Hey there! In today’s post, I’m excited to help you Setup Wi-Fi Profile for macOS devices using Intune MDM Platform. We’ll go through the process of understanding the types of Wi-Fi profiles Intune support and their purposes. We’ll publish a sample Wi-Fi profile to make things easier, so Let’s get started!
If you haven’t checked out, Last week, we published an article on Device Restriction Settings for macOS Offered by Intune, It’s a helpful piece covering all the different types of restriction settings available in Intune for the macOS platform. We even included a sample article that showcases many of these settings.
It’s important to note that many people work from home post-COVID. However, some users may still need to visit the office premises two or three times a week. When they do go to the office, it’s crucial that they have a stable and smooth Wi-Fi connection.
Also, Access to the internet on organisation-managed devices must be restricted, and site restrictions should be implemented to prevent malware infiltration. So IT Admins should create a policy to avoid allowing connection to any harmful sites. Organizations must use a proxy server or file to filter out unauthorized connections and only allow access to approved sites on managed devices. Failure to comply with these security measures can result in severe consequences.

What is a Wifi Setting and what Types Supported by Intune
In simple words, Wi-Fi (known as Wireless Fidelity)or Wireless LAN is a device using which users can connect to the internet wirelessly from anywhere within a location without physically connecting to the device. It has a standard called IEEE Standard (802.11) that works in two frequency ranges: 2.4GHz and 5GHz.
Although both bands serve the same purpose, they have some technical differences. The 2.4GHz band has a wider coverage area but is slower than the 5GHz band, which provides faster speeds but has a smaller coverage area. Many businesses establish wireless networks in their offices, allowing business devices to connect. To save time, Intune can be used to configure and distribute Wi-Fi settings automatically.
To better understand Wi-Fi settings, it’s important to know the two types supported by Wi-Fi Profile supported by Intune, Basic and Enterprise. A basic Wi-Fi Profile uses WPA/WPA2 to secure the connection. It saves the Wi-Fi name and password (pre-shared key) in the device’s settings, enabling automatic connection when the user is in the office location without needing to enter the password again.
Whereas Enterprise Wi-Fi settings utilize the Extensible Authentication Protocol (EAP) to authenticate Wi-Fi connections. It is commonly used by organisations to enable the use of certificates for secure authentication and to configure additional security options.
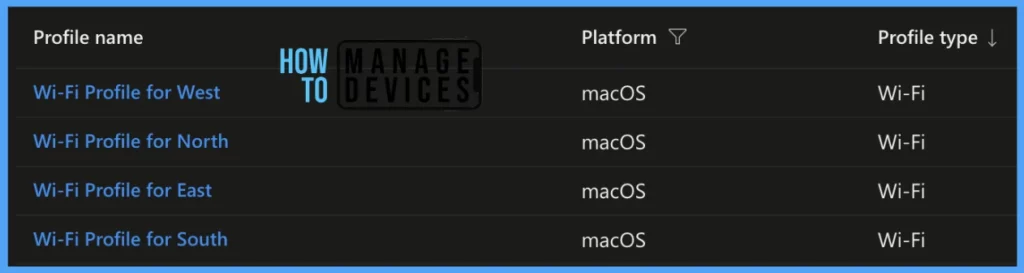
In today’s article, we will focus on smaller organisations, where Basic Wi-Fi Profile can be used, and in the next article, we will cover setting for Enterprise Wi-Fi Profile. So as a sample, we are considering an organisation that has 4 Offices across India in cities like East (Kolkata), West (Mumbai), North (Delhi), and South (Bangalore).
How to Setup Wi-Fi Profile for macOS
To create a basic Wi-Fi profile in the Intune portal, it’s important to ensure that you have the necessary access to the portal. Here are the steps you need to follow when creating a configuration profile for setting up Wi-Fi.
- Sign in to the Microsoft Intune admin centre https://intune.microsoft.com/.
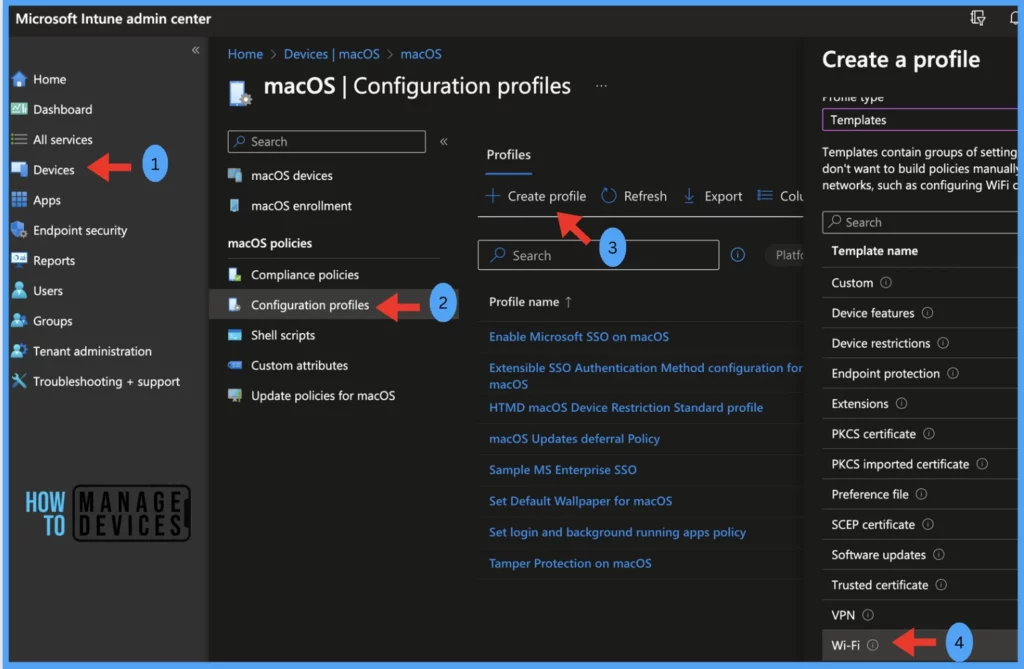
- On the left sidebar, select Devices > select macOS > Configuration profiles (under macOS policies), To create a new profile, click on Create Profile.
