Let s discuss Windows LAPS Configurations from Azure AD and Intune. Windows LAPs are now available for both Azure and hybrid AD joined devices. This update was shared by Alex Simons (@Alex_A_Simons) on Apr 21, 2023.
LAPs Client for Windows 11 and 10 are explained in detail in my previous post-New Built-in LAPs Client for Windows 11 and 10, and there are Conflicts with the Old Version of LAPs. We also have a post on managing local administrator (not LAPS) accounts using Intune. Now let’s learn the server part of LAPs, i.e. (Azure AD and Intune).
Microsoft made new updates in LAPS from the server side (Azure AD and Microsoft Intune). You can easily start using it with Azure AD and Microsoft Intune to secure your Windows devices joined to Azure AD. This post is to guide you with Azure AD and Intune configurations for LAPS.
LAPs is a Windows feature; every Windows device has a built-in local administrator account that you must secure and protect to mitigate any Pass the Hash(PtH) and lateral traversal attacks. Windows LAPS is a superior solution for safeguarding your local admin passwords, and it automatically manages and backs up the password of the local admin account.
- Setup New Windows LAPs Using Intune Policies
- Windows LAPS Role Based Access Controls Using Intune
- Windows LAPS Configurations from Azure AD and Intune
- Microsoft Intune 2304 April Update Windows LAPS Management
- New Built-in LAPs Client for Windows 11 and 10 | Conflict with Old Version of LAPs
- Azure AD LAPs Group Policy Settings for Windows 11 | Intune Policy for LAPs
- OLD LAPS for Windows 10 11 Privileged Access Management
What is Local Administrator Password Solution?
Local Administrator Password Solution is a Windows feature that automatically manages and backs up the password of the local admin account.
What is Windows LAPS with Microsoft Entra?

Microsoft Endpoint Manager supports the deployment and management of LAPS through a feature called Microsoft Endpoint Manager Policy CSP. This feature allows administrators to configure LAPS settings on Windows devices using Endpoint Manager policies. This provides a centralized way to manage local administrator passwords across all devices in an organization.
What are the Important Capabilities Microsoft Enabled in the Preview?
1. Turn on Windows LAPS using tenant– and client-side policies to back up the local administrator password to Azure AD.
2. Configure client-side policies via the Microsoft Intune portal for local administrator password management to set account name, password age, length, complexity, manual password reset, and so on.
3. Recover stored passwords via Microsoft Entra/Microsoft Intune portal or Microsoft Graph API/PSH
4. Enumerate all LAPS-enabled devices via the Microsoft Entra portal or Microsoft Graph API/PSH.
5. Create Azure AD role-based access control (RBAC) policies with custom roles and administrative units for authorization of password recovery.
6. View audit logs via the Microsoft Entra portal or Microsoft Graph API/PSH to monitor password update and retrieval events.
7. Configure Conditional Access policies on directory roles that have the authorization of password recovery.
Intune and Azure AD Configuration of Windows LAPs
Local Administrator Password Solution (LAPS) is now accessible for devices joined to Azure Active Directory and hybrid Active Directory. This means that regardless of the domain type joined, Windows devices can utilize LAPS to manage local administrator passwords securely.
Whether the device is joined to the cloud-based Azure AD or the on-premises Active Directory, administrators can implement LAPS to ensure that local administrator passwords are unique, complex, and frequently rotated. This unified LAPS support for both types of domains joins more flexibility and consistency in password management across all Windows devices in an organization.
Requirements for Intune to Support Windows LAPS in Your Tenant
The requirements for Intune to support Windows LAPS cover the Licensing requirements. The Licensing requirements include the Intune subscription and Active Directory subscription.
| Licensing requirements | Discription |
|---|---|
| Intune subscription | Microsoft Intune plan 1, which is the basic Intune subscription. You can also use Windows LAPS with a free trial subscription for Intune. |
| Active Directory subscription | Azure Active Directory free is the free version of Azure AD that’s included when you subscribe to Intune. With Azure AD free, you can use all the features of LAPS. |
Setting Up LAPS in Microsoft Intune Endpoint Security
Microsoft Endpoint Manager and LAPS provide a powerful solution for managing local administrator passwords on Windows devices, helping organizations secure their endpoints and protect against security threats. Windows LAPS is now built into Windows of the following.
- Windows 10 20H2 and later
- Windows 11 21H2 and later
- Windows Server 2019 and later
Note! – The most beneficial aspect of LAPs is that it is readily accessible in Azure Active Directory without any cost. In other words, the LAPS is available in Azure AD for free.
