Le’s check how you can manage Windows LAPS Role Based Access controls using Intune. Local Administrator Password Solution is a Windows feature that automatically manages and backs up the password of the local admin account.
Local Administrator Password Solution (LAPS) is now accessible for devices joined to Azure Active Directory and hybrid Active Directory. This means that regardless of the domain type joined, Windows devices can utilize LAPS to manage local administrator passwords securely.
The requirements for Intune to support Windows LAPS cover the Licensing requirements. The Licensing requirements include the Intune subscription and Active Directory subscription.
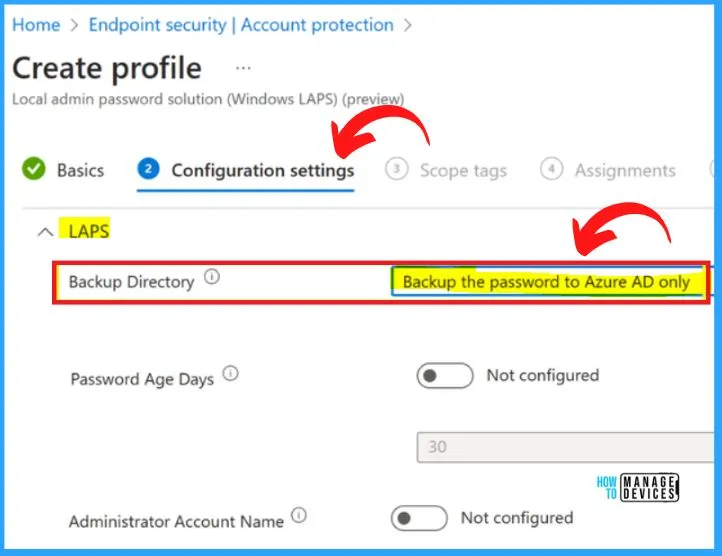
You can deploy the Local Admin Password Solution policy to Windows by accessing Account Protection in Endpoint Security within Intune console. Once you have set up LAPS, the local administrator account password on each Azure AD device will be automatically changed and managed by LAPS.
The password will be stored in the computer’s Active Directory object and can be retrieved by authorized users when needed. This post helps you to know more about the required access for creating LAPS policy and managing local administrator passwords.
- Setup New Windows LAPs Using Intune Policies
- Windows LAPS Role Based Access Controls Using Intune
- Windows LAPS Configurations from Azure AD and Intune
- Microsoft Intune 2304 April Update Windows LAPS Management
- New Built-in LAPs Client for Windows 11 and 10 | Conflict with Old Version of LAPs
- Azure AD LAPs Group Policy Settings for Windows 11 | Intune Policy for LAPs
- OLD LAPS for Windows 10 11 Privileged Access Management
Create and Access LAPS Policy in Intune
Microsoft Endpoint Manager and LAPS provide a powerful solution for managing local administrator passwords on Windows devices, helping organizations secure their endpoints and protect against security threats.
To work with and view LAPS policies, your account must be assigned sufficient permissions from the Intune RBAC category for Security baselines.
- Sign in to the Microsoft Intune admin center https://intune.microsoft.com/.