- Select the correct categories for Profile creation as per below.
| Platform | Profile Type | Template Name |
|---|---|---|
| macOS | Templates | Wi-Fi |
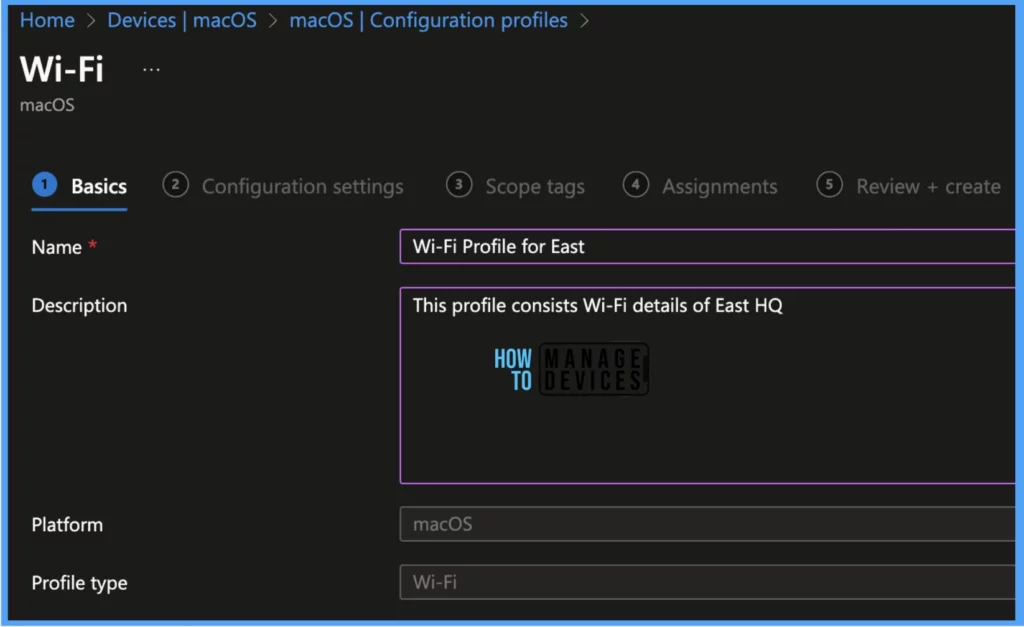
Under Basics, Provide the Name of the profile and a detailed Description and click Next.
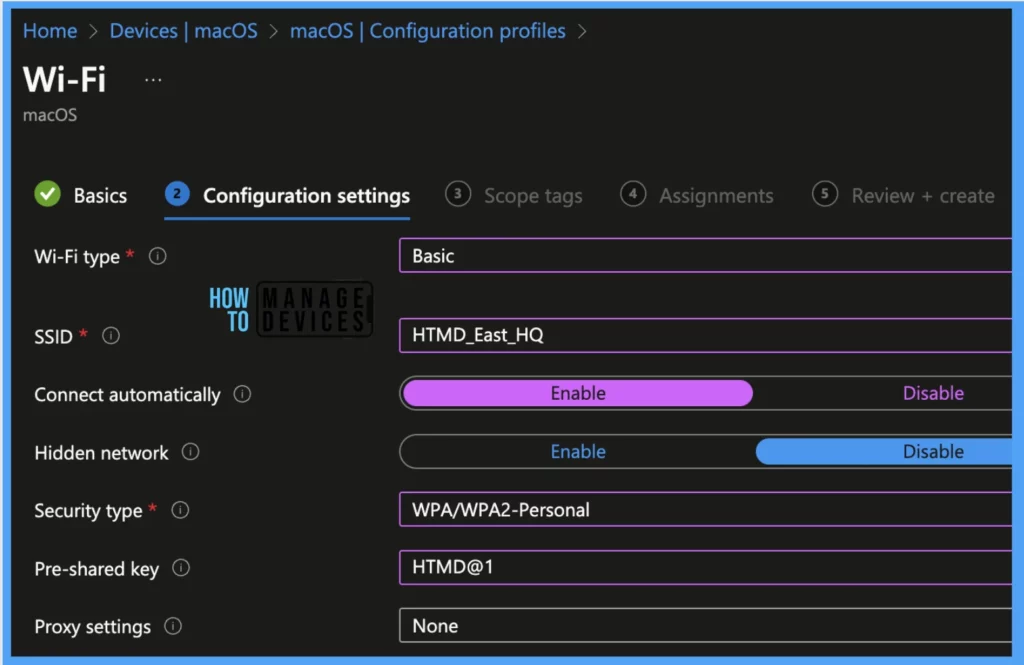
Under Configuration settings, there are 7 settings, let us configure each of them accordingly.
