Hello Techies, I Hope you are doing great! This week, I want to discuss the New Managed Settings in macOS Catalogue using Intune service release 2309 or later. If you are unaware of what a configuration profile is and how to deploy configuration profiles, check my previous post here: How to deploy a sample Configuration profile on macOS Using Intune.
Before we jump into the new available settings, If you are unsure about how to check the service release status on the Intune portal, check out the Section How to Check Microsoft Intune Version in the post: Intune August Update 2309 New Features Improvements.
In case you missed reading our previous post on How to set Microsoft Outlook for macOS using Intune, we’ve got you covered; The article includes everything a user needs to perform while setting up Outlook for the first time in macOS and its awesome productive features, which save a lot of human effort.
Also, do you know the macOS Sonoma was released on September 26th? We’ve got it covered with an article, Upgrade to macOS Sonoma and Intune Management, which includes eligible devices for the Upgrade, and all the awesome features that’ll make tech lovers’ hearts skip a beat. We covered configuration profile settings available only for macOS Sonoma through Intune.
If you like my posts on how to manage macOS devices using Microsoft Intune, check out all my related posts here. Recently, we have covered a video on how to restrict corporate macOS devices using Intune, and we discussed in detail all the restriction settings and their purpose. For example, disabling AirDrop or iCloud to keep your data safe. Check it out below.
In our previous articles, we discussed the definition of a configuration profile and why deploying configuration profiles is necessary for macOS devices. Now, let’s dive into the topic and explore the latest settings available in Intune service release 2309 or later versions, specifically those applicable only for macOS.
| New settings in macOS | Configurations | Description |
|---|---|---|
| Managed settings | i. Bluetooth ii. MDM Options | This setting determines the level of protection Defender provides for Endpoint for blocking and scanning suspicious files. |
| Microsoft Defender | Cloud-delivered protection preferences > Cloud block level | This setting determines the level of protection provided by Defender for Endpoint for blocking and scanning suspicious files. |
| Remote Help | Supports on link: https://remotehelp.microsoft.com/ | Access view-only remote assistance sessions on macOS devices running Big Sur or later with the Remote Help |
| Endpoint detection and response (EDR) | Value & type of tag | Set up EDR preference settings in Microsoft Defender for Endpoint using this setting. |
What is EDR?
Before we initiate the configuration, let us understand what EDR is and its purpose, and then it would be easy for us to configure.
As we know, Microsoft Defender for Endpoint can be integrated with Intune to manage endpoint detection and response (EDR) settings and onboard devices. The EDR capabilities of Microsoft Defender for Endpoint provide advanced, real-time attack detections.
EDR policies include platform-specific profiles that manage EDR settings and automatically onboard devices. The policies are deployed to device groups in Azure AD managed with Intune and Configuration Manager for on-premises devices. Separate EDR policies are necessary for different device types.
Prerequisites to Deploy EDR Configuration Profiles
Also, before configuring the settings, let us check the pre-requisites required:
- Devices must be enrolled with Intune
- Devices are managed through the opt-in public preview for Security Management for Microsoft Defender for Endpoint.
- Microsoft Defender for Endpoint tenant must be integrated with your Microsoft Intune tenant to create EDR policies.
This article covers the new settings which can be configured through the configuration profile. In upcoming posts, we will cover the remote help feature in a separate article. Let’s get started. Before we start the configuration, we must ensure the required access is provided in the Intune Portal.
Configuration Profile Creation using New Managed Settings in macOS Catalogue
In this configuration, we will be configuring only two settings, i.e., Bluetooth and MDM options. To configure, please follow the steps mentioned below.
- Sign in to the Microsoft Intune Admin Center: https://endpoint.microsoft.com/.
- Select Devices > macOS > Configuration profiles.
- Select Platform – macOS, Profile – Settings Catalog, and Click on Create.

After clicking on Create, Provide the Name of the Profile with a detailed description and click Next to move further.

Under the Configuration settings, let us configure all the 3 categories and provide values as mentioned in the sample configuration profile below.
New Managed Settings
Let’s explore the new settings available on Intune service release 2309 or later for Bluetooth and MDM options and review their configuration based on usage and impact.
| Configuration Setting | Description | Value |
|---|---|---|
| Bluetooth | Under this configuration, Admins permit users to configure to enable/disable Bluetooth on devices. | Enabled / Disabled |
| MDM Options | Under this configuration, a supervised device registers itself with Activation Lock when the user enables Find My on their Apple account. | Allowed / Disabled |
For the sample profile, Below are the configuration settings I have used. You can set the configurations according to your requirements.
| Configuration Settings | Value |
|---|---|
| Bluetooth | Enabled |
| MDM Options | Allowed |
Note! When granting Bluetooth permission, be aware that it may impact with data-sharing abilities of the end-users.