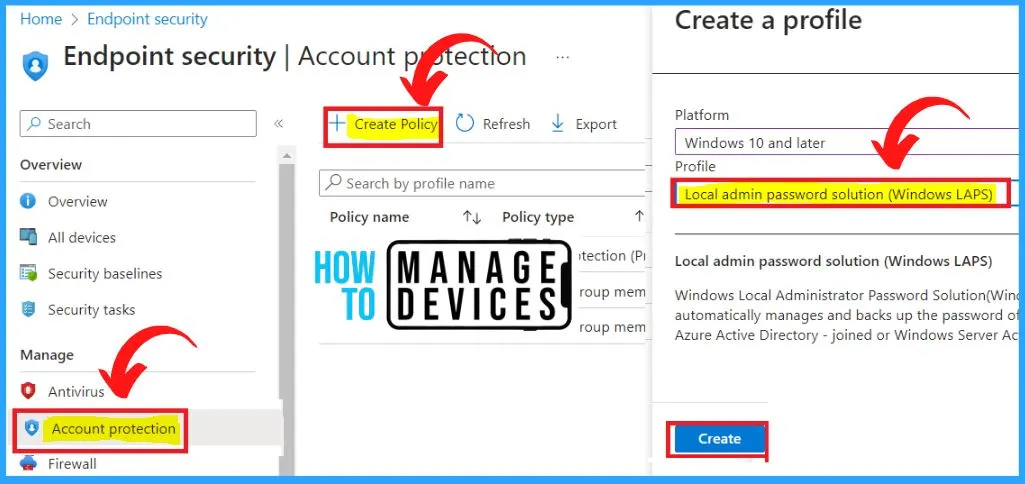
- In the Microsoft Intune portal – Endpoint security menu, select Account protection
- Select Create Policy to create a Windows LAPS profile for Windows 10 and later
- During profile creation, the pick Backup Directory to be Azure AD
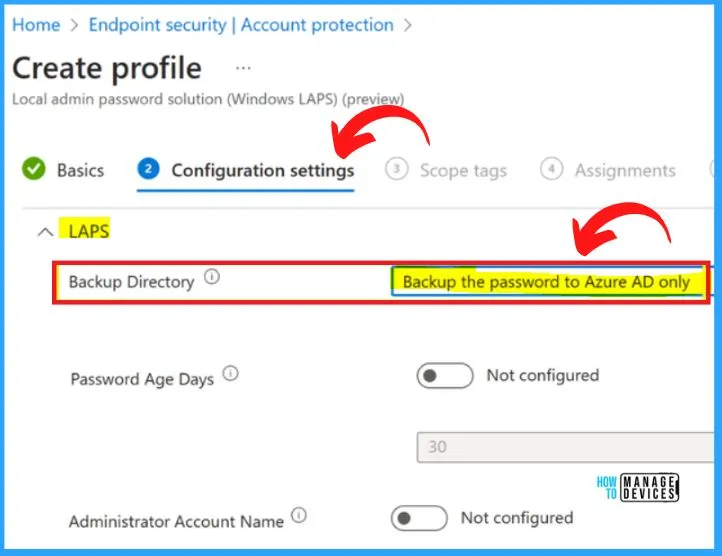
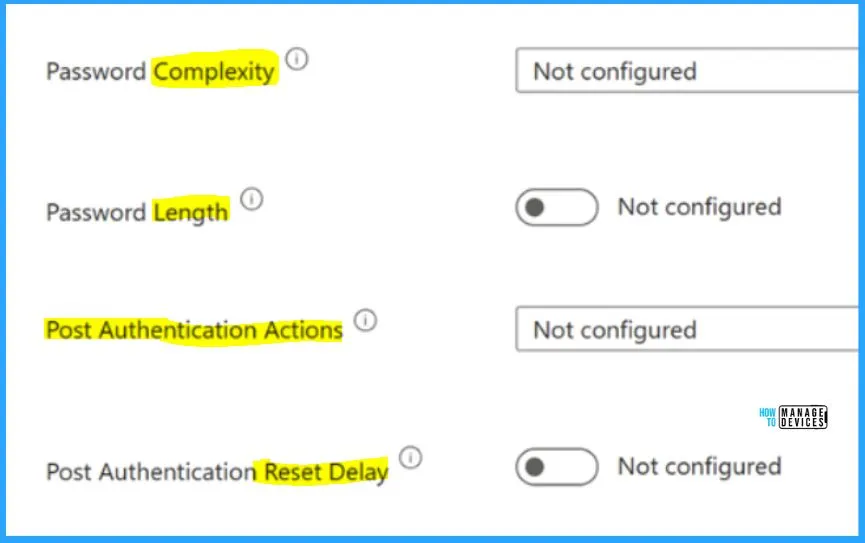
And can also configure other client policies for LAPS, do the Assignments to Azure AD groups, and finally, selects Review + Create. Setting up LAPS in Microsoft Intune Endpoint security includes the following options.