| Configuration Settings | Description | Value |
|---|---|---|
| Wi-Fi type | Currently, we are opting for Basic. | I. Basic II. Enterprise |
| SSID (Service set identifier) | It defines the name of the wireless network the device needs to connect to | Provide Wi-Fi Name |
| Connect automatically | I. Select Enable, the device automatically connects to the network when it is in range. II. Select Disable, so the user needs to click on Connect to join the network manually. | I. Enable II. Disable |
| Hidden network | I. If we select Enable, the SSID won’t be visible to the end user. II. In case of disable, it will be shown on the device | I. Enable II. Disable |
| Security type | I. If the network is an unsecured or open network, select Open II. If the Wi-Fi has the password configured, select WPA/WPA2 – Personal and provide the password as a Pre-shared key. III. If Wi-Fi is not secured as WPA2, Select WEP and connect to the Wi-Fi without a password | I. Open (no authentication) II. WPA/WPA2 – Personal III. WEP (Wired Equivalent Privacy) |
| Proxy settings | I. proxy settings are not required II. Admin needs to provide Proxy server details ( IP address and Port number) III. Admin must provide Proxy server URL containing the configuration file. | I. None II. Manual III. Automatic |
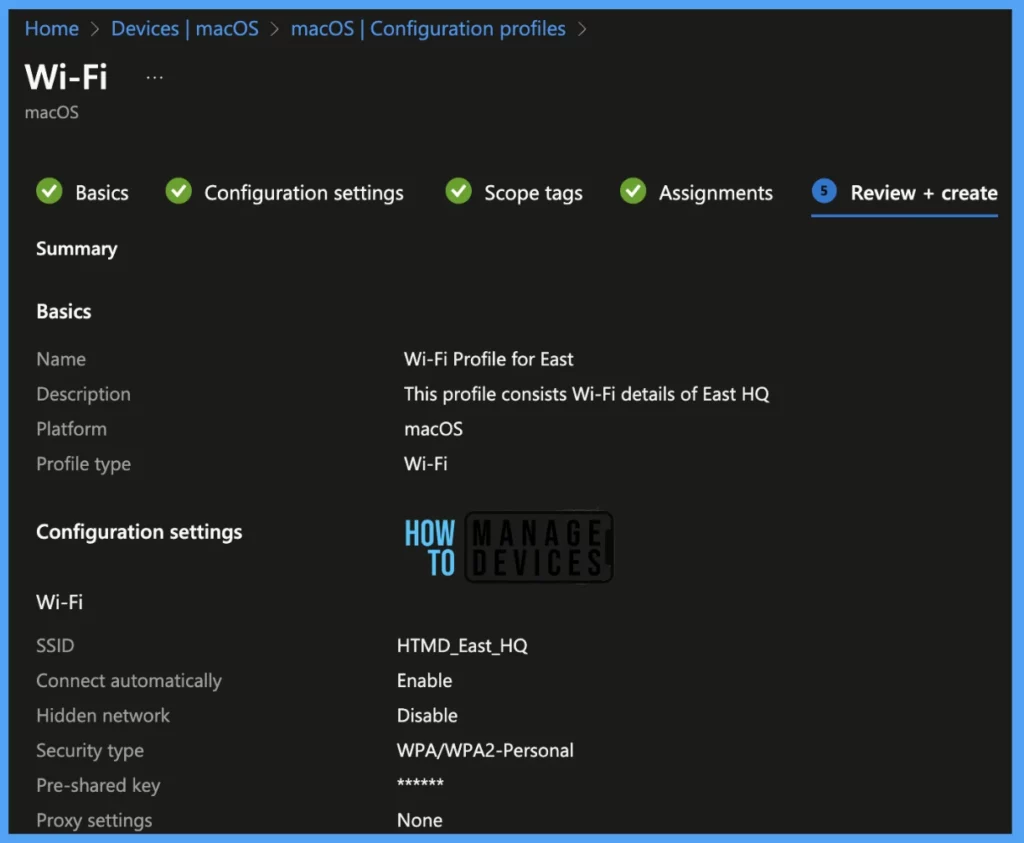
For HTMD, we have set up the configuration as per the below details. But you can choose the settings according to your requirement.