Microsoft Defender Configuration
Let’s take a look at the new configuration setting for Microsoft Defender. It’s been categorized into 5 values ranging from Normal to Zero tolerance. I’ll break it all down for you in the table below.
| Configuration Setting | Description | Value |
|---|---|---|
| Cloud Block Level | Under this configuration, Admins can set the level of protection provided by Defender for Endpoint for blocking and scanning suspicious files. According to the below categories Normal: The default blocking level Moderate: Verdicts are given only for highly confident detections under this category. High: The system blocks unknown files to prioritize performance optimization and prevent potential harm. High Plus: The system blocks unknown files and uses additional protection measures that could affect device performance. Zero Tolerance: Blocks all unknown programs. | i. Normal ii. Moderate iii. High iv. High plus v. Zero Tolerance |
Below are the configuration settings I have used in the sample profile.
| Configuration Settings | Value |
|---|---|
| Cloud Block Level | Moderate |
While configuring the setting, For strict environments, like banking finance-related companies, pick Zero Tolerance. For simpler end-user management environments, pick Normal.

EDR (Endpoint Detection & Response) Configuration
To manage EDR preferences on Microsoft Defender for Endpoint for macOS, use the GROUP tag to filter and group devices by a specified value visible on the device page in the portal.
| Configuration Setting | Description | Value |
|---|---|---|
| Value of tag | Specifies the value of the tag | Any string values |
| Type of tag | Specifies the type of tag | GROUP |
Below are the configuration settings I have used in the sample profile.
| Configuration Settings | Value |
|---|---|
| Value of tag | anoopcnair.com |
| Type of tag | GROUP |
Note! You can only set one value per tag type, and each tag type is unique and should not be repeated in the same configuration profile.

On the next page, Scope tags are filtering options provided in Intune to ease the admin jobs. In the scope tag section, Admins get the option to configure according to which market the profile should be tagged or deployed to before selecting the assignment group, once it is configured. Click on Next.

On the next page, select Assignments group (Included groups and Excluded groups), or else as shown below, we have selected to deploy to all devices as the mandate option and click Next.
Assignment Group: It determines which group should get the app, policy, or configuration profile by assigning the group name with user details to include and exclude.

On the Review+create page, please review if any settings need to be changed, or else go ahead and create the policy.

Change in Existing Profile
As we discuss the additional configuration, Administrators can follow the steps below to edit it in an existing Antivirus policy.
- Ensure the Intune Portal is running on Intune release 2309 or later
- Go to Devices > macOS > Configuration Profiles
- Search for the existing policy, and click on the profile to edit.
- Click on properties > Configuration Settings > Edit
- Now you can configure the new settings and click on save.
Note! In the picture below, we are adding the MS Defender profile to the existing one.

Although the policy already exists on the end-user device, as we have made new modifications, it should be reflected upon the next sync on all the devices.
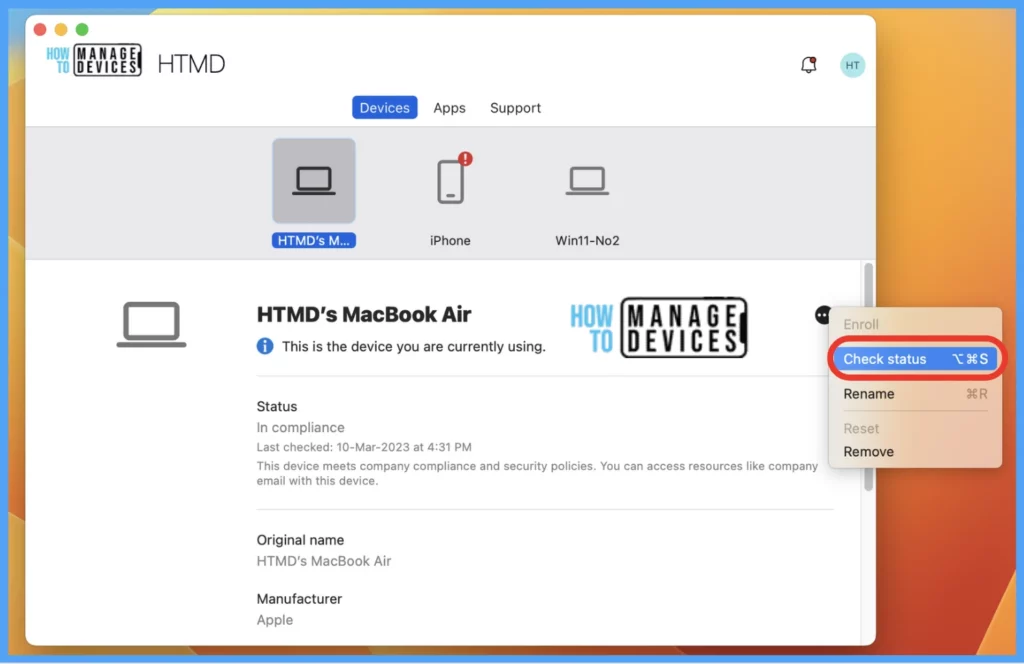
Manual Sync on End-user Device
Once the application deployment policy is created, it will take a few minutes to get pushed to the targeted devices in the selected group; also, we can manually install the app from the macOS device, by launching the company portal app and running check status.
Policy Deployment– Monitoring on Intune Portal
Once the Antivirus policy is created, it will take a few minutes to get pushed to the targeted devices in the selected group; also, to view the push status on the list of targeted devices, we can check as per the below steps.
To see all the device statuses, Navigate to Endpoint Security> under Manage, and select Antivirus. Click on the deployed policy name, and on the Overview page, you can find the list of devices under categories such as below.
- Succeeded
- Error
- Conflict
- Not Applicable
- In Progress