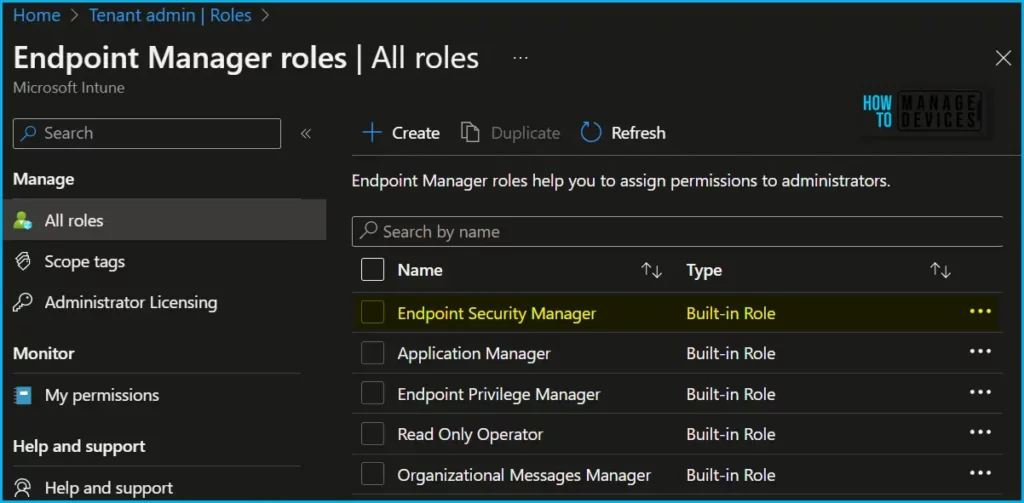
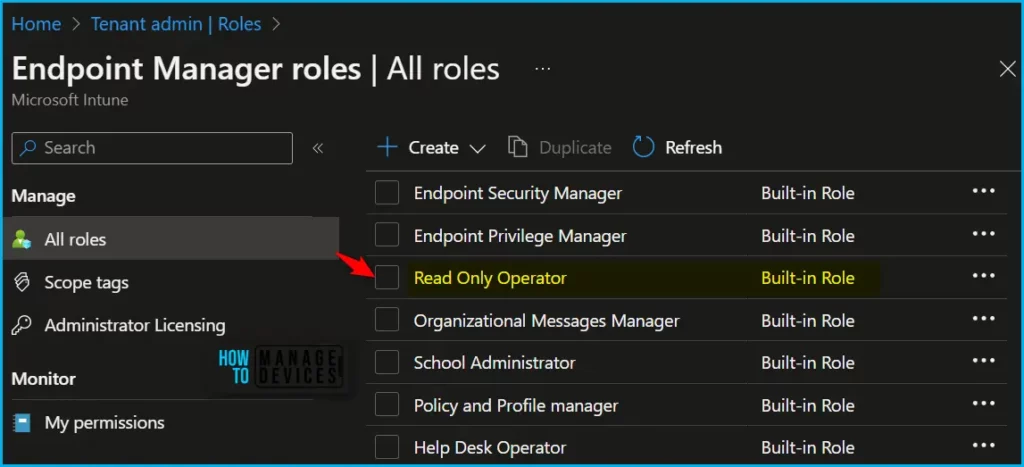
- Navigate to Tenant administration > Roles.
- In the All roles, you will find all the built-in roles, and created custom roles available in the tenant.
The Endpoint Security Manager built-in role manages security and compliance features, such as security baselines, device compliance, conditional access, and Microsoft Defender for Endpoint. in Intune console.
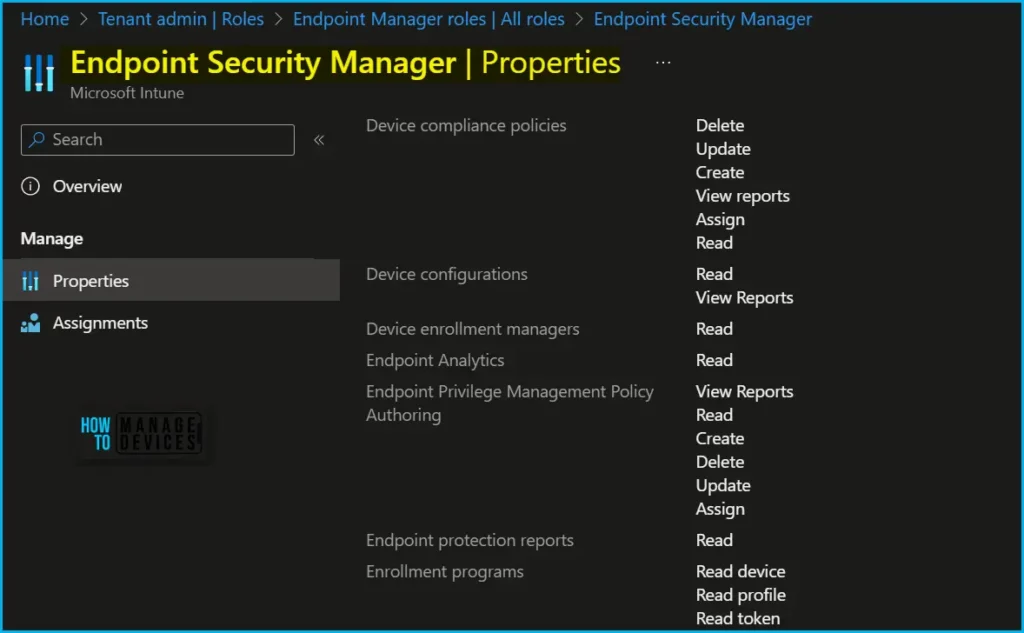
Here is how you can check the LAPS Role Based Access permissions by navigating to the roles by clicking on Properties. By default, these are included in the built-in role Endpoint Security Manager. To use custom roles, ensure the custom role includes the rights from the Security baselines category.