| Configuration Setting | Value |
|---|---|
| Wi-Fi Type | Basic |
| SSID | Wi-Fi Name |
| Connect automatically | Enable |
| Hidden Network | Disable |
| Security Type | WPA/WPA-2 Personal |
| Pre-Shared Key | Wi-Fi Password |
| Proxy Settings | None |
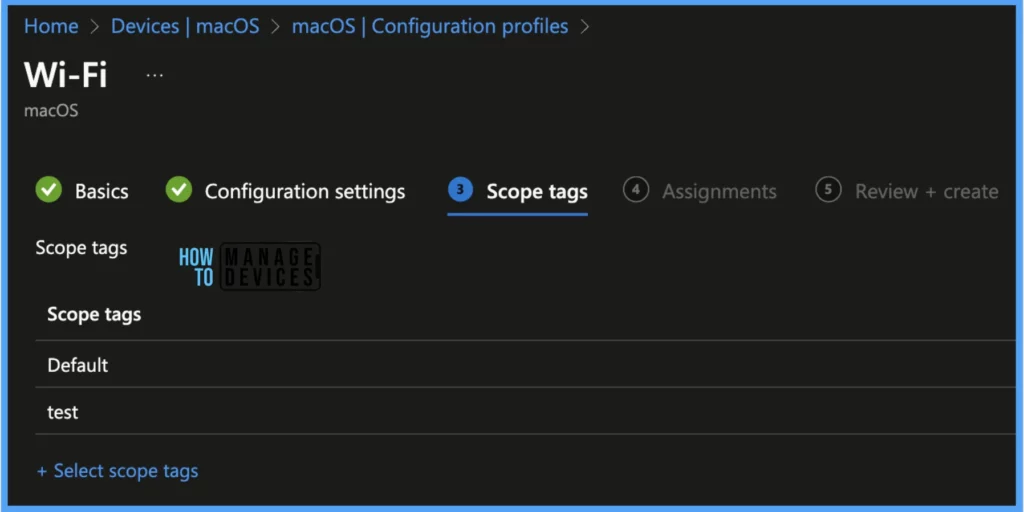
Scope tags are filtering options provided in Intune to ease the admin jobs. In the scope tag section, you will get an option to configure scope tags for the policy. Click on Next.
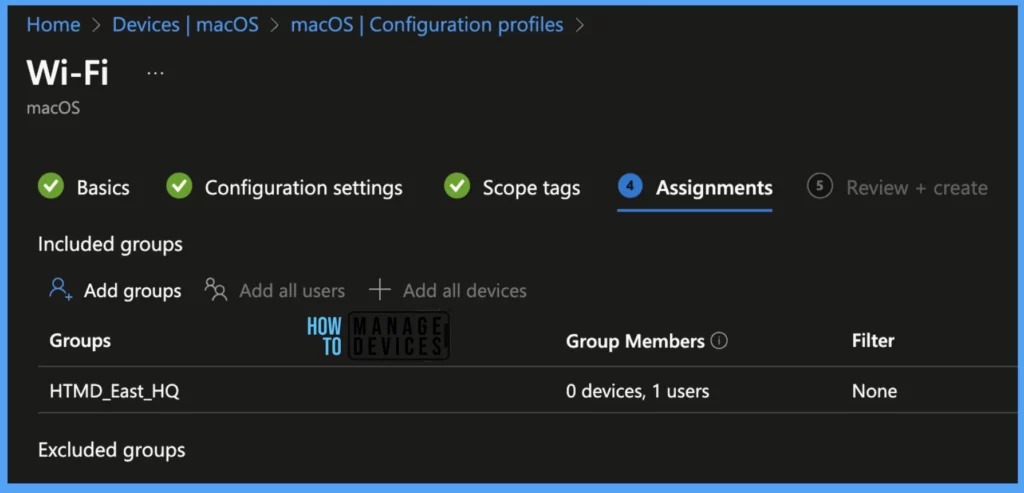
The assignment Group determines who has access to any app, policy, or configuration profile by assigning groups of users to include and exclude. Select Assignments group (Included groups and Excluded groups) and click Next.
On the Review+create page, please review if any settings need to be changed, or else click the Create button.
Same way, we have created 3 more configuration profiles for other HQ locations as well. Now that the Groups are created, and users are assigned, it takes a couple of minutes to get pushed to the targeted devices in the selected group.
Intune Report to View Setup Wi-Fi Profile Status
IT Admins can monitor the deployment status of each profile on the list of their targeted devices in the ways below, by navigating to Devices > Configuration Profiles > Select the Profile, and you can find the list of devices under categories such as below.