Once you click on the view report button, you can see the list of devices along with their details Device Name, Logged-in User, Check-in Status and Last check-in time.

Also, we can view the two different types of reports, and you can quickly check the update as devices/users check-in status reports.
Device assignment status, This report will show the list of targeted devices under the configuration profile, including devices in pending policy assignment status.
Per settings status, This report will show the configuration status of each set for this policy across all devices and users.

Here’s how to export the Intune setting catalogue Profile report from the Intune portal. You have two options to navigate to the compliance policies node either you can navigate to the Devices node or Endpoint Security, Intune Settings Catalog Profile Report.
- Configure FileVault Encryption For MacOS Devices Using Intune
- Configure macOS Compliance Policy in Intune for Devices
Monitor Antivirus Policy on macOS
Once the Policy gets pushed to the list of macOS devices as part of the assignment group, it may take a few minutes to reflect on the end user’s device. Once the user successfully logs in to the device, we can follow the steps below to check the profile status.
- Click on the Apple icon at the top-left corner.
- Select System Settings from the list of options.
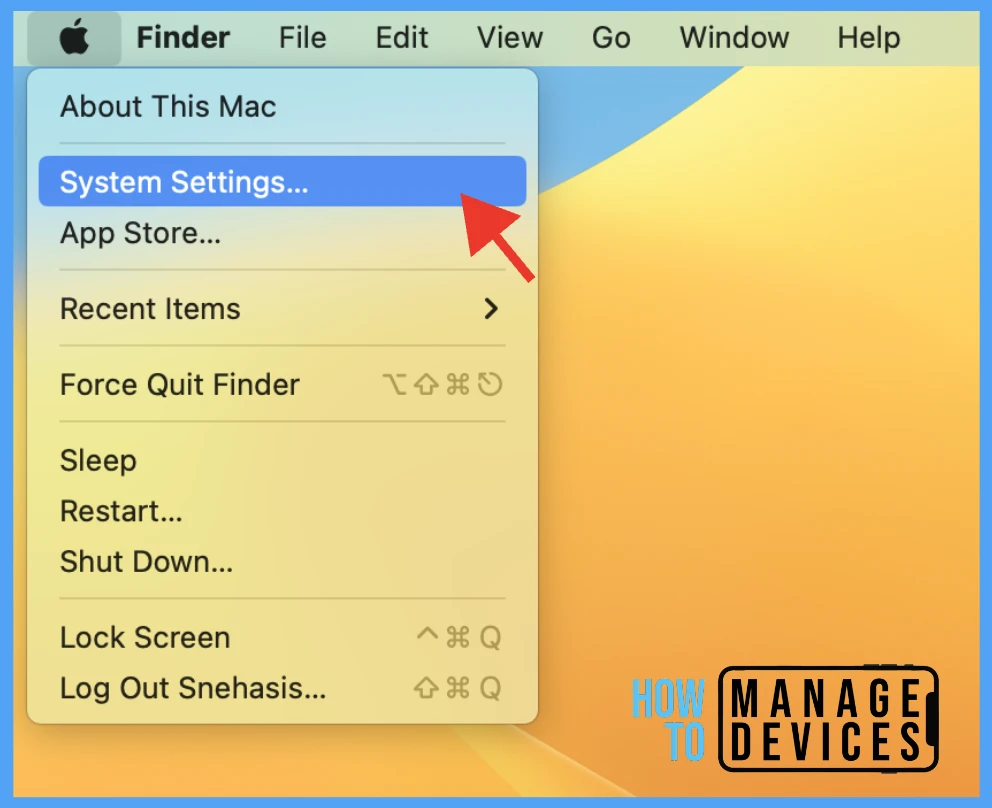
Go to Privacy & Security > Profiles > you can see profiles deployed related to the Antivirus setting on the Mac.

To view the settings in the profiles, double-click and open them to view the details. Here you can see the detailed status of the applied policies.

Conclusion
Organizations must implement antivirus policies to protect company resources and check and add new configurations or settings through Intune for a secure environment across all operating system platforms. These policies secure network activity on user devices.
Author
Snehasis Pani is currently working as a JAMF Admin. He loves to help the community by sharing his Apple Mac Devices Support knowledge. He is an M.Tech graduate in System Engineering.