroll macOS in Intune with Step by Step Guide
- Configure macOS Compliance Policy in Intune for Devices
How to Check Deployed FileVault Disk Encryption Setting on macOS
Once the Profile gets pushed to the list of client macOS devices as part of the assignment group, it may take a few minutes to reflect on the end user’s device. As per the settings, it will be activated on the next user logon, so when the next time user logs off and log in to the device below prompt should appear.
Please click on Enable Now button to enable FileVault on the device.

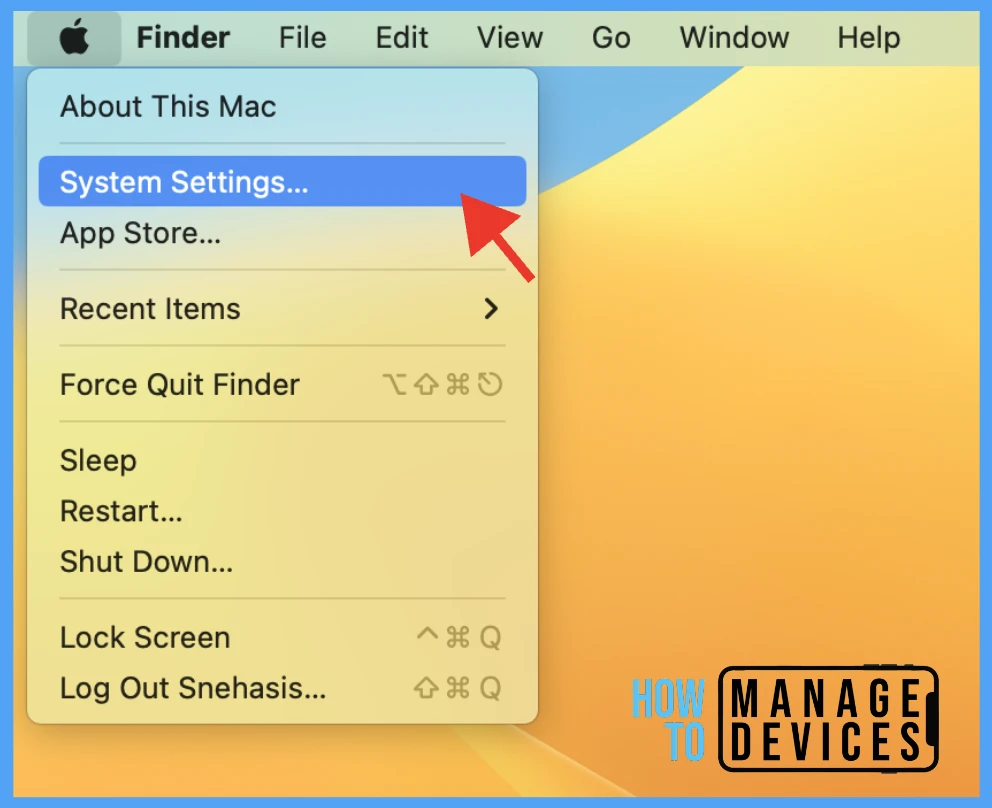
Once the user successfully logged in to the device, we can follow the steps below to check the profile status.
- Click on the Apple icon at the top-left corner.
- Select System Settings from the list of options.
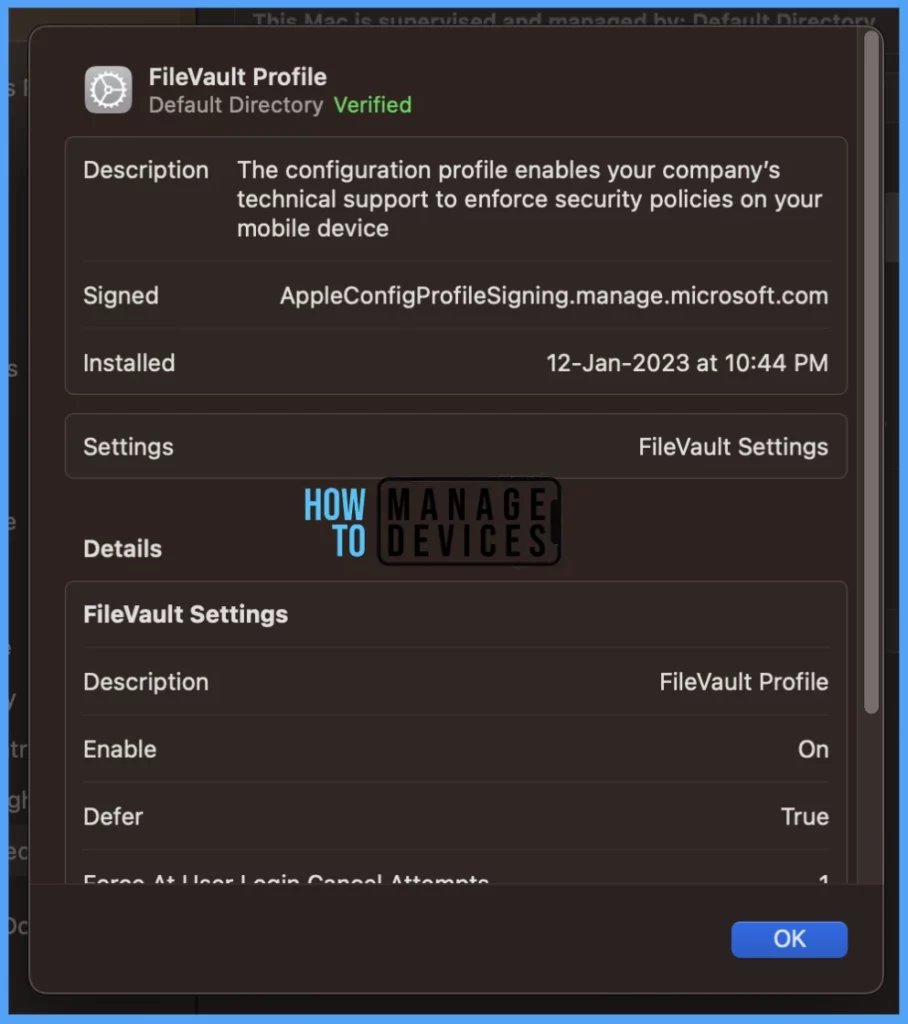
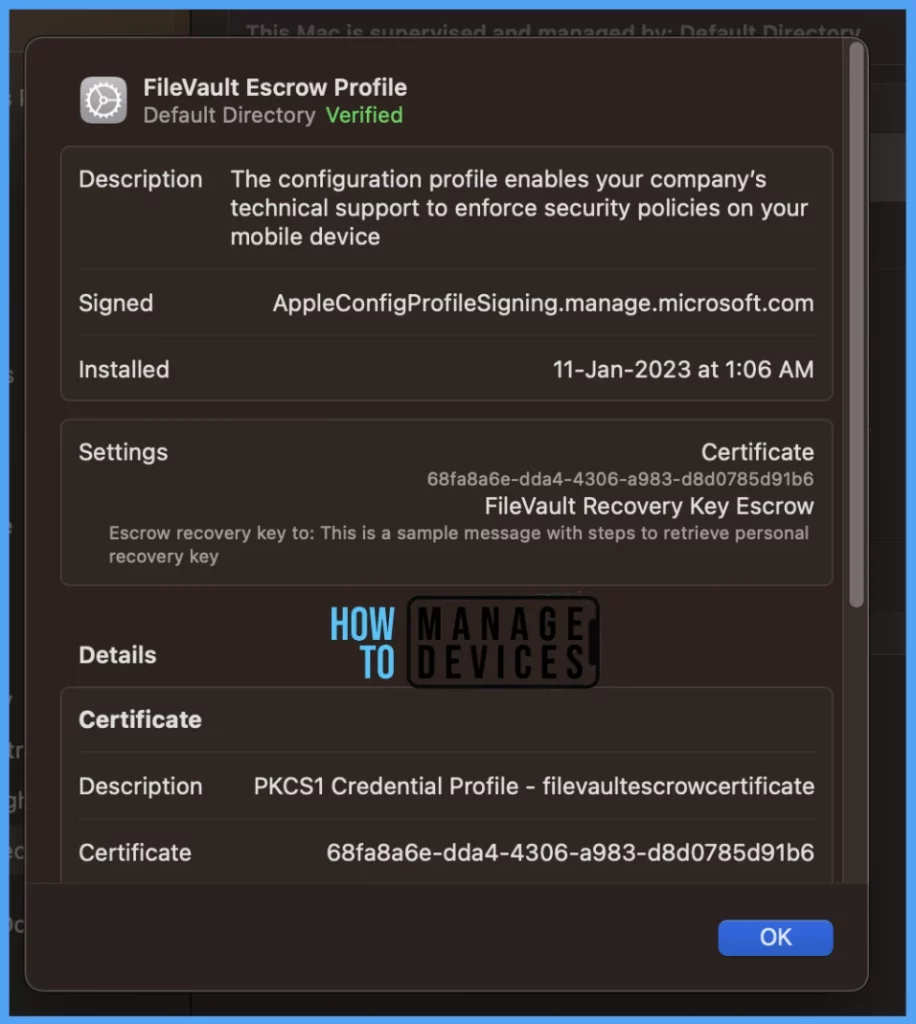
Go to Privacy & Security > Profiles > you can see 2 profiles deployed related to FileVault Encryption on the mac.

To view the settings/restrictions in the profiles, double-click and open them to view the details. Here you can see FileVault profile has been applied.
Your groups will receive your profile settings when the devices check in with the Intune service the policy applies to the device. Here you can see FileVault Escrow profile has been applied.
Conclusion
Organizations, as a mandate, should push FileVault encryption profiles to all company-owned macOS devices to secure company data on the device as per Organizations’ policy, ensuring data leakage and access of unauthorized users to company resources.
Author
Snehasis Pani is currently working as a JAMF Admin. He loves to help the community by sharing his knowledge on Apple Mac Devices Support. He is an M.Tech graduate in System Engineering.


hi,
did you try to apply this profile on already encrypted MacOS devices ? it will end with error and it is not re-encrypted or it is not take control over the existing recovery key. Have you some fix for that ?
Hi,
I have followed above the steps for FileVault Encryption for macOS devices. But it’s not succeed.
Checked the status in per-setting status as below error:
Enable FileVault
Disable prompt at sign out
Allow deferral until sign out
Number of times allowed to bypass
Hide recovery key