- Succeeded
- Error
- Conflict
- Not Applicable
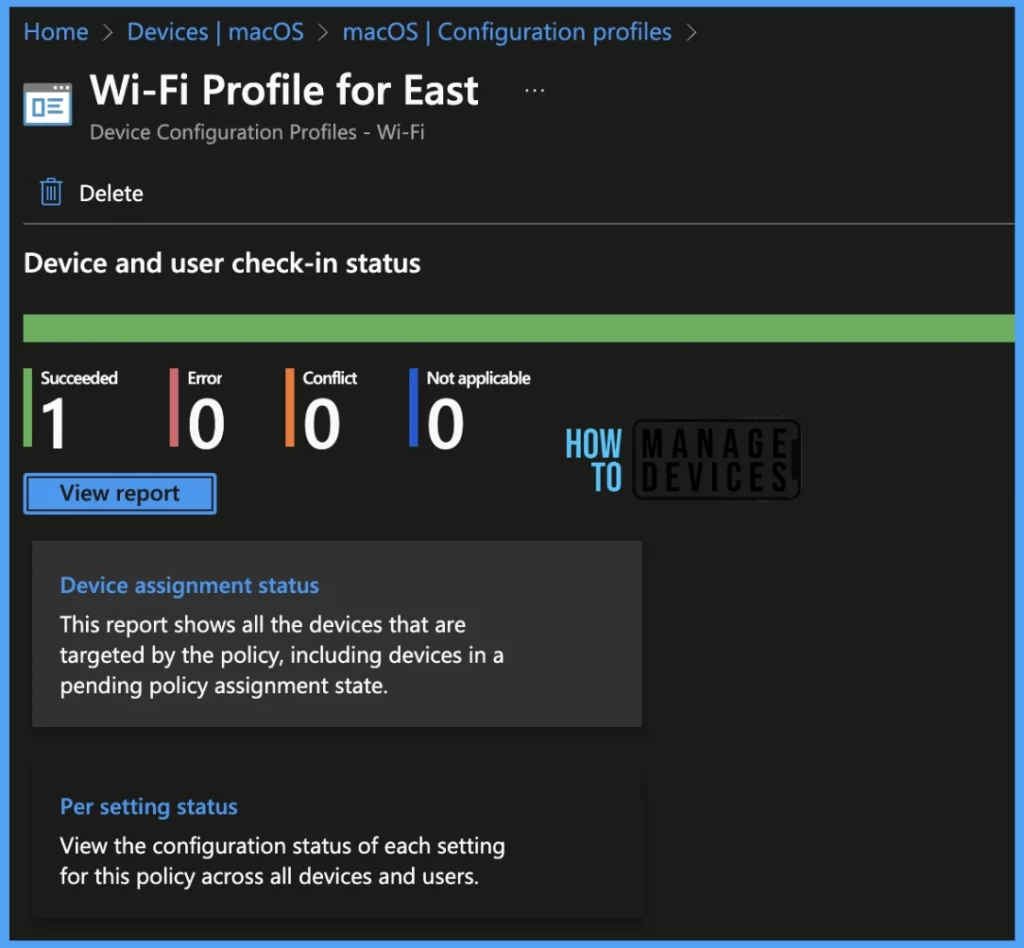
Once you click on the view report button, you can see the list of devices along with their details Device Name, Logged in User, Check-in Status and Last check-in time.
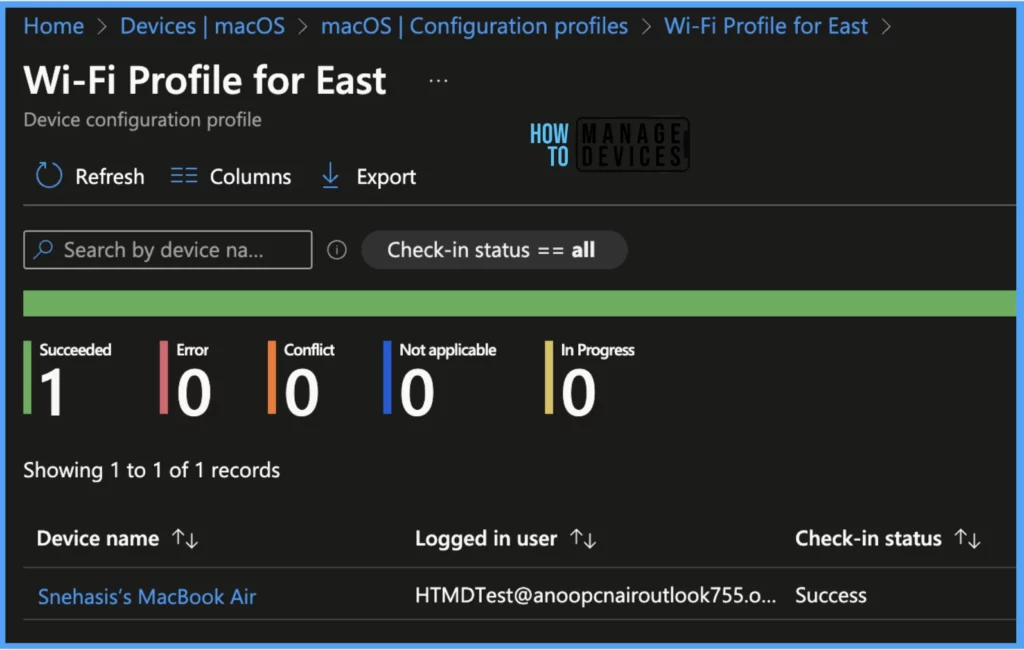
Also, we can view the two different types of reports, and you can quickly check the update as devices/users check-in status reports.
Device assignment status, This report will show the list of targeted devices under the configuration profile, including devices in pending policy assignment status.