Note! You can assign built-in roles, Endpoint Security Manager, to groups without further configuration. You can’t delete or edit the name, description, type, or permissions of a built-in role.
Local Admin Password Solution policies can be configured from Endpoint Security Node, Account Protection view. Clicking on “Create Policy” button will present the policy creation wizard.
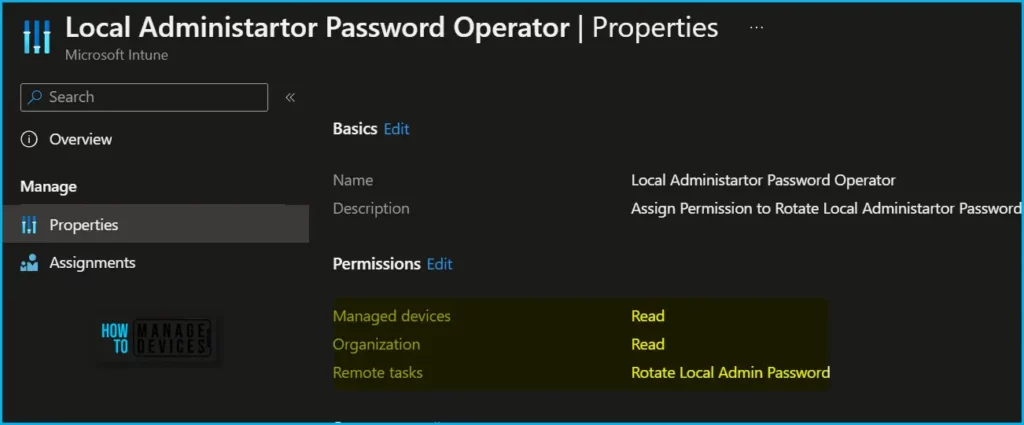
Rotate Local Administrator Password
To use the Intune admin center to rotate a devices local admin account password, your account must be assigned the following Intune permissions:
- Managed devices: Read (View Intune managed devices.)
- Organization: Read (View tenant settings such as device categories and Exchange Connectors. This permission is required to activate all enrollment workflows.)
- Remote tasks: Rotate Local Admin Password (Initiates a manual rotation for the local admin password on the device)
Retrieve local Administrator Password
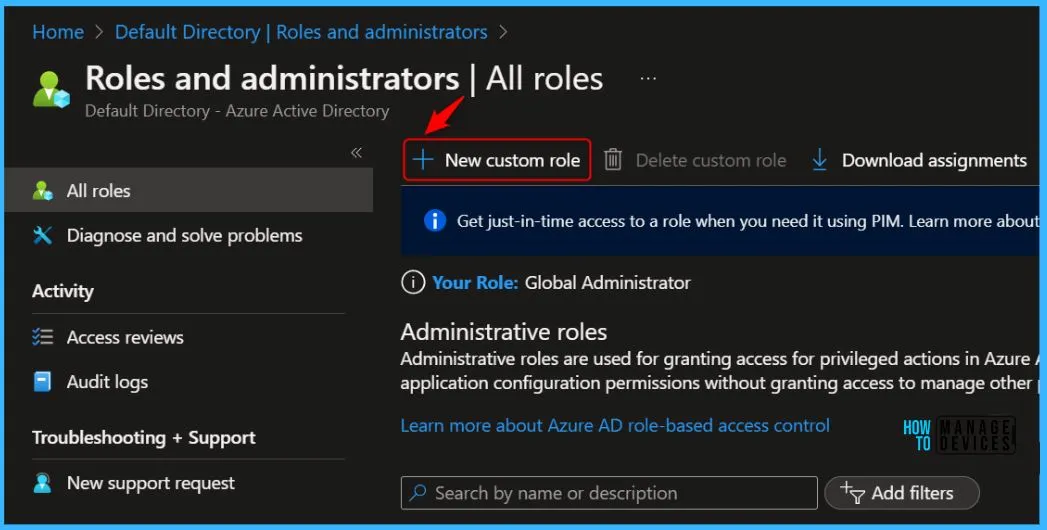
To create, edit, or assign roles, your account must have Global Administrator or Privileged Role Administrator permissions in Azure AD.