- Password Complexity – It includes large and small letters, numbers, and special characters
- Password Length – It indicates the length of the password
- Post Authentication Actions – It helps to show the Authentication action
- Past Authentication Reset Delay – It helps to establish whether the Authentication reset delay is configured or not
Deploy Local Admin Password Solution Policy to Windows
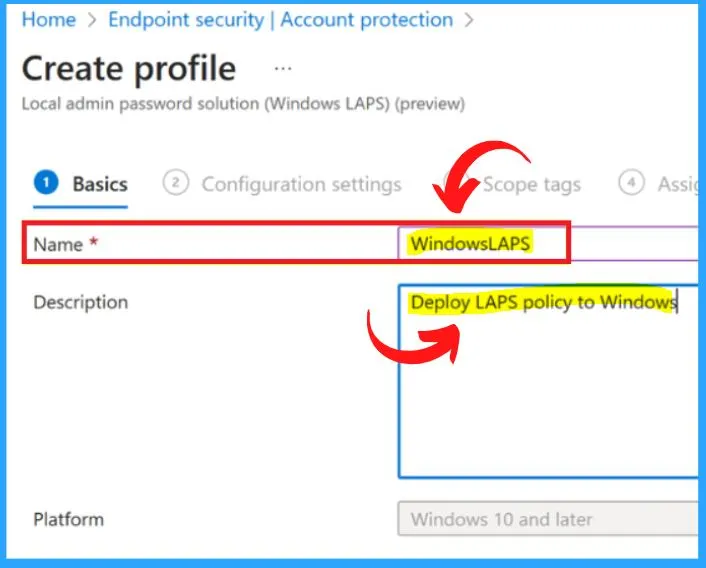
The basic settings to deploy the Local Admin Password Solution policy to Windows are shown in the below screenshot. Under the name section, type the WindowsLAPS, and Unde description, type Deploy LAPS policy to Windows.
Account Protection in Endpoint Security
Account protection is an important component of endpoint security that focuses on protecting user accounts from unauthorized access and credential theft. Implementing strong authentication, password policies, PAM, and IAM solutions can help organizations better to protect their user accounts and sensitive resources from attackers.
- In the Microsoft Intune Endpoint security menu, select Account Protection.
- Select Create Policy to create a Windows LAPS profile for Windows 10 and later.
- Under Create a Profile,
- Platform – Windows 10 and later
- Profile – Local admin password solution ( Windows LAPS )
- Select Create button from the below window
Setting Up LAPS in Azure AD Devices
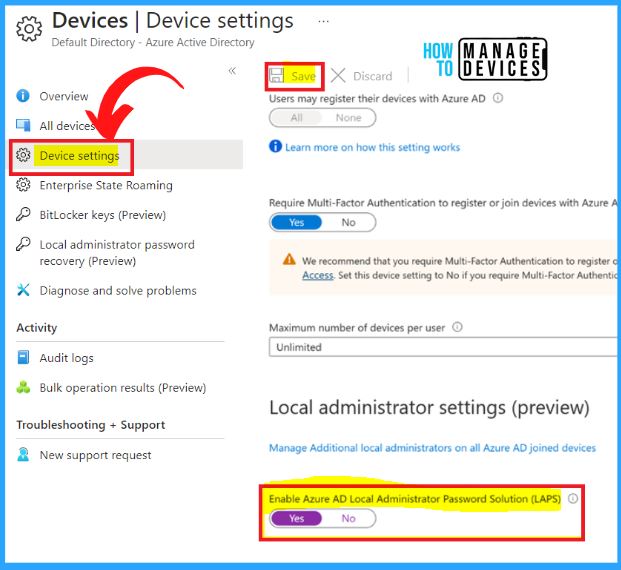
Once you have set up LAPS, the local administrator account password on each Azure AD device will be automatically changed and managed by LAPS. The password will be stored in the computer’s Active Directory object and can be retrieved by authorized users when needed.
This helps to prevent the spread of a compromised password across multiple devices, improving security in your organization.
- In the Azure Portal – Azure AD – AD Devices menu, select Device settings
- Select Yes for the LAPS setting
- Click Save
Reference site – Introducing Windows Local Administrator Password Solution with Microsoft Entra (Azure AD) – Microsoft Community Hub and Announcing Windows LAPS management through Microsoft Intune – Microsoft Community Hub
Author
About Author – Vidya is a computer enthusiast. She is here to share quick tips and tricks with Windows 11 or Windows 10 users. She loves writing on Windows 11 and related technologies. She is also keen to find solutions and write about day-to-day tech problems.


Does anyone have any information on the correct process for migrating from On-Premis LAPS to Intune? I have read there are issues with it, but I want to know if there is a clear process to perform the migration.
One quick question. I already have it on my on prem server (hybrid) but as I want to move on Azure cloud only, should I first remove it from on prem and then deploy it on Azure Cloud through Intune or can I have it on the same time and remove it after?
With this in place is it possible for the password to reset while the device is not connected to the internet to update Azure? I am concerned about the possibility of not being able to look up the password because it reset but hasn’t updated the entry online.
Thank you
Greetings,
we alredy have LAPS install on the Prem Server..so we want install the new built from LAPS that were released in Afril 2023. Can someone please tell me how to do this with the migration?
Bestt Reagrds
Bah
Hi, It’s available here https://learn.microsoft.com/en-us/mem/intune/fundamentals/deployment-guide-intune-setup
After setting up the LAPS as explained in the article, you can look for the migration options.