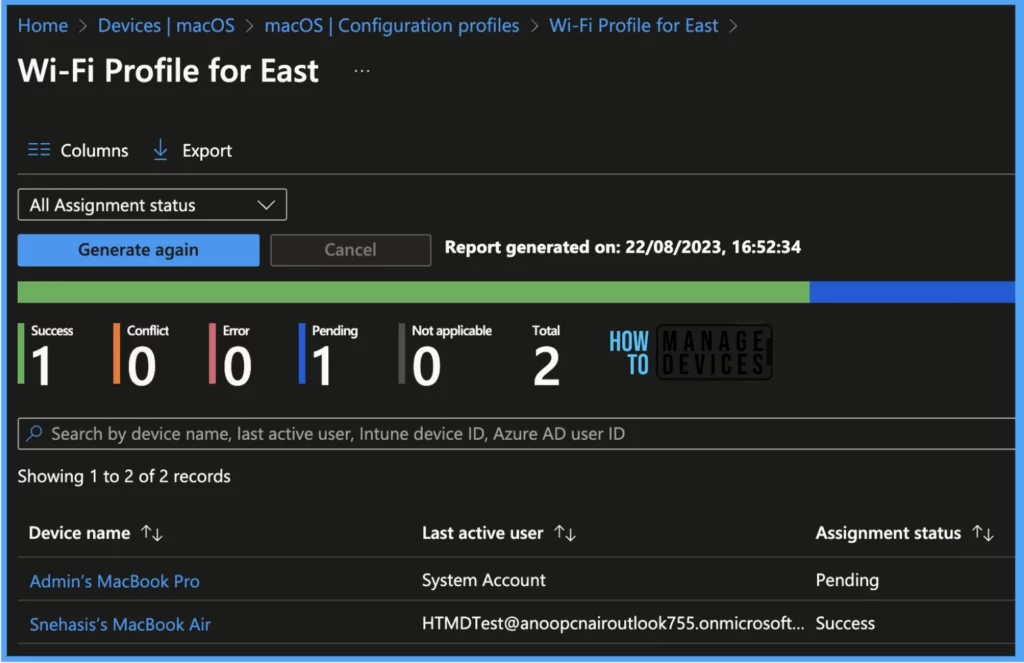
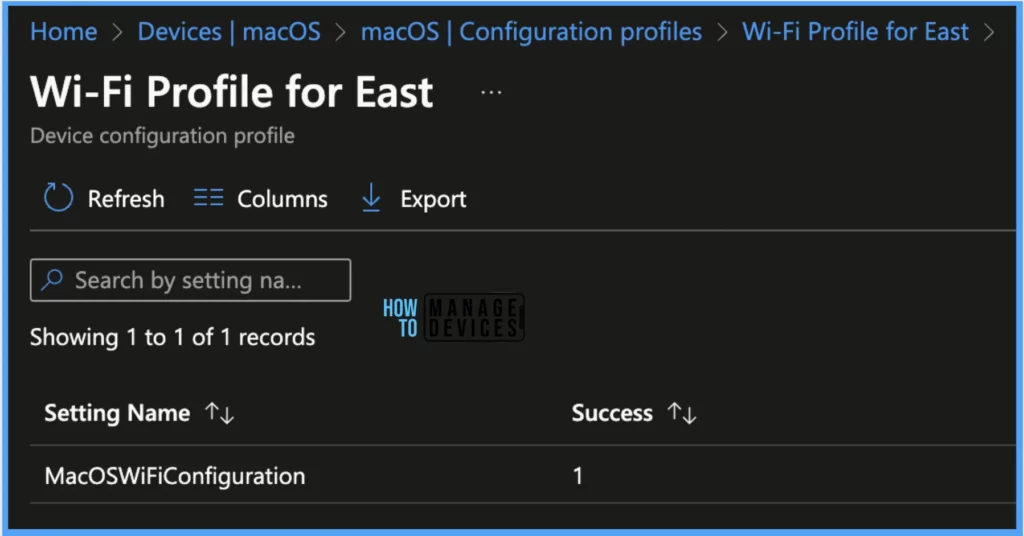
Per settings status, This report will show the configuration status of each set for this policy across all devices and users.
Here’s how to export the Intune setting catalogue Profile report from the Intune portal. You have two options to navigate to the compliance policies node either you can navigate to the Devices node or Endpoint Security, Intune Settings Catalog Profile Report.
- An Easy Method to Enable Tamper Protection for macOS using Intune
- Types of MacOS Enrolment Methods in Microsoft Intune
Results – Check Deployed Profile on macOS
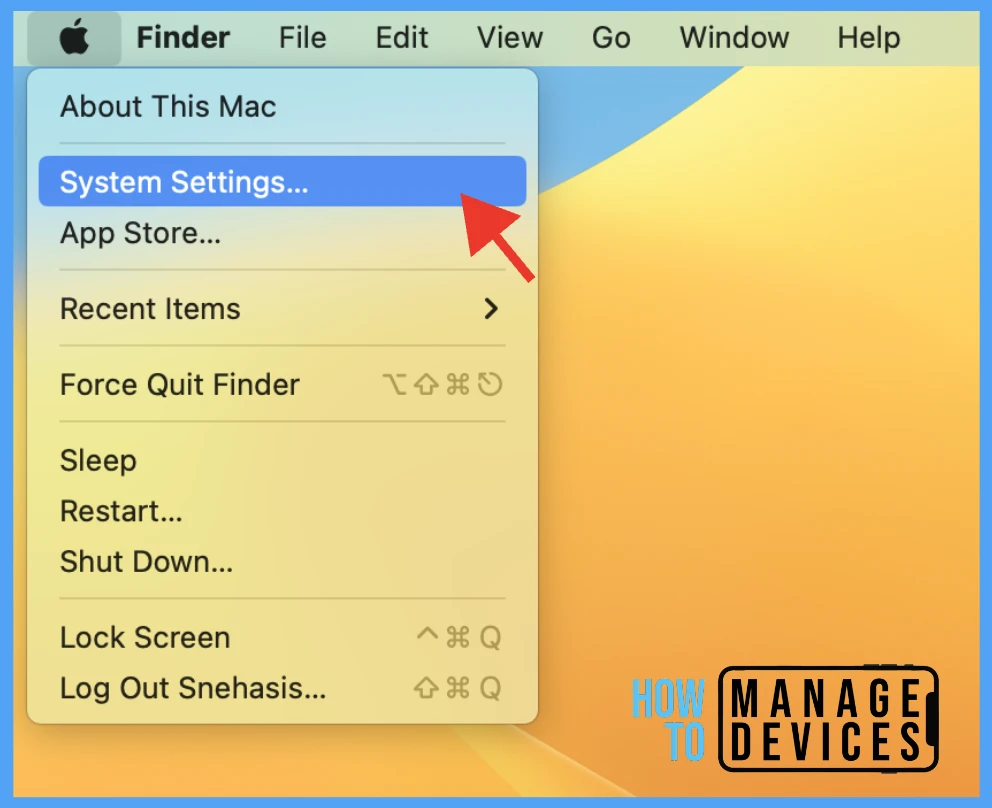
Once the Profile gets pushed to the targeted macOS devices, it may take a few minutes to reflect on the end user’s device. To check the profile status on the client device, we can follow the below steps.