- Sign in to the Azure portal or Azure AD admin center.
- Select Azure Active Directory > Roles and administrators. Click on the New custom role.
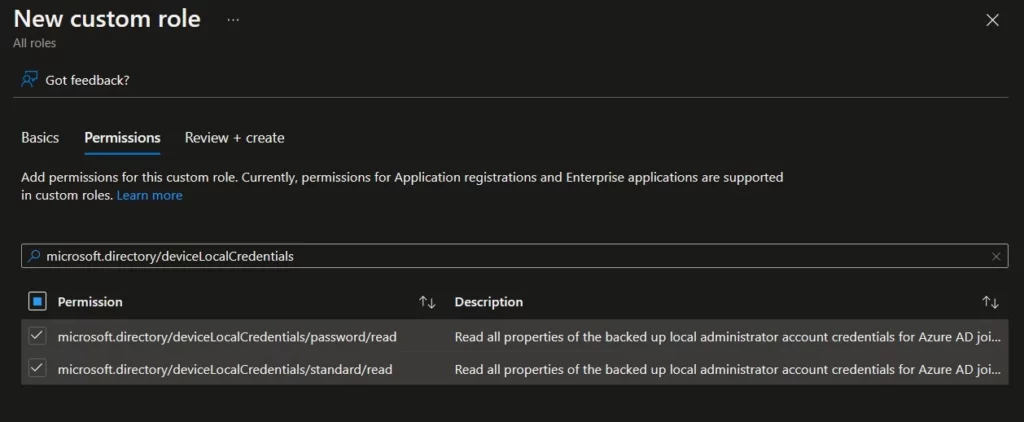
On the Permissions page, choose the permissions you want to use with this role. To add Local Credentials read permission, search with the keyword “deviceLocalCredentials” and To view password details, your account must have one of the following Azure Active Directory permissions.
It is necessary to create a custom role, and assign it to the group of users for access. Also, to allocate permissions use either the Microsoft Graph API or PowerShell. Once the custom role has been created, it can be assigned to users.
| Permission | Description |
| microsoft.directory/deviceLocalCredentials/password/read | Read all properties of the backed up local administrator account credentials for Azure AD joined devices, including the password. |
| microsoft.directory/deviceLocalCredentials/standard/read | Read all properties of the backed up local administrator account credentials for Azure AD joined devices, except the password. |
View Azure AD Audit Logs and Events
All Windows LAPS operations are tracked with rich eventing. Learn about key events and view the log, you should have the required permissions. To view details about LAPS policies and recent device actions such as password rotation events, your account must have permissions equivalent to the built-in Intune role Read Only Operator.
Event Logs for New Windows LAPs Client? The following is the event log path for the new Windows LAPs Client! Applications and Services Logs – Microsoft – Windows – LAPS.
Author
About Author – Jitesh, Microsoft MVP, has over six years of working experience in the IT Industry. He writes and shares his experiences related to Microsoft device management technologies and IT Infrastructure management. His primary focus is Windows 10/11 Deployment solution with Configuration Manager, Microsoft Deployment Toolkit (MDT), and Microsoft Intune.


Hey Jitesh,
Thank you for this amazing article. I have one question, this Local Administrator Password Operator, that you created, is it InBuilt role or a custom role that you created ?