- Click on the Apple icon at the top-left corner.
- Select System Settings from the list of options.
Go to Privacy & Security > Profiles > you can see the WiFi Profile deployed to the device.
Note! Here, I have added the same device for all locations, which shows in case any user is common for all locations, can be part of all groups and can connect from each location as soon as he is in the office.
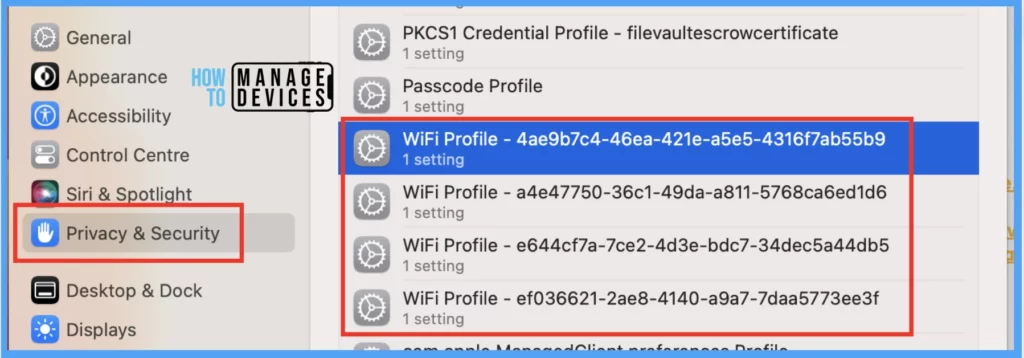
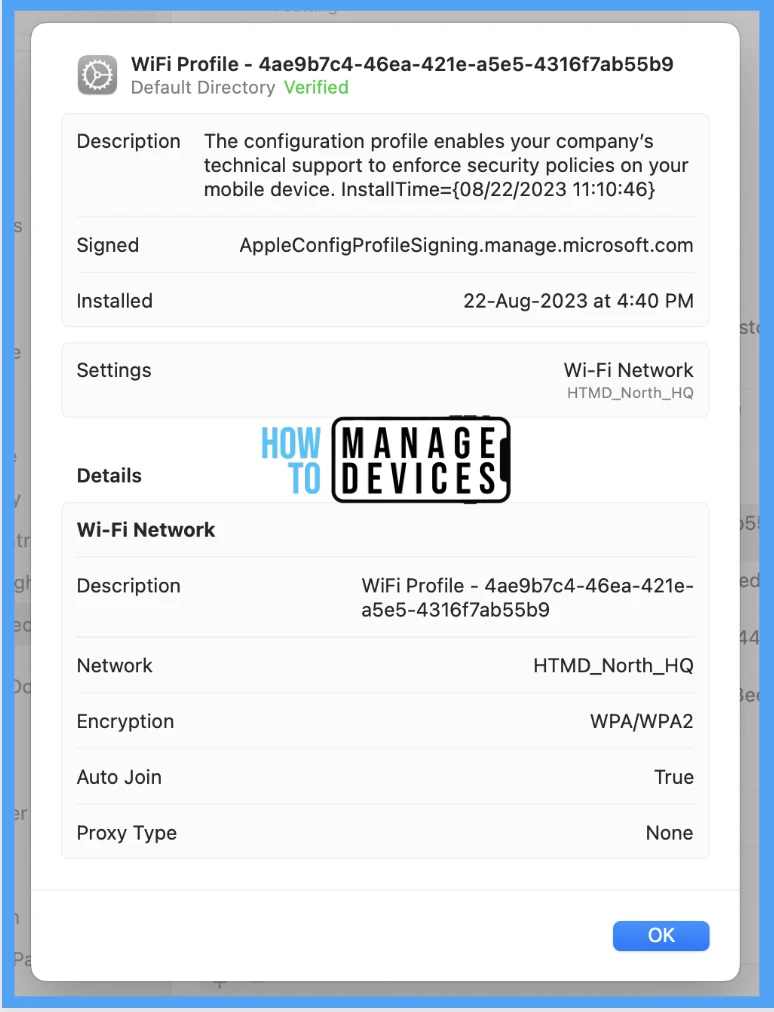
Also, to view the settings/restrictions in a profile, double-click on each Profile and open it to view the details.
End-User Experience
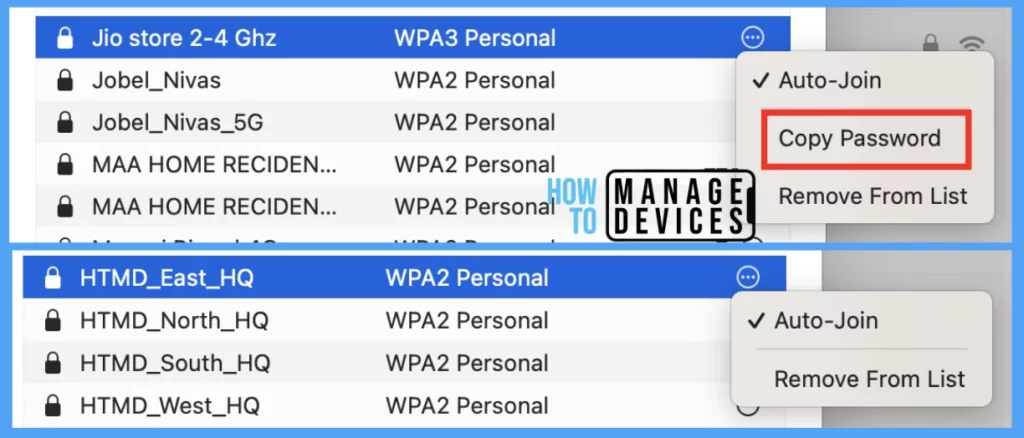
Also, the Wi-Fi configuration details can be seen, by going to System Settings > Wi-Fi > Advanced, and user can see the Wi-Fi profiles pushed to their devices as shown below.
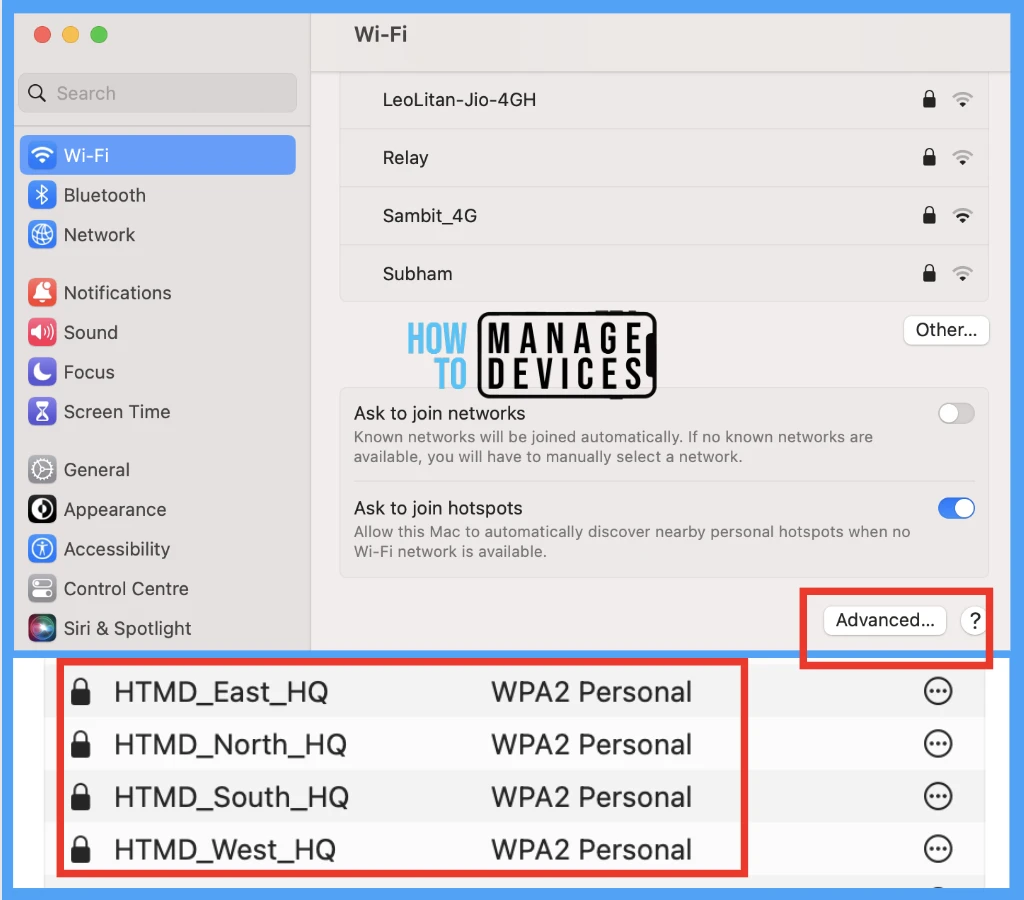
It’s worth noting that Intune not only secures passwords but also ensures that users are not aware of them. This prevents users from sharing their passwords with anyone, whether inside or outside of the organization.
Conclusion
As shown above, IT Admins can easily configure Wi-Fi profiles and distribute them to users’ devices to prevent them from being aware of passwords and sharing them with others. Organizations should plan for ethical ways to prevent data leakage, also, using Proxy settings, Admins can prevent malware infiltration to the network as well.
Author
Snehasis Pani is currently working as a JAMF Admin. He loves to help the community by sharing his Apple Mac Devices Support knowledge. He is an M.Tech graduate in System Engineering.


